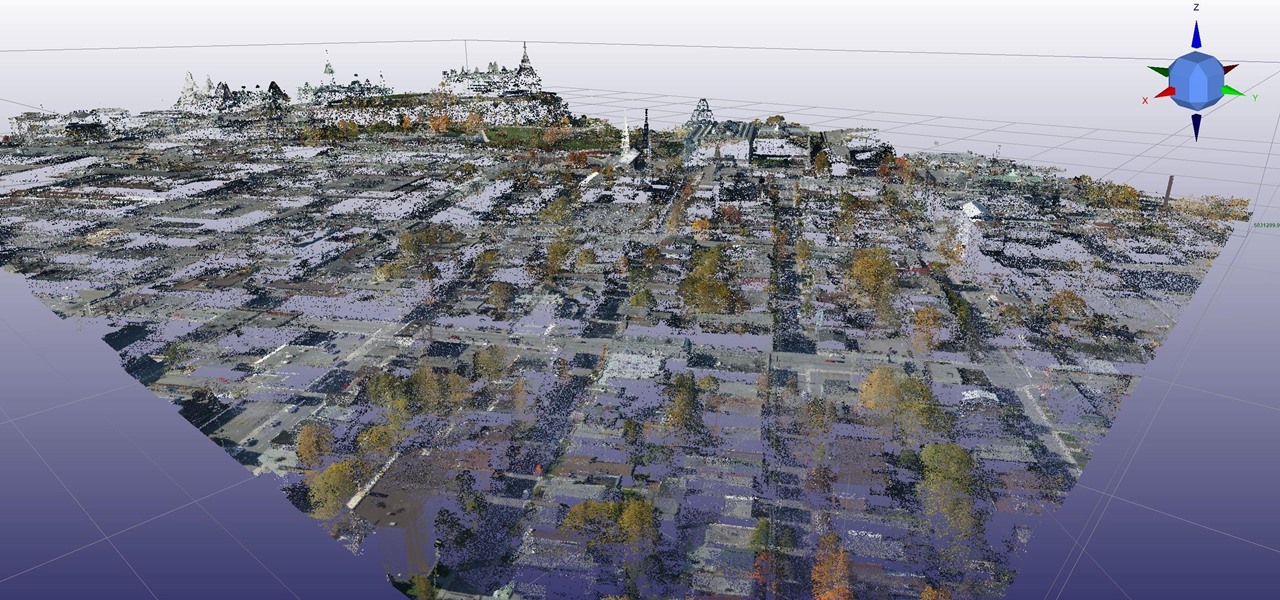
News: Arvizio Adds LiDAR Point Cloud Support to MR Studio
Mixed reality developer Arvizio has updated its MR Studio software suite to integrate processing of 3D light detection and ranging (LiDAR) point clouds.

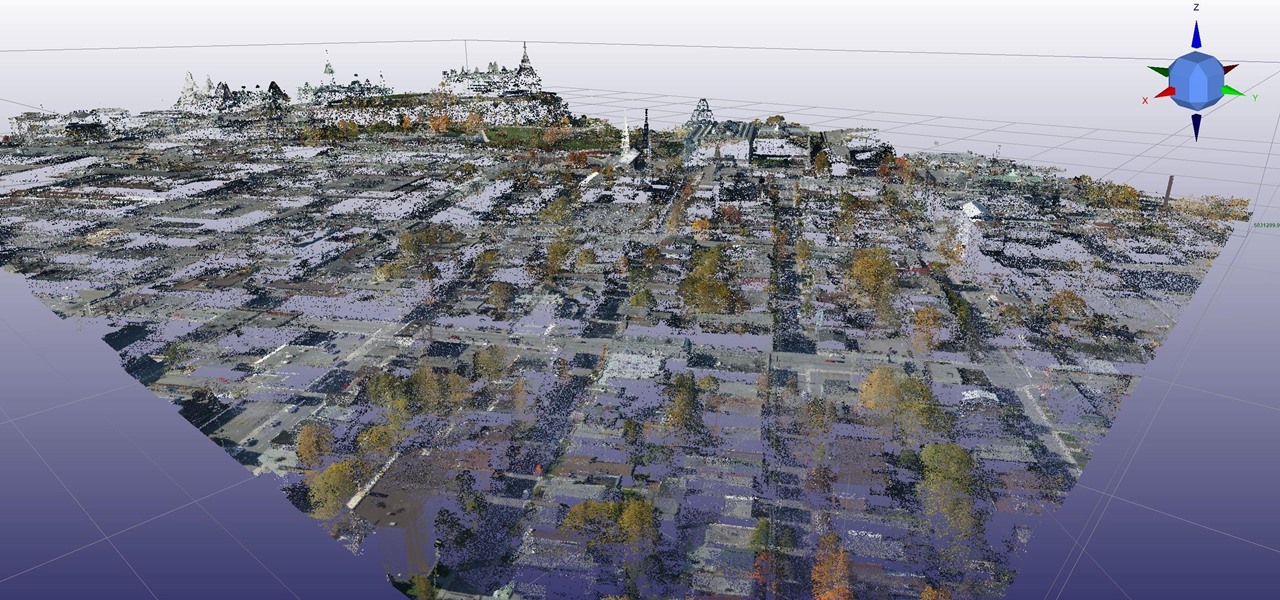
Mixed reality developer Arvizio has updated its MR Studio software suite to integrate processing of 3D light detection and ranging (LiDAR) point clouds.

What a week for iPhone rumors. Monday saw an intriguing photo leak on Reddit of what could be the final designs for the iPhone 8, 7S, and 7S Plus (highly suspect, of course). Today continues the intrigue — iPhone assembler Wistron told reporters in Taipei that Apple's newest smartphones will be waterproof and feature wireless charging.

The next-generation Audi A8 to launch in July is expected to be the world's first Level 3-capable production car to go on sale in retail channels.

If you thought the selfie would only ever be used to bombard your feed on Instagram, you were wrong. Dead wrong. JetBlue is looking to take those selfies and use them to check you in for your next flight.

When a new jailbreak method comes out, Apple is quick to patch the vulnerability it exploits by issuing a new iOS update. If you were to accept such an update, you'd no longer be able to jailbreak your iPad, iPhone, or iPod touch unless you could roll back your firmware to a version that could be jailbroken. But Apple even takes things a step further and stops signing older iOS firmware versions, which makes downgrading next to impossible. This is where your SHSH2 blobs come into play.
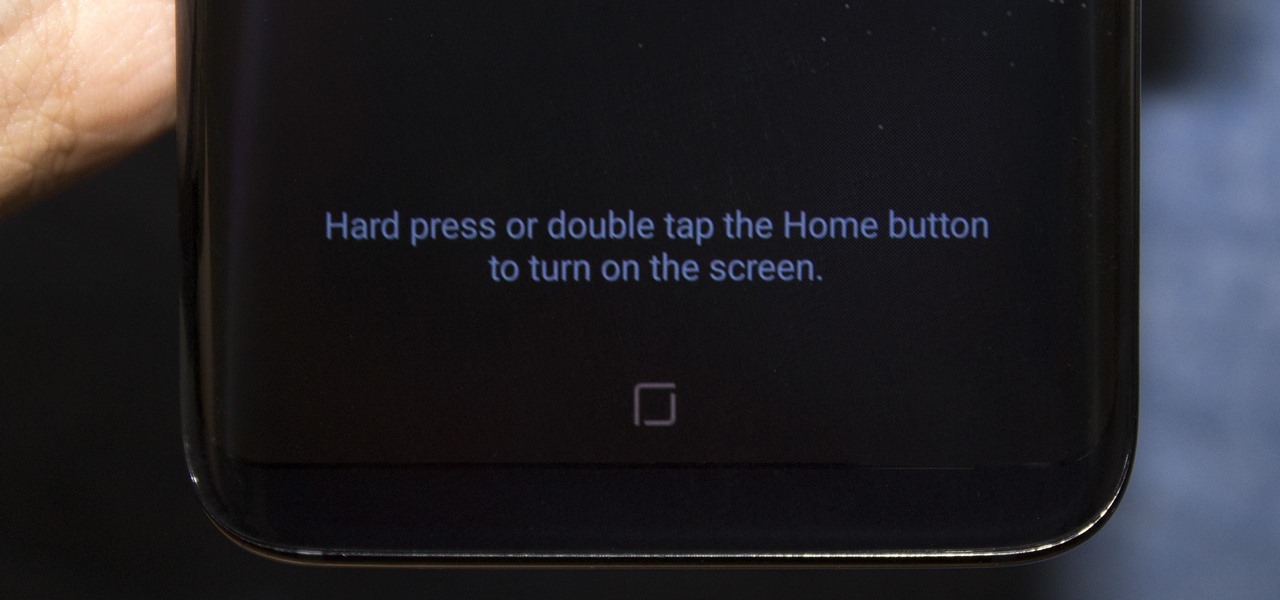
Everyone's been talking about Samsung's new Galaxy S8 and S8+, but not all of the chatter is positive. The fingerprint scanner is in an awkward location, the North American variant is simply not as smooth and fluid as the international model, and Samsung Experience is nothing more than TouchWiz with a bow on it. But perhaps worst of all, user reports are starting to roll in that indicate the Galaxy S8 may have a serious problem with premature screen burn-in.

The culprit probably wasn't what doctors were expecting when a 57-year-old man in Hong Kong came to the hospital. The patient was admitted to the intensive care unit in critical condition. A clue to the cause of the infection would lie in the man's profession—he was a butcher.
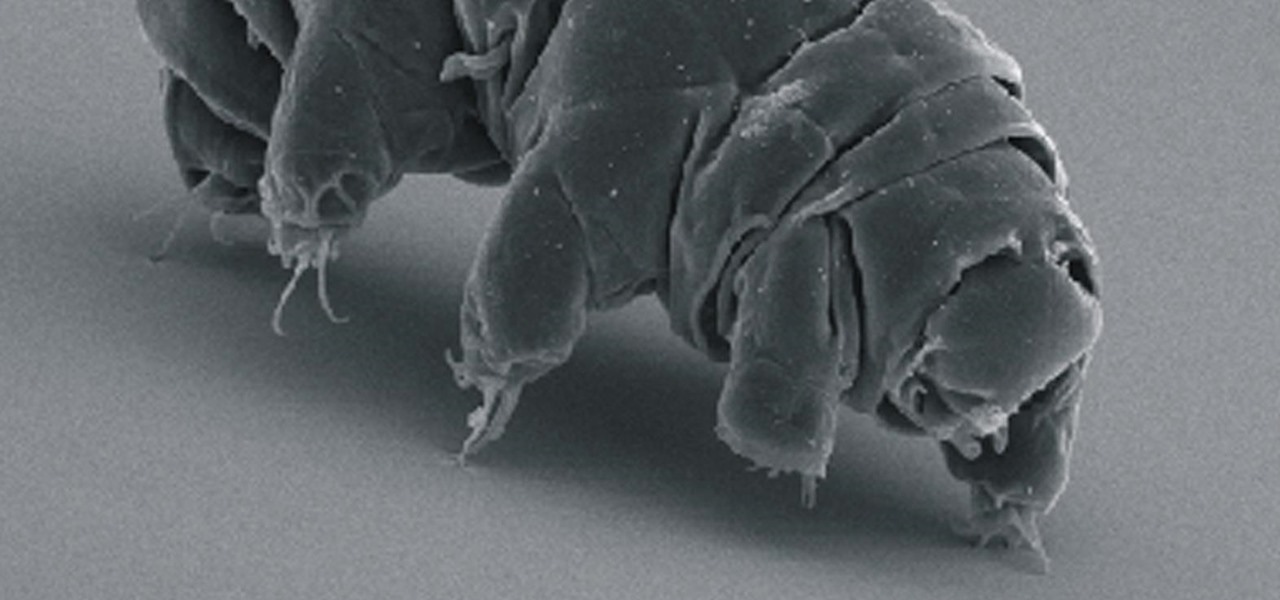
Call them what you will—moss piglets, water bears, or by their real name, tardigrade—but these intriguing tiny creatures can come back from the brink of death. They can survive boiling, deep freezing, UV radiation, completely drying out, and even a trip to space—without the benefit of being in a spacecraft.
Early this morning, Unity held their keynote at GDC 2017 in the InterContinental San Francisco hotel. During the event, they talked about their upcoming roadmap and many changes that are coming down the pipe. This list included the lighting explorer, progressive lightmapper, the new 4K video player, native support for Vulkan graphics, TextMesh Pro integration, and the one that really excites me as a HoloLens developer—dynamically/runtime created navigation meshes.

Android is Google's project, so of course you can see the search giant's fingerprints all over the operating system. Aside from the obvious user-facing apps, there's Google Cloud Messaging, Google Connectivity Services, and the much-maligned Google Play Services running in the background, to name a few.

Some bacteria can already do it—generate electric current, that is—and those microbes are called "electrogenic." Now, thanks to the work of a research group from the University of California, Santa Barbara, we know how to easily turn non-electrogenic bacteria into electricity producers.

GitHub is an extremely popular site that allows developers to store source code and interact with other users about their projects. Anyone can download public, open-source files on GitHub manually or with Git, and anyone can fork off someone's project to expand or improve it into its own project. It's a really great site for programmers, developers, and even inspiring hackers.

While you can't turn art into a formula, the film industry has managed to come stupidly close. While many storytelling principles still stand across mediums, successfully crafting a compelling, immersive narrative in virtual reality requires a brand new rulebook. Through trial, error, and success, writer/director/editor Adam Cosco figured out the right rules to follow (and break) in "KNIVES"—his latest 360-degree short film. The film tells an old-fashioned tale of a woman, Kelsey Frye, strugg...
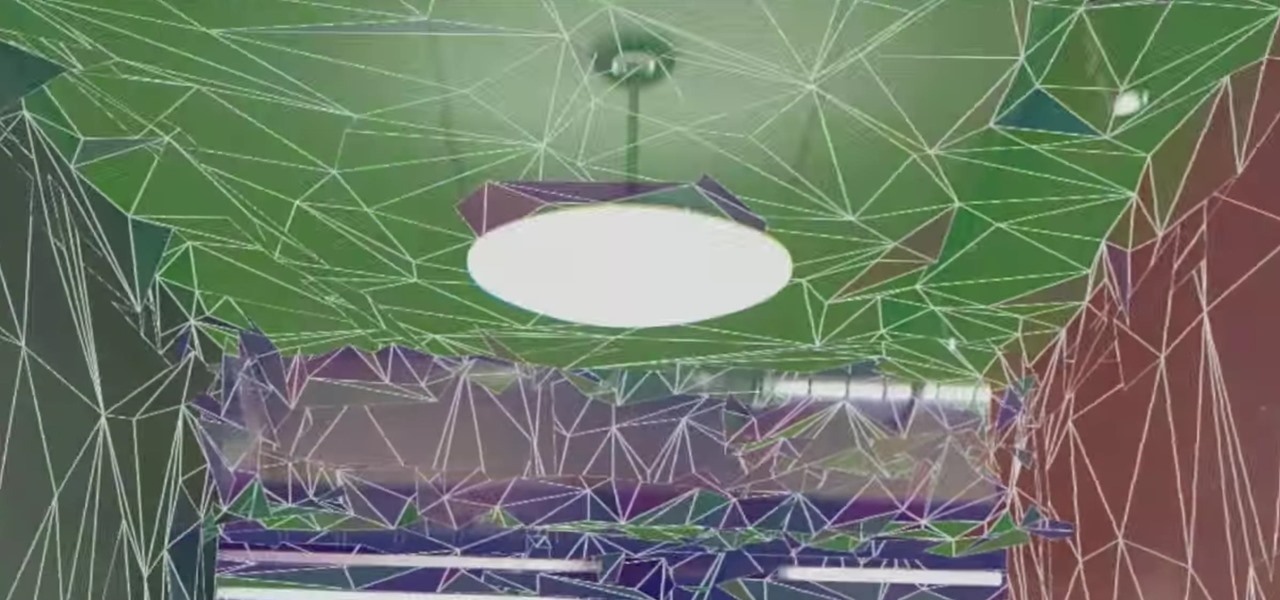
Complex games in mixed reality require a pretty detailed scan of the room, and getting this process right can be both time-consuming and annoying. Computer science students at the University of Washington decided to fix that by turning it into a game.

When Hey Siri was first introduced in iOS 8, it was a pretty lackluster feature since you had to be plugged into a power source in order to even use it. Since then, newer devices (iPhone 6s, 6s Plus, SE, 9.7-inch iPad Pro) don't need to plug in to have always-on Siri, which makes the feature actually worthwhile—when it works.
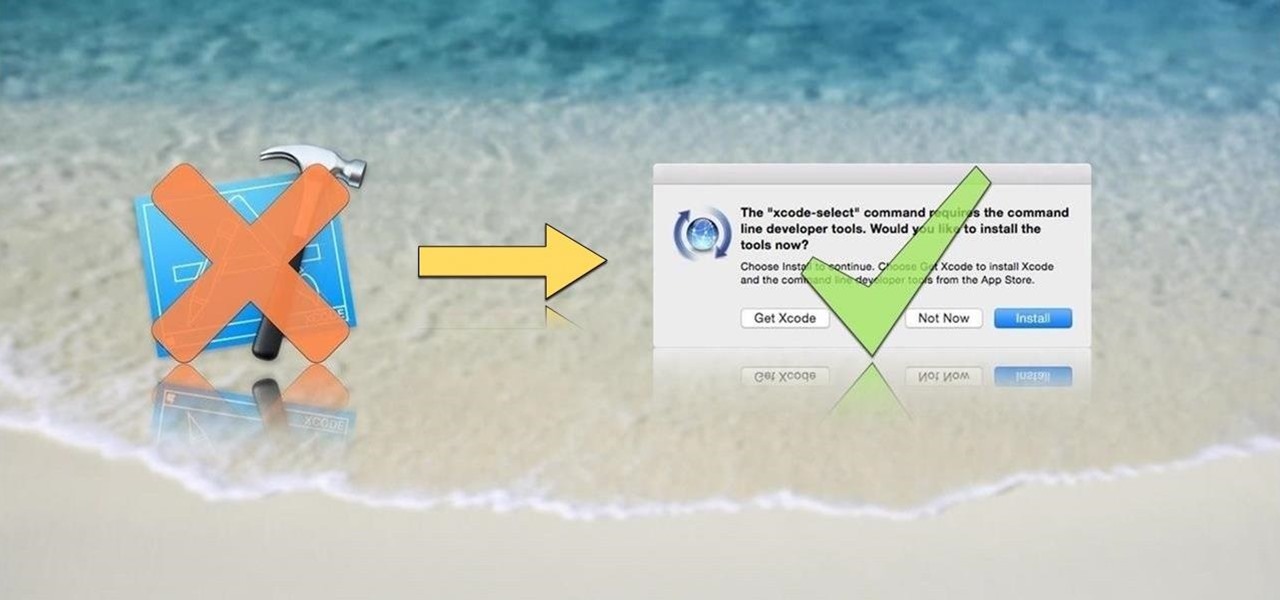
OS X is built upon a UNIX foundation, which grants you access to the benefits that UNIX offers, including the standard toolkit (make, gcc, clang, git, perl, svn, size, strings, id, and a lot more) via the command line developer tools, which are an essential if you're a developer. Aside from developers, the command line tools can offer benefits to normal users as well, like the ability to purge RAM for better performance.

If you've been around computers long enough, you've probably heard the phrase "have you tried turning it off and on again?" This trick usually works because it forces your computer to empty out the contents of its RAM and disk caches when you restart.

Welcome back, my greenhorn hackers! Many new hackers come from a Windows background, but seldom, if ever, use its built-in command-line tools. As a hacker, you will often be forced to control the target system using just Windows commands and no GUI.
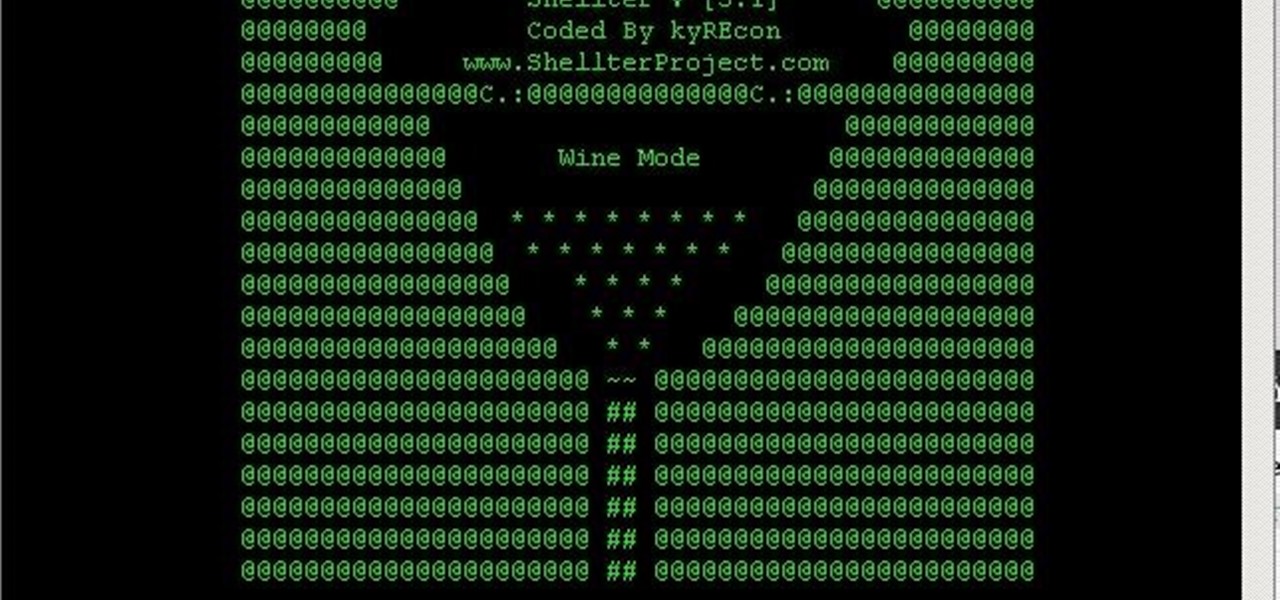
You always wanted to make an undetected payload and make it look legit, Well this is what this tutorial is about, You're going to learn how to backdoor any (Unfortunately only 32-Bit) software, Let's get into it
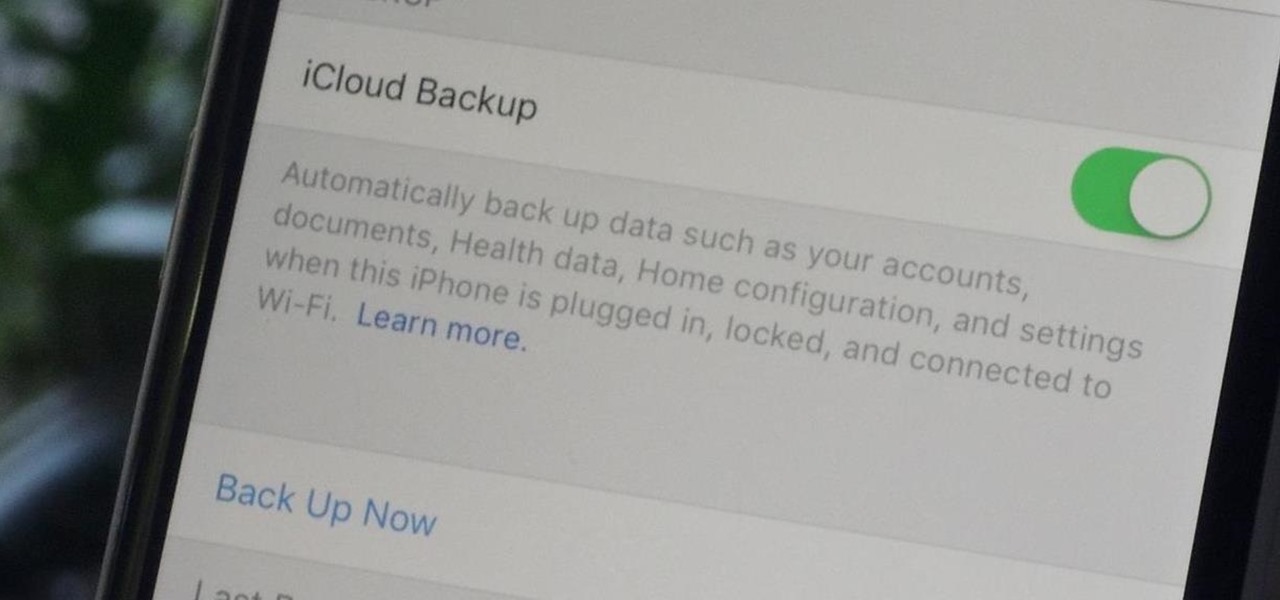
Enabled from the moment you first booted up your device, there's a feature deep in the iPhone's settings that automatically backs up your device in the background. As long as you're connected to Wi-Fi and a power source and your screen is locked, your photos, text messages, apps, and everything in-between gets safely stored to your iCloud account.

The day has finally come, and after quite a bit of hype and buildup, Windows 10 is now officially available. The update itself is on a staged rollout, which means it will be slowly becoming available to users over the coming weeks and months, so don't panic if you haven't already received an update notification. Besides, you have until July 29th, 2016 to download your free copy of Windows 10 if you're eligible, so there's plenty of time to get your ducks in a row.

Researchers at the cyber security firm Zimperium have recently uncovered a vulnerability in roughly 95% of Android devices that has the potential to allow hackers to take total control over your phone with a simple picture message (MMS). The gritty details of this exploit have not been made public yet, but hackers now know the general framework for this type of attack, so you can be certain that they'll hammer out the details in no time.

Just recently, I was experimenting with a dual-boot Windows setup, and somehow managed to wipe my primary Windows installation in the process. "Why," I asked myself, "Why didn't I make a backup before I started this?" Still to this day, I'm going through the painstaking process of installing and configuring all of my favorite programs, and I may not ever get things back exactly the way they were.

Last week, NowSecure security researchers revealed that nearly 600m Samsung mobile devices are vulnerable to a type of MitM attack.

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

Hi nullbytes! I've been recently reading the whole Linux Basics for the Aspiring Hacker series and felt like it was missing some stuff I know, so I felt like sharing it with anyone who might find it useful too.
Your iPhone's home screen is a tricky thing. You can sort your collection of apps in any order you'd like, but where you place those apps is a totally different story. App and folder placement follows a strict grid on iOS from left to right, top to bottom. No exceptions, and that's how Apple wants it. So you might think without a jailbreak you're stuck with this layout — but you're wrong.

Garlic: almost every cuisine in the world considers it a staple, and for good reason. Its pungent flavor gives depth and character to food. Dishes made without it seem bland and forgettable. And on top of all that, it's been studied for its potential anti-cancer properties (and don't forget: it's been mythologized for warding off vampires).

The Nexus line of devices consistently offer the most bang for your buck. It's why many of us purchased a Nexus 5—at a $350 entry price, it's half the cost of any other phone with similar specs.
Whether you have the original Nexus 7, or the 2013 Nexus 7 tablet, rooting it will give you access to tomorrow's features, today.

While websites may run smoothly without any noticeable vulnerabilities, there's always the looming threat that any background weakness in the site can be exploited by hackers. Once a site is compromised, it can be difficult to get it fixed without the proper help. Google has recently launched a new series entitled "Webmasters help for hacked sites”, which teaches web developers and site owners how to avoid getting hacked and how to recover their website if it gets compromised in any way.

Most people need their morning pick-me-up to get the day started right. There's a Starbucks on every corner and caffeine "shots" are sold in convenience stores everywhere. Even Mountain Dew is getting in on the action with its new KickStart "breakfast" drink (whatever that means). With a whopping 5% real fruit juice!

If you've never heard of cookie butter, it must be because you live in a town where there's no Trader Joe's. It was their most popular item in 2012, and when it started to become popular, the Internet promptly went nuts, posting recipe after recipe using it as an ingredient. For those of you who don't live near a Trader Joe's but still want to see what all the fuss is about, there's good news—you can make it at home—and you don't need spiced Speculoos shortcrust biscuits either!

While the majority of America was watching the Super Bowl yesterday, the crew over at the evad3rs was finishing its work on their untethered iOS 6.1 jailbreak called evasi0n. Well, the wait is finally over!
As someone who writes an extreme amount, it's a necessity for me to have an organized and multifunctional text editor. The stock iPhone Notes application is useful to an extent, but it sorely lacks in features and design. Writing and text editing applications are nothing new to the iPhone, but many of them are overloaded on features, making it even harder to keep organized. Here are just a few alternatives that I find helpful in my day-to-day writing.

These three videos will show you how to build a rustic, distressed kitchen table. I'll be walking you through the process of selecting some recycled timber from a junk pile, and with a little care and some simple joinery techniques, transform that waste timber into a distressed timber kitchen or dining table. In fact, you could use the table for whatever you wanted really.

A few days ago, Russian hacker Alexy Borodin found a way to get free in-app purchases on an iPhone or iPad. In-app purchases include things like items and power-ups for iOS games, as well as subscriptions and "premium" memberships for certain apps.

Hub bearing assemblies are one of the most expensive things you could get fixed on your vehicle. And it's not an easy task to repair yourself if you're not a semi-professional mechanic. But with the help of this video, you'll learn the steps to changing hub bearing assemblies, from a licensed technician.

Julie Goodnight guides you through how to safely mount and dismount a horse. First make sure you put the reigns up over the horses head. Keep the reigns in your hands so you always have control of your horse. Check the cinch on the saddle before putting your foot in the stirrup. Make sure the horses feet are square so it can properly brace when you go to mount. Stand to the front of the horse, facing the rear, so you can see the legs at all times. This will also discourage your horse from ste...

With a little time, you can turn a pair of rabbits into lifetime bunny buddies. Step 1