September is nearly here, which means new iPhones are, too. We're looking forward to iPhone 11 Pro and 11 Pro Max, as well as the more affordable iPhone 11R. All three iPhones will run iOS 13, so Apple's entrusting beta testers to ensure its new OS is ready. The latest update, developer beta 8, is now here for us to test.
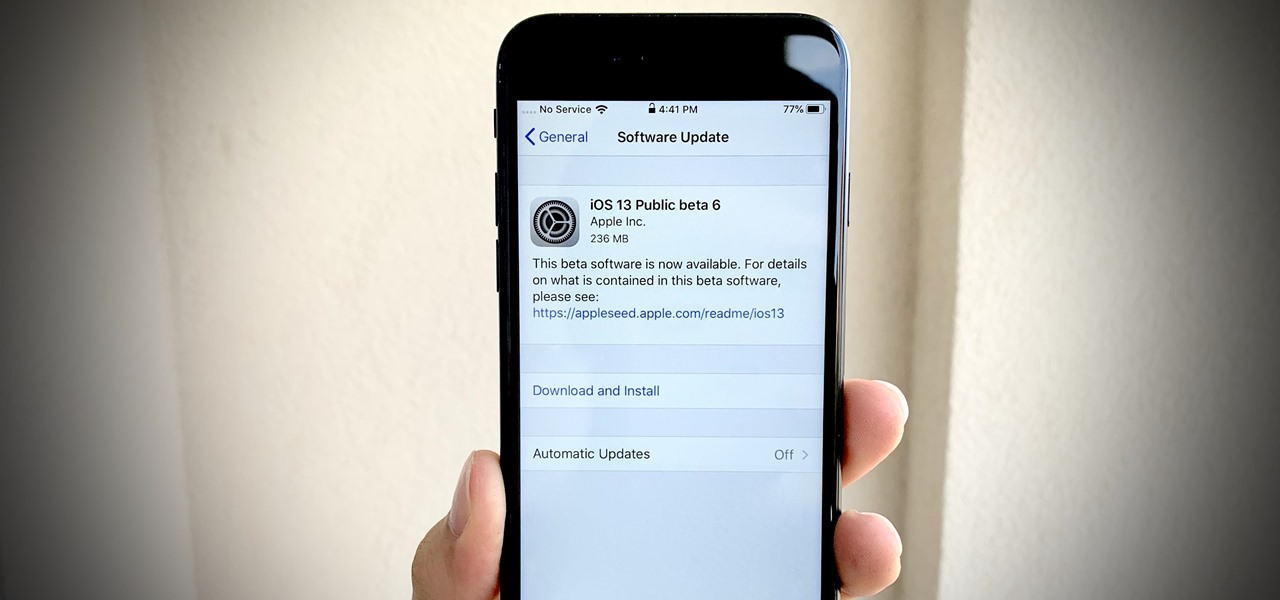
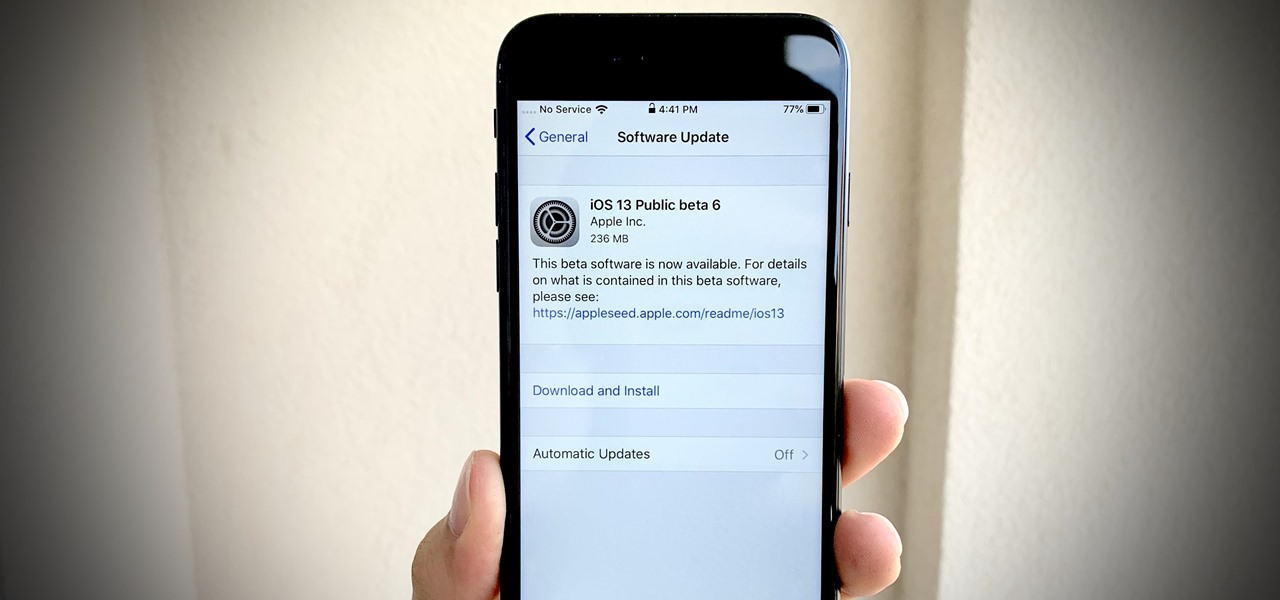
Apple dropped the sixth public beta for iOS 13 today, Aug. 15. This public update comes just hours after the release of developer beta 7, an interesting move for Apple. The company has recently stuck to a schedule of seeding the public beta at least one day after the developer beta, presumably to weed out any debilitating bugs that might have gone unnoticed.

Apple's sixth iOS 13 developer beta was a welcome update for us beta testers. New options for toggling Dark Mode, a way to hide website previews when peeking links, plus UI changes made for a significant iOS 13 upgrade. We're hoping Apple continues this trend of fun and excitement with the release of iOS 13 dev beta 7.

Life's pretty good for iOS public testers — we get to check out new iPhone features months before the general public even knows they exist. That said, we aren't first to the party. Developers get priority during beta testing, as evidenced by yesterday's iOS 13 dev beta 6 release. It's not all bad though since Apple just released the public version of that software, public beta 5, this afternoon.

If tradition holds, we're roughly one month away from Apple's big iPhone announcement. While we're excited to see what will mainly be a significant camera upgrade, it's not all about the hardware. Apple will also release the official version of iOS 13 to coincide with the iPhone XI. Before then, however, iOS 13 needs beta testing, and developer beta 6 just hit on August 7.

Apple just seeded the fourth public beta for iOS 13 to software testers today, Tuesday, July 30. AppleSeed participants saw this beta one day early, alongside the release of developer beta 5. Now, developer and public testers alike are up-to-speed with the latest in iOS 13.

Beta testing for Apple's big upcoming iPhone update, iOS 13, is well underway. So far, each of the four beta versions we've seen brought new features and changes to the table, many of which were never even mentioned by Apple during WWDC in June. Now, it's time to do it all over again, as Apple just released the fifth developer beta for iOS 13.

This clip presents an overview of the general technique required for pairing a mobile phone with a headset via the Bluetooth wireless protocol. For detailed instructions, and to get started pairing your own cell phone with Bluetooth-enabled devices, take a look.

Adding resistence in the form of weights to your workout is the best way to increase the difficulty of the exercise. This forces your muslces to work harder and makes you burn more fat (which is always a good thing).

This video takes us through a process of speeding up our internet connection using OpenDNS.com. Open the webpage and go to solutions and click on the icon open the DNS page and it lists computer or router, she selects computer and list of operating system is listed, she selects vista. She goes to start and selects control panel, click on view network status and connection, in that select view status and then click on properties and on the networking page, go to internet protocol version 4 and...

This medical how-to video demonstrates how to do an equipment setup for hemodynamic monitoring. Follow the instructions and protocol for the equipment needed to setup hemodynamic monitoring before the physician arrives. This procedure is typically used for pulmonary artery catheter insertion.

Going to school to become a nurse? Then one of the many things you will do as a nurse is trying to keep your patients comfortable while they are in the hospital. Follow along in this nursing how-to video and watch as the nurse places an abductor pillow under a total hip replacement patient. Sue, a physical therapist, shows you the correct protocol for administering abductor pillows.

Studying to be a nurse? Then follow along with this nursing how-to video to learn how to administer an intradermal injection. This injection technique is very common in nursing. Watch and observe the nursing student as she shows you the proper protocol for an intradermal injection. Before starting always make sure to check the doctor's orders and have all your equipment handy.

Studying to be a nurse? Then a very common procedure in nursing involves removing a saline lock or an IV line. This procedure is also called DC IV, or discontinue an IV. Follow along in this nursing how-to video to learn the proper protocol for discontinuing an IV line. Before DCing the IV always double check the doctor's orders and have your materials handy.

Studying to be a nurse? Then a very common procedure in nursing involves removing a saline lock or an IV line. This procedure is also called DC IV, or discontinue an IV. Follow along in this nursing how-to video to learn the proper protocol for discontinuing a saline lock. Before DCing the IV always double check the doctor's orders.

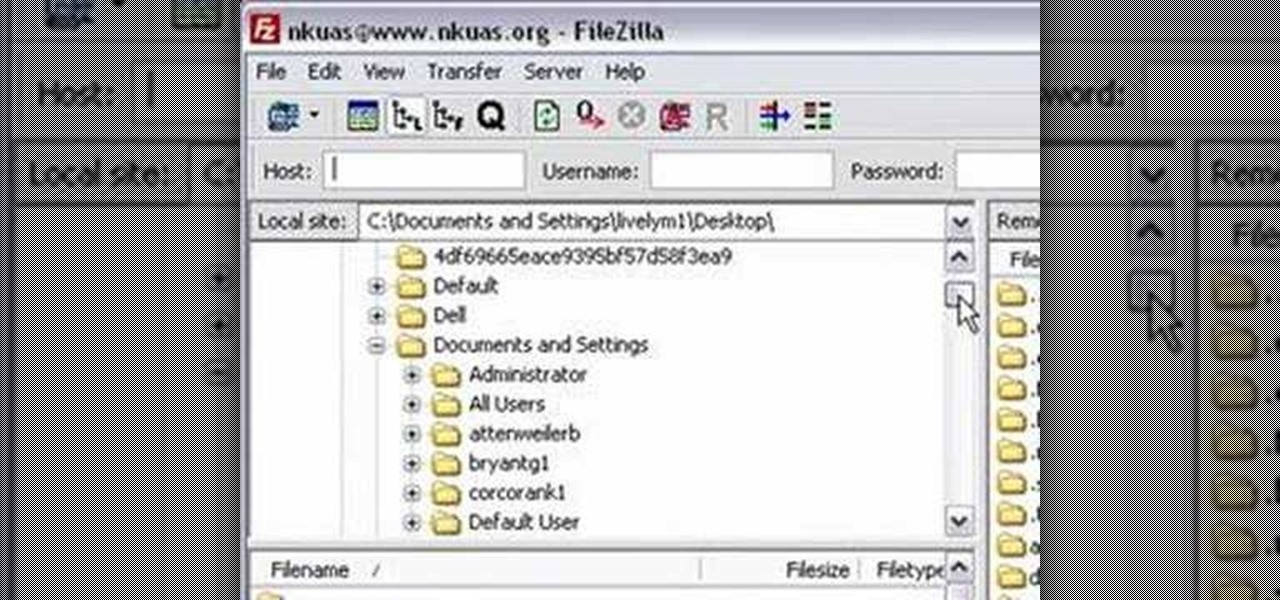
In this video tutorial from Matt Overwine of the Instructional Design Group at Northern Kentucky University, you'll find instructions on how to use the FileZilla FTP, or file transfer protocol, client to upload to the web. FileZilla is available for both Mac OS X and Windows XP and Vista. For more information, and to get started using FileZilla for yourself, watch this handy how-to.

Armis Labs has revealed eight vulnerabilities, called "BlueBorne", which put 5.3 billion Android, iOS, Windows, and Linux devices that use Bluetooth at risk. With it, hackers can control devices, access data, and spread malware to other vulnerable devices through networks. In this post, we will learn about the vulnerabilities, then look at how to find devices that have them.

With more people joining the internet scene each day it's important that it's security is.. well it has to be good. Of course everything can be hacked and that's the way hackers work. They know there IS a vulnerability but they don't don't know the rest. in this article i'll try to explain the big difference between HTTP and HTTPS

Some of us woke up at the KRACK of dawn to begin reading about the latest serious vulnerability that impacts the vast majority of users on Wi-Fi. If you weren't one of those early readers, I'm talking about the Key Reinstallation Attack, which affects nearly all Wi-Fi devices.

Welcome back, my novice hackers! This new series on Bluetooth hacking was inspired by a recent episode of Mr. Robot (my favorite TV show). In episode 6, Eliot hacked the bluetooth keyboard of the police office in order to hack the prison and release his nemesis, Vera. This is just one of the many hacks we will explore in the series.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

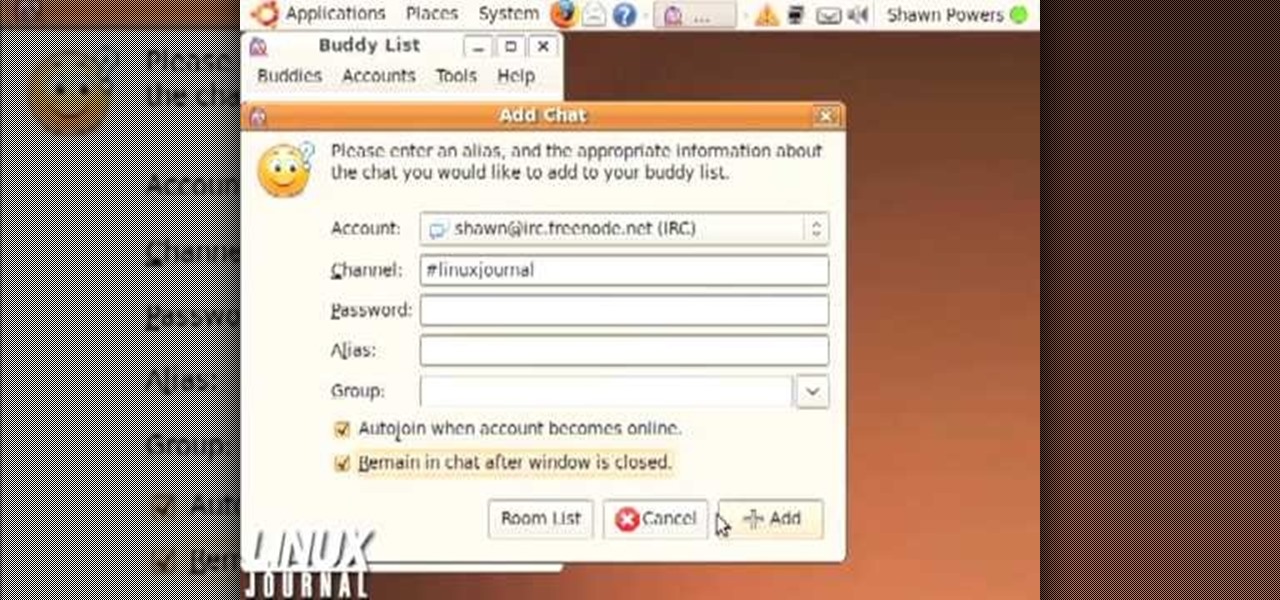
This video shows how to enter an IRC chat with a program called Pidgin, which is normally an instant messaging client. First, you should open Pidgin and open the protocol IRC, selecting or creating a username and changing the server to irc.freenode.net in order to connect to the Linuxjournal channel. After connecting to the channel, wait until you are connected. At this point, you should still not be able to see anything, so you have to go to "Add Chat" and join a channel, in this case #Linux...

In this tutorial above, you'll be finding out how to quickly set up IMAP in order for it to run with your Gmail account. Now first thing is first, IMAP has nothing to do with apps or anything else that is Apple. What it stands for is Internet Message Access Protocol. And what it does is that it's basically email but differs from the other email retrieval program, POP. It keeps email messages in the server while POP deletes them. So check out how to set it up with your Gmail account today! Goo...

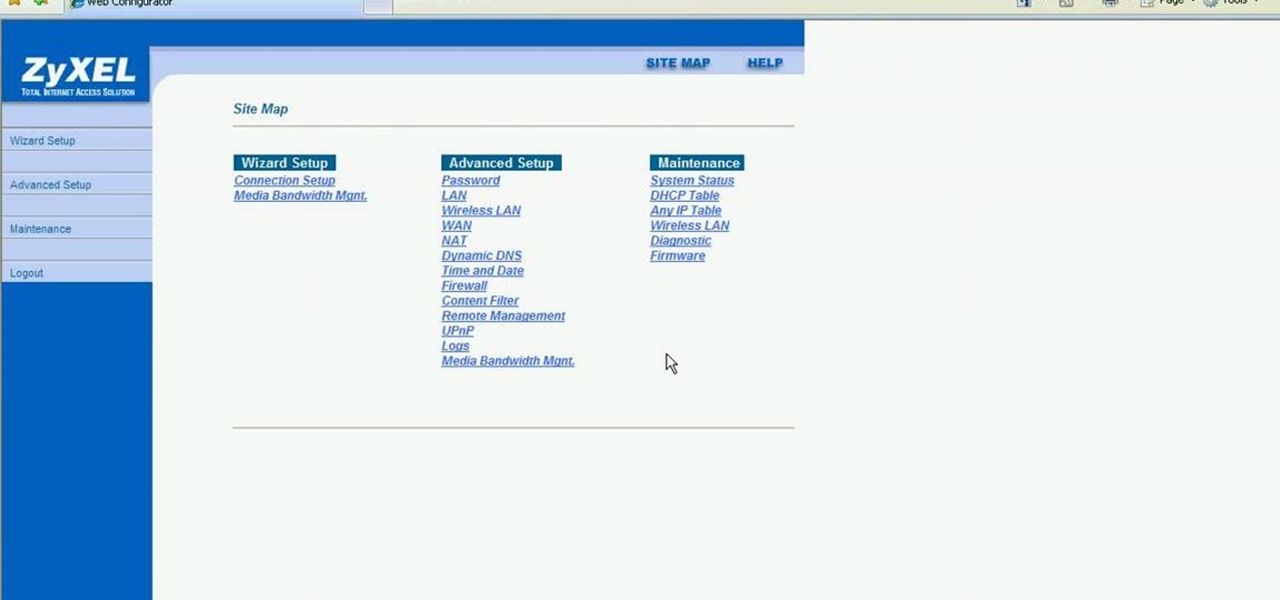
This video shows how to secure a wirelees internet connection on your Zyxel P-660hw-t1. For this, first click on Start button and open Internet Explorer(or any other browser). On the address bar of the browser, type in the IP address of your router. On the next page, enter your password and on the next page, either change the password or ignore. On the next webpage, under Advance setup, click on Wireless LAN. On the next page, click on 8021xWPA. Select authentication required and then click a...

POP3 stands for Post Office Protocol, a way in which you receive mail on the internet, paralleling how mail is received in your mailbox. To set up your POP3 for Outlook, go to tools, click “view or change existing e-mail accounts’ and press next. You’ll be able to see a list of your current email accounts that you can change or remove. When you select an email and press change, you’ll be able to see the account in detail: the email address, the POP3 and SMTP server information, and th...

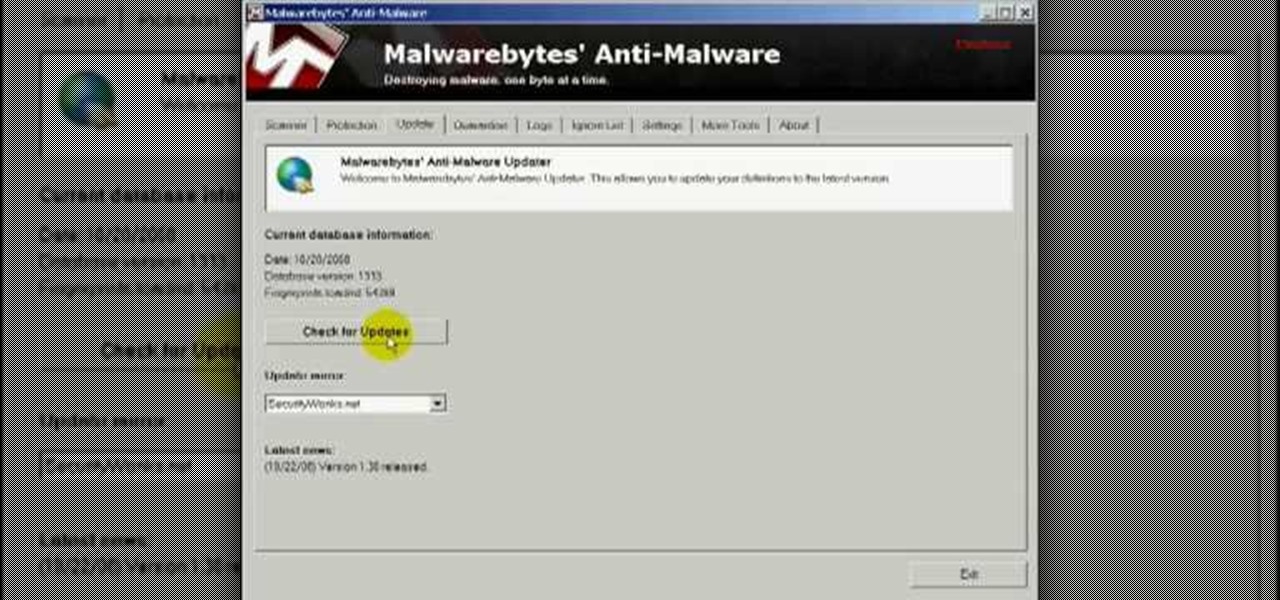
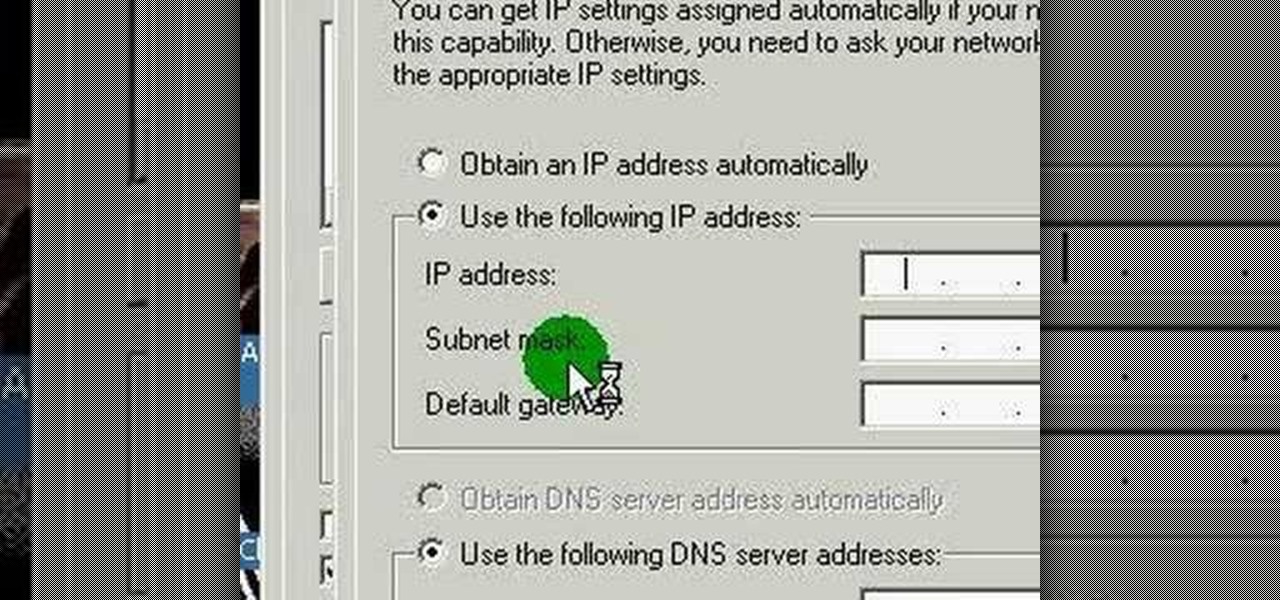
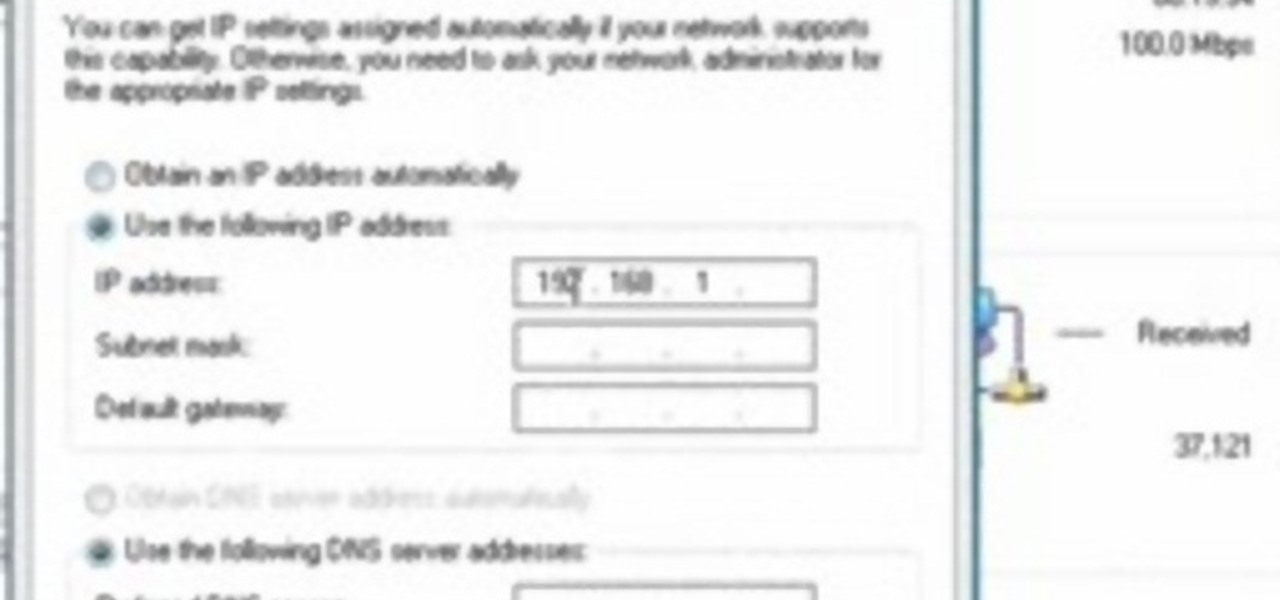
In this video you will learn how to remove the Trojan .dnschanger virus with Malwarebytes. To see if you got a Trojan .dnschanger virus go to your network connections right click on Local Area Connection, select proprieties, click ok internet protocol, click again proprieties and if you got an ip address at preferred DNS server that means that the Trojan entered a fake ip address. You can remove the Trojan. To do this first run the Malwarebytes application, click on the update tab, click on c...

In this video tutorial, viewers learn how to find an I.P. address. Every computer that has Internet connection has a unique identifier called a Internet Protocol Address. This video provides 2 methods on how to find your I.P. address. The first method is to simply open your web browser and search on the Internet. The second method is to click on the Start menu and select Control Panel. Click on Network and Sharing Center. Right-click on your connection and select Status. There, users will be ...

iPhoneElite8 teaches viewers how to easily SSH into their iPhone or iPod Touch using Cyberduck! First, open Safari, Google 'Cyberduck Space Mac". Click the very first link you get and download Cyberduck on the right. Now open Cyberduck on your computer. Get your iPhone of iPod Touch and open up settings. Under settings, connect to Wi-Fi, and copy down your IP address that shows. Go back to Cyberduck, go to open connection and click on 'protocol'. Open up SFTP and copy the IOP address you got ...

This video discusses how to change your IP address in Windows XP. Start by clicking on the Start Button and then Run. Type in "cmd" and press enter. This will open a Command Prompt box. From here type in "ipconfig" which will show your current IP configuration, including your IP Address, Gateway, DNS Servers, etc. Next type "ipconfig /release". This will release all IP information from your current network adaptor. Next open up network connections, right click on Local Area Connection and sel...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to organize your desktop with Microsoft Scalable Fabrics.

This medical how-to video demonstrates the simple steps for inserting a nasogastric tube. A nasogastric tube is more commonly known as a NG. Follow along and learn the basic protocol for doing this procedure. To do a NG tube insertion you will need 14-16 French gauge nasogastric tubing, water soluble lubricating jelly, catheter tip syringe, suction drainage system, and hypoalergenic tape. For your patient, you should have ready a cup of water with a straw, emesis basin, and a towel.

Studying to be a nurse? Then here is a nursing how-to video that teaches you how to do a central venous access. Every nurse should know the basics of this technique, follow along and see how easy it is to draw blood from a central line. These medical tips are sure to help you pass your nursing exam with flying colors. Remember when performing a central venous access, all caps must be replaced each time blood is drawn. You must swab the port for 1 min prior to withdrawal. Follow your hospital'...

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

This video describes that how to use the file transfer protocol prgram. First we have to download filezilla to our computer. Go to google and download it first into the computer. There is a username and password to use the FTP. Open the filezilla and come to Host. There we have to type ourdomain.com or ftp.yourdomain.com. Next you have to enter the username and password. Next you have click quickconnect there. Then you will connect to your webserver. In filezilla there are four quadrants ther...

This video tutorial from iTouchMaster2 shows how to SSH to iPod or iPod Touch using FileZilla application.

Steps to Configure Your Modem/Router are: 1. Open Network connection and click properties

This video tutorial shows how to open a port for torrent downloading on your computer. Click Start menu, type cmd command in Search area. In cmd window type ipconfig and press Enter. Remember or write down your IP adress. Type exit and press Enter to close cmd window.

This video shows the method to SSH into iPod Touch 1G or 2G. You need an iPod touch 1G/2G with Firmware 2.2.1 or previous (Windows), a Windows based computer and a jailbroken iPod Touch which has Wi-Fi connectivity. Open Cydia, go to search and type OpenSSH and install it. Go to settings, Wi-Fi and click on the blue arrow next to the network. Copy down your IP address from the resultant window. Open WinSCP.net and go to Downloads, installation package. Install the package and open WinSCP from...

This Lynda tutorial teaches how to use the Logic pro, a songwriting application. Midi sequencing and quantizing is the main focus of this video. Midi is a short name for Musical instrumental digital interface. Midi is not sound. It is a low resolution computer protocol, developed in early 80’s to enable computer to communicate each other. Midi is fast, simple and reliable. It has a intensity stream. In this project, Scot Hirsch explained how a midi file is manipulated in Logic pro. Midi file ...

Going to be a nurse? Then one of the procedures you are sure to encounter in the hospital is the removal of an arterial line. Follow along in this nursing how-to video to learn how to remove the arterial line from a patient. Remove of you a line is also known as discontinuing the line. In shorter terms many nurses also say DC the line. Follow along and learn the standard protocol for removing arterial lines.