
How To: Create a Drag Drop with ListBox Using VB.Net
Hello guys, today I wanna share how to create a drag and drop with listbox using VB.net. Just copy and paste the following code under public class.


Hello guys, today I wanna share how to create a drag and drop with listbox using VB.net. Just copy and paste the following code under public class.

Apple's new iOS 8 has a ton of new features, and so does their revamped Safari app, only some of the features aren't quite as obvious as others. In this guide, I'll show you my 5 favorite Safari secrets in iOS 8 for your iPad, iPhone, or iPod touch.
As you may know, your iPhone stores data on your location from time to time. If you'd rather that information be kept private, watch this video for some helpful instruction on how to protect your location information. Encrypt the information being gathered by iPhone tracker.
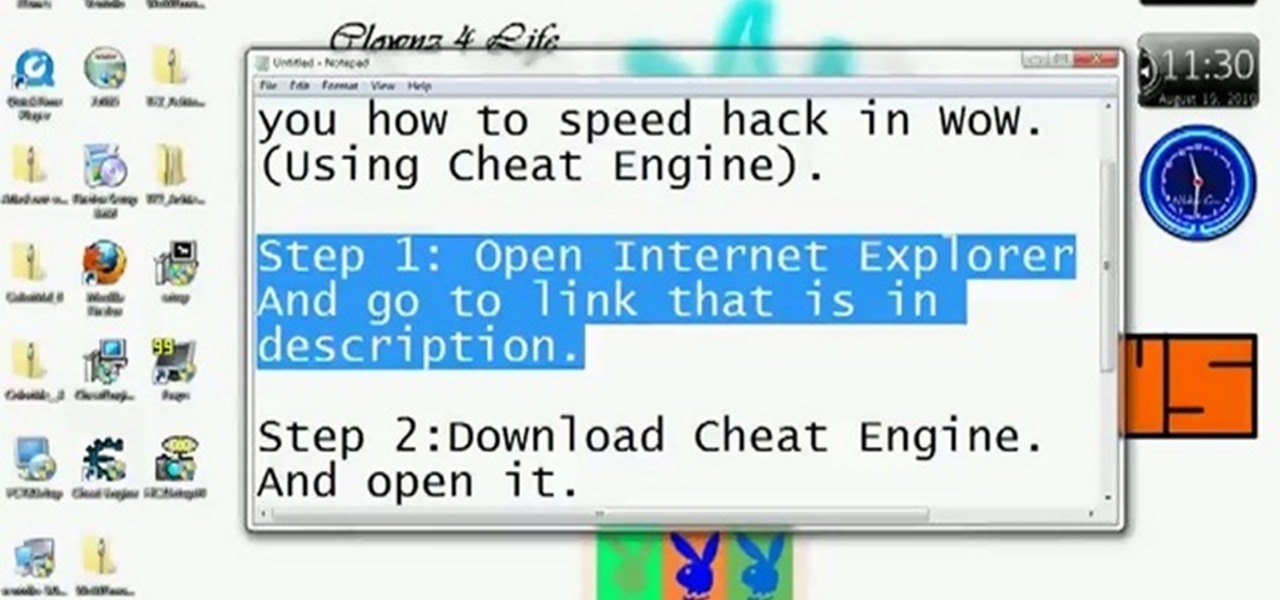
Be careful! If you use this on a public World of Warcraft server, you might get caught and banned by the GMs. However, if you are on a private server, or don't mind the risk, here's how you can use Cheat Engine to hack the game.
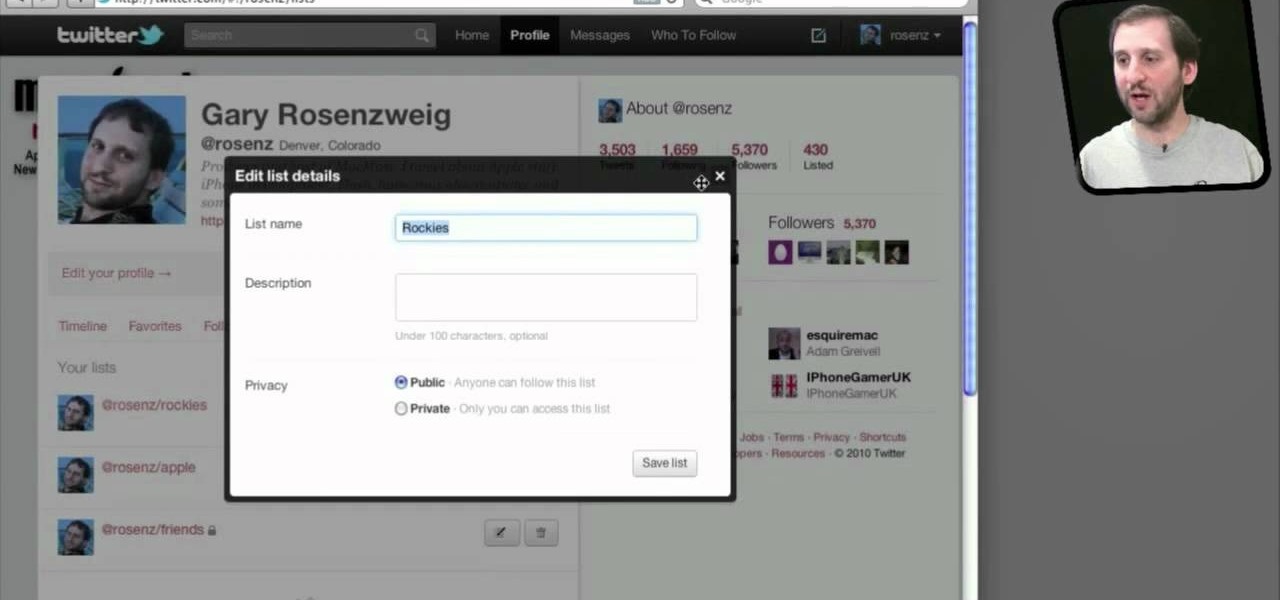
Do you spend a lot of time on Twitter? You can sort and organize the people you follow by grouping them together into Twitter lists and then viewing only that list. These lists are arbitratry categories that you create and can be viewable by others, or made private. You can also view other public lists that people have made. This video shows you how.

When you use Gmail, Google Maps, Google Documents or any of the other Google products, you send trackable information about yourself to Google. By going in and configuring your account settings in Google Dashboard, it's possible to manage the information about yourself that you send them. This informative video shows how.

In this tutorial, we learn how to keep personal information private when using Facebook. It's an easy process and this video presents a complete guide. For more information, including a full demonstration and detailed, step-by-step instructions, watch this helpful home-computing how-to.

Big Brother is closer to becoming a reality than ever before, especially in the UK. If you're concerned about whether you phone is being tapped, watch this video to learn about steps you can take to find out whether your phone has been bugged or not and make sure your communication remains private.

Protect your Facebook posts! This clip will show you how it's done. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.
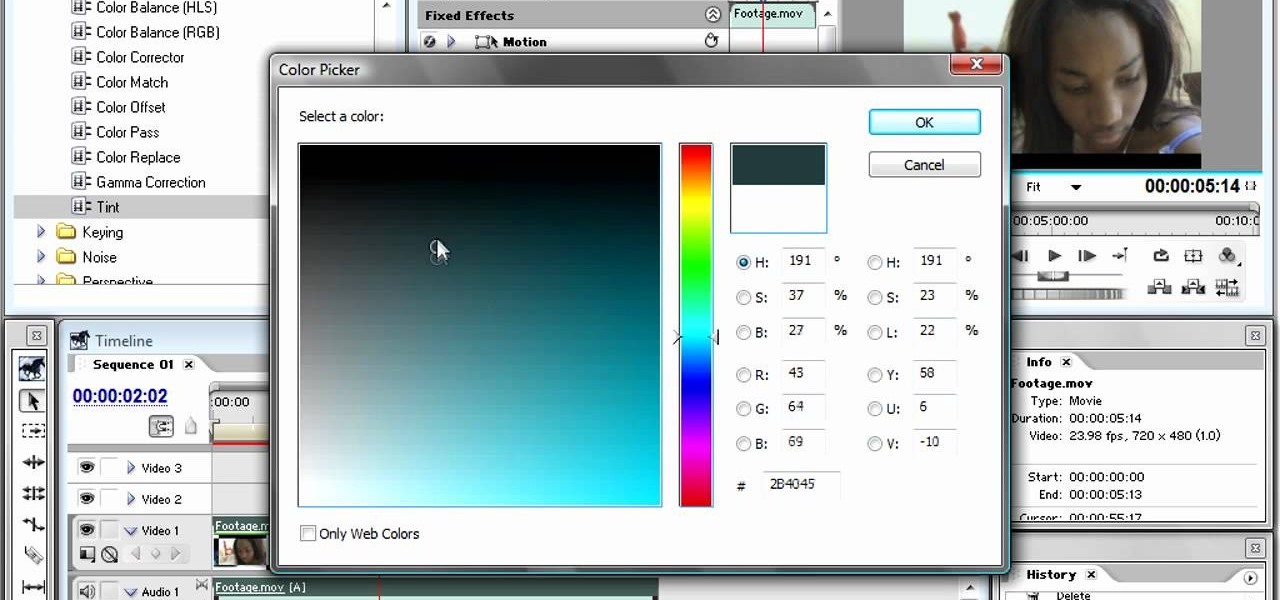
The bleach bypass effect is a classic, and is large part of what gave Saving Private Ryan it's distinctive look. This video will teach you how to apply bleach bypass yourself using Adobe Premiere Pro. Give your video that old-school look using the most modern of technologies.
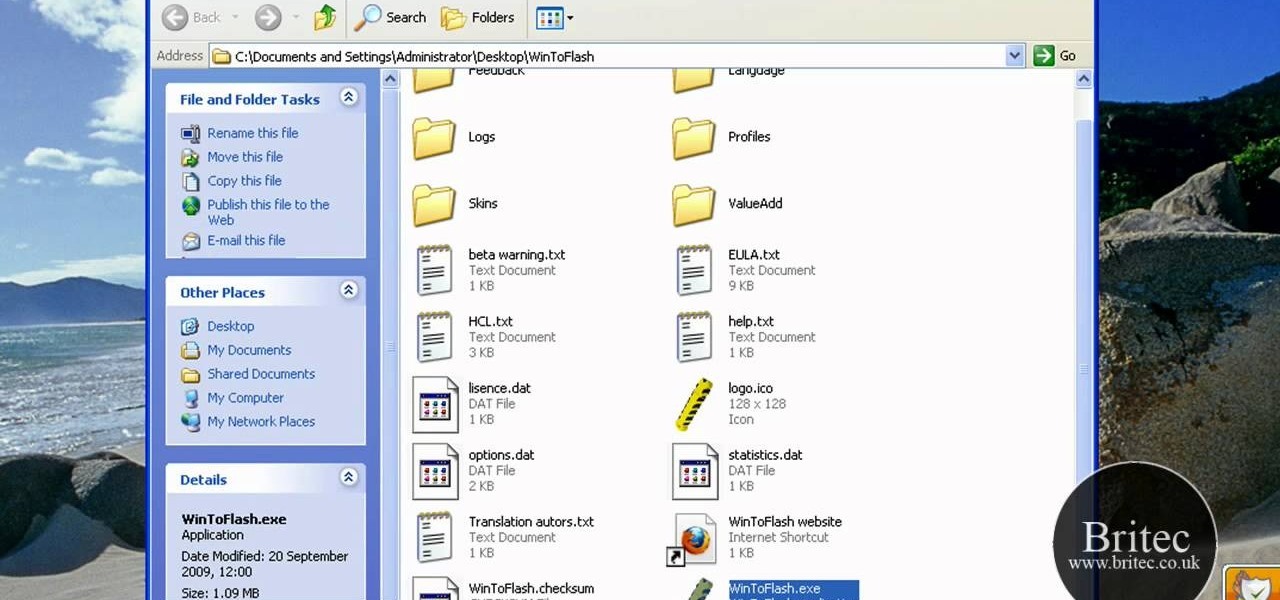
This is a how to video to prepare a bootable USB installer for windows 7/XP using wintoflash. Here are the steps to do.
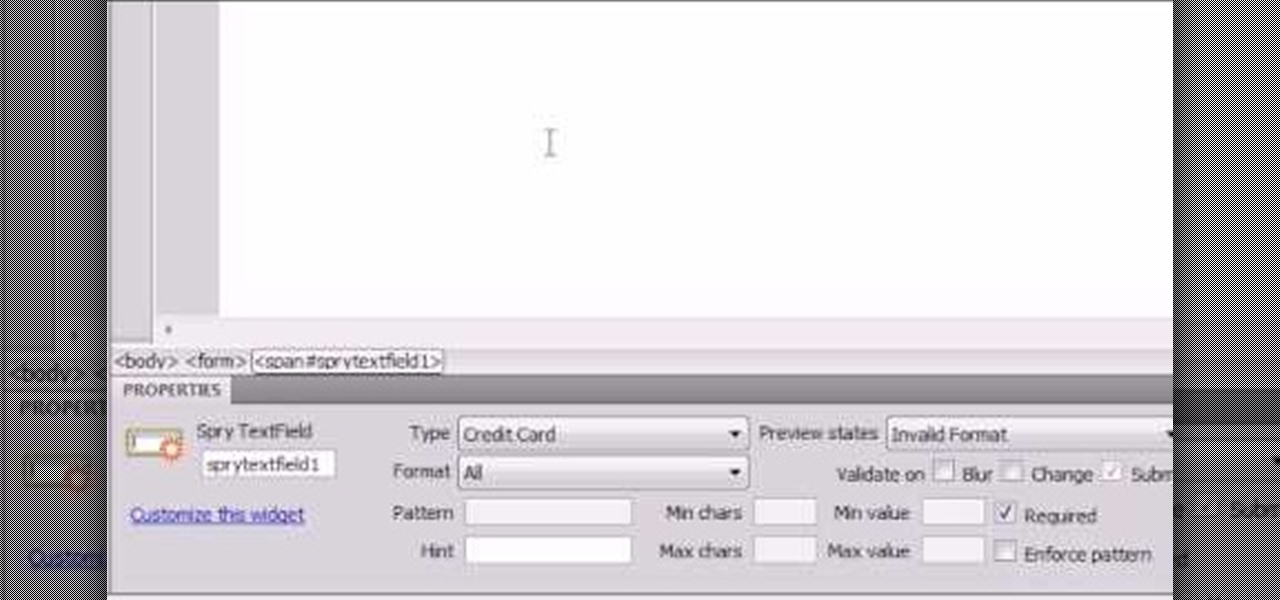
Here the New Boston shows you some tips about using the Spry Validation Text Field. To begin you will go to the Spry Validation Text Field, on Dreamweaver CS4. Looking at the bottom of the page notice the various options that are available for Properties. You find drop-down boxes for Type, Pattern, Minimum or Maximum values, Required, Enforce pattern, Format, Validate on, Blur or Change and Preview States. You can see the types of text available for validating by left mouse clicking the Type ...
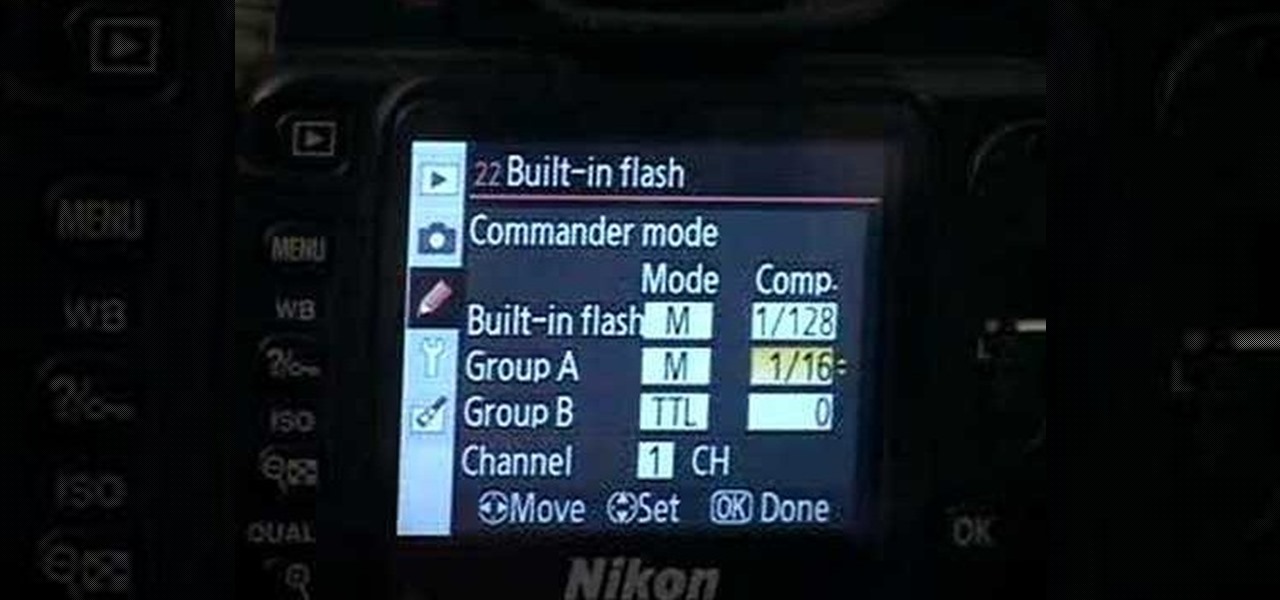
These are the steps required to set your D80's pop-up flash. First, go to the "Custom Shooting Menu." Then you choose #22 on the screen: "Built in Flash." Choose the "Commander Mode" option. The modes that are available for the pop-up flash include TTL, AA (Auto Aperture) M (Manual) and Off (no flash). If you are using an external flash unit, you use either group A or B. The light frequencies and proper settings are related to how much light compensation is needed. +3. 0 is high power, 1. 1 i...
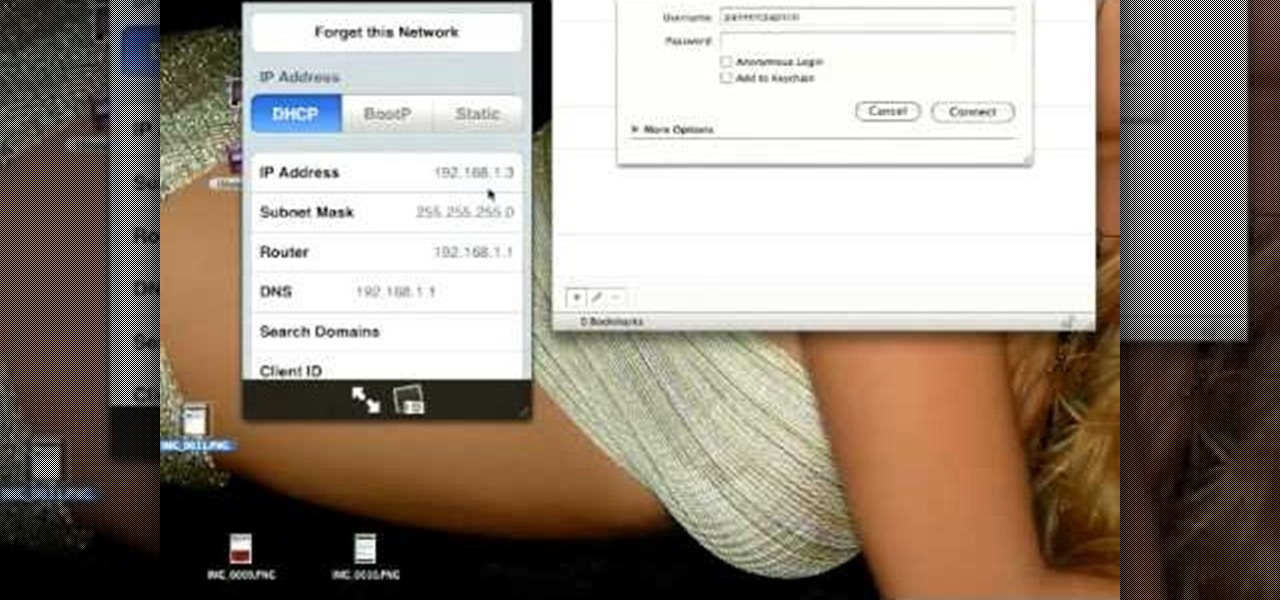
Curious about all those jailbreak videos and what they mean when they say "SSH into your phone"? In this video, learn how to SSH into either an iPhone, iPhone 3G, or an iPod Touch. Additionally, learn how to download videos from Cycorder on an iPhone and iPhone 3G with Cyberduck. Links & codes you will need:
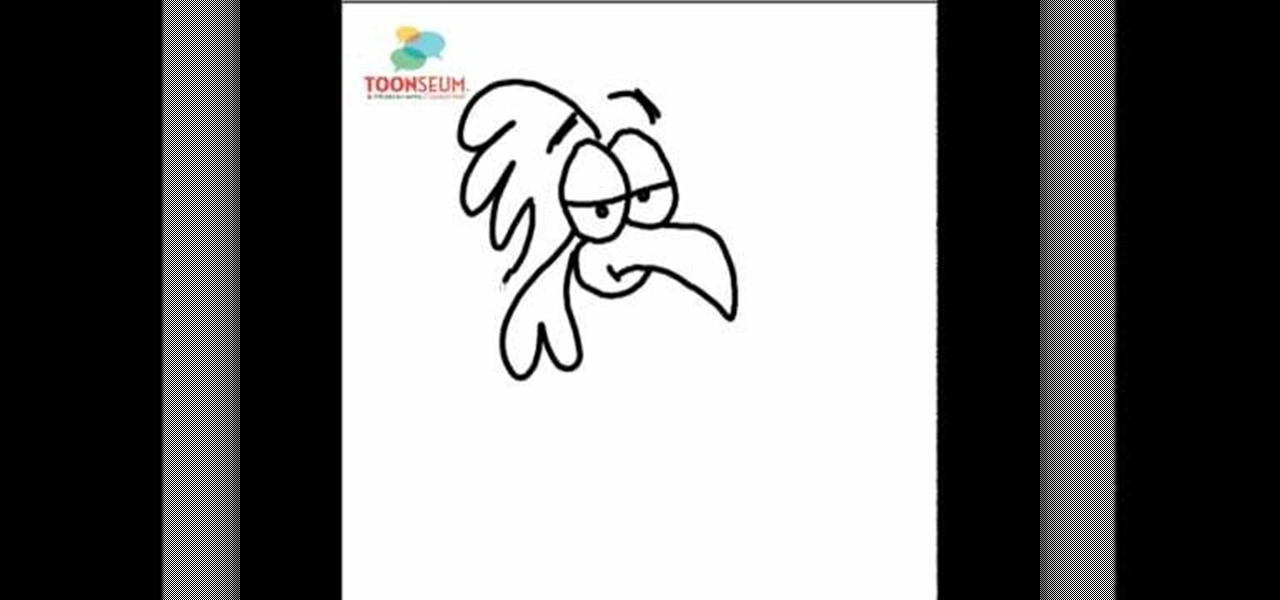
the video starts out with Joe talking you through the basic steps in how to draw or sketch a chicken. Starting with the eyes, shaped like to ovals, side-by-side, touching. Drawing a curved line all the way across each one to represent the eyelids and two small dots to form the eyes. Next draw a sharp curved line down from the eyes forming the beak, with a c like shape towards the back, connecting back to the eyes completing the formation of the beak. Draw an upside down, narrow heart at the b...
Video demonstrates tutorial of how to hide the logical drive icons in Windows. In the demonstration there is two partitions C and D and also there is a DVD drive, DVD Rom and DVD Writer. Here drives C, D and F from My computer is going to be hidden with help of utility called “No Drives Manager”. If you don’t want your young ones to access some of your important data you can hide it. It will just be hidden. This means if go to the address bar and types the name of the drive you can go to that...
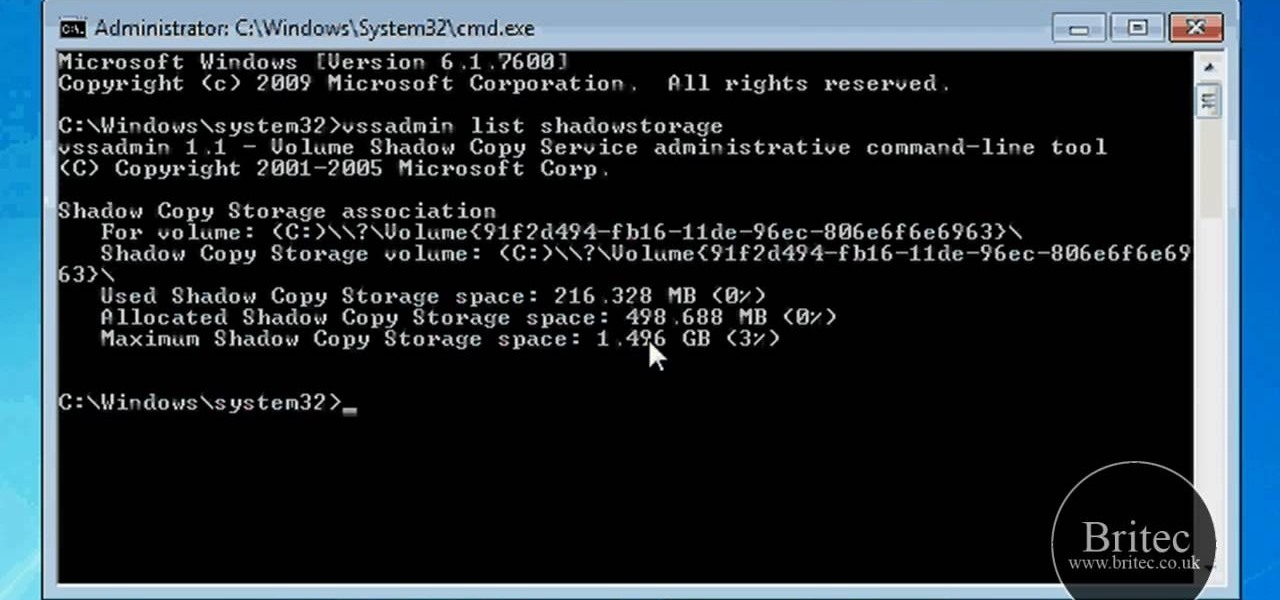
Is your computer getting up in its years and running slower than when you first purchased it? Your problem may lie in the machine's System Volume Information. Watch this video to see how to reclaim or resize disk space from SVI.

Woops! Make a mistake? Whether you’ve made a mistake, like writing the wrong year or wrong amount, or want to set up automatic bill payments or direct deposit, you may need to void a check. In this tutorial, learn how to properly void a check.

Attention aspiring screenwriters! In this tutorial, learn how to sell that script. You may have written the next Hollywood blockbuster – but unless you can finance the film yourself, you’ll need to sell the screenplay to a producer who can make it come to life.

If you want to stop telemarketers from calling, use this guide and try a multi-pronged approach. You Will Need
Have you been typing at computers for so long that your handwriting has become unreadable? Follow these steps to make your handwriting beautiful again. This Howcast guide demonstrates how to improve your handwriting - just follow the steps!

While it may be tempting to tell your boss where he can stick his letter opener when you’re ready to quit, it’s not a great career move. You will need a job to resign from, good stationery, acting skills (optional). Submit resignation. Submit resignation.

Keep private info from prying eyes and earn some peace of mind when you safeguard your PC or Mac against nosy intruders. You will need several great passwords, virtual desktop software, snoopware blockers, a screen filter, a mirror, a healthy sense of paranoia, WPA encryption, and an understanding IT specialist.

There is a security flaw with any Apple iPhone running firmware version 2.0.2. This flaw potentially gives a person access to your email account and contacts when you have your iPhone locked. This video demonstrates a simple, but impermanent, fix for stopping others from accessing your private information. To protect your own Apple iPhone, watch this tutorial.

This sequence of instructional videos provides a near comprehensive lesson on how you can change your voice from that of a male to that of a female. This video series is aimed at aiding transgender individuals, but is also useful for people who want to learn to do really great voice exercises and impersonations.
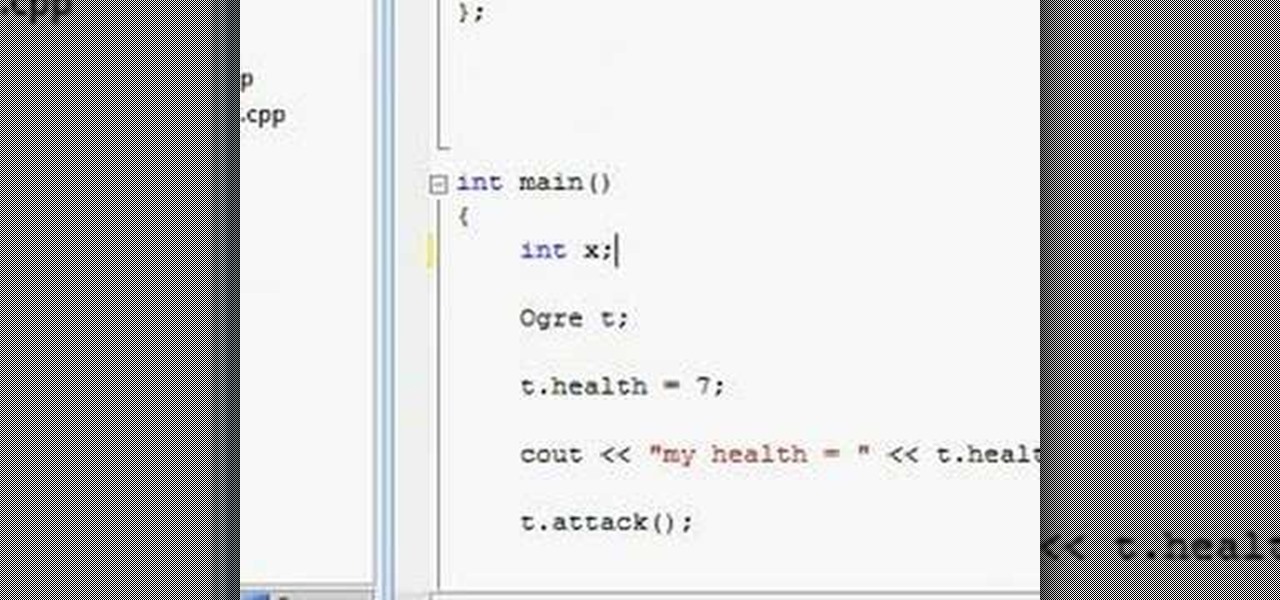
Watch this video to learn how to create OOP design with C++. This video also covers public and private variables and functions.

Today's word is "reticent". This is an adjective which means not revealing one's thoughts, or being reserved.
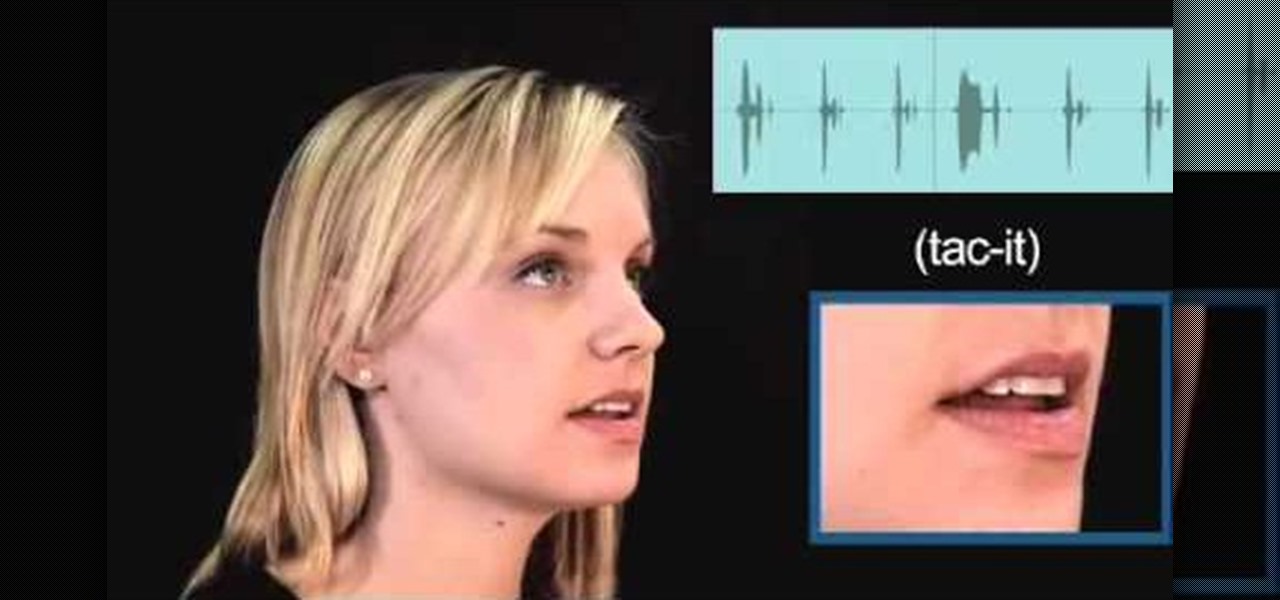
Today's word is "tacit". This is an adjective which means implied or conveyed without words.
In this AeroCast episode, UND Aerospace discusses the Slow Flight maneuver as performed in the Piper Warrior (PA-28-161), referencing the procedures and standards outlined in the UND Warrior Standardization Manual. All performance tolerances are based on the performance standards set forth by the FAA Private Pilot Practical Test Standards. Since the most critical phases of flight occur at airspeeds less than cruise, a pilot must always be comfortable with his or her airplane’s handling charac...

In this AeroCast episode, Anthony Bottini discusses the Power On Stall maneuver as performed in the Piper Warrior (PA-28-161), referencing the procedures and standards outlined in the UND Aerospace Warrior Standardization Manual. All performance tolerances are based on the performance standards set forth by the FAA Private Pilot Practical Test Standards. Power On Stall practice is vital in increasing a pilot’s proficiency in regards to stall recognition and stall recovery techniques during an...

Unless you have your own private airport (I’m looking in your direction John Travolta) then you will most likely have to coordinate your takeoffs and landings with all the other air traffic using your specific airport. Whether it be a towered or non-towered airport, this latest UND Video Standardization Lesson is designed to help you, the student pilot, become familiar and hopefully more comfortable with Airport Traffic Pattern operations.

Need internet access and you don't have a login? Hack into a private or controlled network with this tutorial. Thefixed.org also shows you how to build a smoke bomb!

Find the biggest files on your computer ordered by size. Learn to order folder by filesize so you can find the ones harboring the most diskspace terrorists. Learn to clear up your private data automatically and wipe it clean from being undeleted.

Technically it's the California Chardonnay vs. the French White Burgundy but since they both use the Chardonnay grape it's still a battle. In this video Gary tastes and compares two against two: 2004 Pessagno Sleepy Hollow Chardonnay and 2004 Beringer Private Reserve Chardonnay vs. 2003 Caves De Colombe Chassagne Montrachet and 2001 Matrot Puligny Montrachet Comb Ottes. See which Gary puts on top.

Becoming a chess master is very hard to do, and one of the most important things you need to learn is chess notation. Chess notation will help you study great chess games and learn classic moves and strategies. Check out this video and start studying, and who knows? You may be the next Bobby Fischer.
Many apps, including Facebook, Twitter, and Facebook, do not let you download videos, even if they are living on your own account. Saving these videos usually requires a third-party app or screen recorder, which is inconvenient and can result in loss of quality. However, TikTok, the newish popular short-form video platform, makes it easy to download videos — even if they're not yours.

With Instagram's archive feature, we have the pleasure of hiding all our stupid photos of #gettingcrunk from back in the day. This wonderful new IG feature will still allow us all to cherish those embarrassing moments in our life, yet hide them from those people we hope would never scroll so far down.
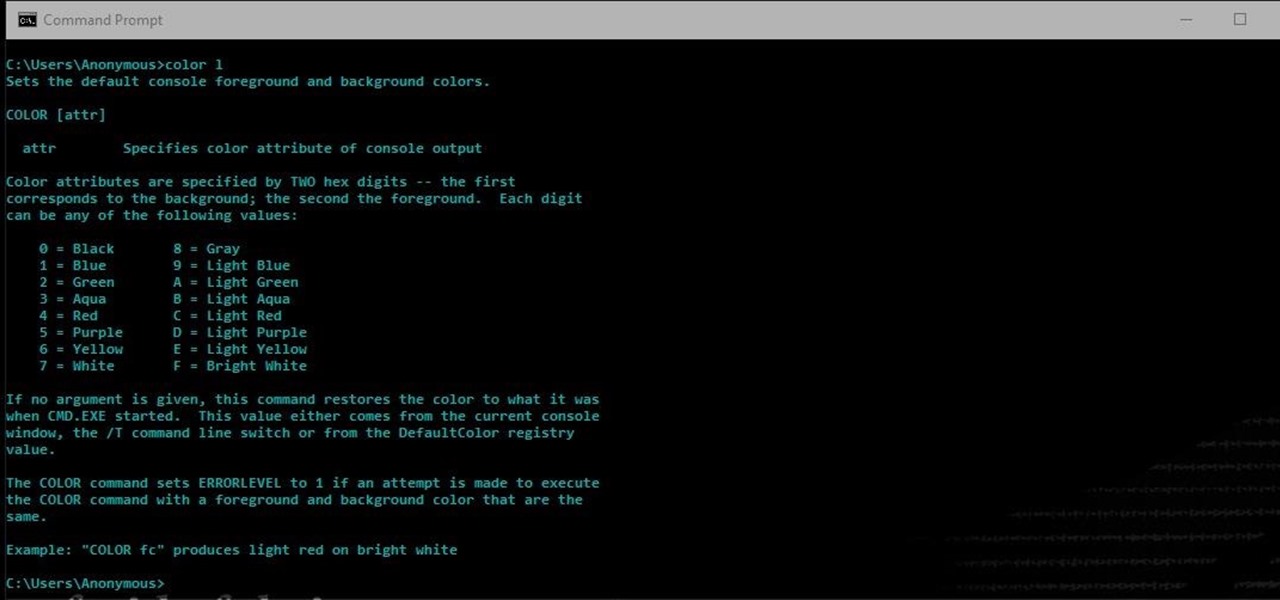
Another series I am now starting, might have to slow down on all of these series, but why tf not. What Is CMD?
Hello there Nullbyters, Last tutorial we discussed navigating and setting some options.

Ruby is a dynamic, general-purpose programming language created by Yukihiro "Matz" Matsumoto in Japan around the mid-90's. It has many uses but with it's flexibility, it makes a great language to write exploits in. In fact, the entire Metasploit Framework is written in Ruby! The sole purpose of this series is to teach hackers the basics of Ruby, along with some more advanced concepts that are important in hacking.