In this Education video tutorial you will learn how to do a yeast experiment to see how much C02 it produces with different types of food. Yeast is a fungus and it has to eat. After it eats, it produces CO2 gas. The bubbles in bread are produced by the CO2 gas from the yeast. Take five different types of food items and measure out the same quantity for each item. In the video it is 8gms of cookie, oil, flour, salt and sugar. Take six glasses of water and mix one packet of yeast in each glass....

Patrick Norton and Veronica Belmont from Tekzilla will show you how to dual boot Windows 7 and download videos from YouTube. The hosts show viewers how to dual boot Windows XP Pro32 bit and Windows 7 RC 1 64 bit. In the first step as always you will want to back up your hard drive and at the very least they recommend to back up your most important files. In the case that something goes terribly wrong you can use a free program called EASEUS to make a complete image of your whole drive, this a...
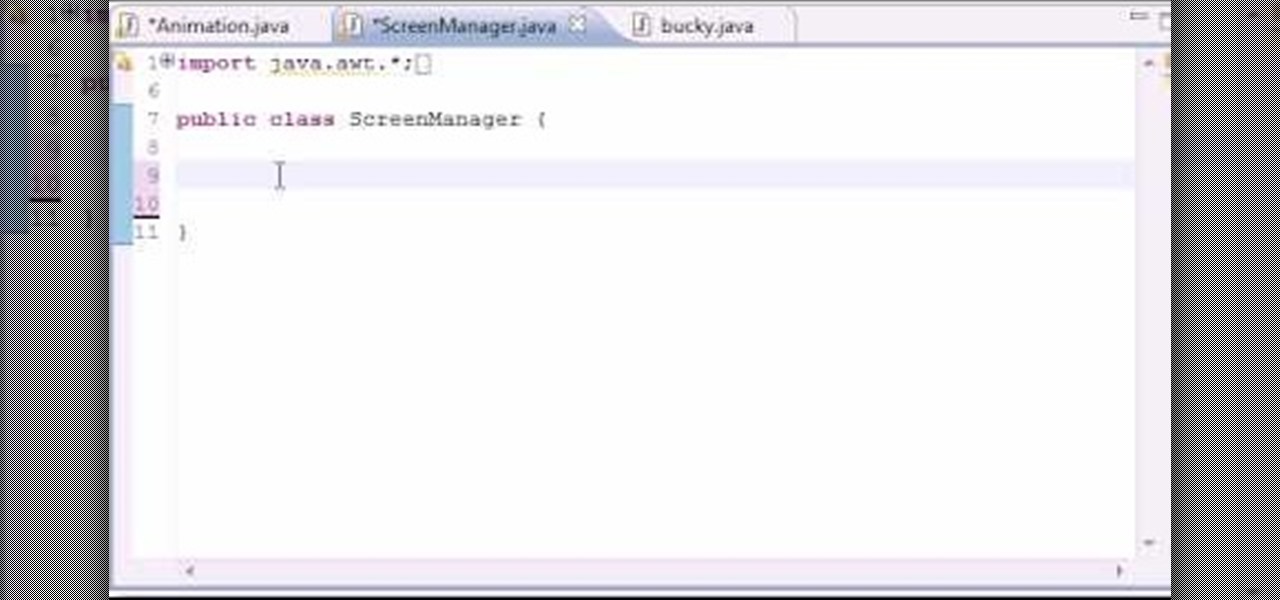
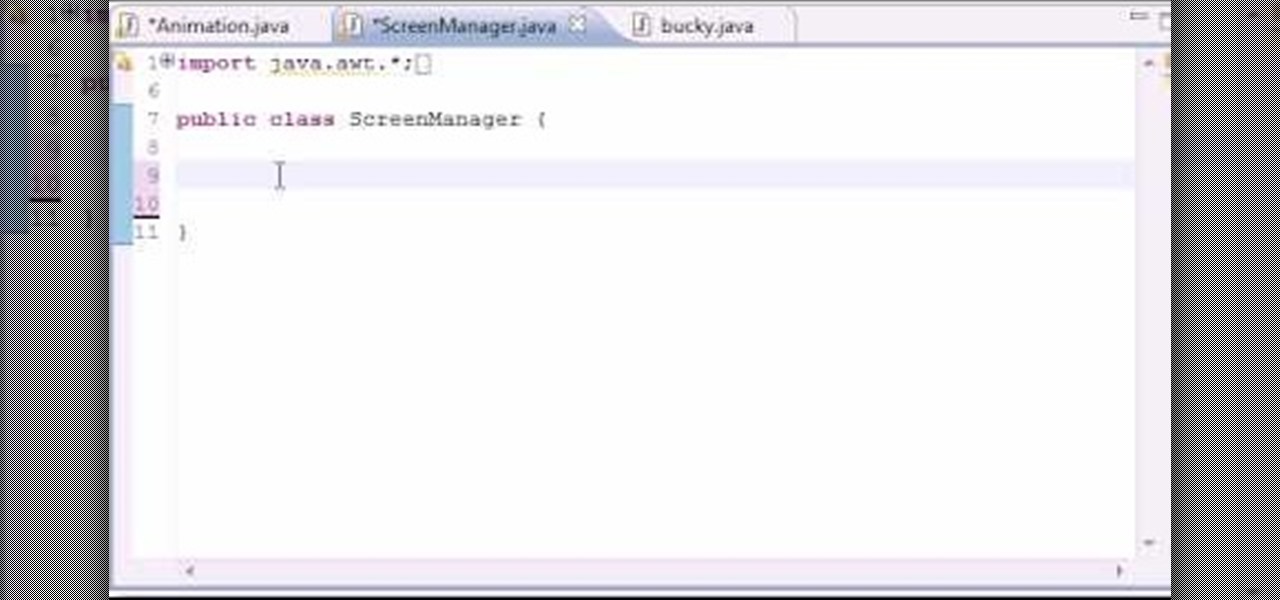
In this 14th video in a series about JAVA game development, "thenewboston" (Bucky Roberts) explains how to redefine your screen to avoid annoying flickering. Flickering in JAVA games often occurs because of time lags as the viewer watches the computer draw a new screen, pixel by pixel. Pre-installed code in JAVA can be used to eliminate this problem by taking advantage of "Buffering" and "Page Flipping". These functions permit you to delay the composition of a new screen until it is finished,...

In this Click Here Photography instructional video, learn how to photograph using a fill flash to produce a great photograph. Equipment, how to set-up, and additional props are gone over. Although a fill flash takes some time to set-up & is an additional item to carry, it will produce better photographic results in certain lighting situations. Learn how to experiment with your fill flash and maximize your photo's potential with the advice, tips, and information given here.

In this video tutorial the instructor demonstrates resonant frequency. In this video the instructor shows the sound of resonance and how to generate it. Resonance is a forced vibration of energy into molecules of an object that makes those molecules vibrate at their resonant frequency. When these molecules vibrate naturally they produce a kind of noise that can be annoying some times. In this video the author makes a small object using a rubber band and a net that produces vibrations when rot...

It's easy to make a peck of pickled peppers – or any other vegetable – with this basic recipe. You Will Need

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

I use my iPhone's personal hotspot all the time. Whether I need a connection on the train, in a coffee shop with no Wi-Fi, or when my friends don't have service, my personal hotspot is a lifesaver. But all that data comes from somewhere, of course, that somewhere being your cellular plan. Luckily, you can see how much data your hotspot has used, as well as who or what used more of it.
Welcome back, my neophytes! Many of you might have a personal diary and might think Why do I spend so much time to write in the damn diary? or Why waste money on the diary, even though you would be wanting it? It's time you found out a solution!

Here's the inevitable food hierarchy you must know if you're a cooking looking to make the most delicious, succulent meals possible: When it comes to cooking with vetables, fresh veggies from the supermarket beats canned, and in season produce beats just about everything else.

Red Bull isn't the only thing that gives you wings. In fact, you can don a pair of wings yourself by painting on winged cat liner on your eyelids. Winged liner is a coveted makeup look because it helps to lengthen and enlarge small eyes, make close set eyes appear farther apart, creates the illusion of more eyelashes, and gives you a sultry siren look. For such a simple tool it produces amazing, face-changing results.

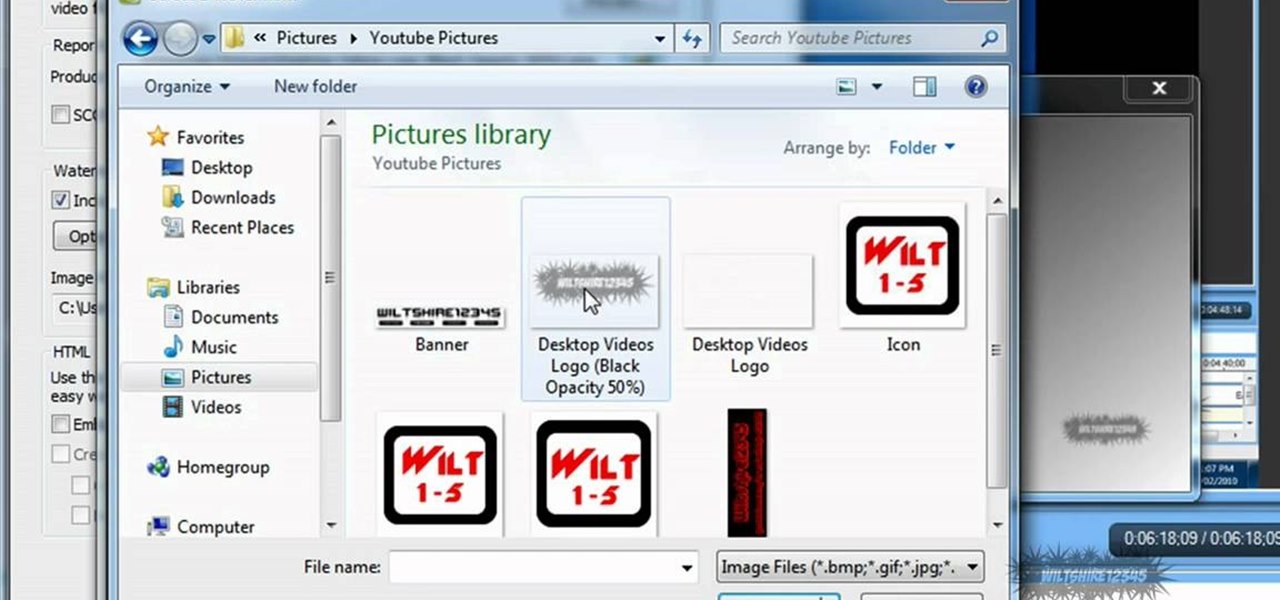
In this tutorial, we learn how to add watermark using Camtasia Studio 6. First, go to the "add" tab and then click "import media". Now, click "add in timeline" and edit it to how you like it. Next, go to the produce tab and click "produce video as". Click "add/edit reset" and choose which one you like, then click "edit" and "next" until you see the watermark tab. Now click "add watermark" and click "options" when you are done. Click the folder to find your watermark and choose how you want it...

Top-Windows-Tutorials is a great site dedicated to Windows tutorials for almost all things Windows. Whether you are a computer novice or an expert in Windows operating systems, you'll find useful information in these guides catering to your level of expertise. These user friendly and easy to follow free Windows tutorials will show you all that you can do with your Windows PC.

Did you know there is hidden data in your digital pictures? Well, there is, and that data might be a security risk to you. Think back at all of those pictures you're in and are connected with. I'm sure some of those you'd like to distance yourself from. And surely you wouldn't mind checking out the metadata in a few of those images. In this article, we'll be going over how to do just that.

West LA Seido Karate-do embeds its personal protection program into its on-going classes. Private instruction in this aspect of Seido can also be arranged with Kyoshi on an individual basis.

Wartex8 demonstrates how to use remote desktop in Windows XP. Remote Desktop is a useful utility that you can use to control another computer and its applications.The necessary steps that are adopted to activate remote desktop are:1) Right click on my computer icon (either the icon on the desktop or the one on the start menu list) and select properties, and a new dialog box called system properties will pop up on the window.2) In the System Properties, select the computer name tab and write d...

What management style is best for you? Each situation can call on a different style. Learn about each style and when to use them from a communications and public speaking expert in the free instructional video series.

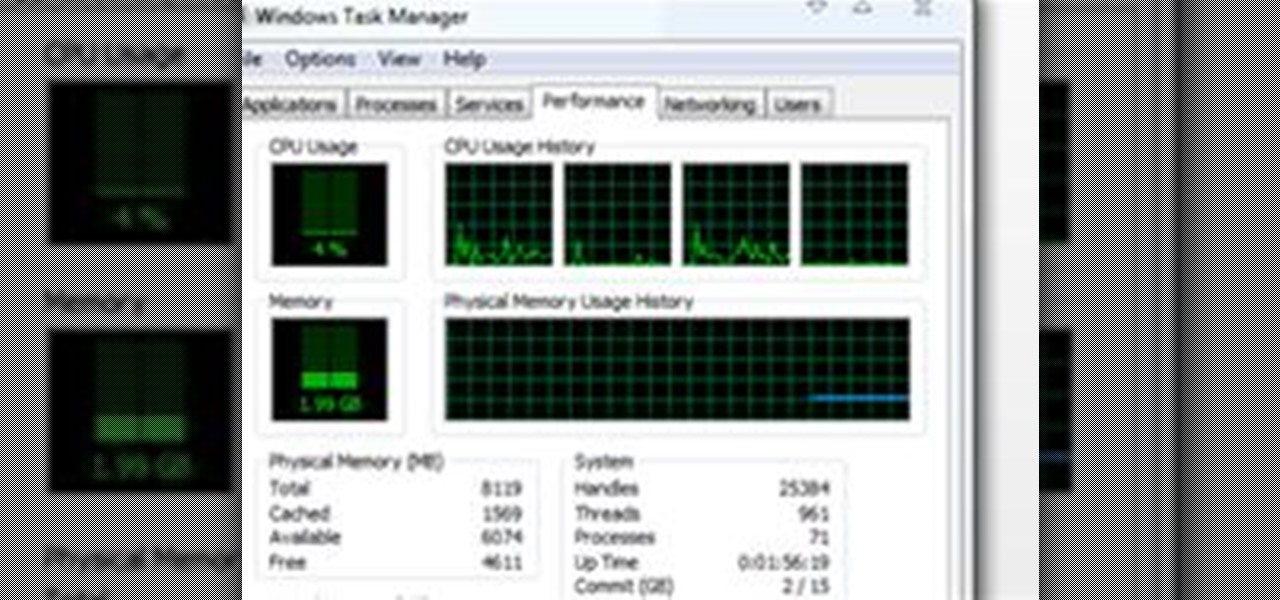
Introduction This is one of the things I am asked the most and there are so many different answers. It is hard to just tell you without know your computer's current speed or what type of hardware it has. So here I will talk about how to speed up a slow computer and how to keep your computer running fast.

Carmen Lynne shows us how use personal numbers in numerology in this series of videos. Part 1 of 16 - How to Understand numerology personal numbers.

Xeni visits the offices of the Electronic Frontier Foundation and speaks with Jake Appelbaum and Bill Paul, two of the authors of a security research paper that shows how your computer's memory can be tricked into revealing data you thought was safely encrypted, and out of the reach of others. Hack into encrypted computer data.

The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.

Ever since Microsoft sunset Windows Phone, they've been working with Android to tap into the growing mobile device market. The tech giant has uploaded over 80 apps to the Play Store for any Android user to download, but some features Samsung has hoarded for themselves.

If you've ever needed to prove you have remote access to a device, or simply want a way to convince someone their computer is haunted, SSH can be used to make a device begin to show signs of being possessed.

Whenever the name Magic Leap comes up, the talk inevitably seems to turn to the company's big-name backers and "unicorn-level" amounts of cash poured into the venture. And if it's not that, observers tend to focus on the company's market strategy and overall prospects.

A powered-off Windows 10 laptop can be compromised in less than three minutes. With just a few keystrokes, it's possible for a hacker to remove all antivirus software, create a backdoor, and capture webcam images and passwords, among other highly sensitive personal data.

Screen mirroring app iDisplay has arrived for Vuzix M300 Smart Glasses. With the app installed on the M300 and the companion software running on a Mac or Windows computer, users can mirror or extend the computer's desktop to the headset's display, which is connected to the computer via Wi-Fi or USB cable. The app does not yet appear on Vuzix's app store.

The world is full of vulnerable computers. As you learn how to interact with them, it will be both tempting and necessary to test out these newfound skills on a real target. To help you get to that goal, we have a deliberately vulnerable Raspberry Pi image designed for practicing and taking your hacking skills to the next level.

Before many games make it to the US-based iOS App Store, they get "soft launched" in a smaller country to get real-world testing for bugs. It's a pilot program, so to speak, as countries like Vietnam or the Philippines have far fewer iPhone users than the US, thus offer a more controlled environment for developers to get feedback and zero-in on issues that may occur in a game's early development phases.

With Apple's Yosemite build of Mac OS X came Continuity, a feature that has allowed us to connect our mobile devices to our computers, letting us access apps, send text messages, answer phone calls, and more while seamlessly switching from one device to the other.

While you can do a lot of things on your smartphone that were once only done on a computer, having a laptop is still necessary and critical for many tasks. Often times, the two devices work very well together.

There are tons of good reasons that you might want to use Android on your desktop. Perhaps your favorite game is only available on Android, or maybe you use a messaging service that doesn't have a Windows companion app.

I regularly use iTunes on my home laptop and my work desktop forty-five traffic minutes away. I'm ashamed to admit it, but until recently, I'd been saving my iTunes library on a USB and transferring it back and forth, over and over again, between the two computers.

Welcome back, my neophyte hackers! In today's hack, we're going to have a bit of Halloween fun. Have you ever had a boss who made you miserable with his micro-management and nagging? Maybe you thought he unfairly fired your friend/colleague? Well, now here's your chance to get a bit of revenge and keep him or her off your back!

For the most part, transferring files from your computer to your Nexus 7 (and vice versa) is a simple process. Just hook up your tablet to your computer with the USB cable and transfer. However, most of the time you'll need additional software on your computer to do this, and then, of course, you need the USB cable.

Most of the time, if you're actually using your computer, it won't just go to sleep on you. But when you're reading a long article or watching a video and don't move the mouse or use the keyboard for a while, the screen automatically dims or goes into sleep mode.

Thanks to Flutter, it's now possible to control the music on your computer simply by making a few hand gestures. The app is available for both Windows and Mac and uses your computer's webcam to monitor your hand movements. Through the use of a few simple hand movements, you can play, pause, forward or replay your music. Flutter works with iTunes, Spotify, Quicktime, MPlayerX and a few other programs.

Ever been halfway to work or school and suddenly remembered you forgot to log off your computer? A lot of people are constantly logged in to email and social media accounts, so if you have a mischievous roommate or sibling, this situation could be disastrous. That's where TweetMyPC comes in—it's a free Windows application that lets you send commands to your computer just by tweeting. Image by Twittermania

With how quickly technology evolves in this day and age, it's only natural that people replace their computers every couple years—even sooner. It seems that right when you get a new desktop, there's always a faster model with more features released the following week.

The iPod kids shows viewers how to covert movie files that are already on your computer into a format that will work with your iPhone or iPod Touch (2nd generation).

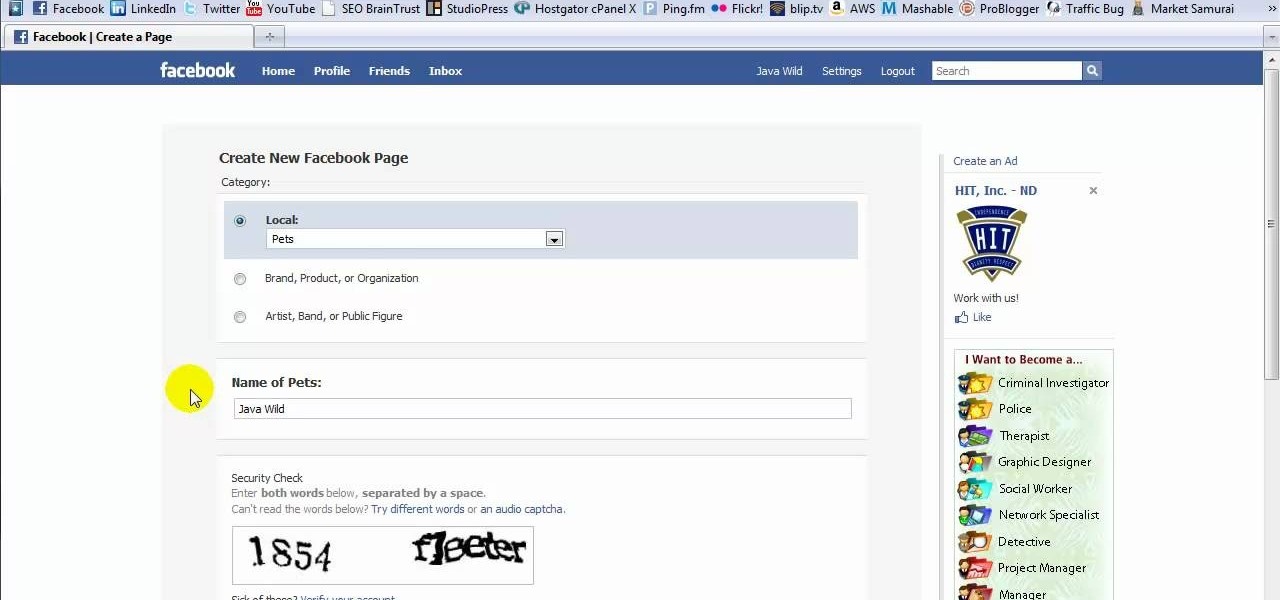
This tutorial is in response to mail to Facebook. Scott Wilde leads you through the process. You can start by creating a brand new profile page. In this case, Mr. Wilde created a profile page for his dog Java Wilde so he could have a fresh new page without having to alter his initial profile page. Fan pages are different than your base profile. Your base profile is not indexed, it is not public, it is private and limited to 5000 friends. A fan page is unlimited up to millions of fans and it c...