
IFA 2014: Samsung's Galaxy Note 4 & Galaxy Note Edge
Today was a big day for Samsung at IFA 2014, with announcements of two new devices as successors to the Galaxy Note 3: the Galaxy Note 4 and Note Edge.


Today was a big day for Samsung at IFA 2014, with announcements of two new devices as successors to the Galaxy Note 3: the Galaxy Note 4 and Note Edge.

This is just another crazy prank you can pull in the work place or at home to make time go by faster and have a little fun in the process.

Many superstars have fallen to the devastating power and destruction of the finisher wrestling move known as the Spear. Among the wrestling superstars who have made this move incredibly popular are Edge, Rhino, Bill Goldberg, and the up and coming superstar Roman Reigns. In this professional wrestling video tutorial you will learn the basic concept and performance of the Spear.

Website Design Tutorial for Xara Web Designer - graphics folder in designs gallery. In this web design tutorial learn how to add various graphics, modify colors and remix images to create your own custom icons or logos. The web design tutorial will put some of the concepts you learned in previous web design tutorials to practical real world use. If you need assistance using Xara Web Designer let us know and we will do our best to create web design tutorials to help you.

This HowTo is about using Pattern Blocks in the classroom. All you need is a classroom set of pattern blocks and a camera. Each student or group of students is given a set of pattern blocks and a time limit. The assignment: make an artwork that illustrates the concept of symmetry, small enough to fit on a single student desk. When the art is finished, take a photograph of it and then let the students vote to choose their favorites.

In this web design tutorial learn to create and delete layers. This web design tutorial for Xara Web Designer also covers deleting pages, deleting objects on different layers and re-arranging layers that have objects on them. A brief discussion about MouseOff Layer and MouseOver layer is also introduced in this Xara Tutorial. I would say this is one of the single most important Xara Web Designer Tutorials because layers allow you to do so many unique things with your website within Xara Web D...
First of all, this was not invented by me. I state this clearly and the link for the original discussion is located below. I made this video, as the original author did not do so, in an attempt to raise awareness as to the awesome concept that it is.

In this language tutorial you will learn to say basic phrases in Bengali. Bengali is the primary language spoken in Bangladesh and is the second most spoken language in India. Repeat and practice the phrases in this how to video and you will be conversing in Bengali in no time.

Watch for water dripping out of a tube in a place that it's never dripped before. There could be a reason for this. It's called the backup condensation line. This is your alert to unclog the primary drip line.

The 2020 iPhone SE had been through the rumor mill for a long time, but Apple finally unveiled the second-generation iPhone SE on Wednesday, April 15. While it doesn't sport the 4-inch design of the original SE, it combines a small form-factor with modern specs. The big question, of course, is when and how you can get your hands on one.

We've got almost a full year until the next installment of Ghostbusters arrives, but in the meantime, it turns out that Sony is about to launch an augmented reality experience that will let fans use immersive computing to combat the franchise's whimsical apparitions.
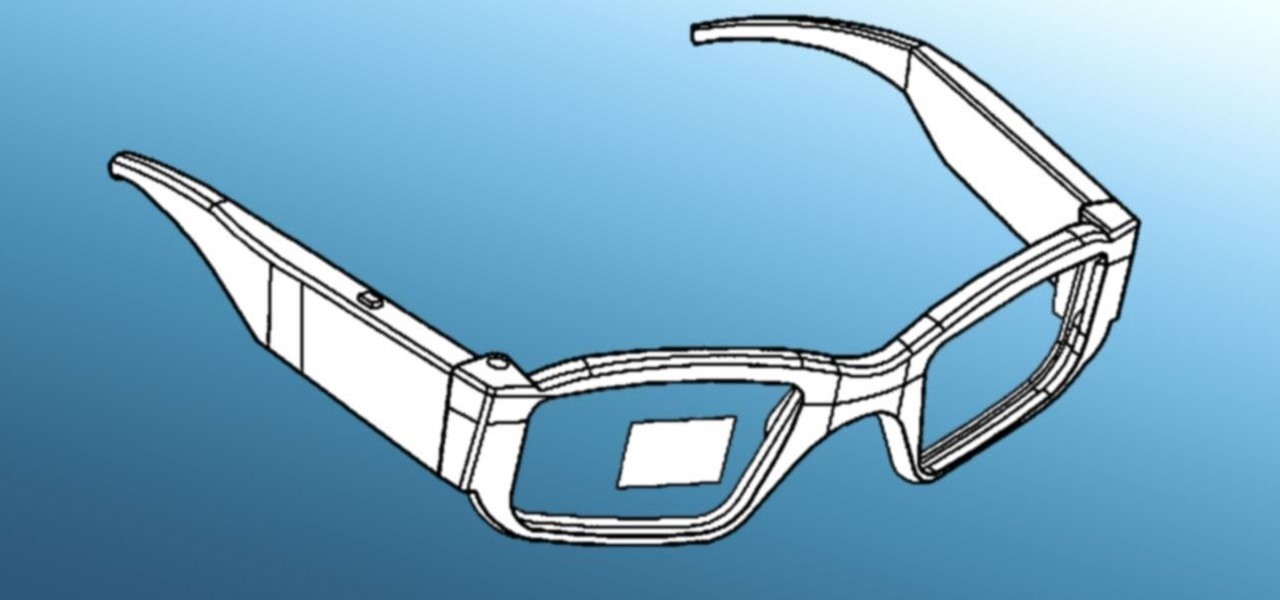
Historically, patents have never been a rock-solid source for uncovering the future of a company's product pipeline. However, sometimes, the images you find in the patent application search archives are so convincing you have to pay attention.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

Among all the new Magic Leap app announcements made at the recent L.E.A.P. conference, an update to one of the company's major in-house apps went mostly unnoticed: Create 1.1.

When it works, Android's Smart Lock feature is incredible. There's no need to enter your PIN when your phone "knows" it's in your hands — just unlock and go. But Smart Lock, particularly its Trusted Places feature, can be finicky sometimes.

Just weeks after being acquired by comedian turned producer Byron Allen for $300 million, The Weather Channel has tapped augmented reality studio The Future Group to integrate immersive augmented reality experiences into its broadcast content.

The once blurry and mysterious vision of Magic Leap's future is slowly coming into focus in the present, despite the company's obsessive attempts to keep any and all information under wraps until the next reveal is absolutely necessary. A new tidbit of information hints at an addition to the company's unfolding story that almost no one had accounted for: retail stores.

In its continued pursuit to elevate retail technology, Amazon has been awarded a patent from the US Patent and Trademark Office for a digital mirror that lets customers virtually try on clothes with different backgrounds.

Last week, augmented reality startup Proxy42 released Father.IO, a multiplayer game that turns any indoor or outdoor space into a laser tag arena.

Like gas on an open flame, rumors and whispers have flared up in recent months around hopes of augmented reality smartglasses from Apple. But among all the false leads and unsubstantiated chatter, we finally have a credible report that some sort of Apple AR smartglasses are actually in development.

One of the more meme-able characters from the animated series Rick & Morty will be able to beckon iPhone owners to "show them me what you got" thanks to ARKit.

The Sharknado franchise is, somehow, releasing a fifth movie "Sharknado 5: Global Swarming" (groan) next month. In anticipation of the film's release, the company has decided to create an augmented reality mobile game called, prepare yourself, "Sharknado: ShARkmented Reality".

The list of HoloLens applications continues to grow as more companies discover ways to enhance their operations using augmented reality. Air New Zealand is the latest to show interest in the technology, demonstrating their vision for AR in a new concept video.

Augmented reality upstart DAQRI announced today that it has strengthened their in-house talent by recruiting renowned physicist Seamus Blackley and acquiring a team of 15 engineers and scientists from Heat Engine, LLC.

If you've played the game Portal by Valve before, you've most likely popped one portal onto the ceiling and another directly below it on the floor, dropped your Companion Cube in, and then watched it fall forever. Well, now it has been done in real life, in an actual hallway, not in a rendered world.

Here at NextReality, we talk a lot about the many different ways of controlling holograms in the HoloLens and other augmented and mixed reality devices; New and creative ways are coming more and more every day. Most recently is something called the HoloSuit. In the 25-second clip below, you can see a woman moving the arm of a jacket which in turn moves a 3D model of Darth Vader on the screen. It's a simple idea with big potential.

Google has been working on its voice recognition technology ever since the days when you had to call a phone number with a Silicon Valley area code to dictate your query. As you can imagine, things have come a long way in the decade or so that has passed, to the point where we talk to our phones as if they were a person nowadays.

It seemed appropriate that we announce the winner of the first White Hat Award for Technical Excellence on the Academy Awards weekend. This is, in essence, our "Oscar" here at Null Byte. Remember, this contest began on January 4th, 2016 and just recently closed on February 15th. In this contest, I was looking for:

Welcome back! In the last iteration of how to train your python, we covered loops, today we'll be covering something that I wish I had learned about much earlier in my scripting career, errors. We all run into them, and they can be frustrating, but there is also a silver lining to them. Today, we'll be discussing why some errors are unavoidable, and what we can do when we run into them. Also, this article will be more of a concept and less of writing actual code, but the information is equall...
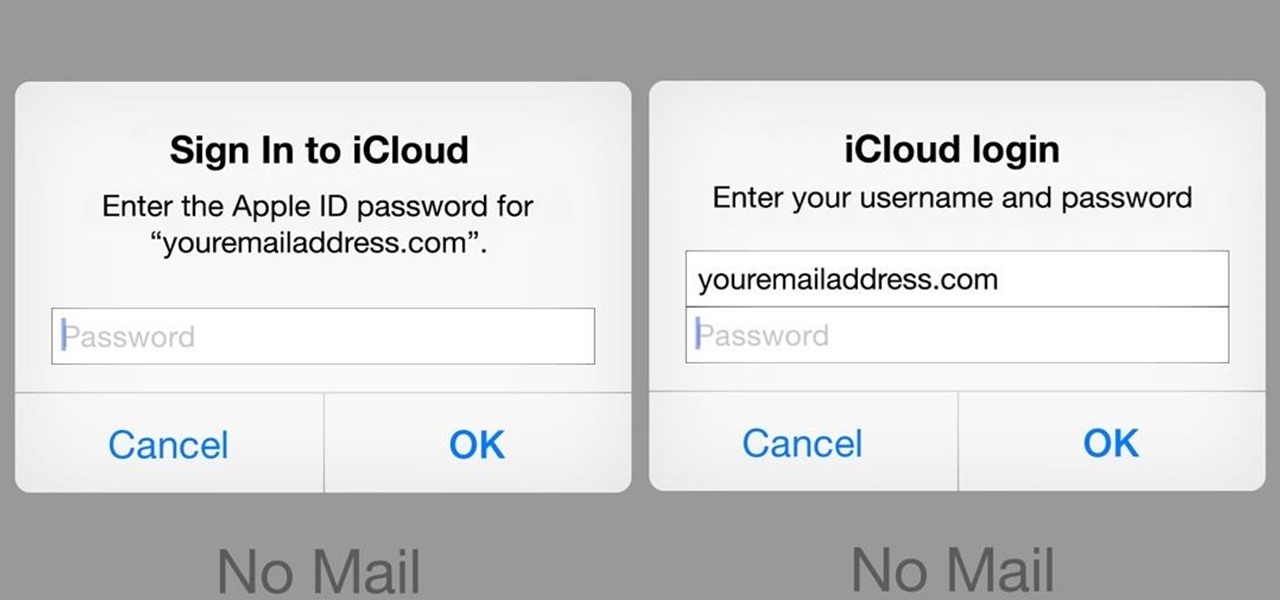
A recently discovered bug in iOS 8's Mail app by Jan Soucek can allow the maliciously-minded to quite easily phish your iCloud password without you ever thinking something has gone awry. Using a bug that allows remote HTML content to be loaded in place of the original email content, unsuspecting victims would be prompted for iCloud credentials in a popup that resembles the native one found on iOS.
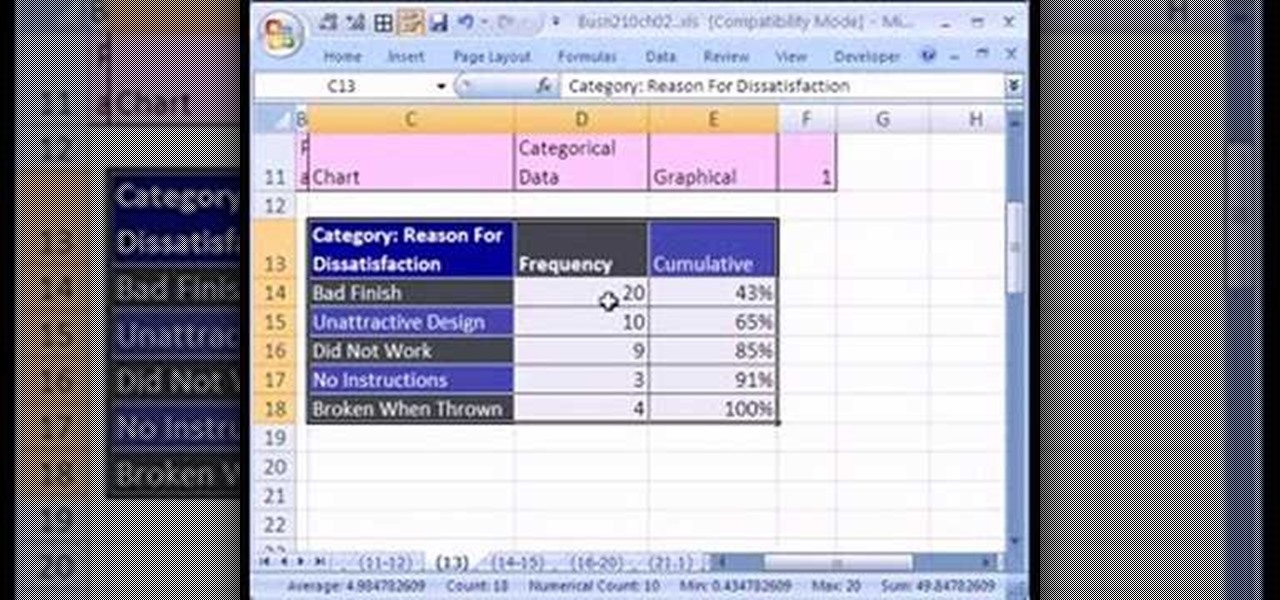
If you want to create a Pareto Chart for categorical data in MS Excel you should first have your data input into Excel already. From your data, you should highlight the cells that you want to count the frequency for and in the frequency box you should type in =COUNTIF and highlight the data you want the frequency for and put in F4 and then press , click on cell to the left and click enter. Now this will work all the way down. If you have not sorted it, you can right click and then click sort....
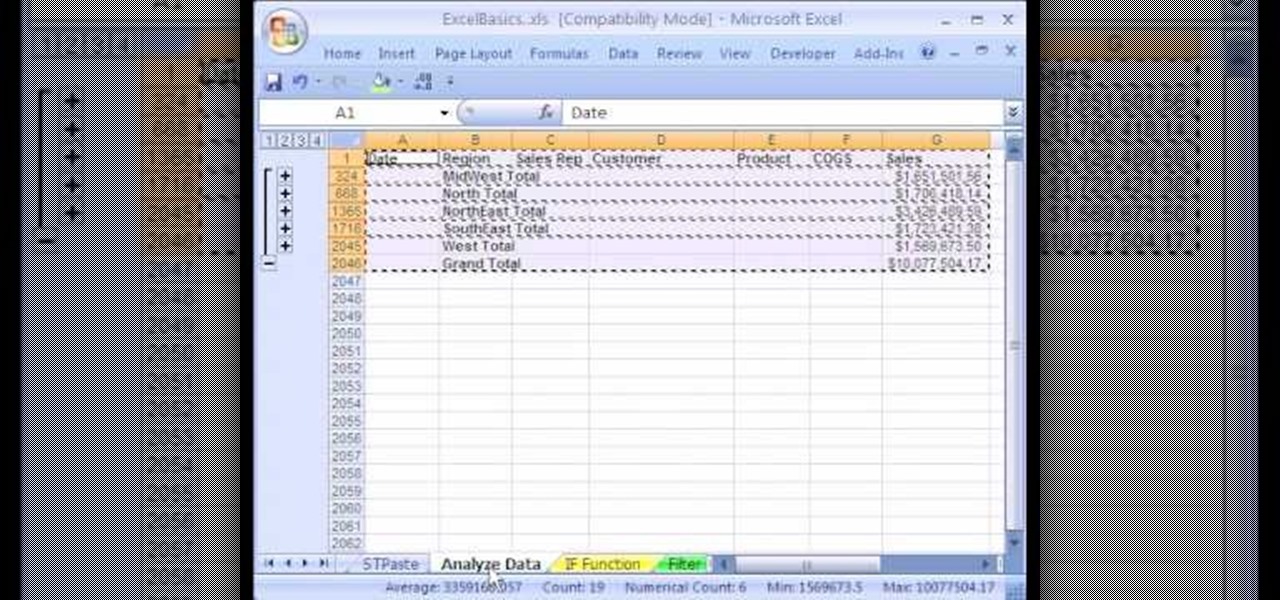
1. The following instruction describes how to generate sub totals in Microsoft Excel Sheet. 2. Take Region as a Primary column and Sales Rep as a Secondary Column. 3. First method to sort: Select a cell in Region and goto Data select A to Z. 4. Second method to sort: Select a cell in Region and Right click and select Sort A to Z 5. Then click a cell in Region and select Data->OutLine->SubTotal 6. In the SubTotal Window select 1.Each Change in: Region 2.Use function:Sum 3.Add subTotal to:Sales...

Safety is of primary concern when driving a vehicle or riding a bicycle. Watch this video tutorial on how cyclists and motorists can safely share the road when the former wants to make a right turn and the latter is cycling straight.

Apple's iOS 15.4 and iPadOS 15.4 updates have a pleasant surprise for iCloud Mail users and everybody that use the Mail app as their primary email client for AOL, Gmail, Outlook, Yahoo, and other third-party email services.

The focus on augmented reality over at Apple is, so far, restricted to the iPhone and the iPad. But if some of the most reliable analysts in the business are to be believed, we'll probably see some kind of AR or VR wearable from the company later this year.

Sorry, Galaxys S11–19, Samsung's jumping straight to Galaxy S20 this year. They're also going with essentially three base models before accounting for niche variants. Of these three models, it's clear which one's the best: the Galaxy S20 Ultra.
Being an Android user and having friends who are in the Apple ecosystem does not need to be a pain. You can easily send high-quality videos to iPhone users, so don't feel handicapped without access to iMessage. Sending high-resolution videos to iOS users is easy with this fast video-sharing method.

When you hear a "ding" on your phone, chances are it's a new notification for Facebook Messenger, and it could be a fairly painful sound depending on how loud your volume's set. Thankfully, you aren't stuck with this singular alert option, so if you're unhappy with both this sound and the call ringtone, you can change it to something else — something less distressing.

The year in augmented reality 2019 started with the kind of doom and gloom that usually signals the end of something. Driven in large part by the story we broke in January about the fall of Meta, along with similar flameouts by ODG and Blippar, the virtual shrapnel of AR ventures that took a wrong turn has already marred the landscape of 2019.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.