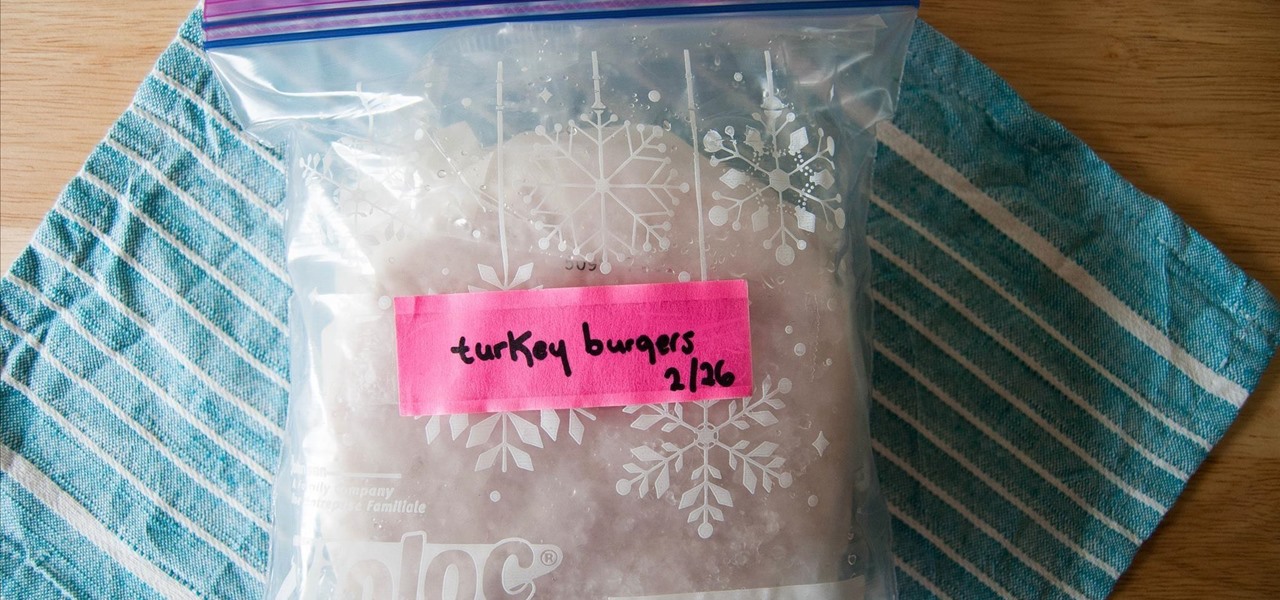
How To: Store Meat to Avoid Freezer Burn
Frozen meat is a saving grace for weeknight meals. Whenever I crave a certain protein, all I need to do is defrost it. Sometimes, I don't even need to defrost it in order to use it.

Frozen meat is a saving grace for weeknight meals. Whenever I crave a certain protein, all I need to do is defrost it. Sometimes, I don't even need to defrost it in order to use it.
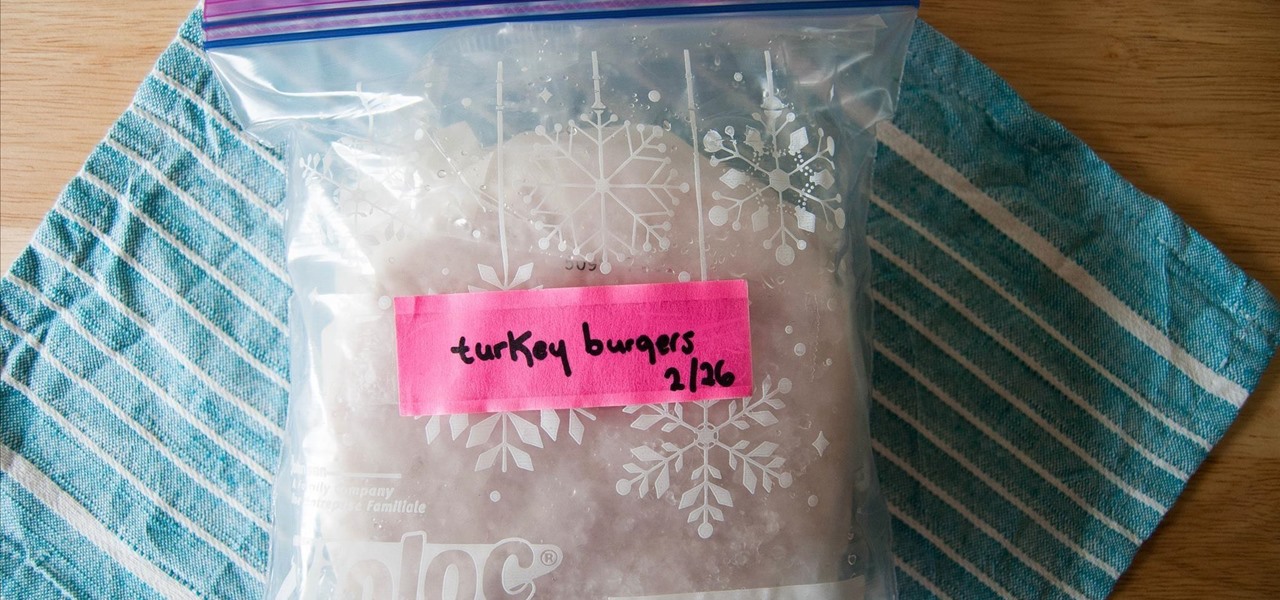
Note: a bug was found in the Insertion Sort implementations. The bug was corrected in each language. Please refer to the pastebin links for the most up-to-date versions of the sample code. Any screenshots may be behind. More about the bug can be found here.

Cellular carriers like to nickel-and-dime us out of every bit of money they can feasibly justify, so as consumers, we owe it to ourselves to make sure that we're getting our money's worth.

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.

Welcome back to another episode of Java Tutorials, In today's tutorial, we'll be learning about what methods are, proper syntax when writing Methods, and why they are beneficial in a program's code.

This article is to all the newbies on here wanting to become a hacker. Since I have seen many newbie questions on here, I need to address this.

Spaghetti squash is a versatile vegetable, but it has a reputation for being intimidating to prepare... not to mention time-consuming. Heating it up in the oven can take at least 30-40 minutes, which is a definite time-suck for those who want to get dinner on the table, stat.

When it comes to cooking grains, there is an unspoken rule to never stray from the exact measurements. Consulting charts for the proper ratio of liquid to grain is considered the difference between crunchy, undercooked pebbles and a mushy mess... that is, until now.
Ready or not, the USB-C cable is about to take over your electronics. The new industry standard is fully reversible and packed with enough power to serve as a laptop charger or an HDMI cable, so it actually has the potential to replace every cord, wire, and connector in your house. In fact, the conversion has already started: The latest MacBook, Chromebook Pixel, and Nexus phones are sporting USB-C connectors out of the box.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.

There are going to be tons of great Black Friday deals on electronics in stores like Best Buy, Target, Walmart, etc. But if you can't endure another holiday of standing in lines and running over people to get what you want, shopping on Amazon from the comfort of your own home is the way to go.

A classic French omelet is supposed to be completely cooked through with no brown edges. This is a delicate balance to strike, though. I always find that the moment I flip an omelet, it completely falls apart—unless it's so well-done it's rubbery, of course.

Black lights come in all shapes and sizes, and they're useful in a variety of ways. They can help you spot fake currency, urine stains, interesting rocks, and deadly scorpions, and they can even help you view cool fluorescent artwork.
OneDrive, formerly known as SkyDrive, is a free online storage solution developed by Microsoft. If you're a fan of using cloud-based storage systems, then OneDrive offers you plenty of benefits. It's also heavily integrated into Windows 10, including the new File Explorer, in an effort to make utilizing OneDrive easier for you.

In an age where restaurants can charge $20 for eggs Benedict at brunchtime (if you're lucky enough to even get a reservation on a Sunday), many people long for a way to create this classic dish at home. But once you've taken pains to perfectly poach an egg and gently crisp your sourdough, the problem of the hollandaise still lies before you. The key to any good hollandaise sauce is to apply enough heat to cook the egg yolks, but not enough to scramble them. The minute the eggs begin to solidi...

Welcome back, my novice hackers! As most of you know by now, a notorious commercial, legal hacking group named "Hacking Team" was recently hacked. As part of the hack, thousands of emails and other material on their servers was divulged. Among the material released were three zero-day exploits. In this tutorial, we will walk through the steps to load one of them, which has become known as the CVE-2015-5119 exploit.

In the past, updating a rooted Samsung Galaxy device has always involved the complicated process of downloading the proper firmware for your variant, installing device drivers, then sideloading the update with Odin.

A good chef's knife is a thing of beauty and, with proper care, a joy forever. It can totally change the way you cook and turn even the dullest prep work into a glee-filled task.

With smartphone screens getting bigger by the generation, one-handed mode mods are becoming rather prevalent. Most of these function by shrinking the screen to a more manageable size, but this is actually kind of boring when you think about it.
The only mail I like getting comes in the form of an Amazon package, but when I go to my mailbox, it always ends up being a pile of credit card offers and catalogs I could never see myself ordering from. Those pieces of junk mail usually end up in the trash, which is horrible when you think about all the trees that had to get cut down in order to produce them.

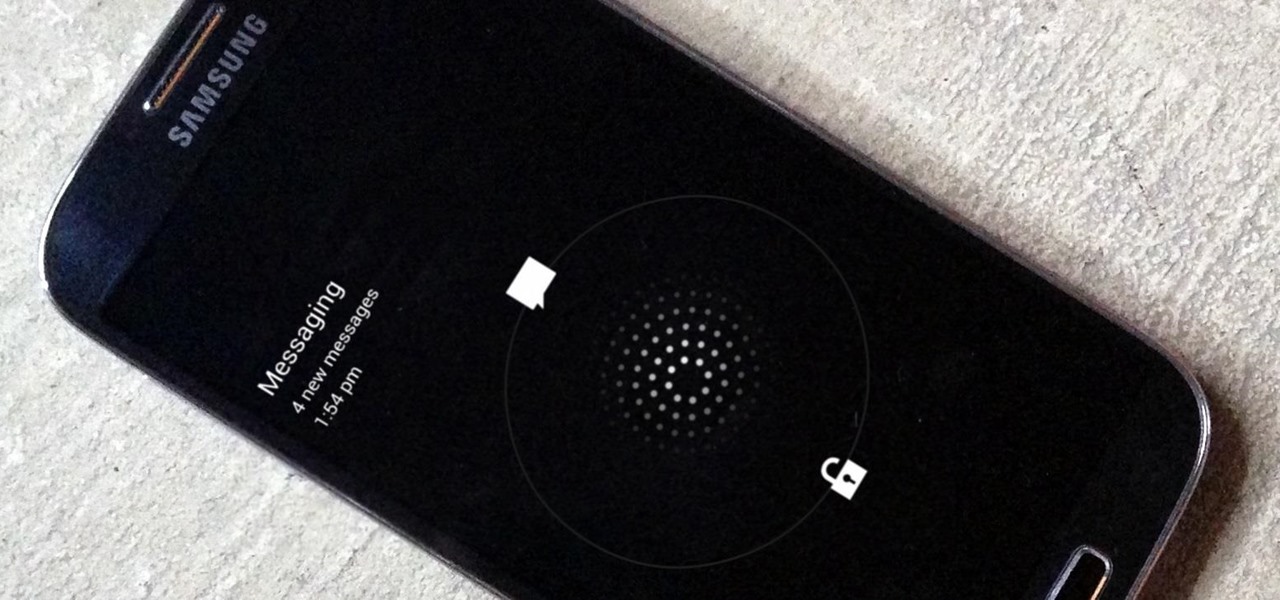
Beginning with KitKat, I've been used to customizing every aspect of my Android phone, but with the release of Lollipop, there is quite a bit of catching up that developers need to do. Most customization features, like quick settings rearrangement and theme support have already been ported over, but any type of lock screen customization has been noticeably absent.

One of the most mind-blowing meals I ever ate occurred when I was 12 years old. The main course and sides were good, if unmemorable, but my jaw dropped during dessert when my friend's mother whipped out a blowtorch—as in a bona fide welding torch from the hardware store—to finish off the crème brûlée.

With the Nexus 6, you get a very clean software experience with minimal bloat. While this is generally the main selling point for most Nexus fans, it can be a bit of a detraction for some.

With the sheer amount of photos, videos, and miscellaneous files we place on our computers, proper organization becomes necessary. Not only so that we can quickly get to a file when it's needed, but also to declutter folders and keep them from looking like random file dumps.

First, I want to give credit to the author where I first found how to do this: Astr0baby's Blog. This article was dated, so I took the script on his page and reworked it to make it work today. (I also included the way to make it hide the cmd line popup.) Requirements

One of the few areas where Android lags behind iOS is a comprehensive backup solution for apps. Root tools, such as the popular Titanium Backup, are capable of backing up all of your apps and their data, but not everyone wants to root their device and potentially run into issues with voided warranties.

Welcome back, my greenhorn hackers! Before we attempt to exploit any target, it is wise to do proper reconnaissance. Without doing reconnaissance, you will likely be wasting your time and energy as well as risking your freedom. In previous guides, I have demonstrated multiple ways to perform reconnaissance including passive recon with Netcraft, active recon with Nmap or hping3, recon by exploiting DNS or SNMP, and many others.

We've previously shown you how to get your Samsung Galaxy S4 looking more like its successor by installing the revamped S Voice app and the new Quick Settings. Now, we're taking it a step further by giving you the Galaxy S5's stock Settings app. After this mod, it'll be pretty hard for others to distinguish your GS4 from a GS5.

Whenever a new Android device is realized, the first thing I figure out how to do is to get it root access. Generally speaking, rooting has never been easier, with many one-touch methods like Stump and Towelroot available. But as manufacturers and carriers increase security with each new product, there is one tried-and-true root method that continues to work on most Samsung devices—Chainfire's CF Auto Root.

There are a lot of great new features in iOS 8, but not everyone is enjoying them. Some of you may just genuinely prefer iOS 7 over iOS 8, and some of you may be experiencing lag on older devices like the iPhone 4S, however minimal it may be. Whatever the reason, if you don't want iOS 8 on your iPad, iPhone, or iPod touch, there's still time to downgrade back to iOS 7.1.2.
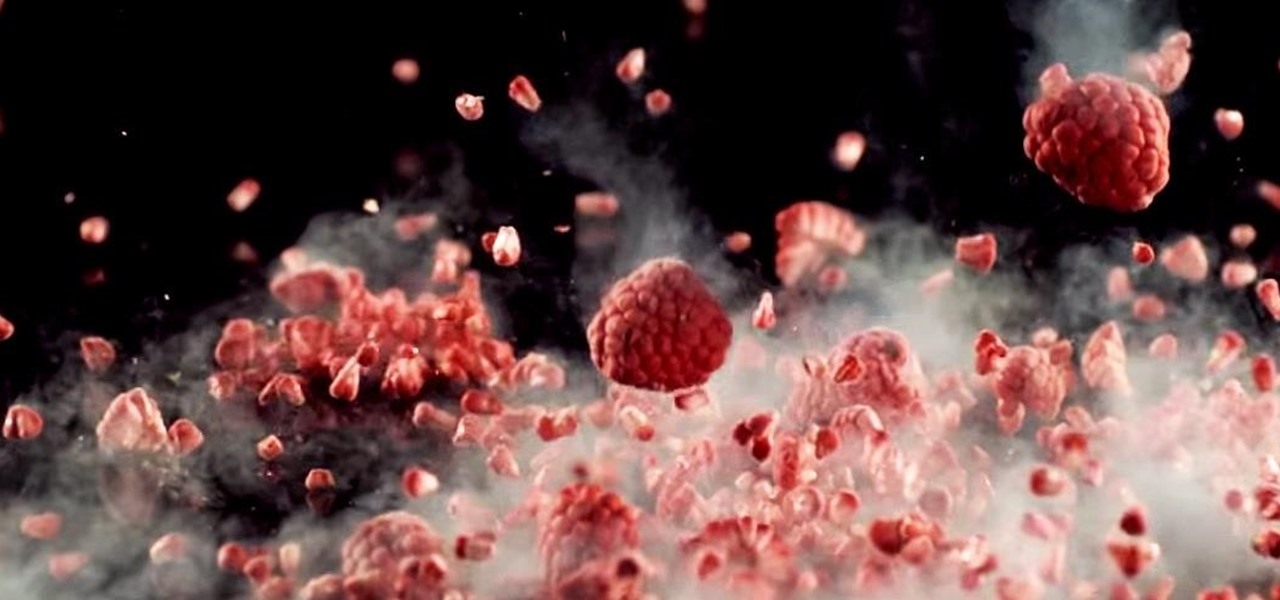
"Cooking" with liquid nitrogen seems like one of those activities that should be strictly limited to pros who are appearing on Top Chef, but it's the only way you'd ever be able to make Dippin' Dots at home. If that isn't enough of a reason for you to get some LN2 for your kitchen, check out this dose of pretty:
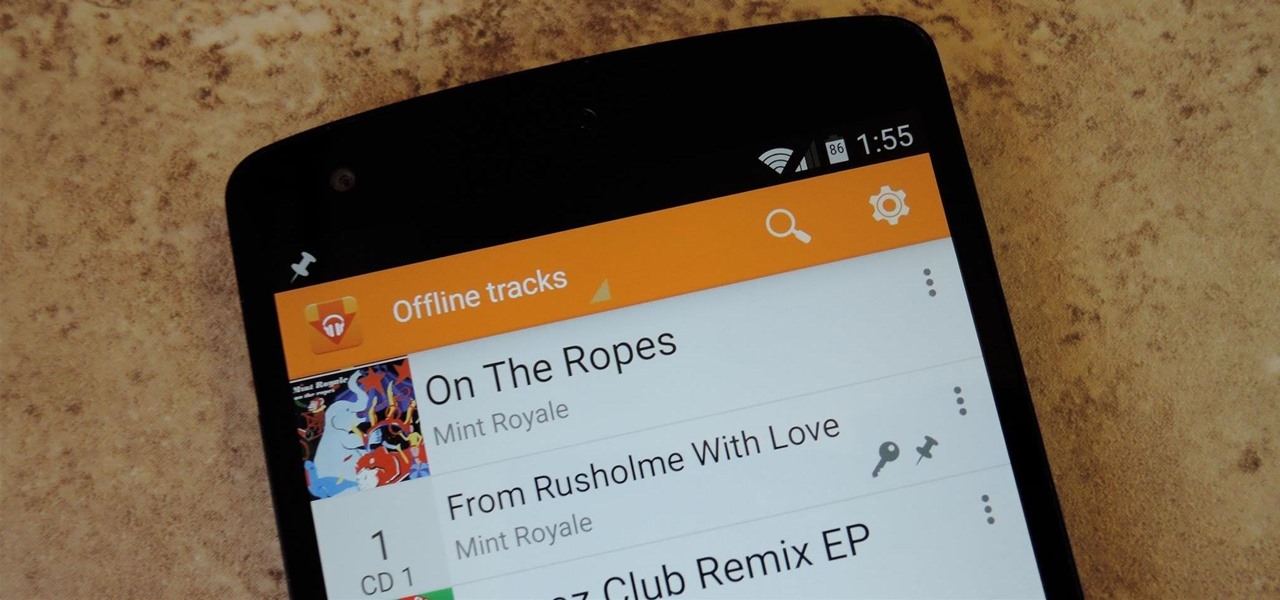
Google Play Music is one of the best cloud music services out there. Without ever paying a dime, you can upload as many as 20,000 songs to Google's servers, then use the app on your smartphone to stream these songs without taking up any of your storage space. And if you're willing to shell out $9.99 a month, you can even play songs from the massive All Access library.

I have literally played Madden, watched YouTube videos, and listened to music on my phone all at the same time. Some would call this pathetic, but I call it talent. Life is way too short, so I need to get the most out of it when I can. Thank goodness for multitasking, which should be a key feature when you're looking into a new tablet or phone.
According to a new study, the majority of smartphone users check their devices 150 times a day. While that number may seem incredibly high at first glance, the influx of notifications and amount of social media apps available reduce the initial shock and make the number seem not so preposterous after all. Yeah, even on a date.

There's no shortage of cool customizations for my Samsung Galaxy S3, except when it comes to the launcher. Sure, there a ton of Android launchers out there, like Nova Launcher or Apex Launcher, that allow you to customize app placement, app grouping, infinite scrolling, etc. There's even Facebook Home for those who are Facebook addicts.

Who am I? First let me introduce myself. I am Th3skYf0x, an -well lets call it

International, T-Mobile, and Verizon customers all share something in common—their carriers provide unlocked Wi-Fi tethering for free. Of course, you still pay for the data used, but they don't charge you extra simply for using your Samsung Galaxy S4 as a wireless hotspot.

Ethylene is an invisible, odorless, naturally occurring gas that aids in the ripening process of fruit. As a fruit produces more ethylene, it begins to create enzymes which help break down cell walls and starches, making the fruit softer and sweeter over time. If it weren't for this small hydrocarbon gas, the shelf lives of most fruits could last well over a year.
We've all been there. Your phone's either dead or barely hanging on with a few minutes of life left, and you only have a small window of time to charge it before you need to head out. Sure, you can charge it for the few minutes you have, but what's the point if your device is going to die again in several minutes?

The upcoming web series "Crypto-Historians" does for cryptohistory what Indiana Jones did for archaeology. For those who don't know, cryptohistory is the study of supernatural or alien elements throughout history, and yes—it's a "real" field.