Linux can have the most beautiful interface in the world, because it is simply what you make of it. You can change every little detail with relative ease because that's what Linux is all about: Freedom and OpenSource.

Something that can shy a user away from making the switch to Linux is not having the option to go back to Windows. Luckily, there are solutions like dual-booting, where you can have both OS's installed right next to each other. However, Windows 8 appears as if it will block dual-boots with its neo-space BIOS that have been developed. Sneaky-sneaky. Windows users could still throw in a Linux live CD to try out Linux, but what does a Linux user do when they need something from Windows?

+Nik Cubrilovic discovered last week that Facebook could track your web activities even after you logged out of your Facebook account. After some blatant denials from Facebook spokespeople, Facebook decided to fix the logout issue, but not before +Michael Arrington, on his new Uncrunched blog, made a concise post revealing Facebook's dishonesty: Facebook submitted a patent application for "tracking information about the activities of users of a social networking system while on another domain...

From cooking shows to concerts, people have been finding all sorts of creative uses for Google+ hangouts. But what about something a little more basic? What if you could watch YouTube live streams with your friends?

Calling all curious minds—scientists, anthropologists, relentless tourists: Saturday, April 9th, is International Obscura Day, the day to "explore hidden treasures in your hometown," or so says Atlas Obscura, a website dedicated to public curiosities and esoterica. If you're the kind of person who appreciates public oddities every day of the year, tomorrow is icing on the cake. Celebrate Obscura Day in one of hundreds of locales—from Los Angeles to Sydney, from Berlin to Manila.

I'm not going to lie. I was Catholic. But one of my reasons for my faithful departure was having to tell my innermost secrets— my sins— to a silhouetted figure behind a latticed screen. With the creepy enclosed booth structure and separation of sinner and confessor, its anonymity was clear, yet deceiving. You always knew the priest and he always knew you. If I wanted total privacy, was there really a need for this intermediary to God?

Some update notes that you should take notice to are:Celestian Furniture Yes you read that correctly! Celestian Furniture has come to the Spiral, as well as recipes for furniture from our newest underwater world! Keyboard Shortcuts

Hotmail just isn't the same anymore— it's better! In the just-released Windows Live Essentials 2011 from Microsoft, Windows Live Hotmail 2011 is jam-packed full of new features.

Google has caught a lot of flack for various privacy infringements over time. Google Buzz was the latest uproar, when lack of proper prior testing allowed the tool to expose a slew of information users did not necessarily want shared, resulting in massive complaints. A Harvard student even went so far as to file a lawsuit (read more).

The shift to remote working in response to the COVID-19 pandemic has not slowed Google's efforts to fulfill its annual Android update cycle, as the third developer preview of Android 11 dropped on Thursday.
Ok, now lets introduce myself i am also a newbie but conducted many pentests.This is the tutorial for customizing kali linux

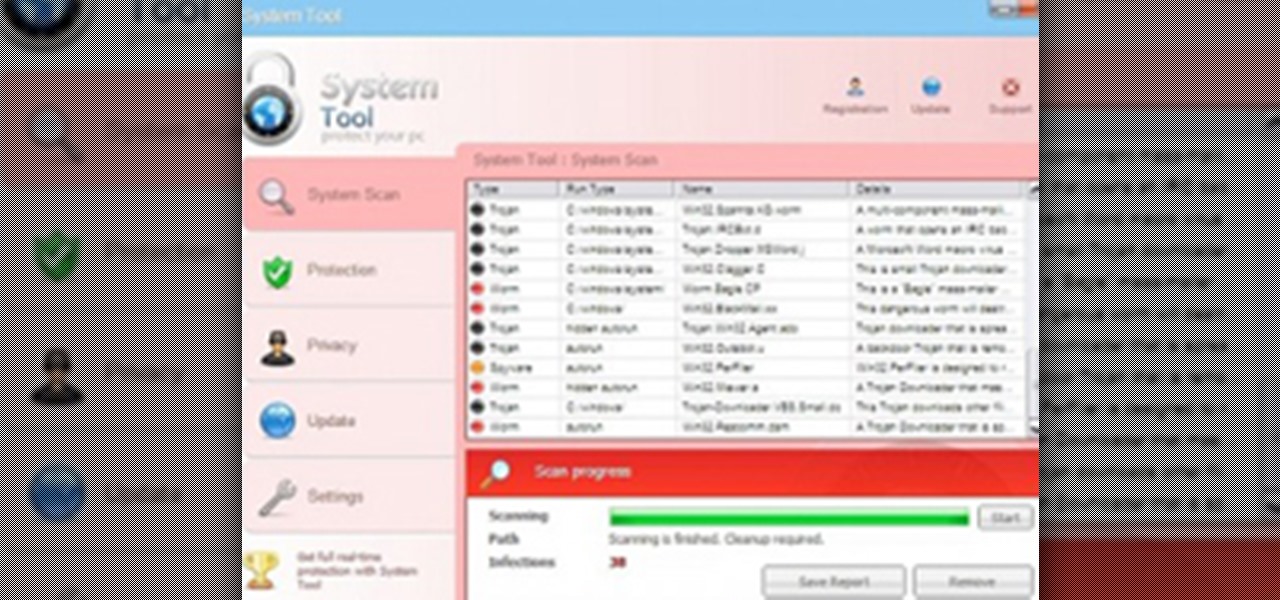
System Tool. It sounds like something your Windows computer might need, but it's the exact opposite.

As you progress in the world of information security, you'll find yourself in situations where data protection is paramount. No doubt you will have files to hide and secrets to share, so I'm going to show you how to use the GNU Privacy Guard (GnuPG or GPG for short) to encrypt and decrypt as you need. GPG is a great open-source version of Pretty Good Privacy (PGP), a similar application used for encryption, but licensing and patent problems led to the development of GPG in its wake.

The dreaded moment you hope never happens—someone has stolen your laptop. You could have private information, pictures, or even private information belonging to the company you work for, all lost forever. It can cause you pain, money, or even a job.

Movies like to show hackers breaking passwords with fancy software and ludicrous gadgets. The reality of busting passwords open is much more mundane. Simple as it may sound, most passwords are broken purely by guesswork. Check out this infographic from ZoneAlarm, as well as this list from the Wall Street Journal of the fifty most common passwords gleaned from the 2010 Gawker hack. If your password is on one of those lists, you need to change it. Right now.

Learn how to play the improve game "Quirks" at your next party in this free video that will keep your party guests entertained and thinking on their feet.

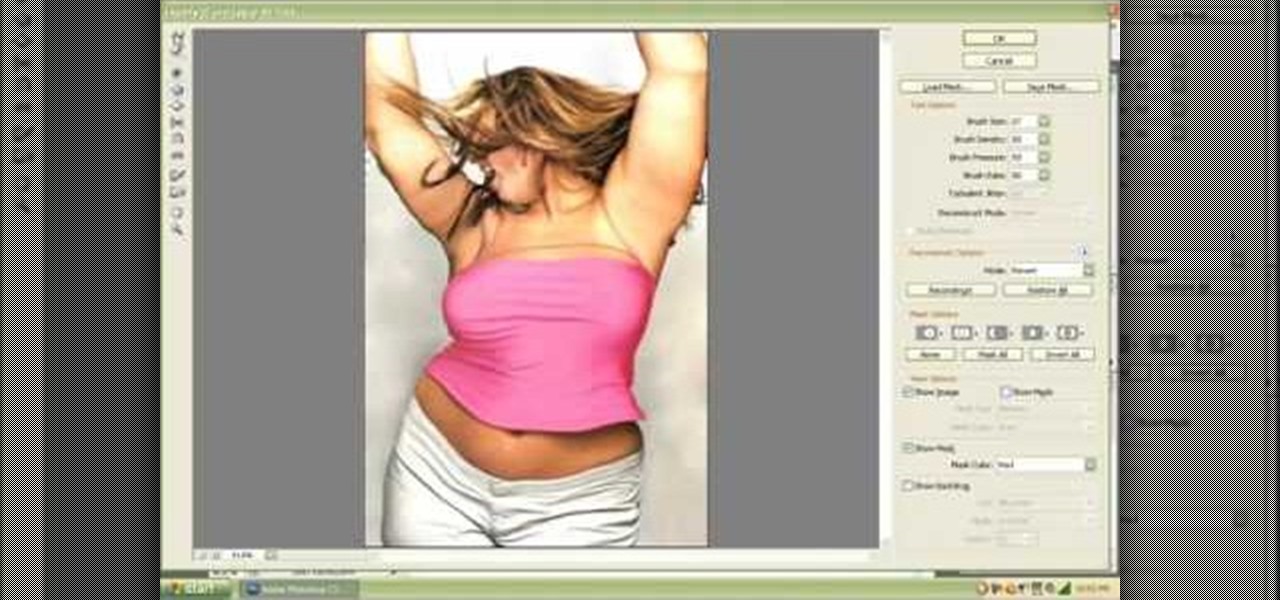
Want to know how to remove a digital tag from a garment for (in this case) a pair of shoes? This clip will teach you what you need to know. Whether you're new to Adobe's popular raster graphics editing software or a seasoned professional just looking to better acquaint yourself with the program and its various features and filters, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-step instructions, watch this free video guide.

I recently posted a link to what seemed to be a very useful guide on Lifehacker for creating a TOR button in Chrome. However, when I tried it myself, it did not work. Also, it lacked a warning on the limits of Tor, which I think are important. Therefore, I decided to create an updated and more comprehensive tutorial.

Skyrim really took the cake this year. With its awe-inspiring gameplay, much improved combat and leveling system, and a fresh new look, it's no wonder the game has already received a Game of the Year award. But for hardcore gamers, the fun may be over. You've played the game for thousands of hours, and have exhausted the entire game's main and auxiliary quests. You need more.

The lack of a search function within Google+ is driving me crazy. It takes me way too much time to find the posts I want to save and refer back to, and it's counter-productive for Google to launch their social networking product without an integrated search.

After the launch of Google+ and its ensuing attendant fanfare and rave reviews, Facebook seemed to undergo an identity crisis. On July 6th, Facebook failed to make waves with its "awesome" announcement - the new group chat and video chat features felt lame in comparison to the Google+ hangout and huddle features. Facebook also faced ongoing criticism for its perceived lack of privacy controls. Over on Quora, workers confirmed a lockdown of sorts at Facebook, for employees to work harder on fe...

We're ending the week with a lot of big announcements and updates. To date, Google+ has updated its name policy, but is still forbidding pseudonyms. Blocking people on Google+ became even easier, and yesterday, games on Google+ launched.

Facebook games are ostensibly all about connecting their players. Yet, in many ways they exist on an isolated island. That's one of the reasons traditional gamers and game franchises have avoided Facebook in the past. And all of the breakout hits so far on Facebook have been cheap PC game ripoffs from the 90s, like FarmVille and ports of other popular casual games.

Do you know how you are perceived by your peers? In real life and online? In the physical world, you could be seen as intelligent, thoughtful and hard-working, but on the Web you could be looked at as irrational, selfish and slothful. There's just something about the Internet that takes away a person's judgement and replaces it with impulsiveness—especially when it comes to Facebook.

Outside the realm of politics, where opposing sides are quite passionate and quite disagreeable, there are few areas in our society quite as divisive as Twitter. People who like Twitter love Twitter and are relentless in trying to co-opt the people they know into joining (this is both altruistic and an unsubtle attempt to boost followers).
LAKE JACKSON, Texas – 2012 Republican Presidential candidate Ron Paul was endorsed today by the Hon. Jordan Mason, City Councilman, Ward 4 of Rapid City, South Dakota.
In a riveting interview on TruNews Radio, Wednesday, private investigator Doug Hagmann said high-level, reliable sources told him the U.S. Department of Homeland Security (DHS) is preparing for “massive civil war” in America.

Let's face it, the world we live in is far from the fairy-tale land we want it to be, where violence doesn't exist and weapons are not needed. Our foremost goal in life out there in the scary world is simply to survive. And if we need a few tools to accomplish this, we should use them, right?

Sometimes, paying for the whole Xbox LIVE service might seem like a waste of money. You're constantly experiencing lag, you've got people modding and cheating, kids are being loud and obnoxious over the mic, and your kill-to-death ratio is getting dumped on. Basically, the whole multiplayer experience just isn't cutting it anymore—you want to go back to the classic world of single player. Well, there's always downloadable content—simply known as DLC.

It's no secret that water and electronics don't mix well, but somehow, people always manage to combine the two. I've had my fair share of water-damaged electronics, everything from cheap headphones to a desktop computer. My devices are getting dunked in water so much, it's like doughnuts in coffee. And I know I'm not the only one. That jam session with your favorite song will end really quick when your iTouch is chilling in the toilet bowl.

Originally made as portable convenience locks, padlocks are known for their cheap, simplistic and relatively secure design. Their construction is made up of a body, shackle and locking mechanism, with the shackle typically assuming a "U" shape to be easily linked to things like fences and chains.

Here's a delicious Byte of information for you. A proof of concept program on Linux was coded to exploit a known bug in how the Linux Kernel (versions 2.6.39+) handles permissions for the

Last Friday's mission was to accomplish solving HackThisSite, realistic 2. This second mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend take down a racist hate-group website.

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

Google is great. They provide us with tons of free services and open source APIs that we can code fun tools for, one of which I don't think gets enough credit: Google Voice.

Last Friday's mission was to accomplish solving HackThisSite, realistic 1. This is the first in a series of realistic simulation missions designed to be exactly like situations you may encounter in the real world. This first mission, we are asked to help a friend manipulate the website voting system for a Battle of the Bands vote count in his favor.

There was a huge ban wave recently on Xbox Live. In the unfortunate event that you decided to do something against Microsoft policy, and have consequently gotten yourself banned from Xbox Live, you may have come to the realization that doing whatever got you banned from Xbox Live in the first place was not worth the risk.

If you saw my last tutorial on retiring early and wealthy, you now know how anyone can invest a small amount of money over the course of their life, and by exploiting compound interest, achieve an extremely comfortable and easy going retirement. In Part 2, we are going to dive into something a little more risky: Tax liens.

This is it! That last basic mission. Last Friday's mission was to accomplish solving HackThisSite, basic mission 11. This final mission in the basic series was made to give us the skills and a place to apply our Apache server knowledge. This will teach us how to traverse through awkward and custom directory structures.

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.