In spirit of the recently posted brightly frosted cupcake periodic table, here are some equally clever, beautiful science-themed holiday cookies from Not So Humble. The creative cooking blog does not offer full instructions for most of these, but does lend tips here and there. Get inspired and bake your own holiday cookies.

Flickr user MR38 has posted a set of photos of bumper cars made street legal, as displayed at the annual Cruisin’ Grand festival in Escondido, California. This mini cars were retrofitted with 750 cc Kawasaki motors. Cool auto mod.

Extreme Holiday Ideas has posted several fun Thanksgiving projects this season. Check out some of my favorites:

Who wouldn't love an indoor swing? The upcoming cold winter season is one good reason to build one, but truly, an indoor swing is just plain fun all year round. Luckily Apartment Therapy has posted a How-To on building a simple wooden plank swing.

Perfect Pandas was kind enough to post link to an English translation of a Japanese Panda Bread How-To (made with green tea and chocolate dough).

Here's a Sunday project for you: Mow your lawn in the style of a flawlessly manicured baseball field.

This Super Mario manicure is frightening in a good way.

Don't want a reclining seat in your lap? Solution: Zip Ties

This video is about a particular pool or snooker game shot technique called "Shooting or Going around the Angles." The presenter, with a alias name of 'Forcefollow', first describes a particular 9-ball pool game situation that would require this technique, using a computer generated picture image to show an overhead view of the pool table, with the pool balls in question placed at certain locations within the table and showing the various angle trajectories paths of the desired ball to be str...

This video will show you how to disable secure virtual memory in Mac OS X. From the top left of your screen click on the apple icon. Click on system preferences from the pull down menu. Click on the security icon. Click on the image of the closed lock from the bottom left of the window so that you can change make changes.

Learn how to care for your pet with help from VetVid. See how to recognize mast cell tumors in dogs.

Pinning a tweet is a great way to get the point across because it's the first post people see when they visit your Twitter profile. When you pin a tweet, reply, or retweet, it sticks to the top of your profile, whether you create new tweets or not. It's the perfect spot to place one of your more popular tweets, a fantastic blog you wrote, or even just a joke that shows your personality.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

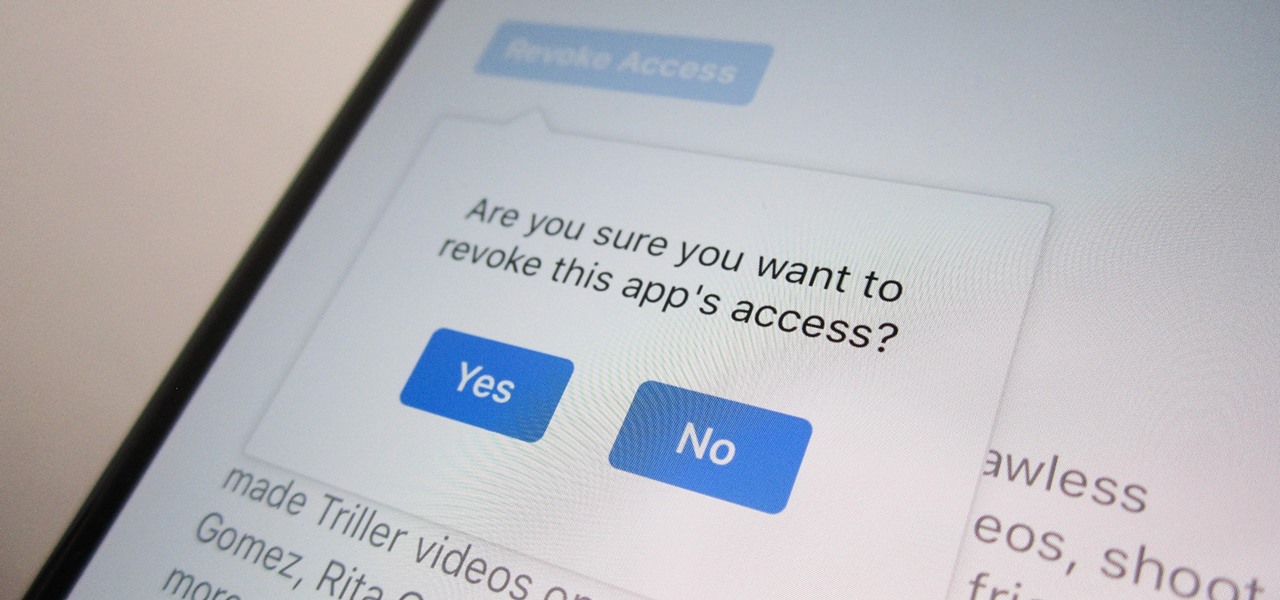
Unless you're completely new to Instagram, it's likely that you've linked your account with a third-party service at some point and forgotten about it. Those services still have access to data such as your media and profile information, so it's important that you not only know how to find these "authorized" apps, but that you know how to revoke their permissions.

Whether you've celebrated multiple cake days or you're just now getting your feet wet with Reddit, it's a rite of passage to choose your preferred smartphone client. Quick spoiler: Your best option most certainly is not the official Reddit app.

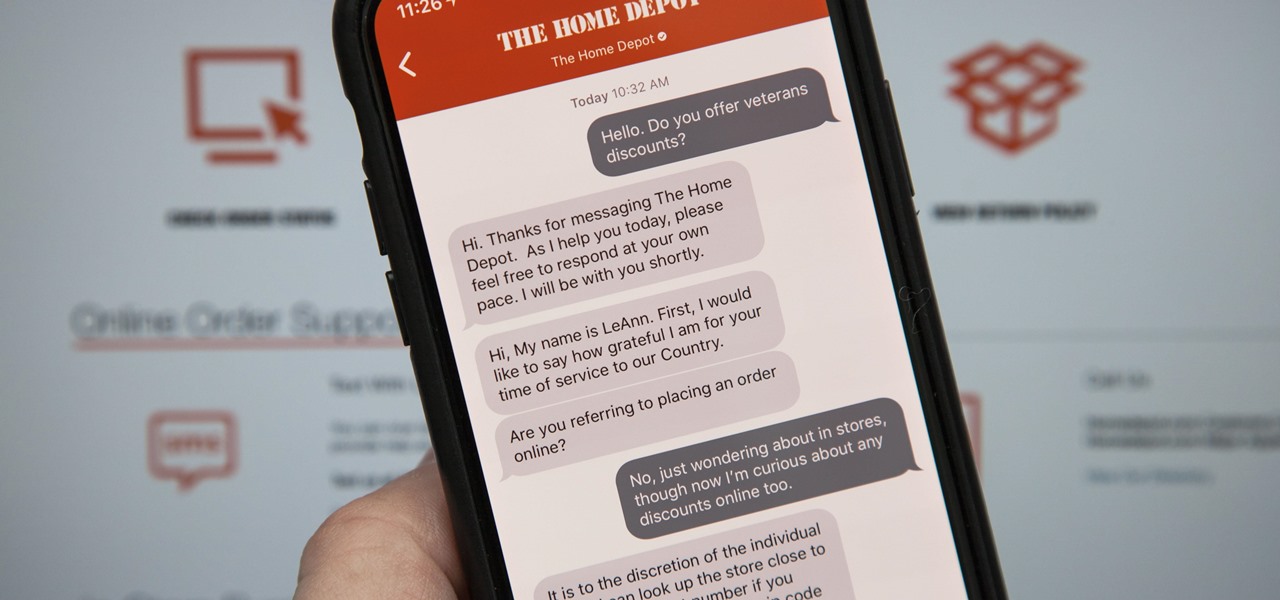
Apple first announced Business Chat, a new way for customers to communicate with companies, at WWDC 2017. While Business Chat did not arrive with the initial release of iOS 11, Apple pushed it out in iOS 11.3 so companies can offer customer service in a whole new way, and it works pretty much the same in iOS 12 and higher as it did back then.

After exploiting a vulnerable target, scooping up a victim's credentials is a high priority for hackers, since most people reuse passwords. Those credentials can get hackers deeper into a network or other accounts, but digging through the system by hand to find them is difficult. A missed stored password could mean missing a big opportunity. But the process can largely be automated with LaZagne.

When most people say, "Damn, look at that rock," regarding an engagement ring, they're usually not referencing an actual rock—let alone a space rock.

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.

Welcome to the Part 2 of the series 'Cryptocurrency'. It has been late because of some errors, where all I typed was lost.

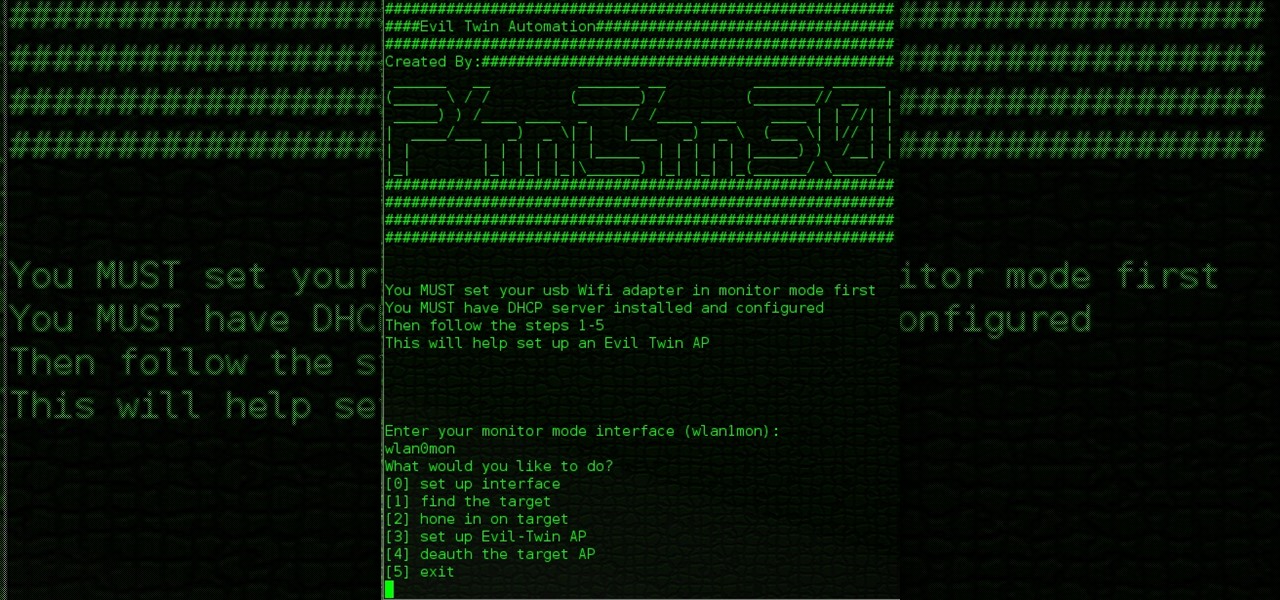
Hello All, So to recap in part 1 I went through setting up the dchp server. Part 2 detailed the bash script. Now in part 3 I will post the entire bash script. I am doing this in its own post because Part 2 is just way to much info on one post IMO.

This is second post in my series of posts for finding hacked accounts online. Please do read the part 1 of the post at http://null-byte.wonderhowto.com/how-to/find-hacked-accounts-online-part-1-0164611/

For many of you, this is common knowledge. But I still regularly see comments posted here and elsewhere asking, "This <AV bypass> doesn't work, because when I upload my payload to VirusTotal...."

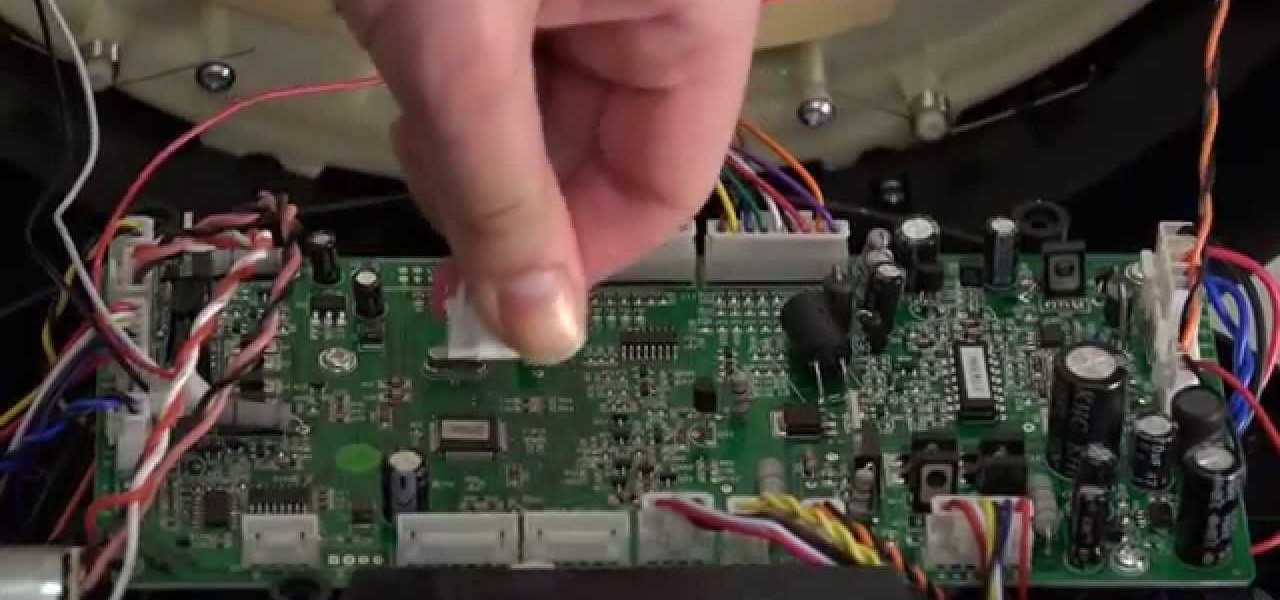
The bumper for bObsweep Pethair and Standard are installed the same way. It holds the sensors that allow Bob to see any obstacles in his path. If a repair of the wall detection sensors is needed, the steps for replacing the whole bumper are the same when working on either bObsweep model.

Welcome back, my novice hackers! We've done a number of tutorials using one of my favorite hacking tools, Metasploit. In each of them, we've used the msfconsole, which can be reached through either the menu system or through simply typing "msfconsole" from the terminal.

Many social networks have become a part of our daily routine. Checking Facebook or sending out a Tweet are things millions of people do every single day. So, one would think that having a great app offering for Windows 8 would be a no-brainer. But, and this is a huge but, there are still no official Twitter or Facebook apps for Windows 8.

Notes: My guides are setup like old Lego instruction booklets; picture intense/text lacking. Just remember you're building from the ground up, each step is a layer to go onto the previous layer.

Last week, we rolled out a major site-wide update on WonderHowTo, making it even easier to follow the subjects you're passionate about—and easier to share your creations with people who'll give you the kudos you deserve!

Call Your State's Nurse Aide Registries for School Inquiries

Zynga games has released their ZLotto feature that you can use to get exclusive prizes for FarmVille, Mafia Wars, YoVille, PetVille, and FrontierVille!

Watch this video from This Old House to learn how to make deck stairs. Steps:

This video crocheting tutorial shows how to crochet the front post double crochet and the bobble stitch. Bobbles are different for different people; demonstrated is a less complex method. Watch this instructional video and learn how to crochet a front post double crochet and bobble stitch.

Mad Science is looking for more hackers, makers, and DIYers to participate in our community madness. If you've recently designed or made a project, we want to see it! Share with the other Mad Scientists out there by posting up a how-to of your pet project on our community corkboard, or even just a few cool, inspiring photos of the build.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

In this article, I'll show you how to send SMS messages with Python. You'll need Python 2.7 or later, urllib and urllib2. The code basically uses an online text messaging service to "POST" html data, as if a person was entering the data themselves. The uses for something like this are unlimited. For example, I modified the basic code so I would receive a text message letting me know every time someone rang my doorbell. The program could interface with Arduino through a serial port, and send d...

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

If you slept in during the peak of the Quadrantid meteor shower this morning, don't fret, because plenty of early risers did manage to wake up—with their cameras. Even if you did wake up and managed to withstand the cold morning air, you might not have seen anything. Cloud cover could have made it impossible, as well as bright city lights. But some stargazers made it their mission to photograph the Quadrantids, and lucky for you, they did.

If you take two flat mirrors and place them front to back and look at them, you can see an infinite number of reflections. While this is a self-replicating pattern and can be somewhat mesmerizing, it isn't anywhere as interesting as looking at the chaotic scattering of light that can occur between 3 or 4 spheres.

When was the last time you took some time out of your day to play with your favorite action figure? Or build an entire town of Legos? Well, it’s time for you to dust off that old toy chest for this week’s Phone Snap challenge!