Wrapping your wrists for boxing is very important to provide protection and support when you are throwing your punches. This video shows you the right way to wrap your wrists to prevent injury. You'll be putting the seam side of the wrap against your skin, and start by putting the loop at the end over your thumb. You will start by wrapping the wrist a few times, depending on how long your wrap is. Watch to see the correct way to cover the knuckles and secure the wrap against your hand before ...

This how to video shows how to fight a cold naturally or how to get over an infection. When you get a cold, there is an imbalance with your blood PH or an outside invader such as a virus. Some tips to get yourself feeling better are to boost your immune system with herbal supplements and getting a good source of protein. Protein helps to form antibodies, and without a good source of protein your body loses that source of protection. This video shows that the best source of protein is meat and...

Learn how to straighten your hair easily. First, wash and towel dry your hair. Next you will add a small amount of Chi silk infusion to your hair. Part your hair where you would like it parted and blow it dry. Now you need to brush out any knots in your hair and spray it well with Chi 44 iron guard. Coat the ends of your hair with a heat protection serum, and use a straight iron to straighten sections of hair starting with the bangs. You can use clips and bobby pins to keep hair that you are ...

AntiVirus Live is a fake antivirus software which comes onto your system and asks you to buy it. It doesn't provide any security to the computer. Here is the procedure to remove it: (1) disable the proxy server for your LAN in Internet Explorer. 2) download the process explorer from ms technet. 3) locate and kill the sysguard.exe. 4) finally remove AntiVirus Live. After following all these steps reboot the computer. Protection against future intrusion is mentioned. You should be aware of the ...

Make your board your own by tailoring it to your skating style. You Will Need
This is a tutorial that shows you how to view and control your computer screen from your iPhone/iPod Touch. But this method is for people who have a jailbroken iPhone/iPod Touch. This works on Edge and Wifi. If you are having problems connecting try going to control panel then security center then turn your firewall off. Also try turning off anything like virus protection.

Eric shares his latest Garden Smart Tip and Ideas. A wonderful addition to your patio garden would be an ornamental fruit tree. Eric shows us a beautiful example of a 'Moro' orange. It's a fantastic tree in a container. There is a lot of flexibility that you have with fruit trees in containers. You can move them around to sunny spots on the patio. In the wintertime you can move them indoors for protection. These trees have great ornamental value plus they have the added benefit of providing a...

Is it time for your planned hiking adventure? Hiking is great, but mountain hiking, through the brush and rocks, is even better. Going for a hike in the mountains can be exhilarating, but it also has its dangers. Make sure you pack for the occasion.

Once we recover from the respiratory infection pneumonia, our lungs are better equipped to deal with the next infection — thanks to some special cells that take up residence there.

As we first reported here on Gadget Hacks, Google's new Pixel and Pixel XL smartphones come with an unlockable bootloader, with the exception of models sold by Verizon.

Before you figure out how to strip the paint on your car to bare metal, you should should first ask the question, should I strip all of the paint off. Depending on the type of job you're doing, it may actually be better not to strip all of the paint off.

Adding to the recent recent slew of bugs and issues within iOS 7, it now seems that emails sent with attachments are not encrypted, despite Apple's claims that they are.

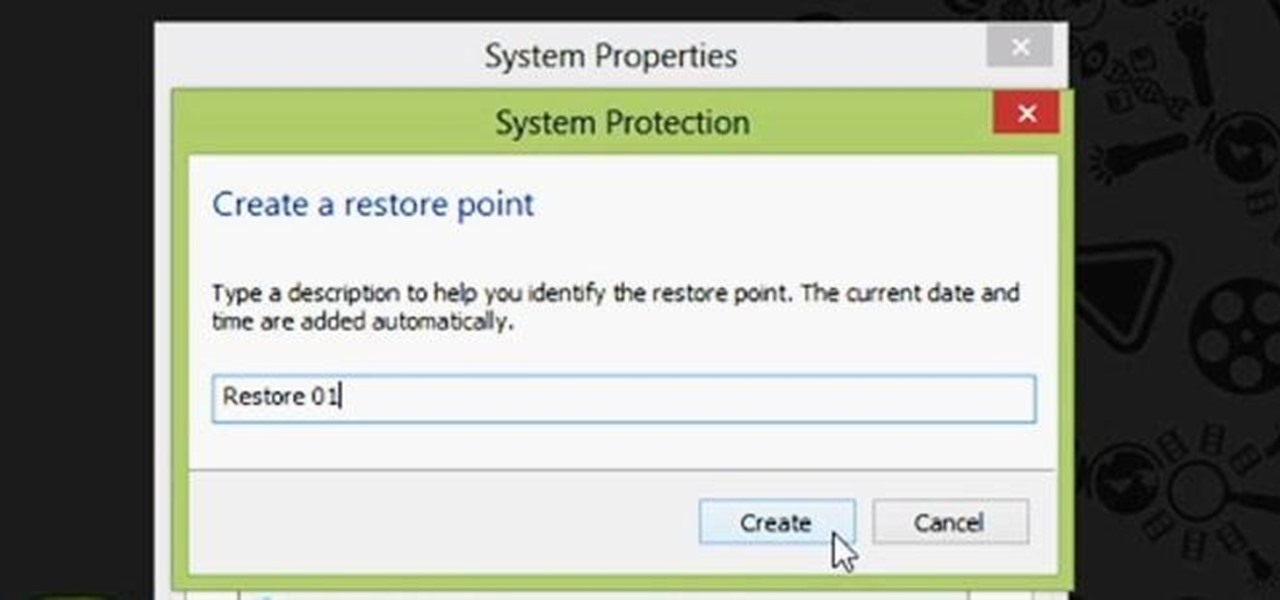
Restoring your computer to a previous point is an extremely important thing if something goes wrong. I've restored my computer at least a dozen times after downloading some suspicious software or running into an error I couldn't remedy on my own.

Bill D., the tech lead at all3sports.com takes us through the steps involved in unpacking and assembling a brand new bicycle. The first he says is to set up or insert the seat post. He recommends using a work stand if you have one at home. He says not to unpack everything at the beginning, but to just expose the seat pack first. Use a wire-cutter to get rid of the film protection used for packing. He has mounted the frame-set on the work stand. The seat post goes into the frame-set. He asks t...

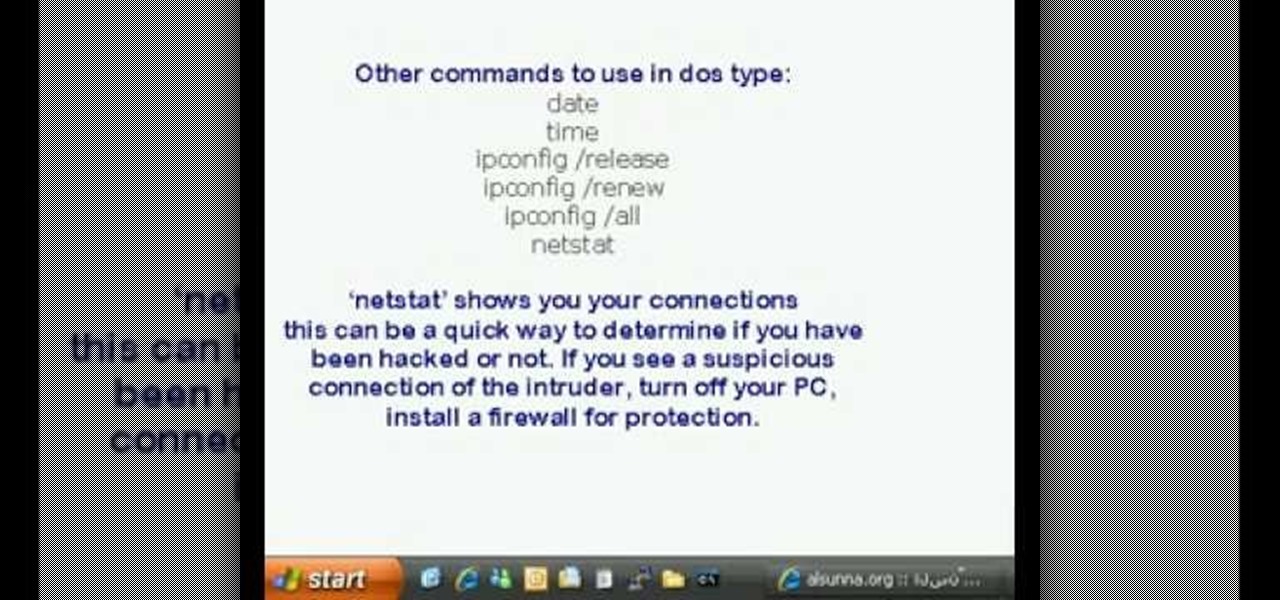
This is a video tutorial in the Computers & Programming category where you are going to learn how to find and ping your IP address. Go to start > run and type in "cmd" to get the DOS window. Here type in "ipconfig" and hit enter. If you are online, your IP address will be displayed. If you are offline, go online and try again. Then in DOS type in "ping yahoo.com". This is to see if you can connect to Yahoo. If you are online, the site will reply 4 times. If you type in "netstat", it shows yo...

Spending five minutes on applying makeup every morning is a lot better than going through the day looking like a sleepy mole person, or, even worse, looking so pale people thinky you're dying of a fatal disease.

Patti the Garden Girl shows her viewers how to install a retaining wall in her urban garden. Garden Soxx is a product that will allow you to make a retaining wall in your garden that will prevent and fix any erosion problem you may have in your yard. After making a small shelf on the eroding section of dirt, place the round Garden Soxx inside the hole, forming a wall against erosion. Create a second layer of the Garden Soxx that overlaps with the first for maximum protection again any soil er...

Learn to steal Kim Kardashian's pin curls and bangs with this video tutorial! Items needed: curling iron, straightener, blow dryer, hair spray, mousse, dual prong clips or bobby pins, comb and medium length bangs.

For $0.25 per transaction, PayPal will soon be allowing you to transfer money through their app that will get delivered within seconds rather than days.

It starts innocently enough, with a nosy friend hovering over your shoulder to see what you're texting. Somehow, that doesn't satiate their inexplicable thirst for curiosity, so the first chance they get, they're rummaging through all of your super private photos—even though you told them not to.

This science experiment deals with sublimation of dry ice into carbon dioxide (CO2) gas. In the video, I'll demonstrate how pushing a quarter into a block of dry ice makes the quarter scream and shake vigorously.

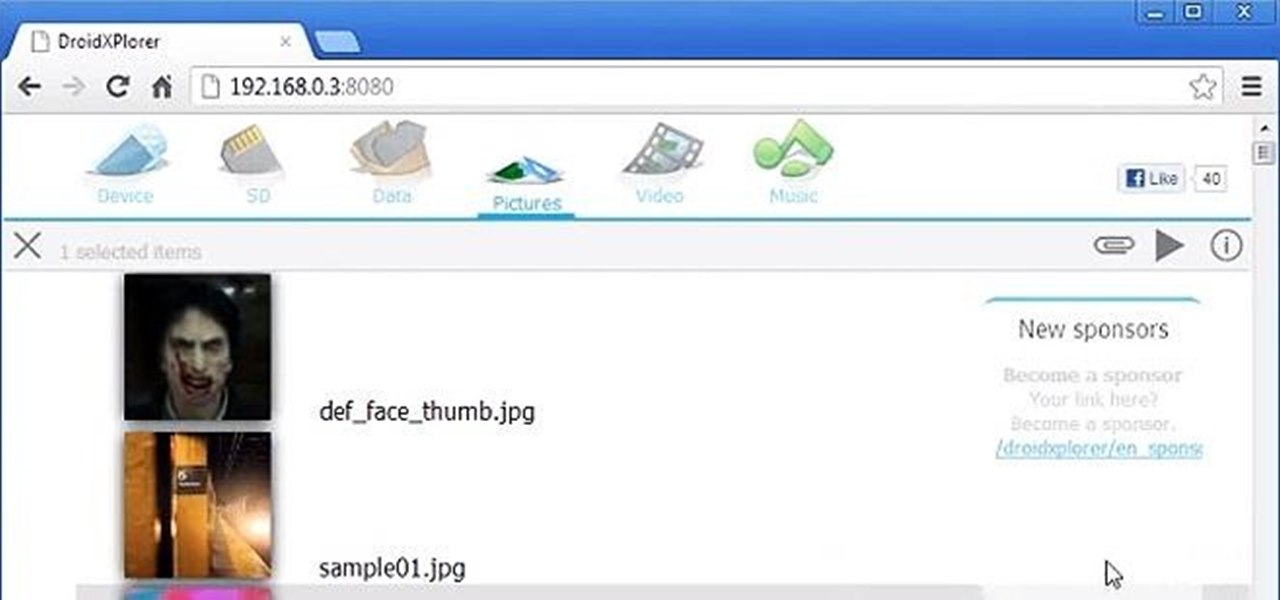
Want to search through your Samsung Galaxy S III or other Android smartphone using only a web browser? Thanks to XDA-Developers member Metal Droid, you can now access and download anything from your phone through any browser on your computer using DroidXPlorer.

Looking to master the art of friendship bracelet making? In this tutorial video, Sherr Bear goes over four different kinds of friendship bracelets, and then goes on to teach the most simple kind, what she calls the "spiral" also known as the "Chinese Stiarcase". Materials you will need include scissors and three to five different colors of string (or what is sometimes called "floss" at stores).

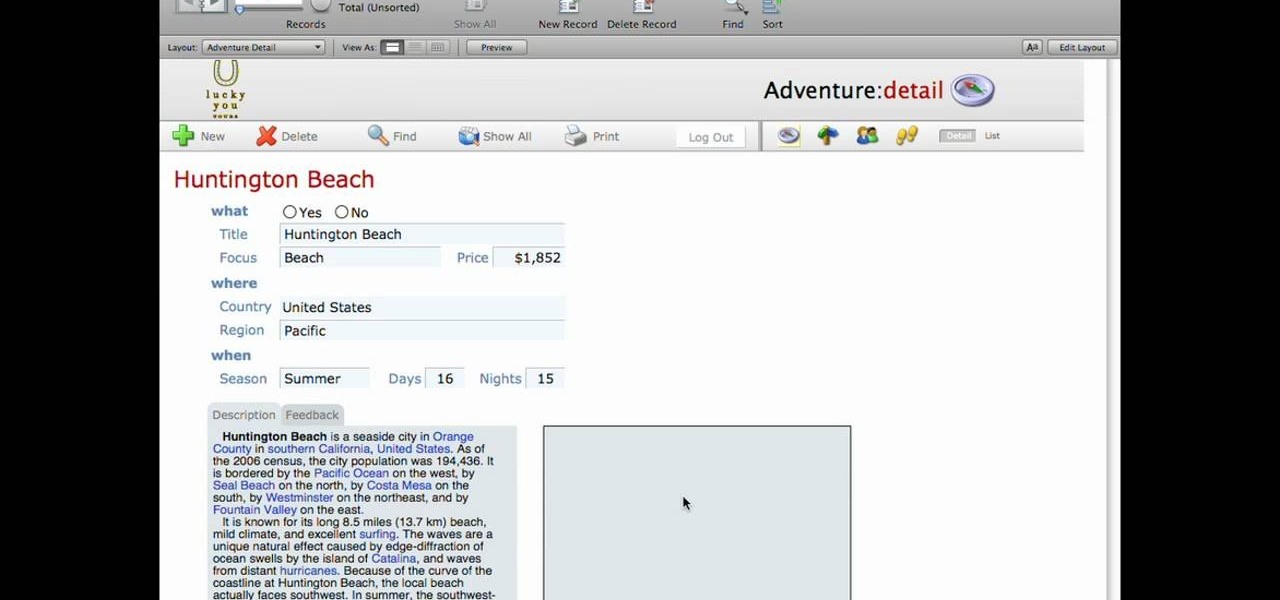
This lynda.com video tutorial shows how to use container fields with FileMaker Pro 10. When you want to create fields in FileMaker database you have the choice on what kind of fields you want to make. Many general fields are self explanatory like text, date etc., but there is a special kind of field called the container field. FileMaker Pro container field is a versatile data type in that it can store any kind of binary data. Container fields can be used to hold binary data in four broad clas...

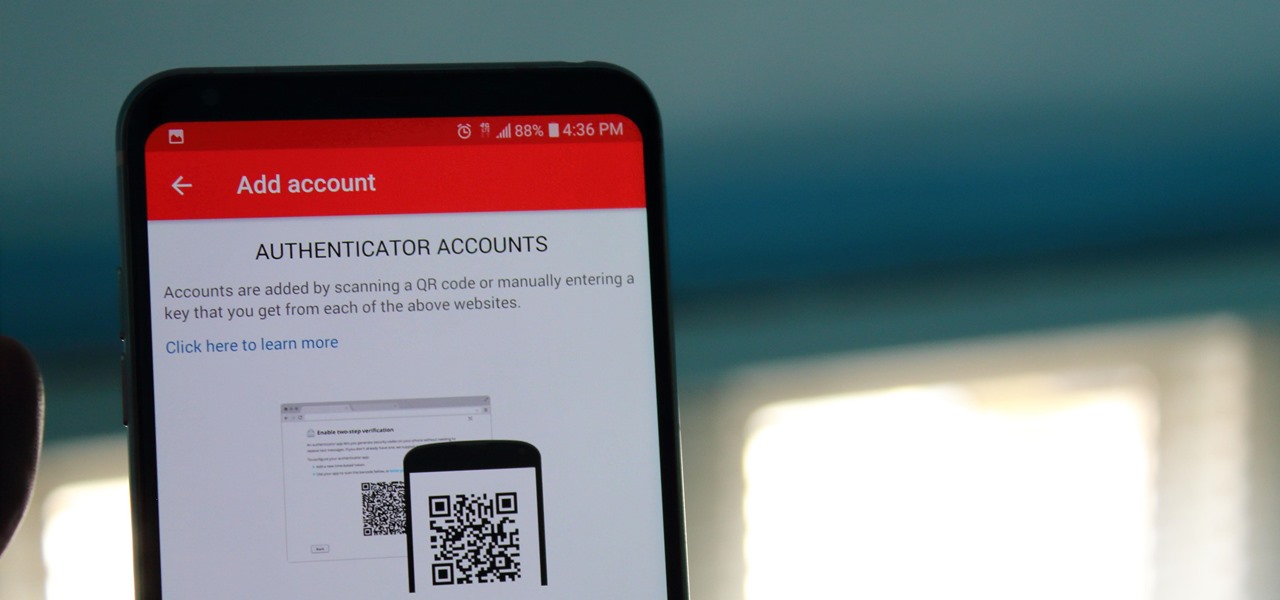
If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

One unique feature of Firefox Mobile is extensions. Extensions allow users to add in features that didn't originally come with the browser. These add-ons provide an array of features, including improvement to privacy and security.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.

It recently came to light that a number of Android phones are unable to stream HD video through services like Netflix, Google Play Movies, and Amazon Prime Video. If you're worried that your phone may be affected, there's a simple tool you can use to find out for sure if you can actually stream video in 720p or higher.

On July 20, 1969, humans set foot on the moon for the first time. But some say our microbes beat us there. With the Space Age came new questions about microscopic invaders from outer space and concern about where we are leaving our microbial footprints. The questions are even more relevant today.

It's not always easy to get to the root of an infection outbreak. Epidemiologists study infected people, contacts, and carefully examine where the infections happened and when. In the case of a 2012 outbreak of pertussis — whooping cough — in Oregon, scientists just published an analysis of how vaccination status affected when a child became infected during the outbreak.

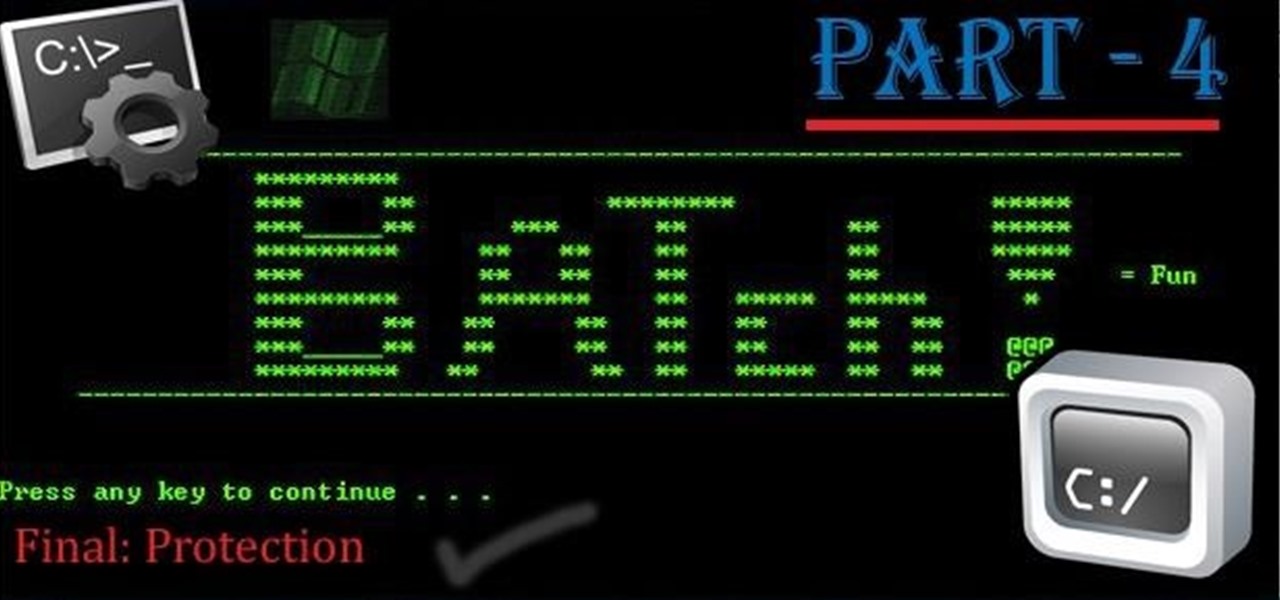
Hi all, Pro Hackers/Crackers, Let's see how we can use batch for our own Protection instead of exploiting someone with it.

While you may not have loads of secret files hiding on your computer, there might be one or two items that need a little extra security, like a file of website logins or a folder of risqué photos.

Former Vice President Dick Cheney was so fearful of attacks, he had his heart defibrillator re-calibrated to block incoming wireless signals so that highly skilled hackers couldn't send him into cardiac arrest.

Most of us have some sort of malware scanner or antivirus program on our computers, but what about our smartphones? A lot of people don't realize that computers aren't the only devices that are susceptible to malicious software and apps—they can follow you on your smartphone or tablet, too.

Increased productivity in Cinema 4D (or other processor-intensive applications) does not always have a linear correlation wtih the speed of the machine that the work is performed on. Nick Campbell of Greyscale Gorilla explains what exactly it is that a fast machine allows one to do, what kind of machine to get, and what kind of work can one expect to do on it.

In our opinion, the best kind of curly hair is the kind that looks the most natural. So rather than tight ringlets that look like they've obviously been twirled around a curling iron, we're talking about loose, carefree waves that are slightly undone.

There's a lot of misinformation about VPN services, and it stems from the fact that not all of them are created equal. Some focus on privacy, others on security, and a few VPNs are seemingly even purpose-built for the polar opposite: data collection. We made this guide to help clear the air on some of these issues while objectively ranking the best of the best.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.

I've had a thing against bananas ever since Mario Kart; not only do I believe it's the worst weapon in the game, but it's also a very funny-looking food. Nevertheless, bananas are a great source of potassium, and I can't overlook that.

We share links on an almost daily basis, usually not even thinking twice about it. Whether you're sending a funny cat video to your sister, or letting your coworker know where to go to download relevant files, there are plenty of reasons you might be giving someone a URL.