Yelp reviews are great for getting a feel for how a business operates, but they can't always be trusted, and they don't always get to the point fast enough. That's where "Tips" come in, and you can view and make them whether you're on an iPhone or Android phone.
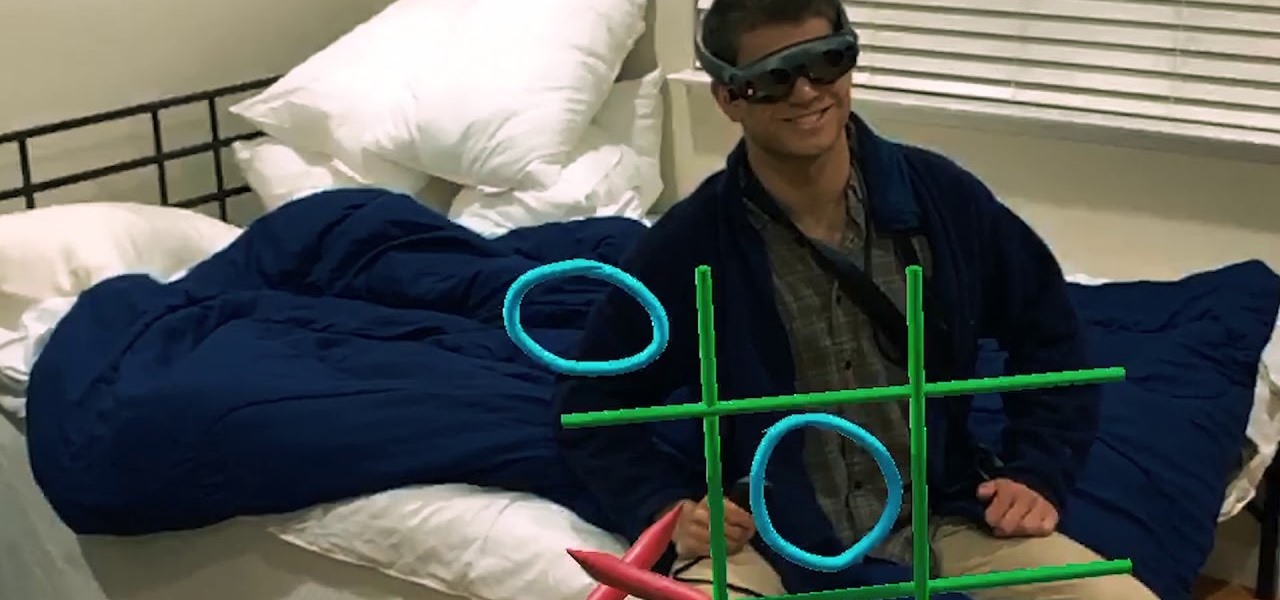
While painting in augmented reality is not a groundbreaking pursuit, the ability for Magic Leap One, iPhone and iPad, and Android users to collaborate remotely on virtual artwork would be.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Ten days after Magic Leap declared that it had selected the winners of its Independent Creators Program, the company has officially released an almost full list of grant recipients.

A relay is an electrical component that works like a light switch, where it's turned on or off with an electrical signal. By connecting a relay to a Wi-Fi connected microcontroller like an ESP8266, you can build a connected switch that can be controlled from the web browser of any device connected to the same Wi-Fi network — all for just a couple of dollars.

Already a powerhouse for its graphic design tools, Adobe is making a run at the 3D content creation realm dominated by Unity and Epic Games by acquiring software maker Allegorithmic.

Many online users worry about their accounts being breached by some master hacker, but the more likely scenario is falling victim to a bot written to use leaked passwords in data breaches from companies like LinkedIn, MySpace, and Tumblr. For instance, a tool called H8mail can search through over 1 billion leaked credentials to discover passwords that might still be in use today.

Ingress, the godfather of location based-AR games developed by Pokémon GO creator Niantic Labs, is getting a new lease on life via Ingress Prime, a reboot of the game built on the Niantic Real World Platform.

The most common Wi-Fi jamming attacks leverage deauthentication and disassociation packets to attack networks. This allows a low-cost ESP8266-based device programmed in Arduino to detect and classify Wi-Fi denial-of-service attacks by lighting a different color LED for each type of packet. The pattern of these colors can also allow us to fingerprint the tool being used to attack the network.

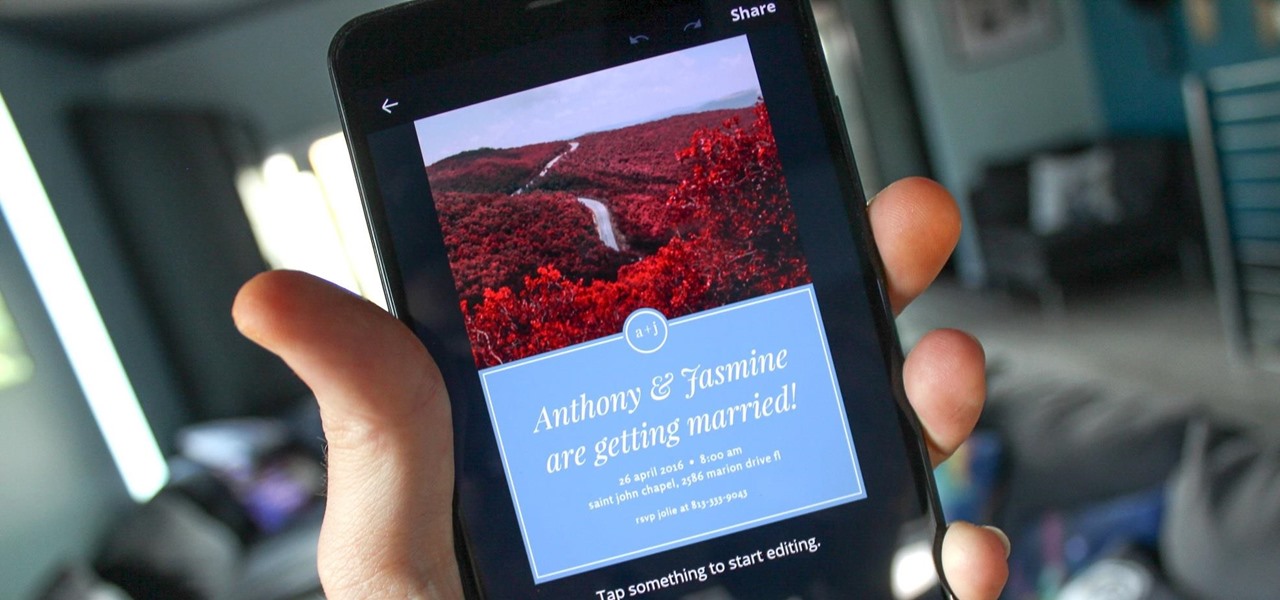
You can never replace the skills and expertise of a professional graphic designer, but Canva comes pretty damn close. It's ridiculously easy to use the drag-and-drop design tool for both professionals and people like me who don't have the need (or knowledge required) to use more advanced graphic design software.

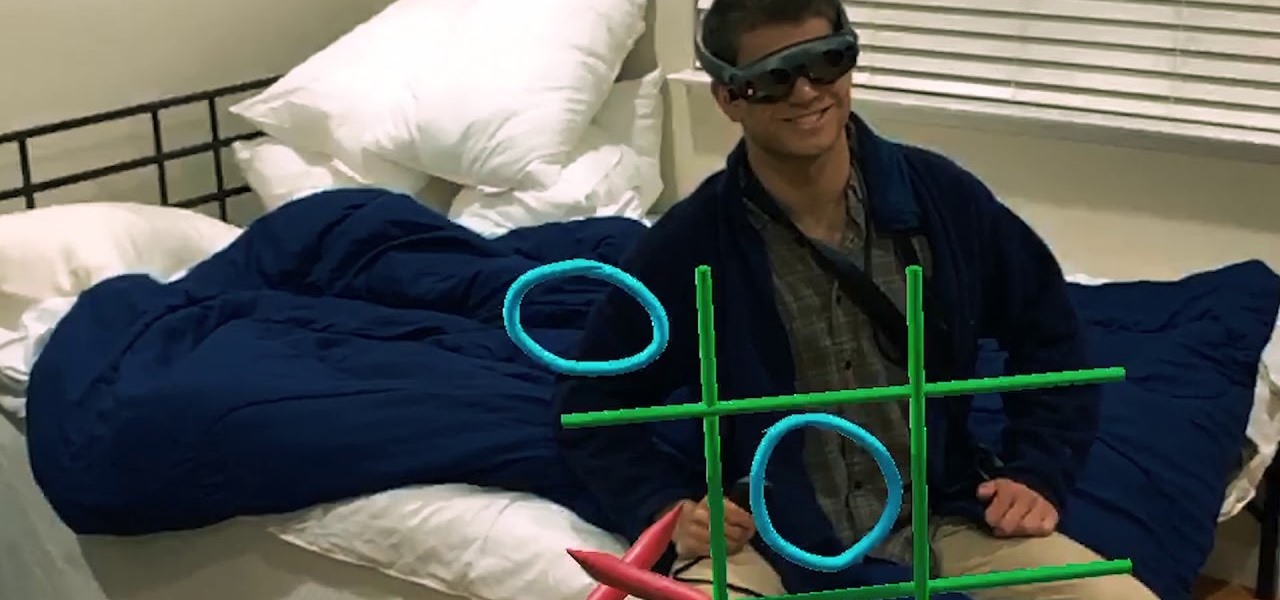
Luxury automaker Mercedes-Benz has joined the growing list of automakers adopting augmented reality to provide an assist to its manufacturing operations, in this case, via the Microsoft HoloLens.

Attention all Redditors: Between June 14 and June 18, Reddit experienced a data breach. The popular website claims it discovered the breach on June 19 and has since made the necessary moves to contain and eliminate the threat. Unfortunately, there isn't much they can do about the data was that accessed and stolen — your user data.

Using the ARKit 2.0 announcement as its springboard, software maker Adobe is looking leap up to the level of Unity Technologies and Epic Games, the companies making the go-to tools for creating augmented reality experiences.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.

If you're looking for a new Reddit client on your iPhone, look no further than Apollo. Launched with iOS in mind, Apollo is a free app that offers an exceptional Reddit experience, but some of its excellent features — as well as some necessary ones — are hidden behind its "Pro" paywall. Are these extras worth your money?

The price tag for the Microsoft HoloLens might be out of range for the average consumer's budget, but for enterprises, like BAE Systems, adopting the AR headset is yielding a return on the investment. And for those with even slimmer wallets, Best Buy just made the Lenovo Mirage, part of the Star Wars: Jedi Challenges package, more affordable.

Upon Google's release of ARCore in February, the platform wasn't only playing catch-up with Apple and ARKit in terms of downloads, but it also lagged in capabilities, as Apple already had vertical surface recognition and image recognition on the way with ARKit 1.5 for a March release.

If it had come out just a week earlier, around April 1, no one would have believed it. But it's true, Leap Motion has developed its own prototype augmented reality headset, and it looks pretty wild.

All those early prototype images Magic Leap is so fond of showing off are great, but they rank a far second when compared to a new set of images just revealed by Microsoft in relation to the HoloLens.

After more than a year and a half of silence, the rumors have morphed into reality: Microsoft has finally released an update for the HoloLens. And with that update comes a collection of new features that hint at big plans for the HoloLens this year.

The Galaxy S9's new wallpapers look fantastic, but you don't need to buy one to know that. Whether you have an iPhone X or a Pixel 2, Samsung's updated wallpaper library is yours for the taking, thanks to an S9 system dump released today.

In any business, there are a number of questions companies must answer in order to get customers to buy a product or service. The same holds true for companies selling augmented reality headsets.

The cup of augmented reality options for Winter Olympics fandom runneth over, with Google pouring a pack of AR Stickers into the mix.

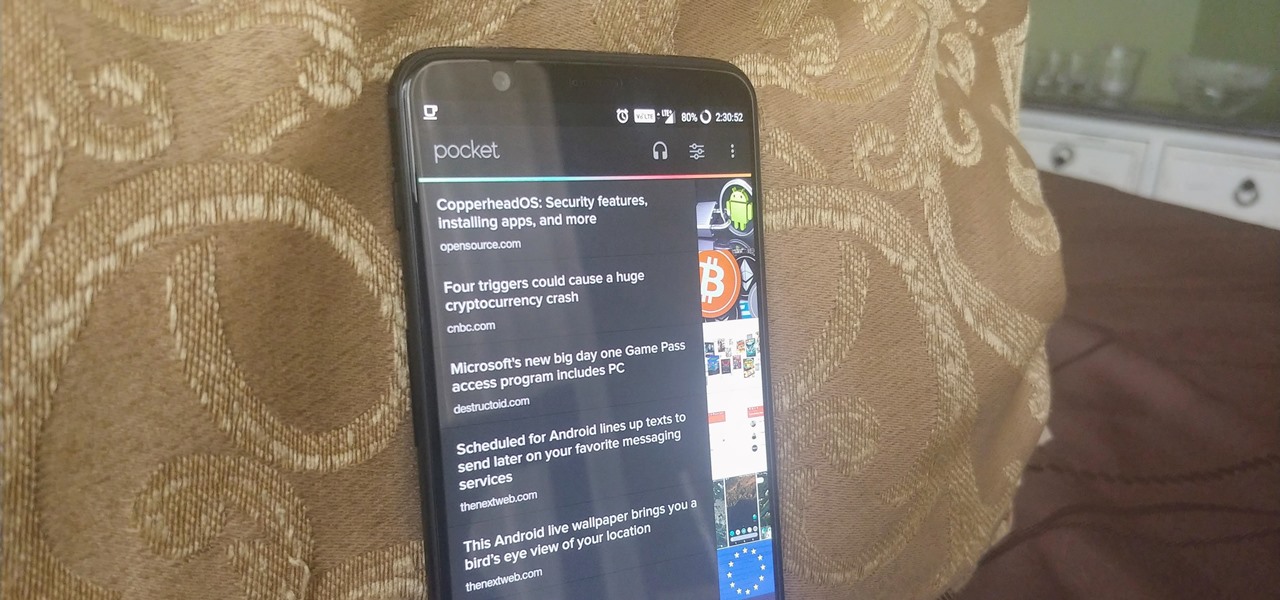
Starting your morning right is an essential first step to a productive day. Whether you're running late, rushing to catch up on the day's news, or lagging behind with early emails, little hiccups like these can have a trickle-down effect and ultimately ruin your day. Like with many problems, though, your smartphone can help.

Snapchat is a wonderful app that allows users to "talk with pictures." You can send other users pictures of what you have going on in your day-to-day life, and they can respond with what's happening in their own. It's a seamless way to have a conversation with someone using visuals — sometimes even faster than you would be able to with words.

The Sony Xperia XZ Premium brought 4K HDR to a Sony flagship along with some competitive internals, while the Xz1 brought some powerful specs in a more midrange, traditional form factor. While it only makes sense to be excited about what's coming next, Sony has yet to show us the XZ2. For now, we need to stick to the rumor mill. Thankfully, the rumor mill is a fun place to be.

Just as we published our rumor roundup for the HTC U11 Plus, the internet happened: A Facebook video revealed the flagship HTC U11 Plus and the midrange HTC U Life in all their glory. The video was in German and has since been taken down, but according to a translation, it revealed exactly what we should be expecting see at HTC event November 2.

You can bet Thor costumes will be prominent among the superheroes seen this Oct. 31. Since the summer, there has been no shortage of coverage for Thor: Ragnarok, and the timing of its November release couldn't be better as a tie-in with the cosplaying holiday known as Halloween. This year, the success of pulling off the Thor costume will rely on how well your new Thor helmet looks, which as it happens, you can DIY at home, using a few simple supplies and perhaps a trip or two to the craft and...

An update to the iFramed social media gateway app for iOS adds an augmented reality feature called JuxImage that gives its users Snapchat-like photo and video effects.

There are so many tips and tricks on how to improve your Instagram photos, but one really easy way is to use the HDR camera setting. HDR is high dynamic range imaging and takes three exposures of a photo — overexposed, underexposed, and one in the middle at the normal exposure. The end result is just one image of the three exposures combined.

Bed bugs are parasites not yet known to spread disease — but they cause plenty of irritation. As scientists and landlords search for new ways to deal with the pests, a new study examines how we can deter bed bugs without so many chemicals.

If you've ever seen me glued to my iPhone, huddled on the corner of the 23rd St subway station fidgeting with my stupid hot pink nails trying to Instagram Story, then now you are about to find out exactly what I've been doing.

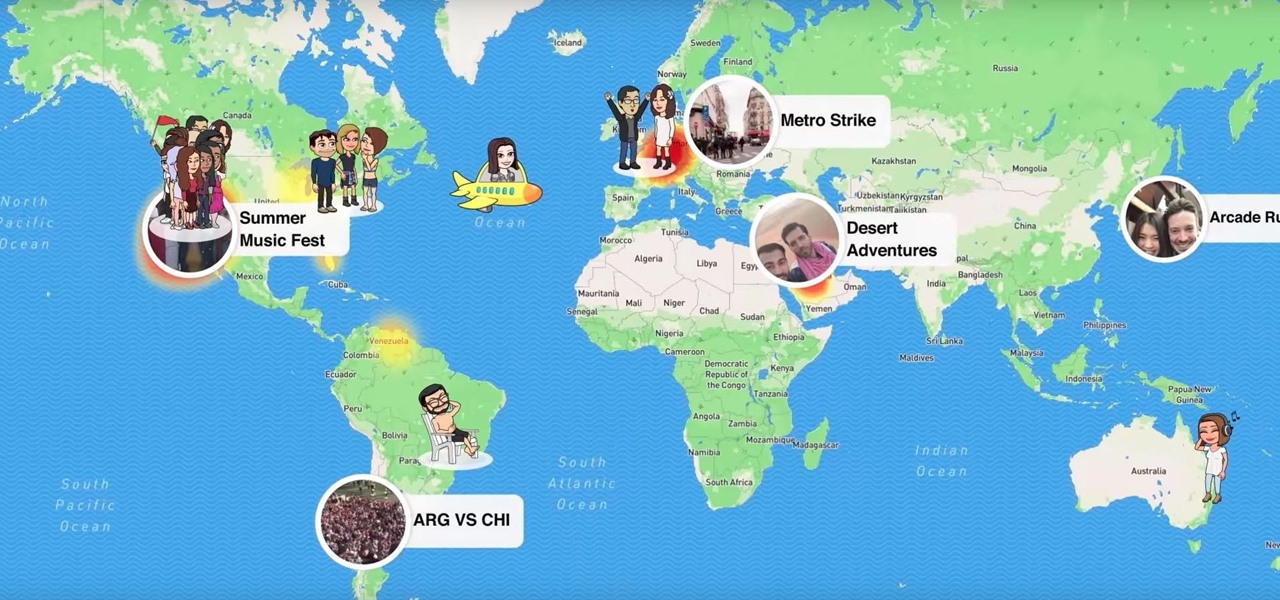
Snapchat's newest feature will allow you to see where your friends are posting from around the world. Called Snap Map, this easy-to-use update gives users the ability to view your friends' stories and locations on a map.

Social media is kind of depressing. On one hand, we love knowing what's happening in the lives of others. On the other hand, everyone seems happier, better looking, and more successful than you. We're putting on a facade by posting statuses and writing comments that present the person we want others to think we are, rather than truly expressing ourselves. Yes, social media has facilitated movements and miraculous events, but let's be real. For the most part, none of it matters.

The rumors were confirmed today at WWDC, Amazon Prime is coming to the TV app on the iPhone. This app will allow users to stream their favorite Amazon Prime shows including Bosch, Mozart in the Jungle, Catastrophe, Transparent, and more.

Throughout this NR50 series, we have talked about the incredible growth the augmented and mixed reality space has seen in the last year. More devices, software, developers, and use-cases seem to arrive daily. For this growth to have occurred, it took the work of many people, from many different backgrounds and skill sets — and Next Reality wants to recognize them for all that they have done and are doing.

It's Monday, and what's a Monday at Gadget Hacks without a new leak to ponder over? Thanks to known leaker Benjamin Geskin, we have a dummy iPhone 8 without one of its most-anticipated features.

Google Assistant just got a lot more powerful thanks to IFTTT. The automation platform, whose name stands for If This, Then That, connects your favorite online services and smart devices to one another, allowing for a seamless experience with many different gadgets—and Google Assistant is officially supported.

These days, when you're setting up an Android device for the first time, you'll be prompted to add extra email accounts directly to the Gmail app. It's really simple, too—just sign in with your work or exchange account, then emails from those accounts will be mixed in with your personal account in the Gmail app's "All Inboxes" view.

No matter how far technology advances, battery life continues to be an issue. Powerful new hardware is introduced each year, but smartphone batteries only get a few extra milliamp-hours to compensate.