
How To: Find The Earthen Ring Quartermaster in World of WarCraft: Cataclysm
The Earthen Ring Quartermaster is as elusive as a long-beaked echidna, so how do you find him in World of WarCraft: Cataclysm?


The Earthen Ring Quartermaster is as elusive as a long-beaked echidna, so how do you find him in World of WarCraft: Cataclysm?

New Year's Eve. It will be one hell of a chaotic night. Trust me. The overcrowded streets. Long lines for the urinal. Maxing out your credit card on that shot of Cuervo. You'll be lucky to make it out alive.

Get Google Chrome Download and install Google Chrome.

Watch this video from This Old House to learn how to maintain a steam radiator. Steps:

Join the Pilot program and learn how to fly! But you're not going to be flying airplanes in this Pilot program, you'll be trying your hands at Google's first laptop computer.

A GFCI outlet (which stands for ground fault circuit interrupter) is a receptacle with its own built-in circuit breaker. It is intended to protect you from electric shock and your wiring and breaker panel from being “shorted out”.

Minecraft just wouldn't be the same without all of those pesky monsters trying to break into your house and jump on you until you die. But that gets tiring after awhile, and sometimes you just want a safe place to go where you don't have to worry about being eaten, shot, or blown up.

Just a couple Saturday's ago, we were blessed with the Supermoon, where the moon was at perigee with our planet, creating a larger than usual Moon for us here on Earth. Now, we've got another spectacular show in the skies coming up, only this one isn't at night. There will be an annular solar eclipse on Sunday, May 20th!

With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard drives. Ideas seem to range from magnets to microwaves and a lot of things in-between. So, I'd like to explain a little bit about data forensics, how it works, and the steps you can take to be safe.

Law enforcement can make a lot of folks cringe. Too often do we hear on the news, and even experience in our own lives, the unjust way that an unacceptable portion of law enforcement treat the very citizens they are supposed to protect. People's rights are violate each and every day by law enforcement, simply because they are timid and uneducated with the laws of society. This dirty trickery shouldn't be played on harmless citizens under any circumstances.

Technology in computers these days are very favorable to the semi-knowledgeable hacker. We have TOR for anonymity online, we have SSDs to protect and securely delete our data—we can even boot an OS from a thumb drive or SD card. With a little tunneling and MAC spoofing, a decent hacker can easily go undetected and even make it look like someone else did the hack job.

Here's a nasty little Null Byte. An open redirect vulnerability was found in both Facebook and Google that could allow hackers to steal user credentials via phishing. This also potentially allows redirects to malicious sites that exploit other vulnerabilities in your OS or browser. This could even get your computer flooded with spam, and these holes have been known about for over a month.

Today's tutorial will teach you how to erase data permanently so that it cannot be recovered. Many believe that having a file shredder on the computer means you are up to no good.

If you've ever heard software piracy terminology being discussed, I'm sure the term KeyGens came up. KeyGens is short for key generator, which is a program that exploits algorithmic faults in software by generating software license keys that appear to be genuine. Normally used as a technique to protect the source code software and prevent piracy, a key generator exploits the key algorithm to effectively nullify the need for any software licenses. For example, we must try to find patterns in t...

Your IP (Internet Protocol) address is your unique ID on the internet. It's synonymous with your home address. Anyone in the world can contact your computer through its IP address, and send a retrieve information with it.

When you're out and about in the dangerous world of Wi-Fi, it's hard for the average computer user to stay protected, or even know what being protected entails. Little do most people know, Windows 7 has a built-in security that few people take advantage of: a VPN (Virtual Private Network) server and client.
Proposition 22 Prohibits the state from borrowing or taking funds used for transportation, redevelopment, or local, government projects and services. Initiative constitution amendment.

In this tutorial, we learn how to restore your American Girl doll's shiny silky hair. You can wash and condition the hair, use a flat iron on the lowest setting, trim the ends and fly-aways with scissors, and more! If you have done all of this and it's just not shiny enough, you can help fix it. First, you will put a plastic bag around her body. After this, this is the bag so her skin won't be affected. Now, cover her face with a towel so just her hair is left. Now, take some Son of A Gun spr...

Materials Needed! Video: Undo a door's chain lock from outside with string, yarn or shoelaces.

The sudden deceleration, shifting in the knee, popping sound and screaming from the intense pain that immediately follows is becoming increasingly common among our young athletes. Those who
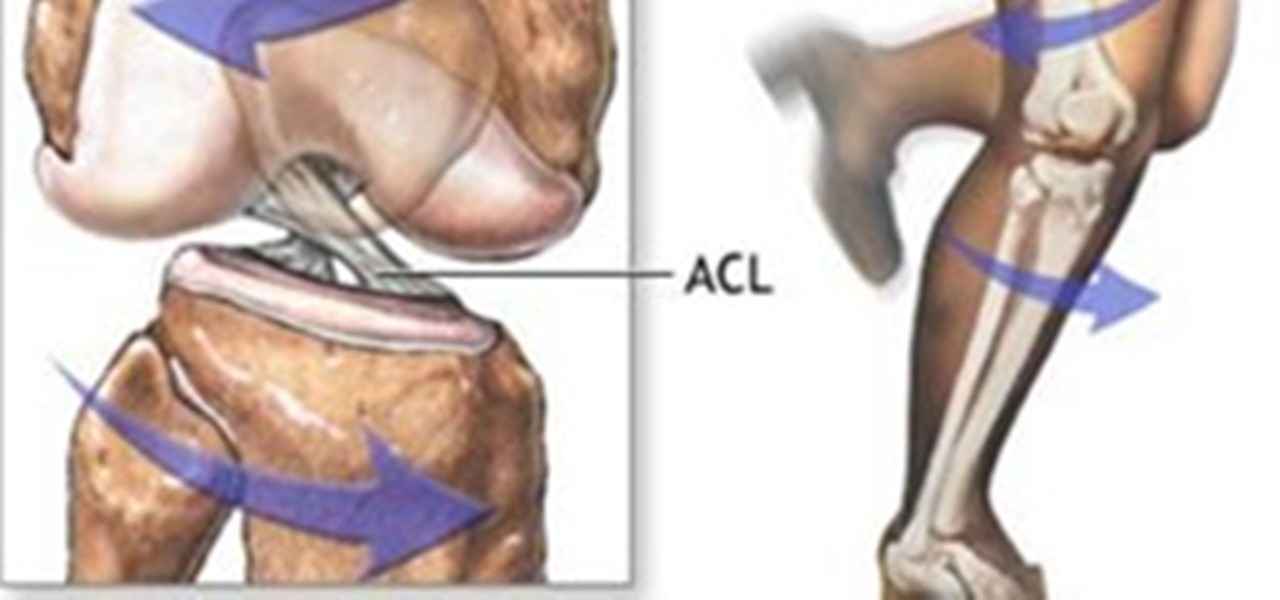
The sudden deceleration, shifting in the knee, popping sound and screaming from the intense pain that immediately follows is becoming increasingly common among our young athletes. Those who have witnessed or suffered a torn anterior cruciate ligament (ACL) are familiar with the pain, surgery and intense 6 to 8 month rehabilitation that accompanies the injury, not to mention the disappointment of ending a season. Nationwide, this will occur more than 500,000 times this year, and female athlete...

Infiniti is like no other car, it has emotion, it has soul, it inspires. There's a difference between being physically transported and emotionally moved, and you can tell them apart when you sit inside this magnificent automobile. Although the Infiniti is like a dream car, it has its problems just like any other brand of vehicle. There's maintenance, minor repairs, major repairs, needed replacement parts, oil changes, headlight adjustment, low tires, transmission and everything else you can t...

If you have hardwood floors in your house, take a look at your baseboards. Right in front of the baseboards there is usually a smaller, curved molding about ¾” tall. How does this short molding look? Is it painted over, chipped and/or just beat up in general? If so, you can easily replace this molding and make a huge difference in the overall appearance of your room. And, it is fairly easy to do.

Believe it or not, you don't need to hire an electrician to add a few electrical outlets in your home. The only thing you really need to worry about is being safe. This Old House walks you through the entire process of adding receptacles, from cutting the hole in the drywall to wiring the outlet to final checks.

Watch this video from This Old House to learn how to prevent frozen pipes. Steps:

Watch this video from This Old House to learn how to repair a kitchen sink sprayer. Steps:

Watch this video from This Old House to learn how to plant a tree in poor soil. Steps:

Watch this video from This Old House to learn how to transplant a tree. Steps:

As useful as VPNs are for securing your browsing experience and bypassing frustrating barriers online, it's hard to find the right one among the horde of choices. VPN.asia: 10-Year Subscription is a great choice for a VPN that keeps your browsing safe and smooth, and right now, it's only $79.99.

Many things cause a bike tire to deflate. Glass, sharp rocks, tacks, and nails can pierce the tire and puncture the tube within. A tube can be pinched between the rim and tire causing the tube to split when inflated. If a tire has a hole in it, the tube, which is filled with air pressure, will bulge out of the opening and pop. As well, the valve holding the air pressure in the tube can be damaged or faulty.
Here’s some news for those who still somehow believe the political left in Washington cares about the People. After U.S. Senator Rand Paul introduced an amendment that would have ended armed FDA raids on raw milk farmers (http://www.naturalnews.com/035966_Rand_Paul_FDA_censorship.html) and legalized free speech about the curative properties of medicinal herbs, nutritional supplements and superfoods, are you curious how many Democrats voted in favor of this?

Want to protect your home from unlawful entry? You may not have the means to invest in an expensive alarm system, but you can definitely use cheap and practical methods around your home to deter burglars from breaking in when you're not home.
In this article, I'll show you how to make an awesome "Death Ray" using the large magnifying lens from an old projection TV. The lens is called a Fresnel lens; a device that employs several ridges to focus light, rather than a complete curve.

Last Friday's mission was to accomplish solving HackThisSite, basic mission 10. This mission teaches us how to use JavaScript to manipulate cookies on poorly coded cookie-based authorization.

OpenVPN is the open-source VPN (Virtual Private Network) client, used over the PPTP (Point to Point Tunneling Protocol). It allows you to connect to a remote network over a secure, encrypted connection and mask your IP addresses over all ports. Since there is only one "hop," the network speeds are barely effected and are far more secure.

SSH is what is referred to as the Secure SHell protocol. SSH allows you to do a plethora of great things over a network, all while being heavily encrypted. You can make a remote accessible shell on your home computer that gives you access to all your files at home, and you can even tunnel all of your traffic to keep you anonymous and protected on public Wi-Fi. It has many great uses and is a must have tool for your arsenal. It was designed to replace the insecure Telnet protocol, which sends ...

This Guy Has My MacBook is a gripping tale for iOS nerds far and wide, documented via interaction designer Joshua Kaufman's tumblr. When Kaufman's MacBook was stolen from his apartment in Oakland, CA, on March 21, 2011, he quickly activated Hidden, a previously installed app that enabled Kaufman to collect photos of the thief, as well as screen shots of the computer in use.

It's not uncommon for nature to inspire technology and innovative products. Airplanes were inspired by birds, Velcro by burrs and dog fur, bullet trains by owls and kingfishers, and gecko tape by... well, you can probably figure that one out. And one of the deadliest fish ever to swim the oceans has also influenced its share of merchandise; Sharks made humans faster in the water with Fastswim Suits, and now they've helped make one of the most rugged smartphone cases in the world—SharkEye's Ru...

Child Safety Window Treatments

Designer Andrew Clifford Capener has made an alternative to the classic Scrabble board that celebrates the expression of typeface. It isn't in production yet, but Capener's set would offer tiles in a variety of different fonts: