In this Outdoor Recreation video tutorial you will learn how to make fire in multiple ways. For this you will need either cigarette lighters or matches. There are also a variety of fire making kits available with fancy strikers to produce sparks and chemically coated paper strips or ropes that catch fire easily. Another method is a fire piston. Put the ‘O’ ring on the plunger and some charcoal powder on the tip of the plunger and bang it in. when you pull out the plunger, the charcoal will be...

The video producer in this instructional lighting video shows the contrast of how to produce a well lit scene. He first makes a cut out of a piece of foam board, then mounts it, placing it just so. He then position the lighting at an angle that appeals to the viewers and compliments the subject at hand. He also shows the difference between the angle of the camera and how the lighting is positioned. He takes us through the process of how to angle the camera and set up the lighting with minimal...

In this video tutorial, viewers learn how to make a dryer machine produce heat to dry clothes. Sometimes the dryer machine doesn't produce enough heat to dry clothes. To begin, users should clean the filter if it's full of dust. Check the discharge tube and make sure it is clean and doesn't have anything inside. Users should also open the back of the dryer machine and clean up all the excess dust located in the machine. The build up of dust clocks up the passage way and prevents the machine f...
This is a presentation of different types of immune responses in human body. There are two types of immune systems i.e., non specific and specific or adaptive immune system. Again, non specific immune system is sub- divided into barriers. It is the first line of defense. The second line of defense is the inflammatory response. They are phagocytes. These are all products of white blood cells. It is also called as leukocytes. Lymphocytes are another type of white blood cells which are carriers ...

Richpin demonstrates how to test an alternator with a standard multimeter. First make sure that the vehicle's battery is fully charged. Take the negative lead of the multimeter and put it on the negative post of the battery. Place the positive lead of the meter on the positive lead of the battery. Set the meter to DC voltage using the 20 scale and read the display to ensure the battery is fully charged. Next start up the vehicle and see what the alternator is producing. The display should now...

The term "Thermite" refers to the mixture of aluminum and ferric oxide used in this experiment. It is sold commercially and is used for such applications as railroad welding and incendiary bombs.

In this video, a doctor gives you great information on how to relieve shoulder, neck, and back pain from prolonged computer use. It's great advice for those of us who work at computers more than a few hours a day. The best way to improve tension is to fix your posture first, and make sure the screen is not too close to your eyes. Stop shoulder, neck and back tension from computer use.

In this tutorial, we learn how to allow only your computer to access your Wi-Fi while using Apple Airport. First, select the Apple Airport Express item on the base station chooser. Double click this and press Configure, then enter your password in the new window that pops up. Now, a new window will open, and you will need to click to "Access Control" tab on the top of the window. Next, click "add" and then select "Mac address" and enter in your MAC address and description. Once finished, clic...

.bat files can be quite dangerous to any machine. Creating and opening these files should be done at your own risk. Sending malicious .bat files over the internet is illegal. This video will show you how to make a virus that crashes your computer.

Remote desktop is a tool that can be used to access you computer from another device over a network. You can also connect to a remote desktop on Iphone or Ipod touch. Note that you will need EDGE and 3G for this to work. The files you need to connect are Mocha VNC Lite, and the desktop application Real VNC free edition 4.1. One is used on your computer and the other is used on your device. First launch you application store on your Iphone. Search for Mocha and open the Mocha VNC lite. Open th...

This video tutorial from SoldierKnowsBest presents how to install Snow Leopard operating system on your Mac computer.

Changing computers or switching to a different type of web browser? If you have been using Firefox for a while, you most likely have some good bookmarks saved. Check out this tutorial and learn how to export your bookmarks from your old browser and take them along with you, wherever you go.

Oh no! You've just accidentally deleted an important computer file! Have no fear. When you delete a file on your computer, it is not necessarily destroyed. This video will show you how to search for and restore your file before it is lost forever.

Changing the drive letter is necessary for reassigning hard drives. This straightforward tutorial breaks down the steps for performing this simple computer-housekeeping task.

Tired of being limited with your right-click options in Microsoft Windows? There's a program that could help you out, and it's called Right-Click Extender. Insert many different additional items to the right-click context menu.

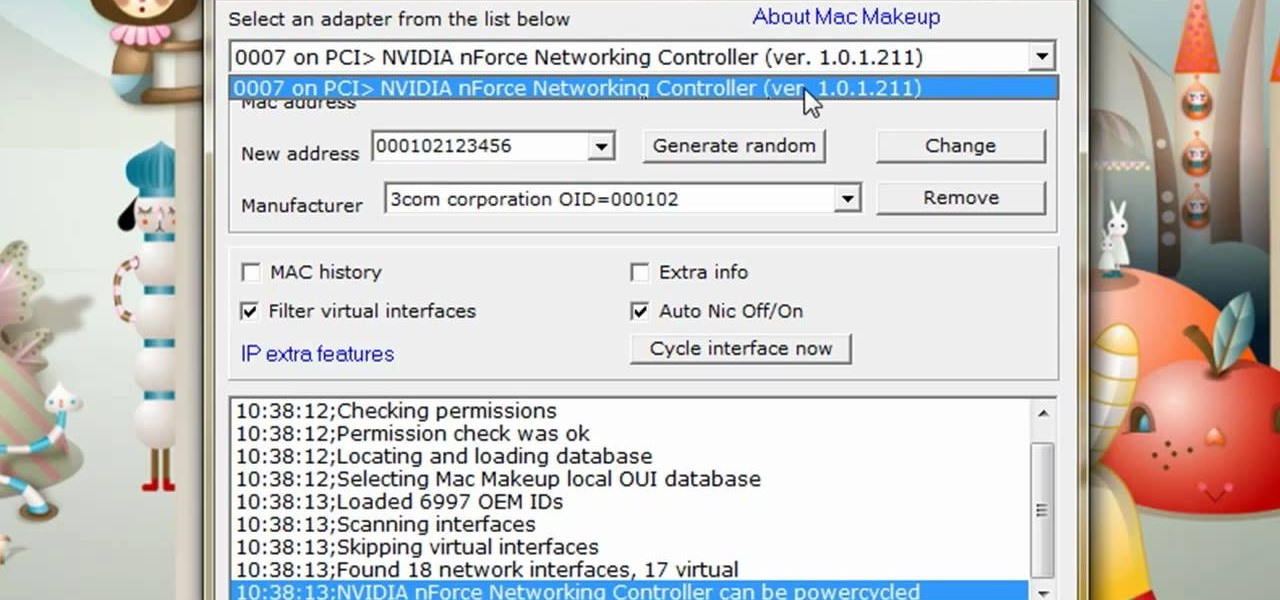
The video is about how to change the IP address. MAC address is the unique identifier a site of the most network adapters. MAC address is used to determine what IP address the computer will have and one way to change the IP address is by changing the MAC address. The method is only applicable for the windows systems and for the MAC systems you need to look at the link provided. In Windows in the start menu, type cmd in the run/search box, which will launch the command window. Type ipconfig/al...

Now you can find your IP address if you need it and you don't know it, it very easy. Or if you have problem with a person on the internet, now you can discover who that person is. You can find her/his IP address and after that you can find her/his real name. But after you find the IP that you were looking for, you have to check if the person who own this computer is in your network, because if you want to find his/her name, the program works only if the owner is on your network. So if you are...

This video tutorial is all about recovering the deleted files in Windows Vista. If you are using the Windows Vista and you have unknowingly deleted a file and emptied the recycle bin, then you can recover it. This can be done by using the Shadow Explorer. Shadow Explorer is a Vista program that accesses the Vista Volume Shadow Copy Service. In Vista, the shadow copy service is turned on by default. It creates backups of files on a regular basis. Shadow Explorer provides access to these backup...

New to Windows? No problem... here's a beginner's video tutorial that will teach you how to prevent cut, paste, copy, and delete on Windows files.

Digidesign has transitioned all of their plug-in software copy protection from floppy drive based key disks to copy protection authorizations that reside on the iLok technology provide by PACE. The following is some information about iLok technology.

Check out how to make a sweet cat bed out of an old computer monitor! Make a Cat Bed from a Computer Monitor.

If you use Google Chrome on your computer, you've undoubtedly saved a ton of passwords since the browser always prompts you to. But Samsung uses their own password service on their phones by default, so you'll have to change a setting if you want to use your Chrome passwords to log into apps and sites on your Galaxy.

While augmented reality industry continues to grow, analog board games are also making a comeback. So, why not join the two together?

The Windows 10 desktop and microphone can be livestreamed without using Remote Desktop Protocol (RDP) software and without opening any ports on the target computer. A hacker with low user privileges can monitor and exfiltrate a target's every move and private conversation in real time no matter where they are. Hackers are watching and listening, and there are few ways to protect yourself.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

With all the recent activity around augmented reality, the possibilities involving immersive computing and commerce are quickly becoming obvious, and digital payments giant PayPal has no plans to sit on the sidelines

Passwords stored in web browsers like Google Chrome and Mozilla Firefox are a gold mine for hackers. An attacker with backdoor access to a compromised computer can easily dump and decrypt data stored in web browsers. So, you'll want to think twice before hitting "Save" next time you enter a new password.

Intel Corp.'s augmented reality division could ship consumer-focused smartglasses before the end of the year, according to reports.

Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

Transparent display maker Lumus has reached a deal to license its augmented reality optical engine models to Quanta Computers for mass production of displays for consumer smartglasses.

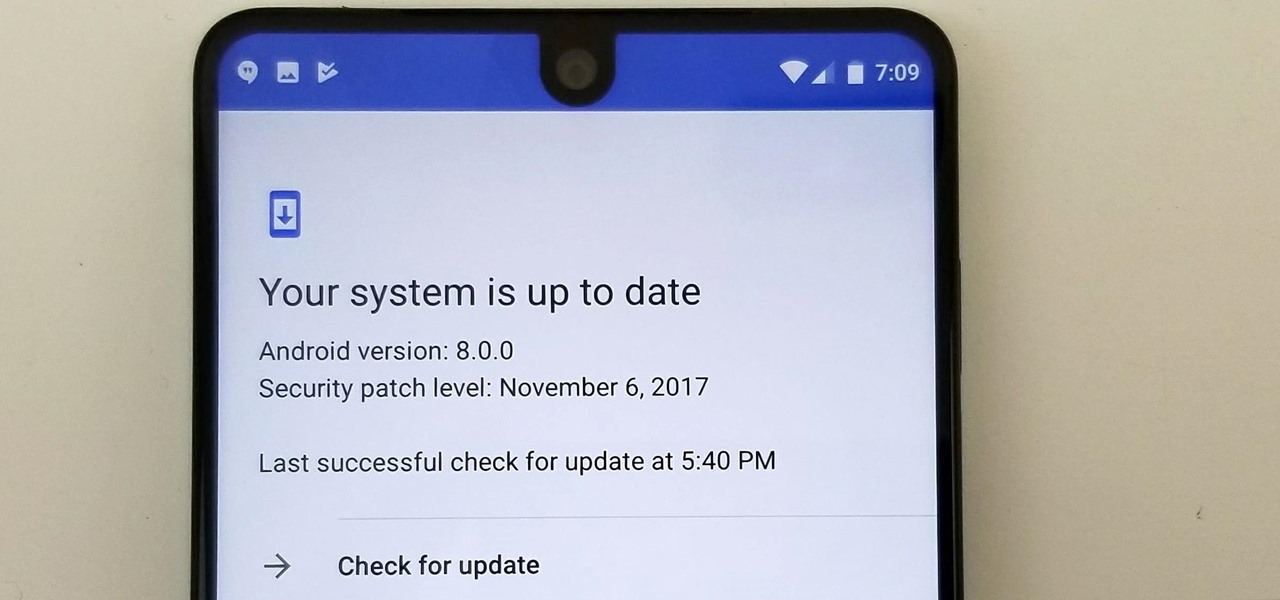
Essential just dropped the Oreo Beta Program for their flagship PH-1 phone. Users have been eagerly awaiting this update as the early Nougat builds of the PH-1 software have suffered from numerous performance issues and lag. The good news is that you can grab the Oreo update today with a few simple steps.

Keystroke injection attacks are popular because they exploit the trust computers have in human interface devices (HIDs). One of the most popular and easily accessible keystroke injection tools is the USB Rubber Ducky from Hack5, which has a huge range of uses beyond simple HID attacks. The USB Rubber Ducky can be used to attack any unlocked computer in seconds or to automate processes and save time.

Deep down inside, Kindle Fires are actually Android tablets — the only trouble is, Amazon has layered so much of a skin on top of it all that you can't normally use Android's main app store, the Google Play Store. The Amazon Appstore, which comes bundled with Kindle Fire devices, only has about 600,000 apps, so it would be great if you could access Google Play's library, which boasts 2.8 million.

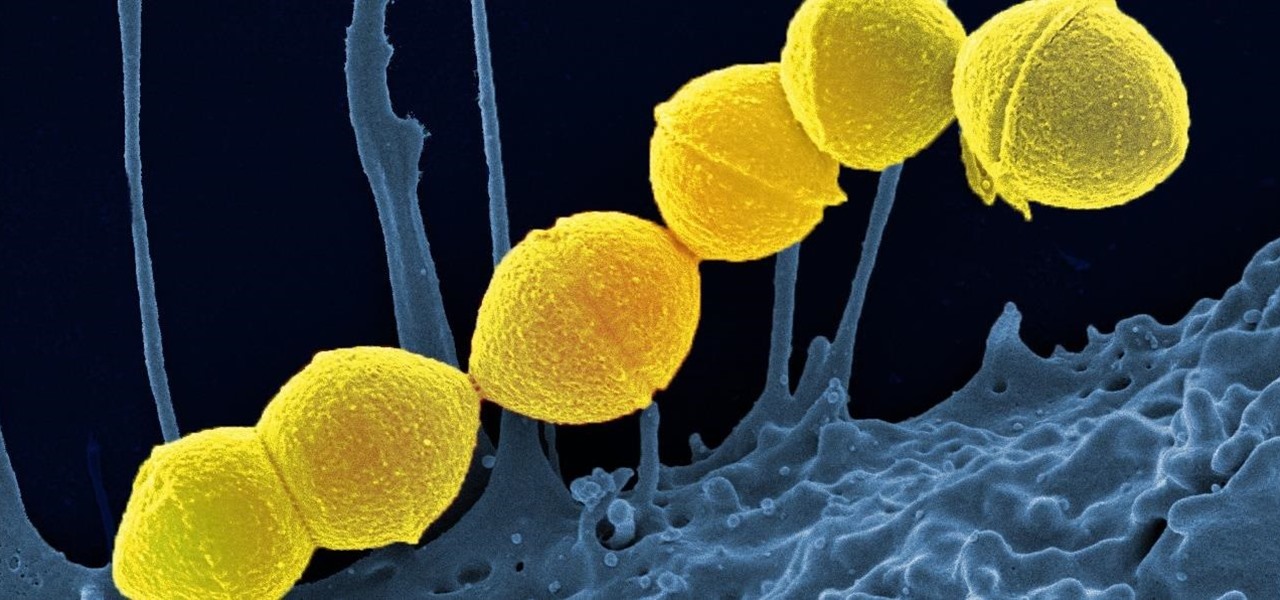
It's not the bacteria itself that takes lives and limbs during invasive flesh-eating bacteria infections. It's the toxins secreted by the group A Streptococcus bacteria invading the body that causes the most damage.

Lightform might just be the thing to have at your next party. The San Francisco-based company just created the first computer ever able to connect to a projector and instantly scan 3D scenes to mix reality with projected light.

User interfaces for computers have evolved over the years, from the introduction of the keyboard and mouse on the personal computer, to touchscreens on mobile devices, to natural voice recognition. However, the same cannot be said for robots or drones—until now.

The '90s were a great decade to be alive. Before the internet became a high-availability service, we were untethered from the bombardment of media present in today's culture. Children ran through the streets with levels of physical exertion beyond what's required to capture fictional creatures found in Pokémon GO. However, there were some video game consoles that kept kids indoors, such as the Game Boy, SNES, and more importantly—the first ever PlayStation.

Greetings to all geeks, hackers, nerds, and explorers of Null Byte. Welcome to my brand new tutorial, "Using BASH for Computer Forensics". This tutorial will give you a look at how the computer programming language, Bash, can be used to find out details on apple devices for later use.

YouTube, the popular video streaming website owned by Google, announced on October 21st that it will be launching a new subscription service titled "YouTube Red" for $9.99 a month. Under the membership, subscribers will be able to watch videos without ads. Yup, all videos—from music to trailers to gaming and everything in-between—completely ad-free. Additionally, individuals can save videos to watch offline on their mobile devices as well as play videos in the background.

The day has finally come, and after quite a bit of hype and buildup, Windows 10 is now officially available. The update itself is on a staged rollout, which means it will be slowly becoming available to users over the coming weeks and months, so don't panic if you haven't already received an update notification. Besides, you have until July 29th, 2016 to download your free copy of Windows 10 if you're eligible, so there's plenty of time to get your ducks in a row.