The Citrix Receiver is an app that allows you to securely access your desktop and business applications directly from your Droid Bionic smartphone. You will first need to make an account at the Citrix site, and from there you can decide what you want to have access to on your phone. On the Android app launcher, be sure to pick the Citrix Receiver app so that you can login with your Citrix account.

In this video, we learn how to do some easy hairstyle for school. To do an easy bun, take a hair tie and put it in the hair in a side twist bun. Let some of the hair stick out, then take bobby pins and stick them in the bun to secure it, then you're done! The next look requires you to take your bangs and braid them together. After this, pull the braid behind your head and secure it with a bobby pin. The next look requires you to braid a section on the side of your hair, then put it into a pon...

My Fat Rocket Hairstyling ideas demonstrates this party hairstyle for long hair. Divide the hair into a few section before beginning. Pull a curling iron through the hair strand in a downward twisting motion. Move the curler through the hair slowly so the hair curls up at the ends. Using the right motion, a hair straightener can also be used to create the curls. Some strands of hair may need to be processed more than once. Use hairspray to secure the look. For a more sophisticated look, after...
For this look, you need some hot rollers and some bobby pins. Using these two items, and some hair spray, you will be able to get a look similar to the one Miley Cyrus was wearing at the 2010 Oscars. She begins the style by putting rollers in all of her hair and allowing them to cook for about 15 minutes. After she removes the rollers, she sprays in some "invisible dry shampoo" in her hair. Next she teases the hair, and puts it in a pony tail in the back of her head. She takes a little stick ...
This video teaches you how to change your computer's account password using the DOS command prompt. The first step is to get to the command prompt, you can do this simply by clicking run in the start menu and typing "cmd." You next type "net user" which will show you all of the user accounts on the computer. Choose the one you would like to change the password for and type "net user (account name)." It will then ask you for a new password, you may type anything you like here keeping in mind t...

This video helps you create a faux hawk hair style. The only thing necessary to create this look are bobby pins, a comb, and lots of hair spray. By sectioning off parts of your hair and pinning it down you are able to create the illusion of a mohawk. While there is no verbal commentary in this video the captions provide great explanation for what is taking place in the video. She makes this hairdo look simple, easy, and effortless.

What are the names of basic picks? How do you use them? Check out this instructional con video that provides an overview of the basic pins used in lock picking. All picks can be put into two basic categories, raking picks and single pin picking picks. Learn the names of the various picks and how to use them with this tutorial video. Learn the basics and start lock picking like a pro!

When researching a person using open source intelligence, the goal is to find clues that tie information about a target into a bigger picture. Screen names are perfect for this because they are unique and link data together, as people often reuse them in accounts across the internet. With Sherlock, we can instantly hunt down social media accounts created with a unique screen name on many online platforms simultaneously.

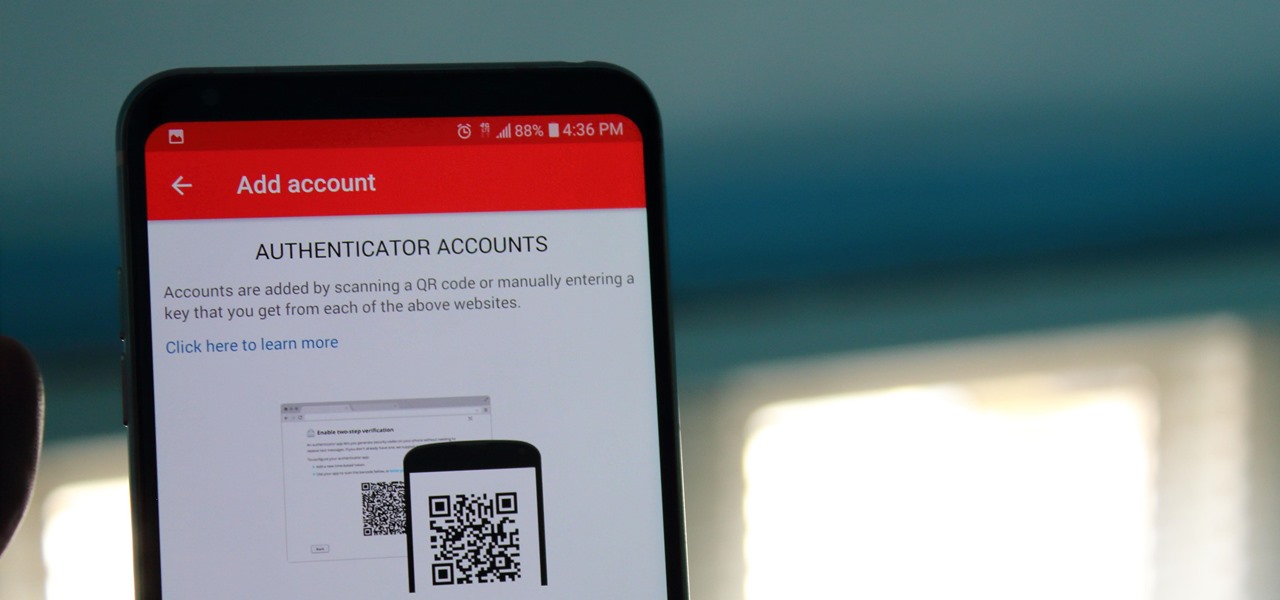
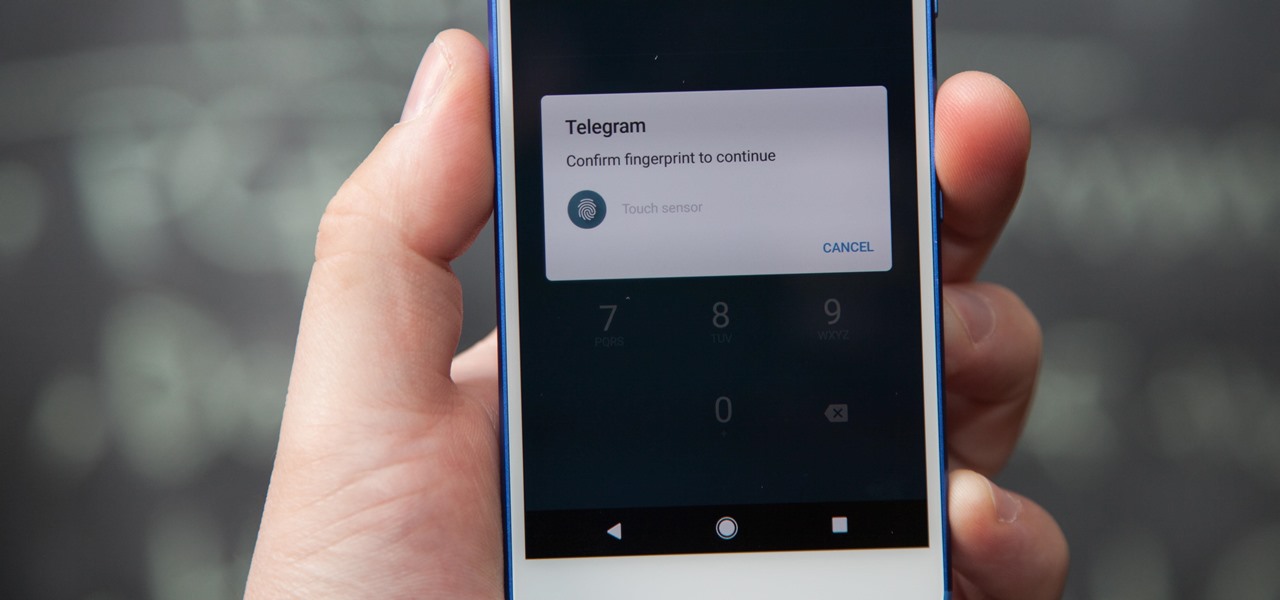
Many of our online accounts now come with an added two-factor authentication (2FA) functionality to help keep our data safe. This essentially means no one would be able to access the account until a specific set of requirements were met. It could be a combination of a password with a security key or even a passcode with some form of biometrics, like a fingerprint or face scan.

As the stigma of online dating fades and swiping potential suitors on your phone becomes the new norm, one very real issue that you may have to deal with is catfishing: the act of being deceived by a fictional online persona. Although dating apps do their best to weed out fake accounts, a few of them slip through the cracks and take advantage of innocent people just looking for a connection.

One of the main reasons Authy was able to top our list of the best two-factor authentications apps was its ability to transfer access to a new device. This feature ensures that whenever you get a new phone, you don't lose all your tokens. However, if the process is done incorrectly, you can leave your account vulnerable.

If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

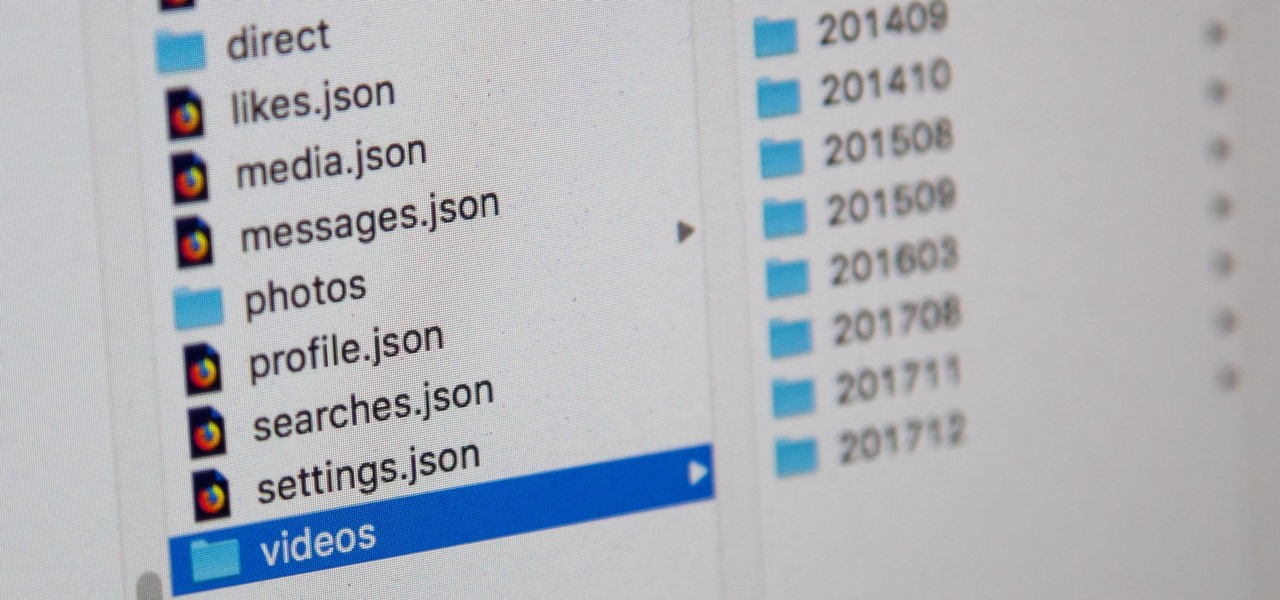
Facebook, parent company of Instagram, has allowed you to download photos and other account data for some time now, but the data request feature is also now available on Instagram to meet the GDPR data portability requirement in the EU — and it's available worldwide, not just in Europe.

Your Instagram bio could always be used to link to other websites or profiles or just to show off your witty personality. Now, you also have the ability to use this section to tag other Instagram accounts as well as add tappable hashtags. Whether you want to link out to your best friend, company, or the latest trend in your city — if it has a profile name or tag, it can be in your bio.

In this day and age, publishing content to one social media account just doesn't cut it. VSCO, Facebook, Twitter, Instagram ... you need to be active on all. And if you prefer editing and posting all of your photos on VSCO, you need a way to share those images with your other accounts.

If you're using Telegram for its "Secret Chats" feature, which provides end-to-end encryption for your messages, then I'd highly recommend locking down the app itself with a passcode, PIN, or password. While your phone itself may have a secure lock screen already, if that gets compromised, you'll at least have an extra layer of security on your important conversations.

If you want to find out the linear distance between your hotel and a landmark or restaurant you want to visit, Google Maps has a great feature that lets you quickly measure the distance between two or more points. It's perfect for getting an idea of how far places are in relation to each other, which can help you plan trips more efficiently.

The photo-centric Instagram app is a great way to share "evergreen" pictures and videos when compared to Snapchat and Facebook's new Messenger Day feature. But like all social media, keeping the account secure is an essential aspect, as it restricts unwanted viewers from seeing your content and can prevent unauthorized users from accessing your account. Instagram has several methods for locking down the account including a new two-factor authentication (2FA) mechanism.

Video: . This is a very simple way to set up a booby trap inside your house for your friends and family, It can get messy so prank at your own risk.

The first time a friend or family member asks if they can borrow your phone or tablet, you probably just hand it over without a second thought. But the second, third, and fourth times? Now it's starting to become a habit, and something probably needs to be done about it.

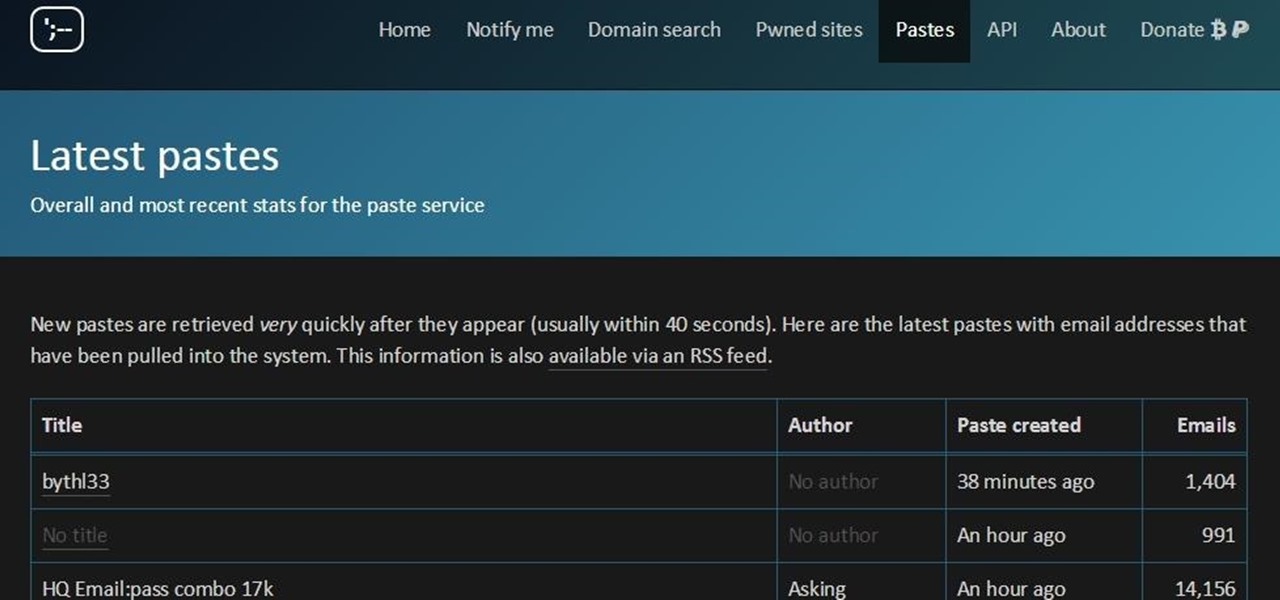
You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series which will help you to find hacked accounts. Some of you must already know about this, but this post is intended for the new learners. This also serves as an example of my learning how a good service can be used in other w...

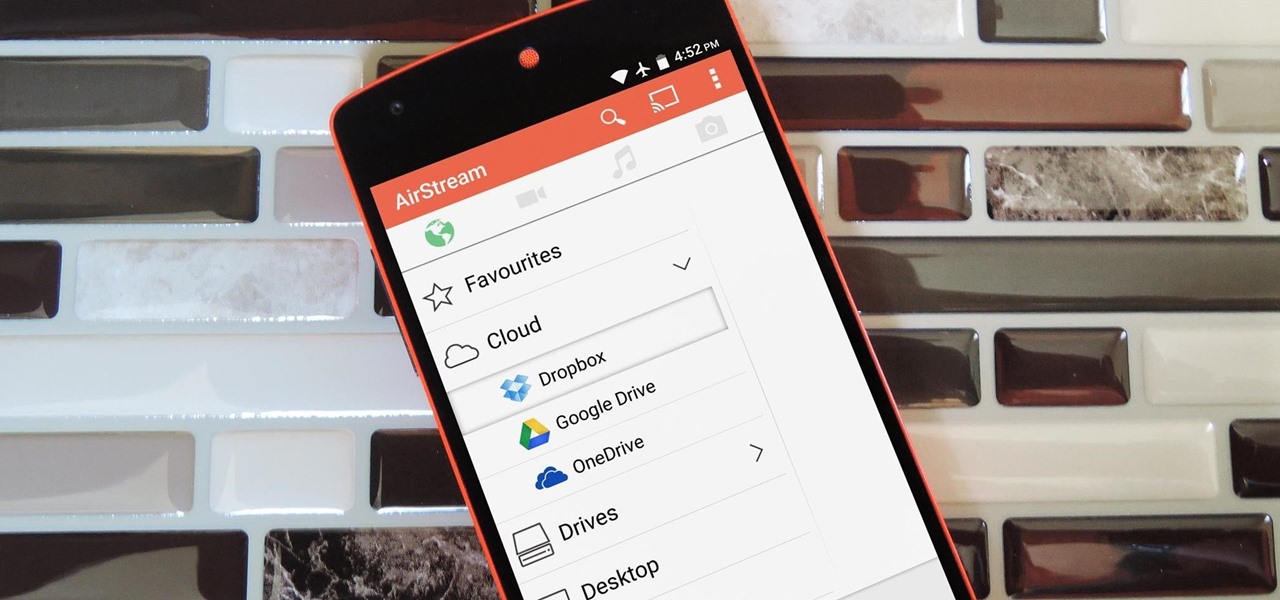
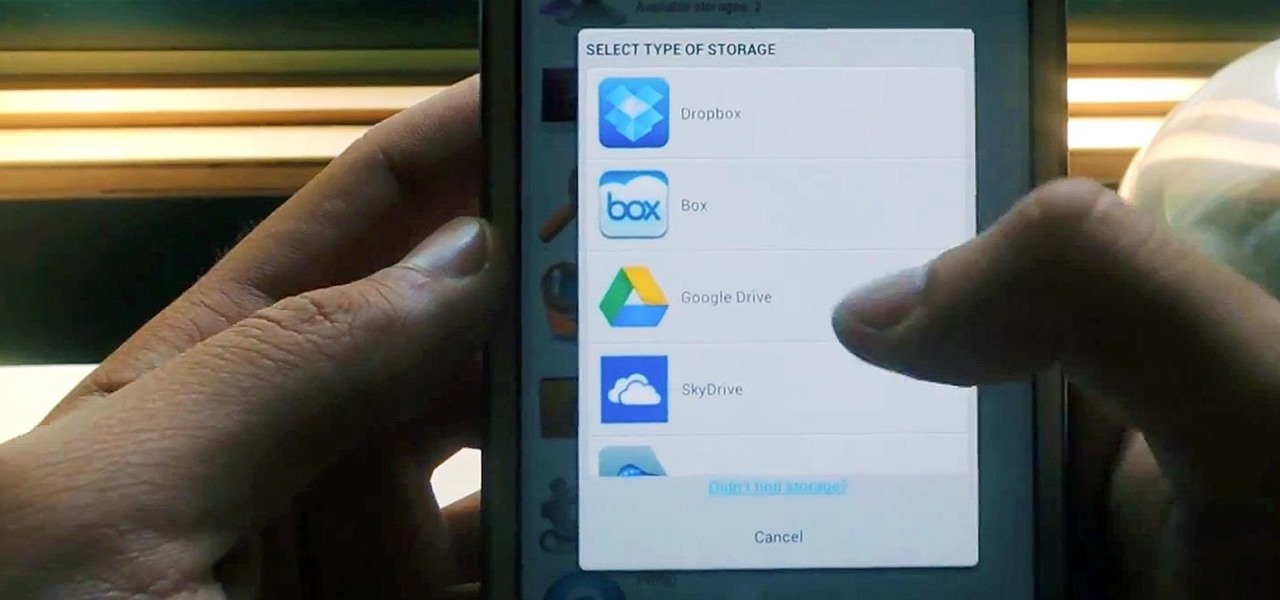
Smartphones generally have limited storage, but counter this issue with an always-on internet connection. This led to the proliferation of cloud storage services, which allow us to store and access our large media libraries remotely.

With troves of sensitive information, like receipts and password reminders, hiding in your email, your inbox can become a sort of Holy Grail for hackers—or anyone with your password. Although my crazy ex-girlfriend had no hacking experience, using my email login, she was able to find a lot of account information with just a general search for "password" in my inbox.

Yes, "Safer Internet Day" is a real thing, and it's actually been around for 12 years. This year, Google again will be commemorating the event by giving away a 2-gigabyte storage bump for their Google Drive cloud service if you simply run through a security checkup.

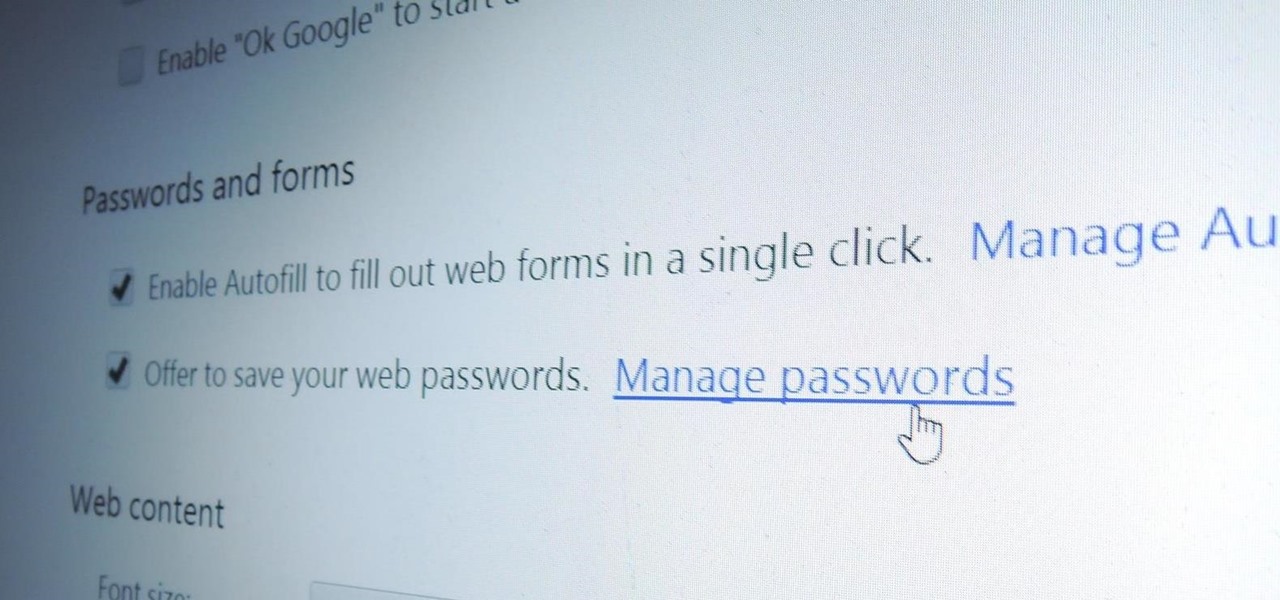
Chrome, Firefox, and Safari all provide built-in features that allow you to save your username and password for your favorite sites, making the process for entering your credentials a breeze when you revisit them.

Snapchat is like that very attractive girl at the bar that has one too many shots and ends up slobbering on the bouncer as she gets led out. Of course she can still recover since she is hot, but you only get so many chances before you just become a complete failure. And that's where Snapchat has been treading these past few weeks.

Cloud storage looks pretty good compared to the heavy restrictions that hard drives and other types of external memory carry. The cloud is not only limitless in what it can hold, but it can also easily be accessed from any device that has Internet—your smartphone, work computer, personal laptop, tablet, and more. While accessing a specific cloud storage system like Dropbox or Google Drive may be easy on your Samsung Galaxy Note 2, managing all of them individually can not only get confusing, ...

There isn't as much use for old-school four-function calculators anymore since we all have them on our cell phones now. If you've still got one lying around, you can hack it to play recorded sounds, use it to make a metal detector, or turn it into a custom name plate that says anything you want...

Dropbox announced Tuesday that a recent security breach compromised a list that included the email addresses of certain Dropbox users. To avoid future complications, the service announced that it would be implementing two-factor authentication, and even more useful, a security page that lets you monitor all activity on your account. In light of this and other recent web security threats, you might also want to know that services like Gmail, Facebook, and Yahoo! Mail have similar pages where y...

Having a secure password is essential in today's interconnected world. Hackers are just around the corner, and if you have an easy to guess or hack password that you use for all of your accounts, someone can login to all of your websites very easily. Look at this guide on how to create a strong password by following the right password rules so that your accounts stay secure.

Can't get enough Facebook? Take your "friends" status updates with you wherever you go by syncing your Facebook account with your Android smart phone. Having access to Facebook on your cell phone will keep you in touch, and come in handy when you need to look up a phone number or email address.

Want more gold in the game Mousehunt? Of course you do! And this technique shows you how to get it without having to resort to a hacking program like Cheat Engine or Charles - intead, you can create a different account and then use that to send gold to your main account!

This bohemian updo looks really elaborate, and seems painstaking to attempt, but it's actually super simple. Composed of several braids wrapped around your head and then pinned up, it only takes a few minutes to achieve and is party perfect.

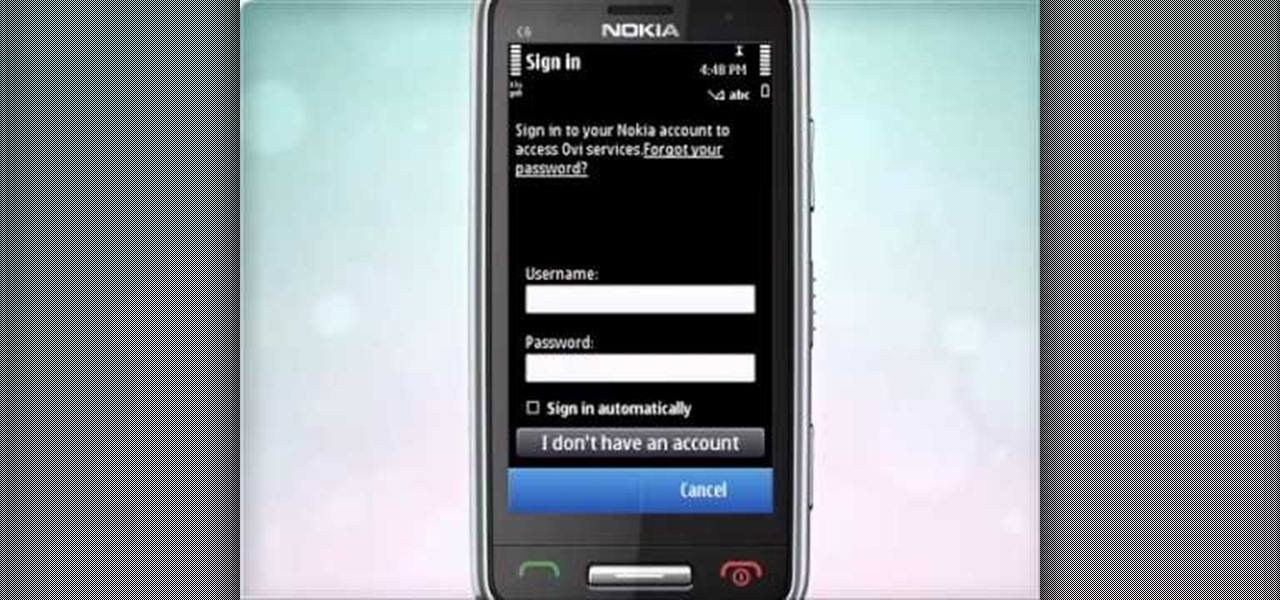
Learn how to access Nokia's Ovi services by creating a Nokia account. It's easy and this clip will teach you everything you need to know. For all of the details, including complete, step-by-step instructions, watch this brief, official C6-01 owner's guide from the folks at Nokia!

Learn how to set up your email account and how to add the E-mail widget to the home screen.It's an easy process. And this clip will teach you everything you need to know. For all of the details, including complete, step-by-step instructions, watch this brief, official N97 owner's guide from the folks at Nokia!

Want to create a new Nokia account on your N97? It couldn't be easier. This clip will teach you everything you need to know. For all of the details, including complete, step-by-step instructions, watch this brief, official N97 owner's guide from the folks at Nokia!

Learn how to set up your email account in the device. The C5 is the first offering in Nokia's new "C" series of mobile phones. It runs on Nokia's Symbian OS and features a 2.2-inch screen and 3.2-megapixel camera. Want more? Search WonderHowTo's sizable collection of C5 video tutorials.

In this clip, we learn how to use the Nokia C5's email wizard to set up a new email account. The C5 is the first offering in Nokia's new "C" series of mobile phones. It runs on Nokia's Symbian OS and features a 2.2-inch screen and 3.2-megapixel camera. Want more? Search WonderHowTo's sizable collection of C5 video tutorials.

You may be just recovering from a hectic - and binge-filled - holiday season, but prom season is just around the corner. Make sure you look like the belle of the ball by creating this simple and romantic hairstyle.

A zipper may look intimidating, but it's really not. This tutorial shows you an easy and quick way to sew a zipper. You will need a zipper, straight pins, matching thread, scissors, your sewing project and a special zipper foot for your sewing machine.