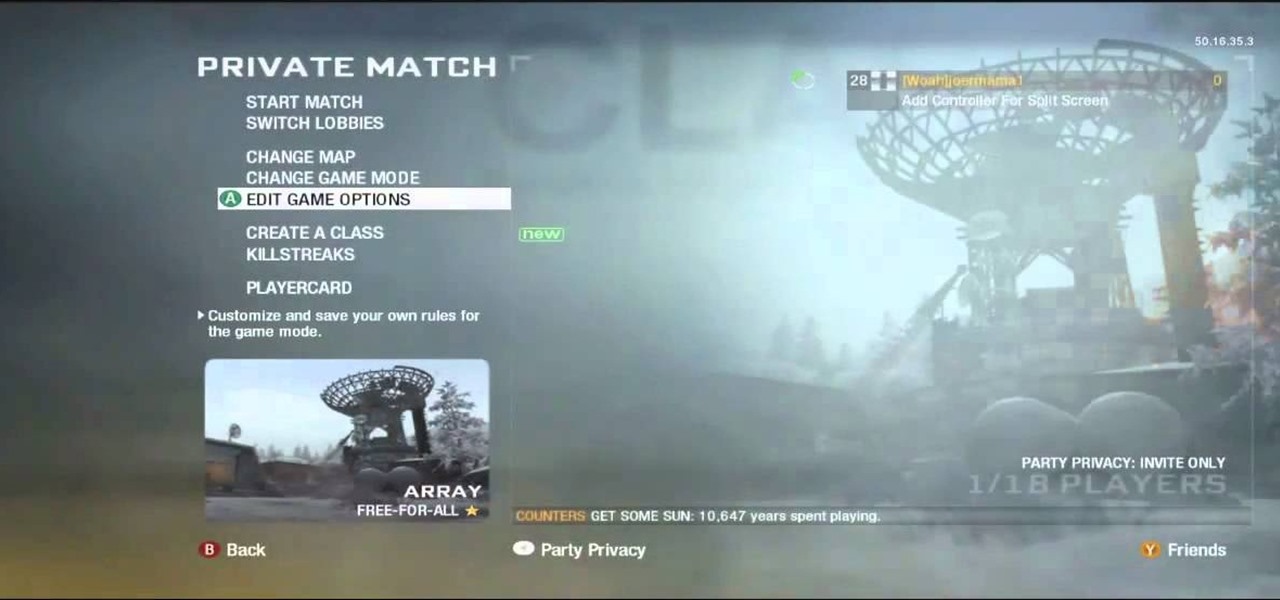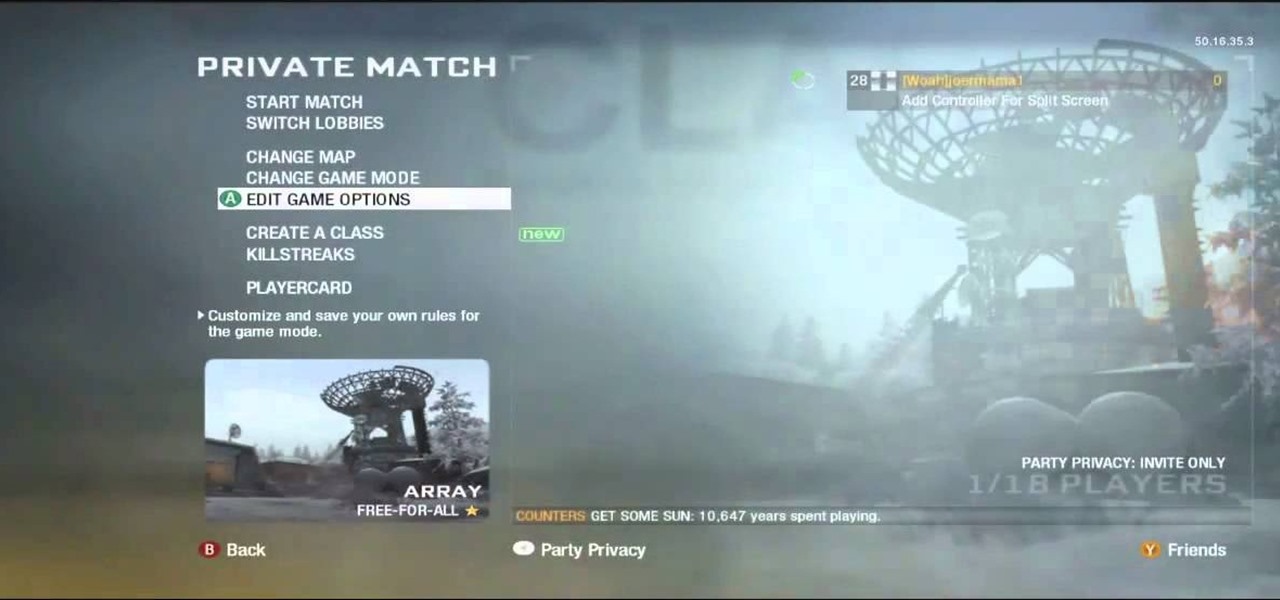
There aren't a lot of games with 3D maps where you can't break out of the levels in some way, and Black Ops is not different. This video will teach you a barrier breaker that you can use to get out of every multiplayer map in the game. Only use this in private matches unless you want it to go away!

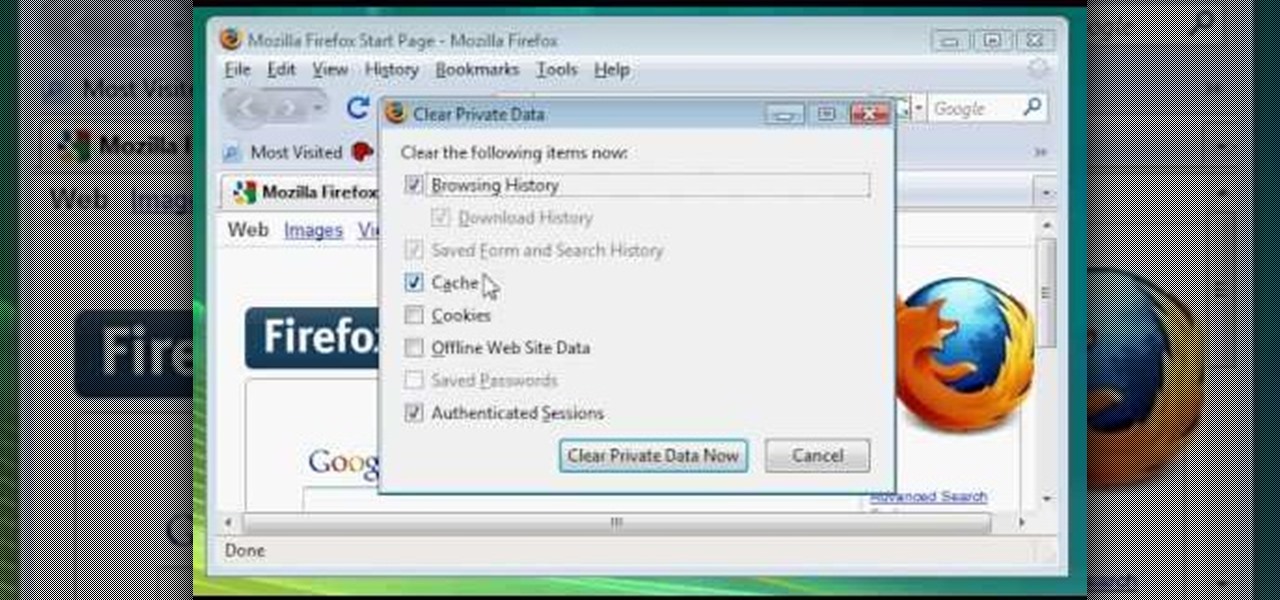
In this video, we learn how to clear browsing history and cache in Firefox and Internet Explorer. First, while in Firefox, go to the tools menu, then click on clear private data. In the new window, click on the items that you want to have cleared, then click "clear private data now". After this, the computer will clear out all the internet files. Next, while you're in Internet Explorer, go to the tools menu, then click on "internet options". Once in here, click the appropriate sections to cle...

Ever wish there were a way to upload a video to YouTube without making it available to anyone with an Internet connection? While you might know about the option to make your uploaded clips private, limiting their viewing to 25 users of your choosing, you might not know about the newly introduced "Unlisted" status, which allows your videos to be viewed by only those people who know the video's direct URL. For more information, watch this free video guide from Tekzilla.

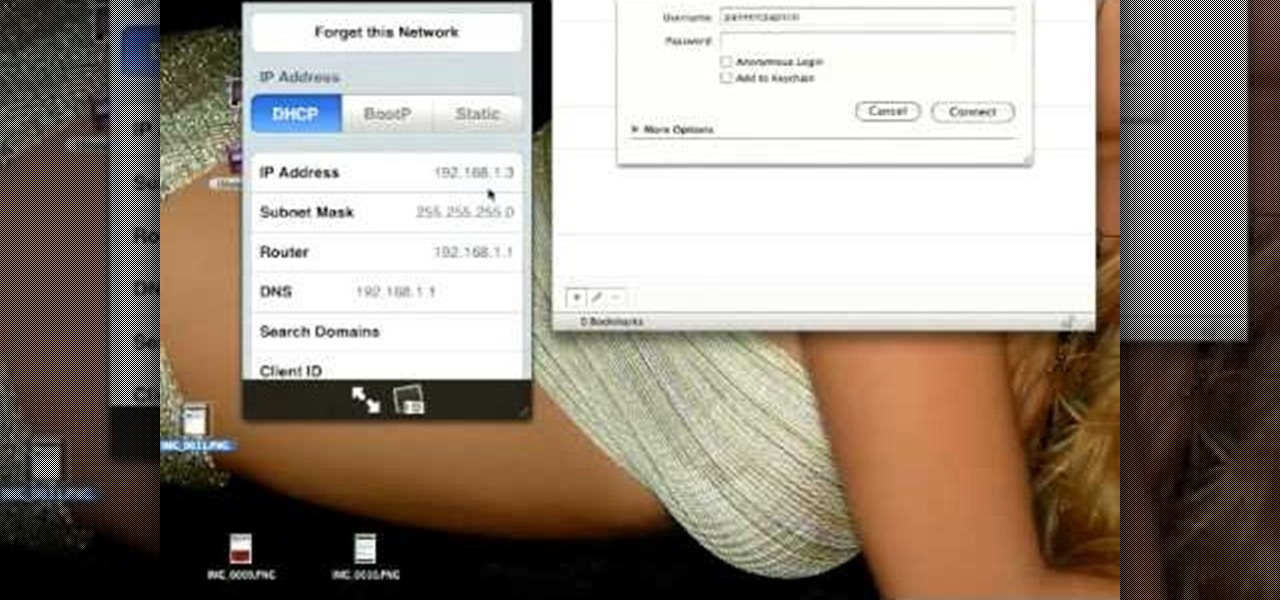
In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....
Lady Gaga is one of the most secretive women in show business, hiding behind her stage performer mask and outrageous costumes so often that we can hardly believe there's a real person underneath all that fluff.

If you're worried about having your private information taken away from you by hackers and other malicious people, this tutorial may help you. This tutorial will help show you how to easily use and understand the phishing filter in Internet Explorer 8. It only takes a couple of clicks to activate and can be the difference between making sure your private information is secure or out in the open for others to use. Good luck and enjoy!

This video tutorial from ChaminadeENN shows how to set your Facebook account to private mode. First what you need to do is to sign in to your Facebook account.

You can use surveillance skills to pursue a career as an investigator or to spy on whoever you like. You will need to have a mobile means of making observation and this might include things like pen and paper, camcorder or camera.

Here Danny Beales shows you how to quickly clear your Firefox cache and cookies. To clear your Firefox cache, do the following: Go to Tools Clear Private Data Select which data you would like to have cleared, and click on Clear Private Data. Your cookies and/or cache has been cleared. Remember to do this from time to time, because it will help speed up your browser's performance as well as keep harmful cookies from tracking your browsing.

This video shows you how to easily delete cookies from your browser. First thing you have to do is open the web browser you usually use (the video shows how to delete cookies from Firefox) and go to the Options tab in the upper menu. Then choose the Clear Private Data or Clear Recent History item. In the pop-up window, check Cookies and Cache and then press the Clear Now button. The Clear Private Data/ Clear Recent History window also can be opened by pressing CTRL+SHIFT+DEL. That's it! Good ...

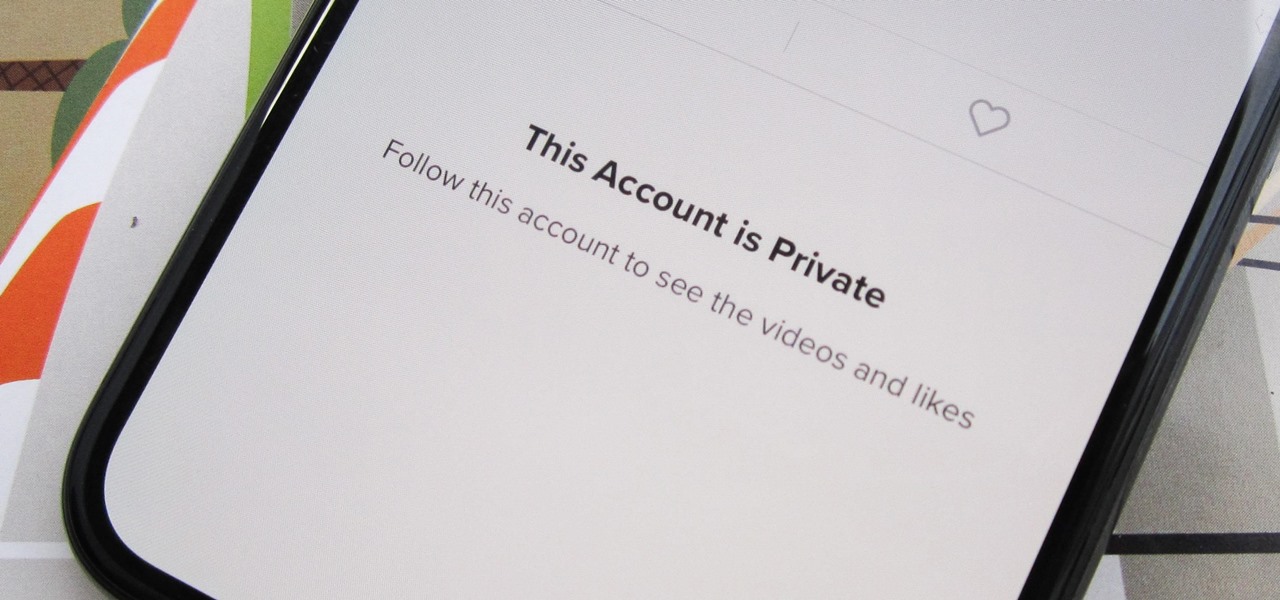
Can you trust every user you come across on TikTok? The answer to that may depend on how use the service, but the real question is — can you trust every user that sees your content? Not everyone on TikTok is someone you want viewing or interacting with your content, and there's a way to prevent them from doing so.

Hi all, Pro Hackers/Crackers, Let's see how we can use batch for our own Protection instead of exploiting someone with it.

Now that you've updated your iPad, iPhone, or iPod touch to iOS 8, there's a lot of cool new things to explore. If you felt a little overwhelmed from all of the detailed information available in our Coolest Hidden Features of iOS 8 post, then I've got a simple breakdown of all of the new features available with quick links to their walkthroughs and pictures, if available. Watch the short video roundup, or skip below for the list.

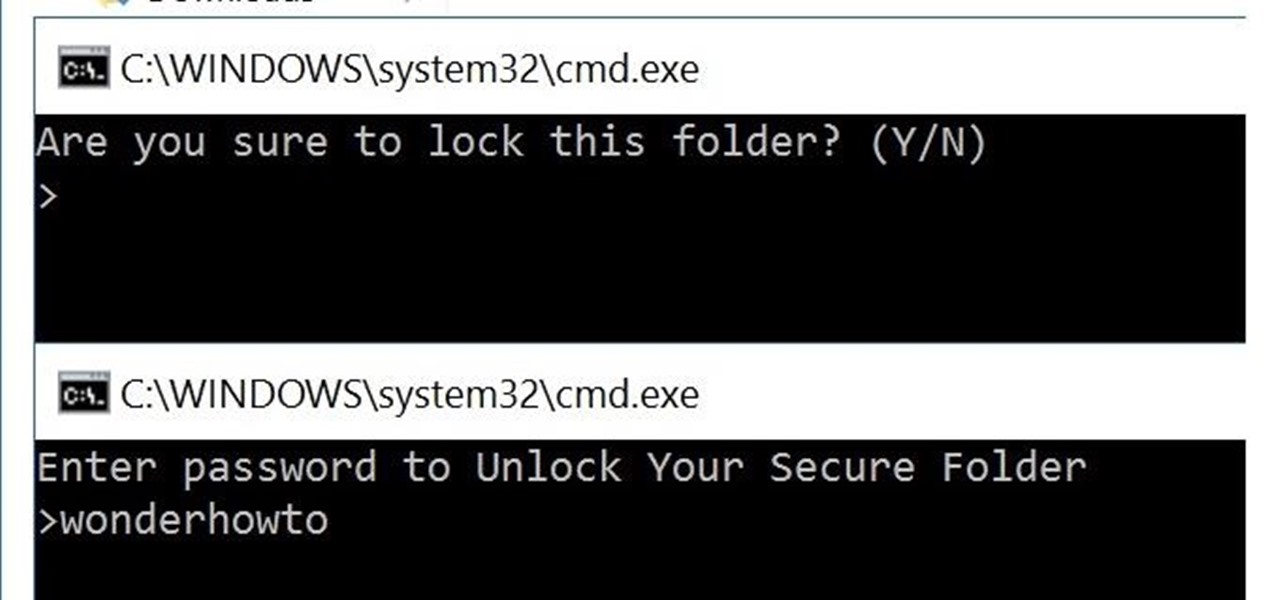
You can easily lock any folder on your Windows computer with a simple Notepad hack. By creating a batch file, you can hide a folder and require a password be entered before it becomes visible and accessible. This is a great tool for locking sensitive information, like pictures, financial statements, and a lot more.
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

Smartphones have so much sensitive information attached to them. If you share your home with others, then you know the pains of trying to keep anything private. Photos are surely among the things you'd prefer to keep to yourself, so OnePlus has you covered.

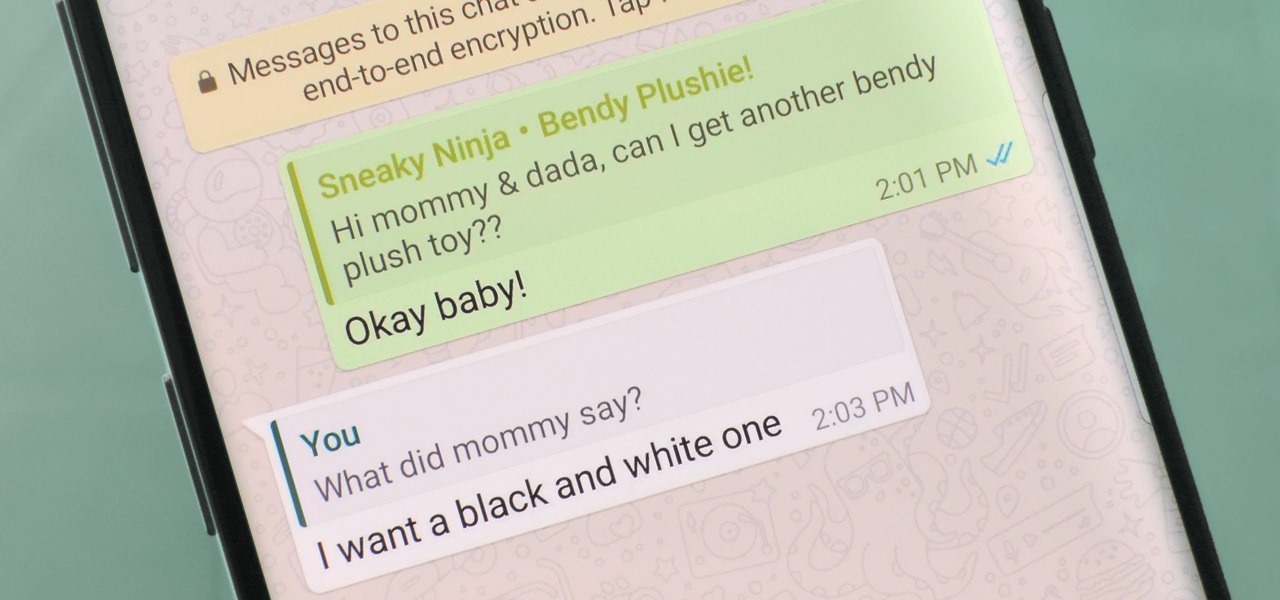
Group chats in WhatsApp are great for communicating with multiple people at once, but that can be a blessing and a curse — any message you send will be seen by everyone, and that's not always ideal. Thankfully, there's a new feature that lets you respond to group messages privately.

When it's most important for me to browse the web incognito, I always seem to forget to enable private browsing. If that sounds like you, it's time you stop making that mistake for good. Manually deleting the cache and browser history is a thing of the past, and as it turns out, so is manually switching to incognito mode.

It's easy to forget sometimes that even when you're sitting in the basement playing Grand Theft Auto 5 Online that you're not really alone. Everything you say into the mic can be heard by anyone else in that same session.

Remember TwtRoulette? TwtRoulette was an online app that turned you into a so-called Twitter spy, letting you peruse someone's own timeline feed exactly how they saw it themselves. So, if you wanted to see what tweets Ashton Kutcher was seeing in his home timeline from the 700+ people he follows, you could.

Data thieves don't have to be programming wizards to get their hands on your personal information. They often find hard drives that contain financial and other sensitive data at flea markets, charity shops, the city dump—even on eBay. In this video tutorial, PC World explains how to completely erase sensitive data from old drives before recycling or discarding them. Wipe your old hard drives with this how-to.

Circular breathing will enable you to play your didgeridoo continuously. In this movie we'll show you how easy it is by breaking the process down in to small simple steps.

If you prefer to use Google or another search engine for everyday browsing in Safari but would also like a more secure browsing experience for all your secret searches, there's a simple way to switch between them quickly while also adding additional layers of security on top of your already clandestine browsing.

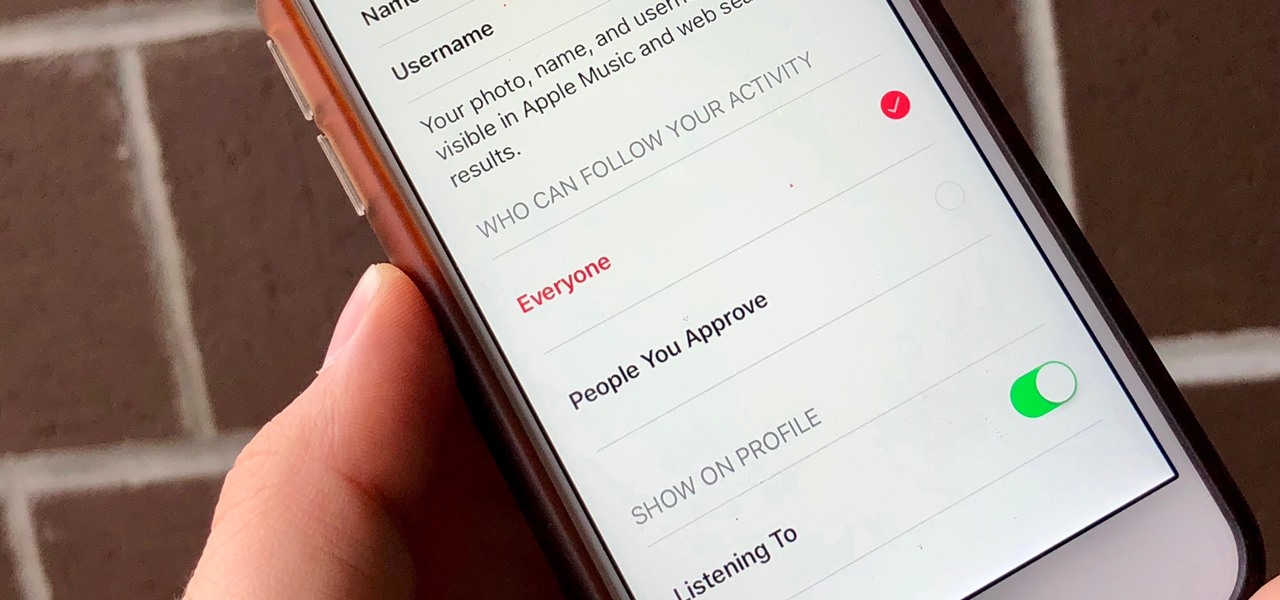
Apple Music, Apple's answer to Spotify, has many interesting features packed in to make that $9.99/month price tag as attractive as possible. One of those features is geared towards social listeners — those who want to follow other Apple Music users and who want to be followed back. But here's the thing: how do you know if your account is public or private?

Remote Desktop gives you access to your Windows 8 PC or device from wherever you are to run your applications and access your files remotely.

If you're interested in joining or creating a fantasy football league, take a look at this guide on how to use leagues in ESPN Fantasy Football and learn the differences between the leagues. You can choose to play in a public or private league, depending on if you want to limit your fantasy league to your friends and family or if you want to play against other team owners you meet online.

What do President Obama, the Dalai Lama and Justin Bieber have in common? Why, they're all on Twitter, of course. Join the party. Whether you're new to Twitter's popular microblogging application or just missed a few of the essentials along the way, you're sure to benefit from this free video tutorial, which offers detailed instructions on how to create a protected Twitter feed.

In this video, learn how to view private MySpace profile pictures. The process is easy & quick. In no time you will surfing MySpace freely with no privacy preferences to stop you.

Jared of the TechCentric crew gives you the lowdown on the basics of keeping your VoIP conversations secure and, on the other side of things, how to use the Cain VoIP sniffing application. For detailed instructions on keeping your VoIP conversations private, watch this hacking how-to.

Hello guys, today I wanna share how to create a drag and drop with listbox using VB.net. Just copy and paste the following code under public class.

Lending someone your phone to make a call is always an awkward situation, as you closely monitor them to make sure they stick to a phone call rather than wandering off into private applications like your photo or messaging apps. You don't necessarily want to eavesdrop on their conversation, but trusting people with your phone is difficult, especially if you have some risqué or embarrassing pictures stored on it.

Apple's new iOS 8 has a ton of new features, and so does their revamped Safari app, only some of the features aren't quite as obvious as others. In this guide, I'll show you my 5 favorite Safari secrets in iOS 8 for your iPad, iPhone, or iPod touch.

As you may know, your iPhone stores data on your location from time to time. If you'd rather that information be kept private, watch this video for some helpful instruction on how to protect your location information. Encrypt the information being gathered by iPhone tracker.

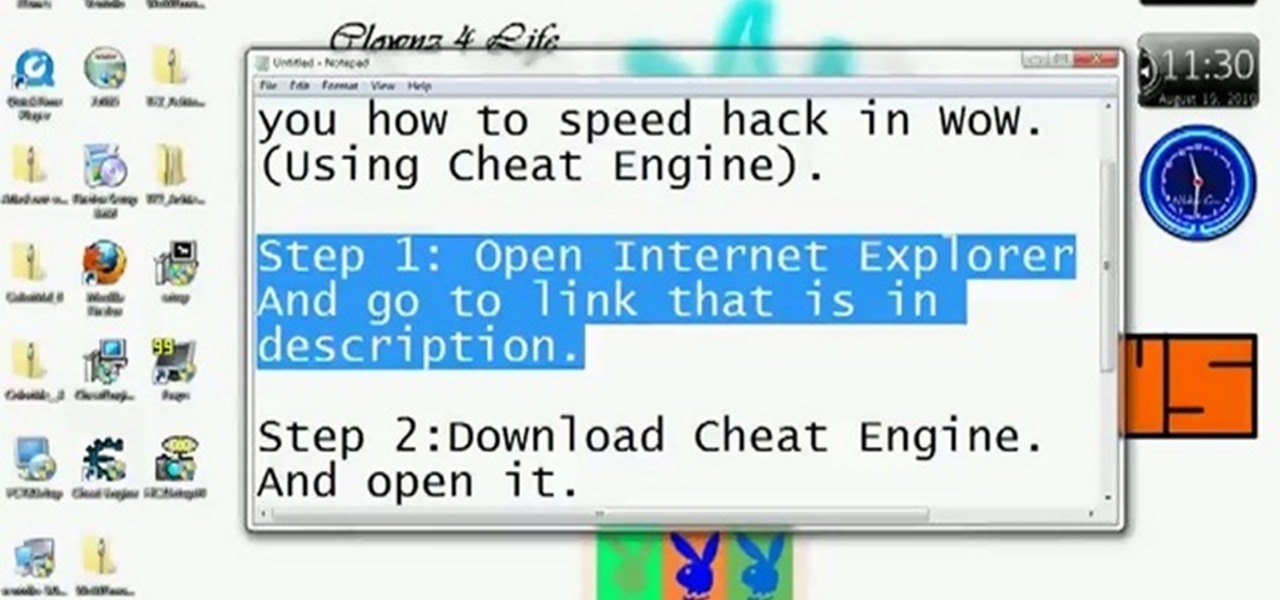
Be careful! If you use this on a public World of Warcraft server, you might get caught and banned by the GMs. However, if you are on a private server, or don't mind the risk, here's how you can use Cheat Engine to hack the game.

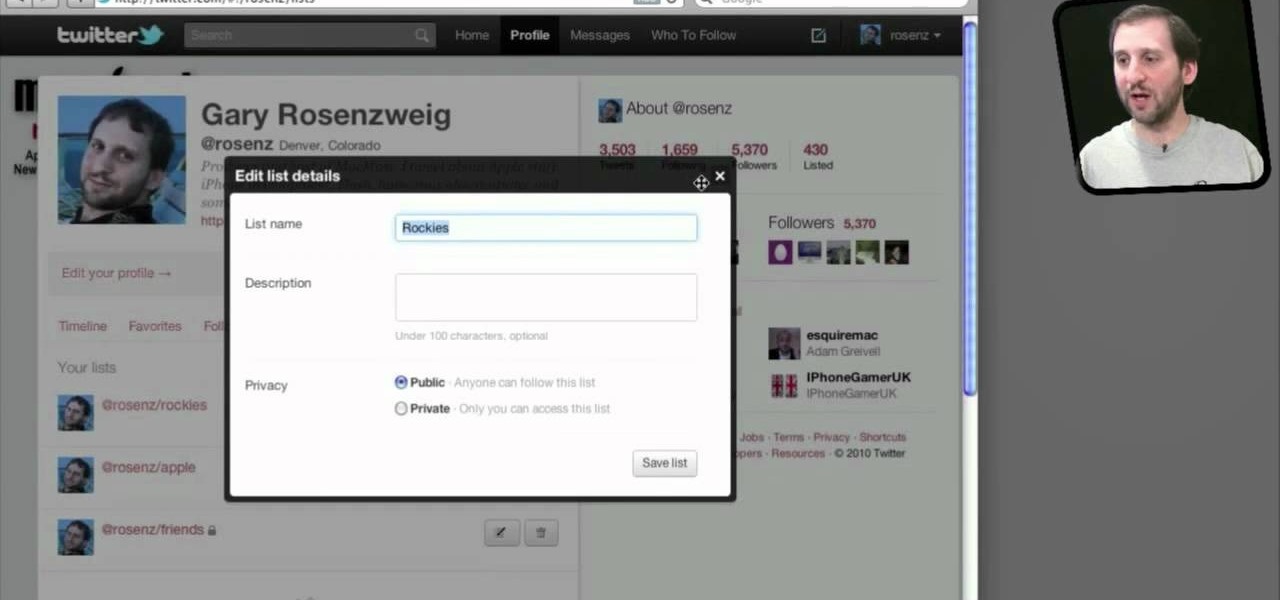
Do you spend a lot of time on Twitter? You can sort and organize the people you follow by grouping them together into Twitter lists and then viewing only that list. These lists are arbitratry categories that you create and can be viewable by others, or made private. You can also view other public lists that people have made. This video shows you how.

When you use Gmail, Google Maps, Google Documents or any of the other Google products, you send trackable information about yourself to Google. By going in and configuring your account settings in Google Dashboard, it's possible to manage the information about yourself that you send them. This informative video shows how.

Big Brother is closer to becoming a reality than ever before, especially in the UK. If you're concerned about whether you phone is being tapped, watch this video to learn about steps you can take to find out whether your phone has been bugged or not and make sure your communication remains private.

Protect your Facebook posts! This clip will show you how it's done. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.

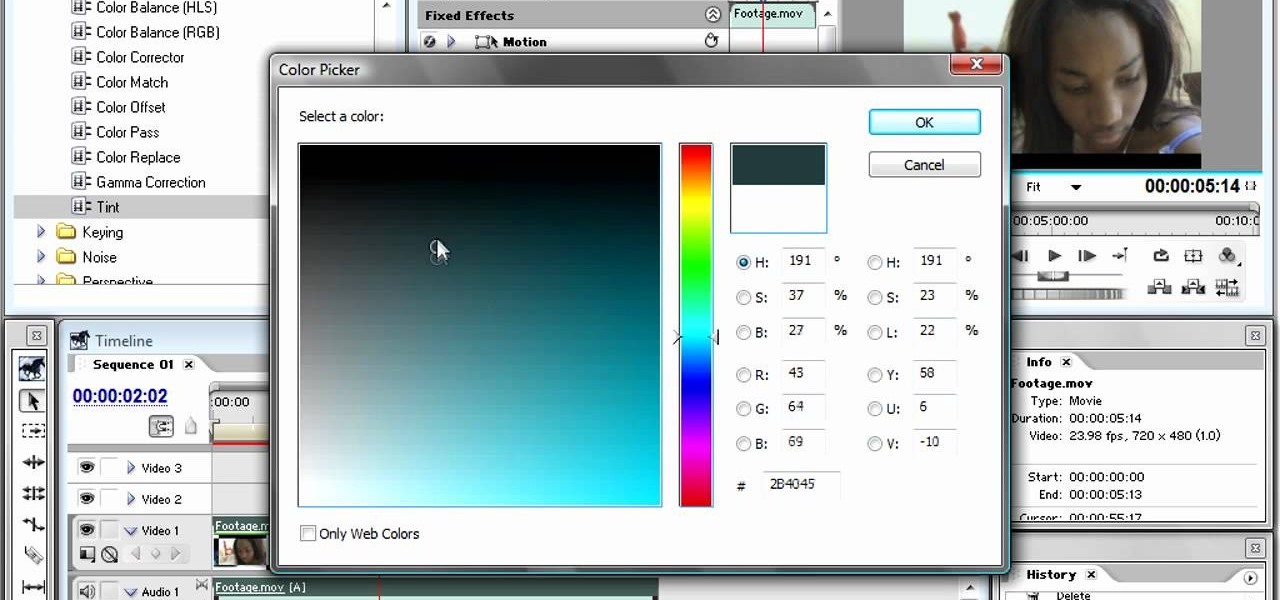
The bleach bypass effect is a classic, and is large part of what gave Saving Private Ryan it's distinctive look. This video will teach you how to apply bleach bypass yourself using Adobe Premiere Pro. Give your video that old-school look using the most modern of technologies.

Curious about all those jailbreak videos and what they mean when they say "SSH into your phone"? In this video, learn how to SSH into either an iPhone, iPhone 3G, or an iPod Touch. Additionally, learn how to download videos from Cycorder on an iPhone and iPhone 3G with Cyberduck. Links & codes you will need: