Highlights add depth and interest to a hair color. Get that beachy, sun-kissed look and change up your style by adding some well placed highlights in your hair. You’ll save time and money by buying a kit and doing it yourself.

If you can't get out into the garden, or you want to get the kids involved on a wet day, why not sprout some seeds?

In this video series, our expert will teach you how to make homemade christmas gift baskets for any occasion. Get step-by-step instructions for picking the best basket, packaging material and gifts for a gift basket. Learn how to add theme items, pampering spa gifts and even food to your gift basket, and get tips for wrapping up a gift basket with cellophane and ribbons.

In this fly tying video series, learn how to tie the Woolly Bugger fly from expert fly tying expert Jeff Wilkins. Jeff will tell you what materials are needed to tie a Woolly Bugger, and he will demonstrate how to lay the base a Woolly Bugger, how to tie the tail of a Woolly Bugger, how to wrap the body of a Woolly Bugger, and how to tie the hackle and rib of a Woolly Bugger.

With this series of card trick video clips, our expert magician Malik Haddadi wraps up his lessons for using the Svengali deck. By now you know enough about these trick cards to go public with your new set of skills.

In this fly tying video series, get free fly tying instructions for tying a Parachute Adams dry fly from expert fly fisherman Jeff Wilkins. Jeff will teach you what fly tying materials you will need to tie the Parachute Adams and will give you a list of the materials you will need. He will show all the steps needed to make a Parachute Adams fly including: fly tying the base and tail of a Parachute Adams dry fly, fly tying the wing, fly tying the body, how to tie in the hackle, and how to wrap...

If you've ever gotten super glue stuck to your fingers, you know what a pain it can be to get it off again! Don't worry - there's a simple household item you probably already stock that can take care of your super glue super mess!

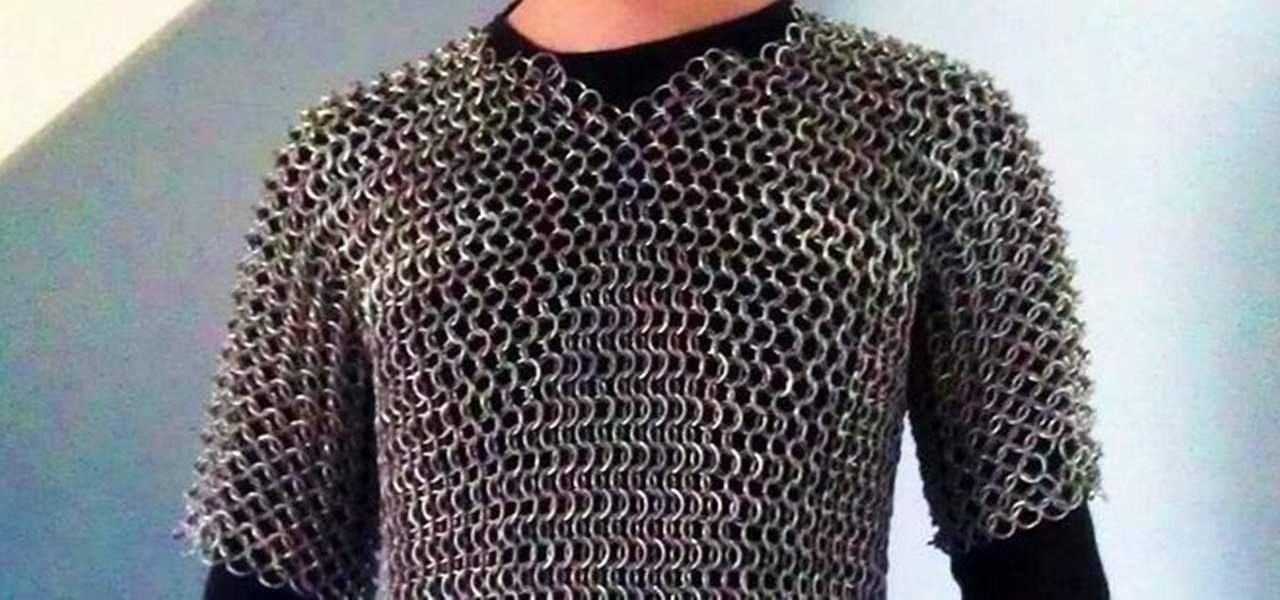
This article is a guide for making Chainmail Armor from start (simple wire) to finish (a finished chainmail shirt). We will be using the European 4 in 1 weave, as this is the most common weave. This is the weave that you usually see in movies. There are several sections to this guide: Materials, Making the Rings, Weaving the Rings, and Making the shirt.

Watch how to wrap a woman's head in a turban in doubletime. You won't ever see anything else like it! (the video plays at double speed.)

Apple's augmented reality teases just keep on coming from the halls of its Cupertino labs. The latest comes in the form of an invitation to Apple's next public-facing event.

Still listening to music and podcasts on your laptop or phone speakers? Mute that right now and switch to a powerful speaker that sounds incredible — which also happens to be on sale for less than fifty bucks. Right now, you can get the Motorola Sonic Sub 530 Wireless Bluetooth Speaker for just $49.95 — that's a 16% discount off the regular price of $59.

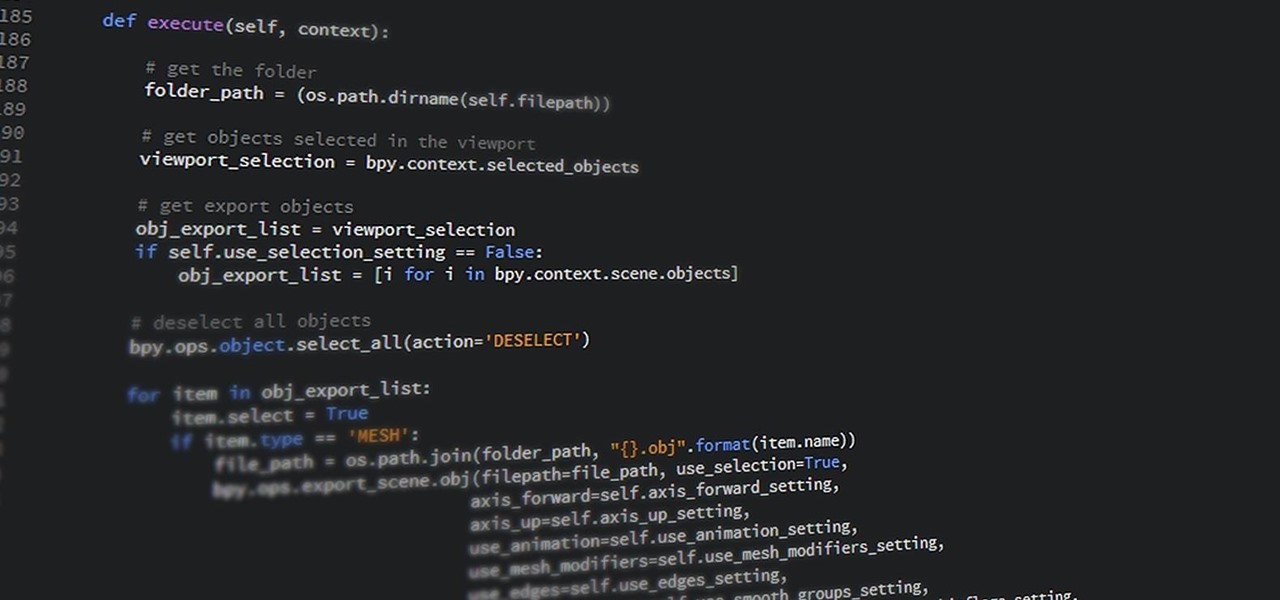
If you have information technology or computer science aspirations — even white hat hacking — then Python is a programming language you absolutely have to be familiar with. According to a recent survey of industry experts, Python is the fastest-growing language in the developer field. It's also one of the most sought-after skill sets among employers and is responsible for some of the best hacking tools.

3D printers allow hackers and makers alike to create something from nothing. They're an incredible technology that lets you build protective cases and covers for gear such as a wardriving phone and Raspberry Pi-Hole. 3D printers can even help you out in a bind when something breaks, and it's impossible to get the part, since you can just print one out yourself.

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

OnePlus phones are easy to root, but that also means they're easy to brick if you get trigger happy with your superuser privileges. If you find yourself in this situation, you'll quickly realize the OnePlus firmware download page doesn't provide files you can flash in Fastboot mode.

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

Hacking web applications can sometimes be challenging due to the sheer amount of moving parts they possess. At the core of these apps are HTTP requests and parameters, but these things are often concealed from the user, due to security reasons, convenience, or both. However, a tool called Arjun can be used to discover hidden HTTP parameters in web apps.

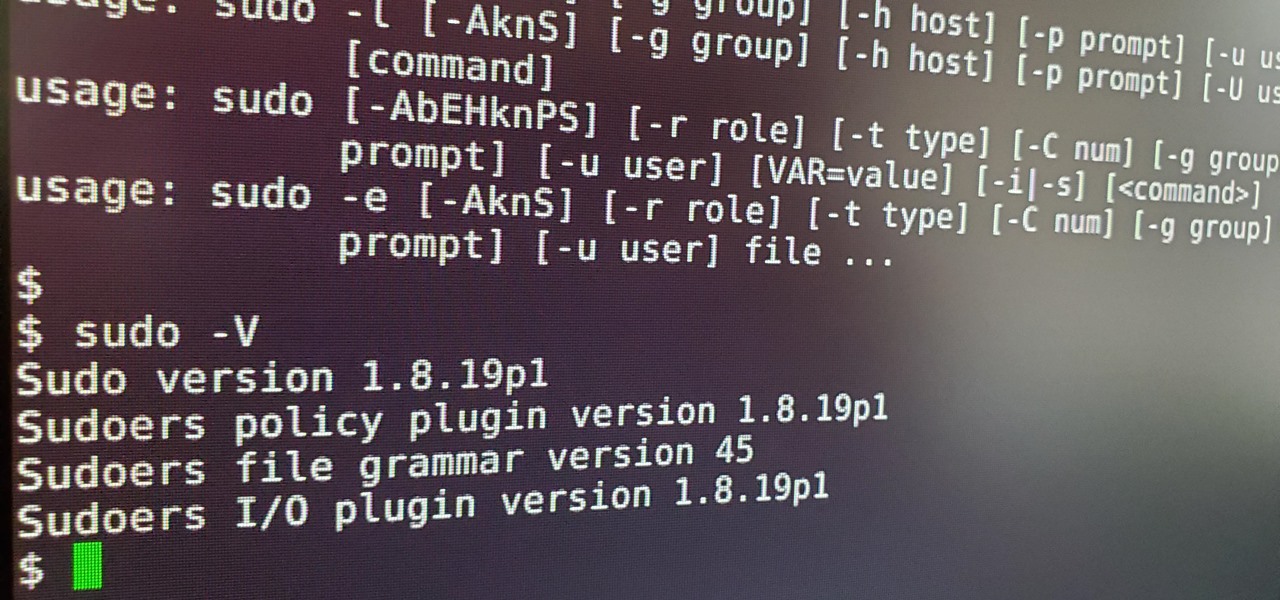
Anyone who has used Linux long enough is familiar with sudo. Short for superuser do (or substitute user do, depending on who you ask), it allows users to run commands as either root or another user on the system. From a hacker's point of view, sudo is often all that stands between them and root access. We'll be exploring an older vulnerability in sudo that allows a user to run commands as root.

You can block artists no matter where you are in Spotify's mobile app for Android or iOS, but it's not as easy when you want to hide songs from playing. Disliking tracks is possible here and there, but not everywhere, and that's a serious problem if you keep hearing songs you hate.

Password cracking is a specialty of some hackers, and it's often thought that raw computing power trumps everything else. That is true in some cases, but sometimes it's more about the wordlist. Making a custom, targeted wordlist can cut down cracking time considerably, and Wordlister can help with that.

Privilege escalation is one of the essential skills a hacker can have and often separates the newbies from the pros. With a continually changing landscape and a plethora of exploits out there, it can be a problematic aspect of any attack. Luckily, some tools can help expedite the process. Linux Exploit Suggester is just one of many to help you get root.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

It looks like Pokémon GO players may get a surprise gift from the game's developer, Niantic, this holiday season.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

We love our set of Apple AirPods. The battery could last a little longer, but overall, there's only one gripe we really have: the dirt that builds up inside the case. Whether you stick it in your pocket, a backpack, or your purse, the inside of the case's lid and main base will get dirty in a week, give or take. But there's a way to stop that from happening.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

Semi-untethered jailbreaks are here to stay, as evidenced by iOS 11's Electra method, Chimera for iOS 12, and even the new bootrom-based Checkra1n tool for iOS 13. While not as convenient as fully untethered, re-enabling a semi-untethered jailbreak is still pretty easy once you get used to the steps involved.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

One of the best ways to dig into a website and look for vulnerabilities is by using a proxy. By routing traffic through a proxy like Burp Suite, you can discover hidden flaws quickly, but sometimes it's a pain to turn it on and off manually. Luckily, there is a browser add-on called FoxyProxy that automates this process with a single click of a button.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

A universal dark theme has long been one of the most sought-after features we've been urging Apple to introduce for iOS. While this wish went unfulfilled with iOS 12, there's renewed hope that it'll finally touch down with iOS 13's arrival. The jailbreak community, however, has had this functionality available for quite some time, and you can too if you're running the right iOS version.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

Dark mode support has steadily made its way to mainstream acceptance, with big-name apps like YouTube, Reddit, and Twitter adopting the feature to satisfy user demands. In this regard, Facebook is lagging, yet to offer the sought-after feature for easier viewing in low-light conditions. If your iPhone is jailbroken, however, you don't have to suffer like everyone else.

Things that are supposed to make life easier for developers and users are often easy targets for exploitation by hackers. Like many situations in the tech world, there is usually a trade-off between convenience and security. One such trade-off is found in a system known as Distributed Ruby, which can be compromised easily with Metasploit.