This video demonstrates the proper way to deep frying a turkey. Before you start frying the turkey, you should make sure the turkey is fully on normal temperature and that your pot of oil is at 350 degrees. Turn off the flame of the pot and then slowly lower your turkey and submerge it in oil, making sure to avoid spilling any oil. Once the turkey is fully submerged in the oil, you can turn the flame back on again. The turkey should be cooked for 3.5 minutes per pound. If the instructions in ...

Polish sausage? Are you kidding? If you ever, ever go to Poland, you need to try the sausage! In this video, learn how to say the word "sausage" correctly in the Polish language... the single word that will act as a portal to a world of sensational tastes... and a few extra pounds.

Directions 1. Boil Tamarind in rice wash or water to soften. Pound and extract all juices and set aside.
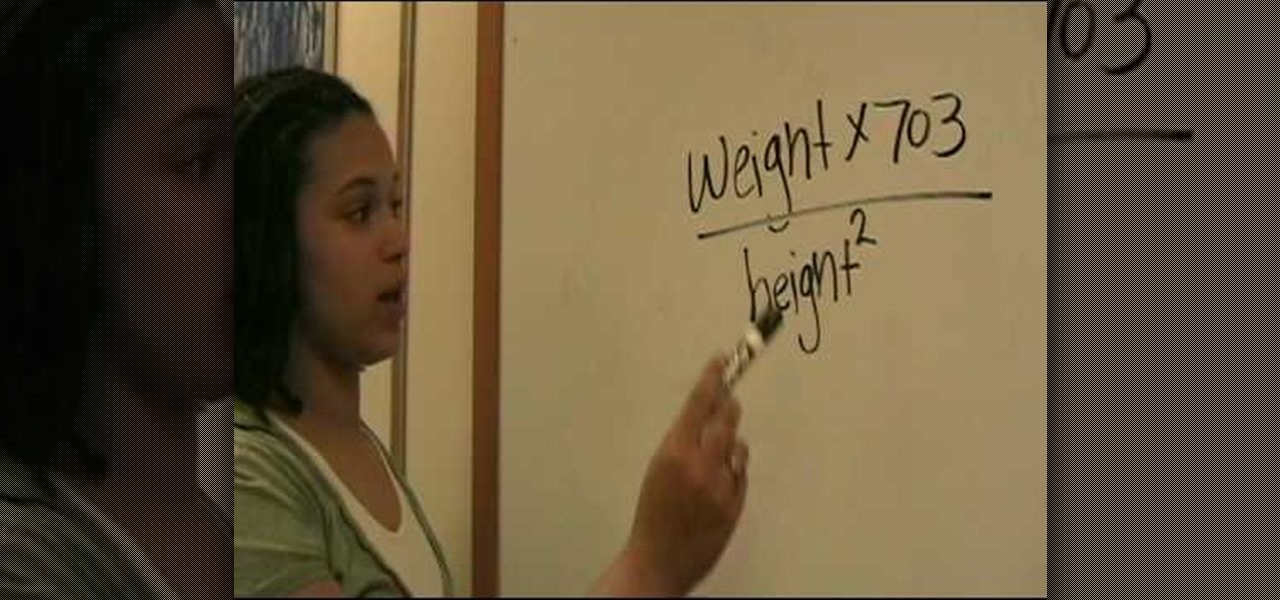
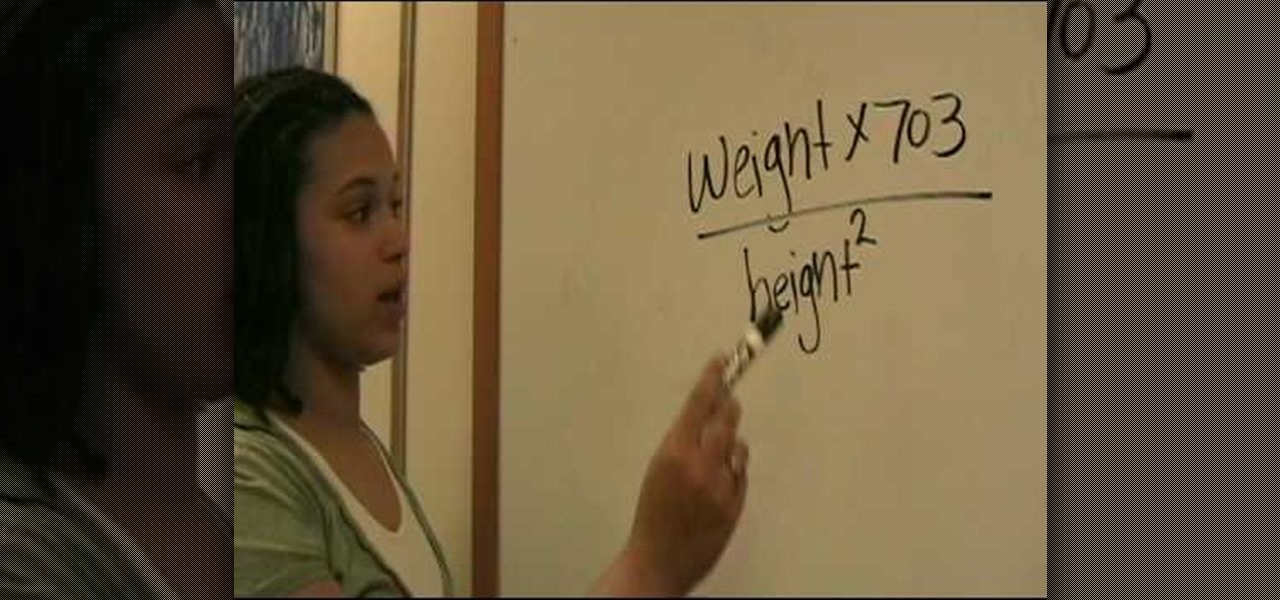
Knowing your BMI, or Body Mass Index, is a great way to see if you are at a healthy weight. In this simple and short video provided by Children's Hospital Boston, you will figure out how to calculate your BMI by taking your weight (in pounds) and multiplying it by the number 703 and then dividing it by your height (in inches) squared.

Why put a steak on a plate when you could make it into an amazing sandwich? Betty shows you her special filet mignon steak sandwich recipe.

Chef Suvir Saran shares his recipe for curried summer squash. - Combine canola oil, 1 tablespoon of mustard seeds, 3 red chilies, 1 teaspoon of cumin seeds, and 12 curry leaves in a pan and stir fry the ingredients.

Handling a 15 pound watermelon is no easy task. This video offers a demonstration on how to create a beautiful centerpiece for your table using basic strategies and handling techniques on your watermelon.

Use top round roast, seasoned with meat tenderizer. Pound the seasoning on both sides of the beef so it is absorbed. Place in crockpot and cook for about 8 hours. Remove the beef and cut into small pieces. Take two slices of bread of toast in the toaster. Place the roast beef on top of the toast. Cut the sandwich in half. Place the two pieces of sandwich on a plate and in the middle of the plate place mashed potatoes. Use the remaining drippings from the crockpot to make gravy. Pour the gravy...

Every day, the average American throws away about four pounds of trash. But a lot of your daily trash could actually be very useful in the garden, as composting. In this episode of Growing Wisdom, Dave Epstein shows you how to use a three-bin composting system.

Paula Deen makes five-alarm chili and serves it in a biscuit bowl. This cooking how-to video is part of Paula's Party show hosted by Jamie Deen, Paula Deen. Join Food Network's queen of southern cuisine, Paula Deen, for Paula's Party. Expect the unexpected when you drop in on Paula: you never know what's going to happen! Follow along today and learn how to make a five alarm chili in biscuit bowls.

Here is sweet and salty seafood recipe that you are sure to enjoy. This cooking how-to video will show you how to prepare and cook honey and soy sauce salmon. Make this seafood recipe at home tonight, we are sure you'll love it.

Tamales are very laborious to make, but they are definitely worth it. This cooking how-to video shows you the step by step process of making Mexican tamales with Mexican chorizo. You can use chorizo as your stuffing agent or any other meat.

Here is a sandwich that is perfect for dinner or a light snack. Watch this cooking how-to video lesson and learn how to make a homemade BBQ pork sandwich. You won't have to turn on your grill for this barbecue pork sandwich.

You've heard of a stromboli sandwich, well here is a how-to video showing you how to make it. Follow along with this video cooking lesson to learn how to make an authentic and delicious stromboli that is big enough to share. This sandwich recipe is very easy to make.

Installing a new garage door and opener may seem daunting at first, but if you take your time and do the job step-by-step, it's a good weekend project. It will take from nine to 12 hours for most doors, then another two to four hours for the opener. You will need help for some portions, such as lifting out the old door and lifting the new door up until the tension springs can be installed (some doors may weigh up to 400 pounds). You may need to remove an old door, or you may be installing in ...

Korean style grilled beef is served with green onion salad, a mixture of bean paste and hot pepper paste called "Ssam Jaang". You wrap it all up into a leaf of lettuce and pop it into your mouth. You can dip some pieces of cucumber and carrot into the spicy paste. Watch this how to video to learn how to cook Korean style marinated beef.

A lot goes into making a hunt successful, and most of it happens before you take to the field--like making sure your rifle is properly sighted in. It's not hard to do if you follow a few simple steps: first, and this is the first step when you do anything with a firearm, make sure it's unloaded. Make sure your scope is properly mounted and the mounting screws are tight. Remove the bolt from the rifle and sight through the barrel to make sure you're lined up with a sight-in target placed at 25...

How to cook Puerco Pibil by Robert Rodriguez. This is an excellent spicy breakfast. This is the slow roasted pork as seen is his film Once Upon a Time in Mexico. 5T whole annato seeds 2t whole cumin seeds

Your target in level 3-13 of Angry Birds is not so much a pig fortress but a series of pig-defended hilltops. Still no problem for a properly trained bird army. Watch the video for a guide to beating level 3-13 with three stars.

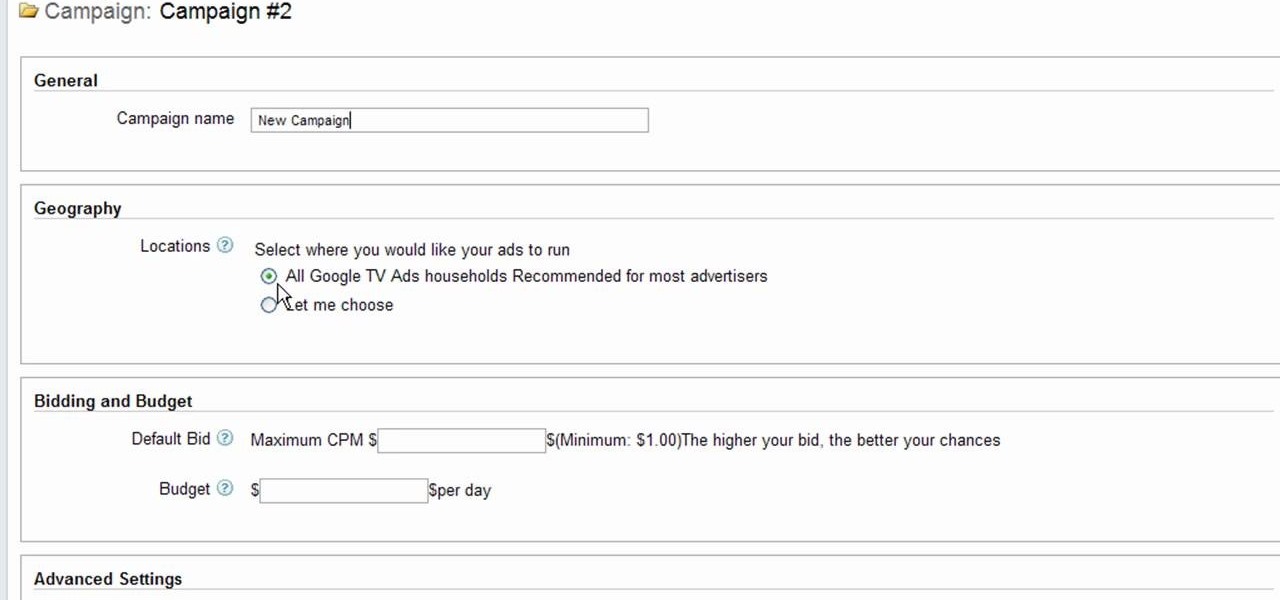
Interested to know how to start a new cable television ad campaign with Google AdWords TV Ads? This official video from Google will teach you how to use the new interface to determine just that. For all of the relevant details, and to get started creating your own televised advertising campaigns, watch this clip.

It's been a few years since Finding Nemo became the highest-grossing animated film of all time, but it's cultural appeal lingers on. If you want to capture some of that Nemo cuteness for your Halloween costume, watch this video to learn how to make a really cute Nemo costume with no sewing required.

Halo: Reach has so many tough to get achievements, but the easiest one that you can get pretty fast is the "Crowd Control" achievement, and you can get it on Courtyard using the target locator. In this video you will learn how to effectively kill off multiple Covenant drop ships to get the achievement in about five seconds!

Two Corpses in One Grave is a difficult achievement in Halo: Reach if you don't know where to look on mission 3. You will have your chance right after you acquire the Target Locator when two Wraiths show up for the killing! Just be sure to aim straight and true and you will be alright!

Thanks to modern technology, we don't have to visit our nearest Target or Rite Aid to get our pictures professionally retouched and printed. With many printers offering photo-quality ink and paper companies that offer photo-quality paper, you can use your home printer to create professional-grade photos.

If you're planning to become a veteran yogini, you'd better start practicing and loving the up dog pose now, because you'll be spending the greater part of your yoga flow doing up dogs and down dogs.

Sometimes searching Craigslist can be a real hassle if you're looking for something specific. You really have to sort your way through all the clutter in order to find whta you're looking for. If you are looking for email addresses of people who might fit your target market, you can scrape Criaglist for emails. This video will show you how.

In this episode of Hak5, Darren shows us a USB key, dubbed the USB Hacksaw, that instantly and silently installs on target Windows 2000 or higher computers with guest or higher privileges which will monitor USB ports for flash drives and automatically download their contents for silent archival and email. For detailed instructions on replicating this hack yourself, watch this video hacking tutorial.

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

Privilege escalation is one of the essential skills a hacker can have and often separates the newbies from the pros. With a continually changing landscape and a plethora of exploits out there, it can be a problematic aspect of any attack. Luckily, some tools can help expedite the process. Linux Exploit Suggester is just one of many to help you get root.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

When researching a person using open source intelligence, the goal is to find clues that tie information about a target into a bigger picture. Screen names are perfect for this because they are unique and link data together, as people often reuse them in accounts across the internet. With Sherlock, we can instantly hunt down social media accounts created with a unique screen name on many online platforms simultaneously.

The Windows 10 desktop and microphone can be livestreamed without using Remote Desktop Protocol (RDP) software and without opening any ports on the target computer. A hacker with low user privileges can monitor and exfiltrate a target's every move and private conversation in real time no matter where they are. Hackers are watching and listening, and there are few ways to protect yourself.

Featured on MTV's Catfish TV series, in season 7, episode 8, Grabify is a tracking link generator that makes it easy to catch an online catfish in a lie. With the ability to identify the IP address, location, make, and model of any device that opens on a cleverly disguised tracking link, Grabify can even identify information leaked from behind a VPN.

The quality and length of your sleep will almost always dictate how the rest of your day unfolds. Sleeping fewer hours increases your chances of spending the day in a tired and cranky state, while having a restful night's sleep contributes greatly to being alert and productive. Luckily, if you want to track your sleep patterns to figure out how you can improve your circadian rhythm, Samsung Health has you covered.

The ability to execute system commands via a vulnerable web application makes command injection a fruitful attack vector for any hacker. But while this type of vulnerability is highly prized, it can often take quite a bit of time to probe through an entire application to find these flaws. Luckily, there is a useful tool called Commix that can automate this process for us.

Epic Games just released update v3.4 for Fortnite Battle Royale on all four platforms. This new version brings a number of UI changes, performance improvements, and bug fixes, but the addition that will get the most players excited is a new weapon: the Guided Missile.

RouterSploit is a powerful exploit framework similar to Metasploit, working to quickly identify and exploit common vulnerabilities in routers. And guess what. It can be run on most Android devices.

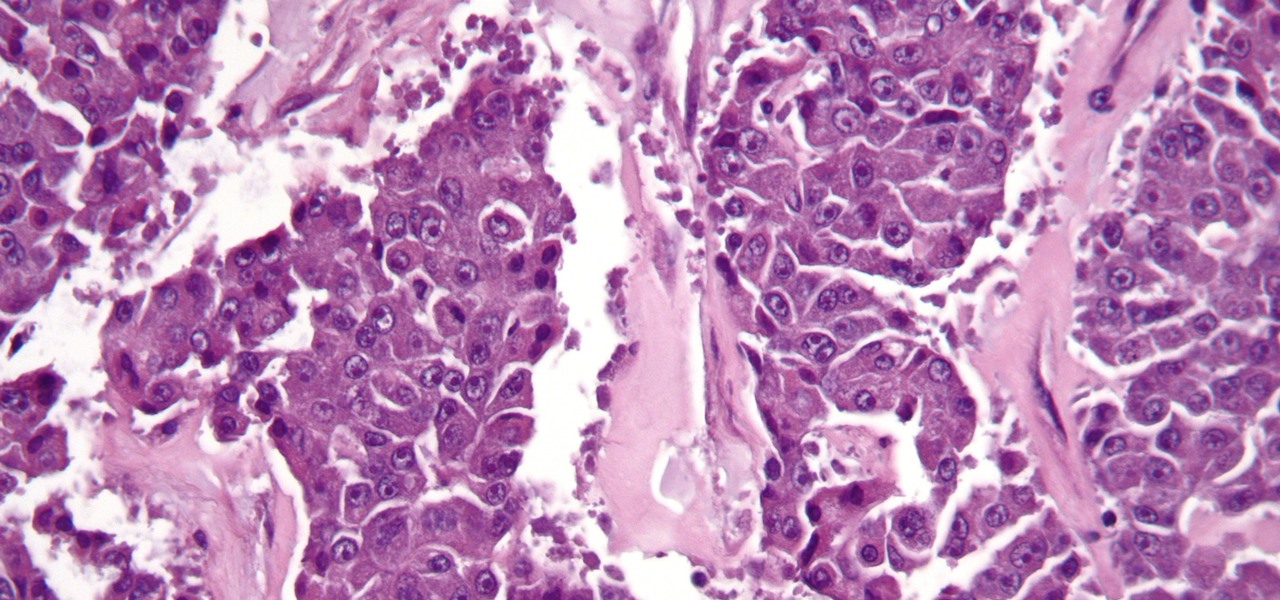
The search for a cancer treatment that selectively finds and kills only the cancerous cells has just made a giant leap forward.

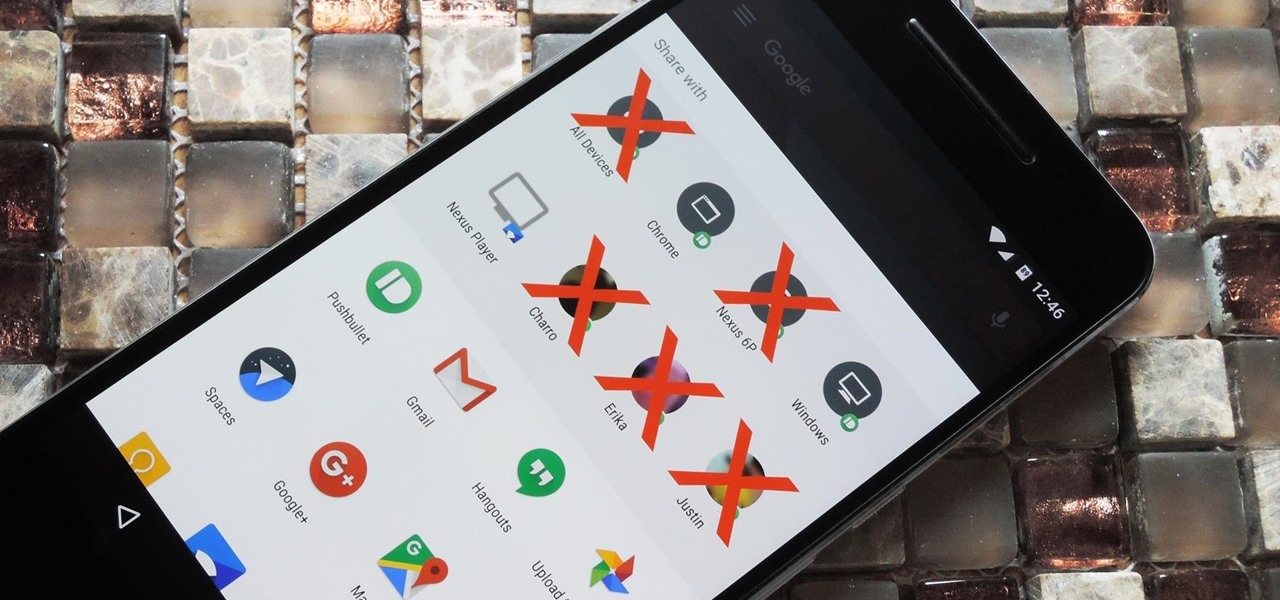
Android 6.0 introduced a new feature called Direct Share that allows apps to pin a more specific set of targets to Android's share menu. You've probably seen it already—messaging apps will allow you to share a file directly to a specific contact instead of just to the main app, and there are several other implementations like this.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.