Legacy Games, developer of mobile games for children, has just updated Crayola Color Blaster, an augmented reality Android adventure for Google Tango devices, with new content.
Early this morning, Unity held their keynote at GDC 2017 in the InterContinental San Francisco hotel. During the event, they talked about their upcoming roadmap and many changes that are coming down the pipe. This list included the lighting explorer, progressive lightmapper, the new 4K video player, native support for Vulkan graphics, TextMesh Pro integration, and the one that really excites me as a HoloLens developer—dynamically/runtime created navigation meshes.

Most people know atopic dermatitis by its common name, eczema—that dry, flaky skin that itches incessantly. Along with the scratching comes frequent skin infections, often with Staphylococcus aureus.

At the WinHEC Shenzen 2016 Keynote, Microsoft showed off a system running Windows 10 smoothly on an ARM processor. This could be great news for developers of mixed reality software.

China's e-commerce site Alibaba has been making heavy investments in augmented and mixed reality startups. In February of this year, they led a $793 million round of Series C financing of Magic Leap. And now they've just invested in Israeli-based InfinityAR, which acquired $18 million in its Series C financing.

HoloMaps, an application by Seattle-based Taqtile, is available for free on the Windows Store. Taqtile, whose Vice President of Product Management was Microsoft's former Director of Business Development, is one of the few partners currently in the Microsoft HoloLens Agency Readiness Program. This interactive 3D map they have created, powered by Bing, offers more than just a top-down view of the world on the HoloLens.

While you can't turn art into a formula, the film industry has managed to come stupidly close. While many storytelling principles still stand across mediums, successfully crafting a compelling, immersive narrative in virtual reality requires a brand new rulebook. Through trial, error, and success, writer/director/editor Adam Cosco figured out the right rules to follow (and break) in "KNIVES"—his latest 360-degree short film. The film tells an old-fashioned tale of a woman, Kelsey Frye, strugg...

When we talk about augmenting our reality, we often first think about vision instead of our other senses—but there's more to an immersive experience than what you see. One inventor figured out how to utilize sound and touch to create a simple, upgraded version of laser tag that you can play with your smartphone.

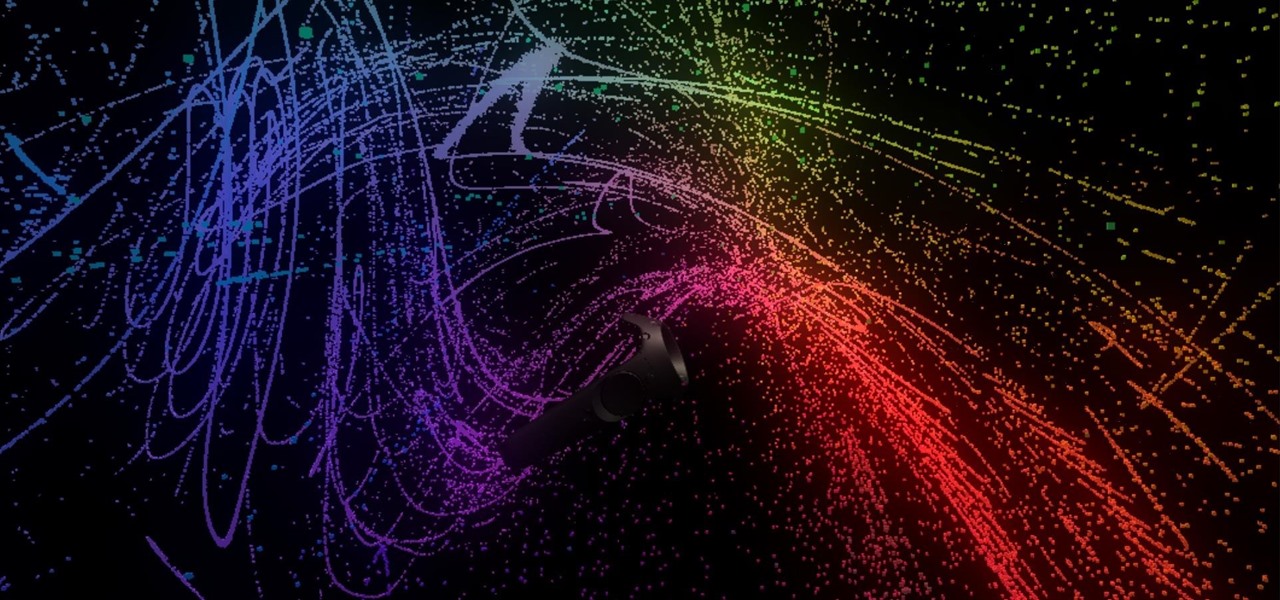
Want proof that user experiences matter? Look no further than the HTC Vive and Omnipudding's particle generator, GPU Cubes VR, which lets you interact with thousands of colorful, cubic particles in a black void. If this was a simulator for your computer only, controlled with a mouse or keyboard, you'd be bored in seconds—but it's just simple, instant fun on the Vive.

Imagine if you combined Tasker with your favorite live wallpaper—that's roughly the gist of a new app from developer feedK. With this one installed, your home screen background will finally be aware of its surroundings.

In this tutorial I am going to show you how to create an undetectable Meterpreter Trojan using a Domain name. I have taken a few guides/tutorials and built it into one. The first part is creating the DNS Payload. The second part is creating the Executable file. Part 3 is using both in Shellter to create your undetectable Trojan. Part 4 is setting up your listener using Armitage.

Not content with bringing the first untethered mixed reality headset to market, Microsoft wants to expand their Windows Holographic operating system beyond HoloLens into vastly more robust technologies.

Most sandboxes wait for children on a playground or the occasional zen garden raking. This one combines light, sand, and depth cameras to create a completely malleable topographical map you can alter with a brush of your hand.

Sautéed mushrooms and boiled green peas simmered in creamy, spicy onion-tomato gravy. Mushroom mutter gravy is typical a North Indian gravy. It is made from onion and tomato. it is spiced up with regular spices. Just like other vegetables, these mushrooms are also healthy and nutritious, good for our body.

This card is awesome, there is no other words for it! It is pretty, eyecatching and just so gorgeous, using cardstock and vellum to create a wreath made of embossed roses. There are a few different techniques in this tutorial to make the wreath but they are all easy when you see how. Step 1: Items Used

In a letter dated February 16th, Apple CEO Tim Cook responded to the FBI's demand that Apple create a "backdoor" to bypass the encryption on an iPhone used by one of the perpetrators of last year's terrorist attack in San Bernardino, CA. Cook began the letter by stating that Apple has "no sympathy for terrorists" and has cooperated in giving the FBI all of the information that it has available.

Welcome to my very first tutorial ever. Today I will be teaching you how you can use Arachni to scan vulnerabilities of web applications. I welcome all criticism good or bad as a teaching method for myself.

Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics series, I showed you how to acquire a forensically sound, bit-by-bit image of a storage device such as a hard drive or flash drive, but now let's dive into live memory.

Hello, in this episode of In the Kitchen with Matt, we will continue with the Star Wars theme, last episode we made Star Wars Death Star Peanut Butter Cups, this episode we are making Star Wars Death Star Popsicles. So we are really getting great value out of our Death Star molds, because of the versatility they provide. These popsicles are super easy to make, if I can make them, you can make them! If you have any comments put them down below, and I will get back to you.

Welcome back to another tutorial on functions. Last time, we looked inside memory to see what functions looked like in the flesh and all that Assembly was pretty nasty. At least you have some exposure to it. This time, we will be examining how functions work with the stack.

Welcome back! In the last training session, we covered logical and membership operators. We're going to switch gears and expand our knowledge of lists.

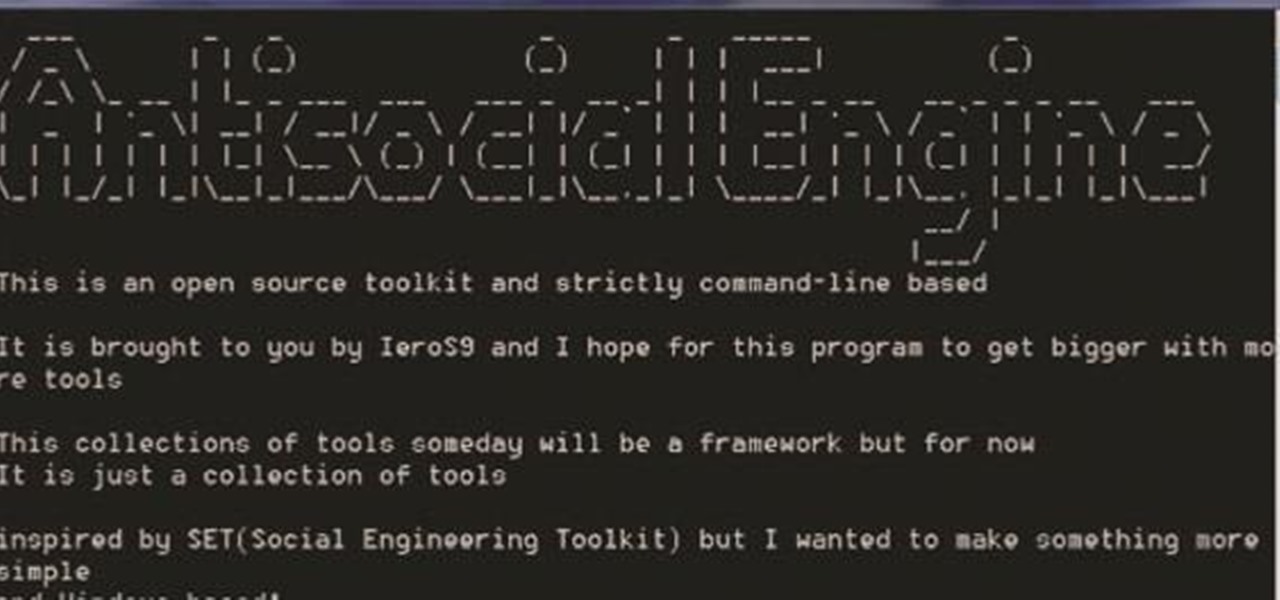
A.E Hi again this is my second post on nullbyte. The first one was on how to make a remote screenshot captor, now I will give you a presentation for a project of mine(I have named It Antisocial Engine) that It is not something extraordinary but will help many guys.

Hello! This is my first post on this awesome website! I know that Windows exploits are less common than the more advanced hacks, but I found something I deem pretty cool and figured why not share it with you all. Alright, enough about me, lets begin.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.

In the wake of Apple Music making its debut on Android devices, Google has finally released its highly anticipated YouTube Music app. With these two tech heavyweights throwing their hats into the ring, the streaming music world is about to get rocked.

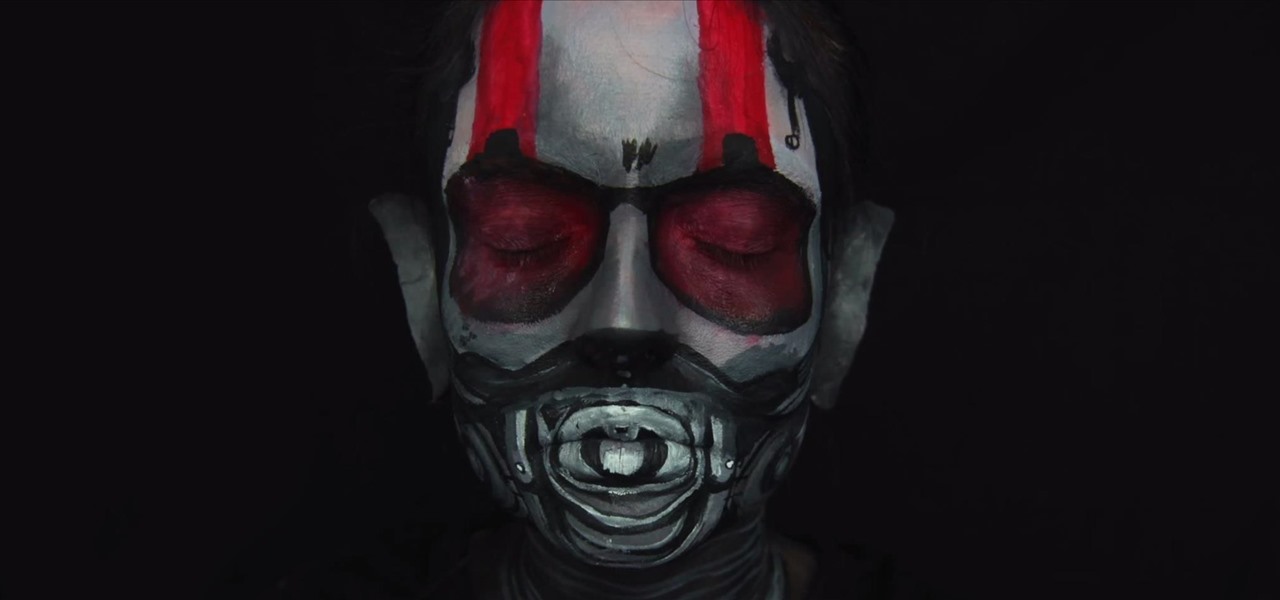
If you don't have the time or patience to build a complete Ant-Man suit from scratch, there's another way to make a Ant-Man costume for Halloween. If you're more skilled with brushes and makeup rather than drills and cardboard, this is the Halloween DIY for you—especially if you're a fan of the Marvel universe.

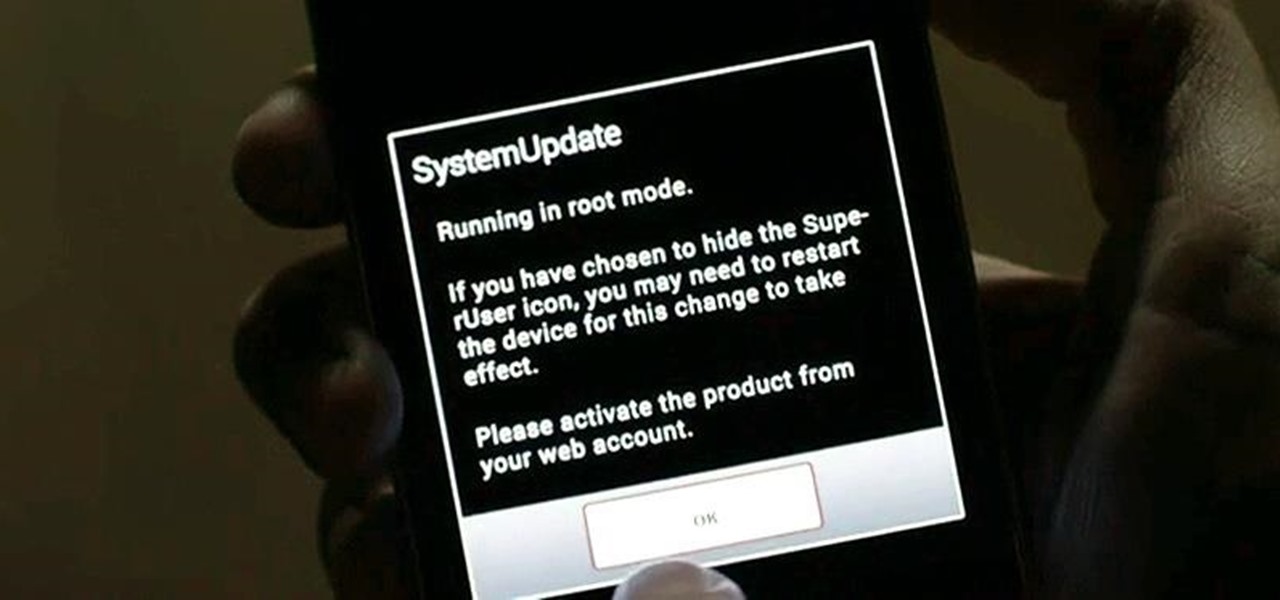
Welcome back, my greenhorn hackers! As all you know by now, I'm loving this new show, Mr. Robot. Among the many things going for this innovative and captivating program is the realism of the hacking. I am using this series titled "The Hacks of Mr. Robot" to demonstrate the hacks that are used on this program.

As Android's de facto virtual assistant, Google Now lets us speak directly to our phones in plain English to answer our questions and perform many basic tasks. With the app open, just say "Okay Google," then wait for the beep, and ask almost any question.

Since the new Mac OS X 10.11 El Capitan is brand new, I recommend installing it on a separate partition on your hard drive. This will keep your current Yosemite system safe from harm, and will let you easily switch back to it should El Capitan become unusable for any reason.

Amazon makes it exceptionally easy to purchase anything you want in just a few minutes. From textbooks for school to live ladybugs, its more surprising when you can't have something delivered to your doorstep in a few day's time.

It's already that time of year again—LG has unveiled its latest high-end smartphone, dubbed the G4. In past iterations, LG released its flagship devices in the fall. But slowly over the course of the past 2 years, the release schedule has been bumped up to be more in line with HTC and Samsung's springtime releases, and further away from the sales-sucking iPhone event each fall.

Hi everyone! Last time we explained what roles Ebp and Esp registers have. We first introduced function's stack frame building, return address and calling conventions, but left some of the concepts floating without a full stop.

Tinder, the extremely popular dating app, has the wonderful tagline, "Any swipe can change your life." However, if you downloaded their most recent update, your next swipe could cost up to $19.99.

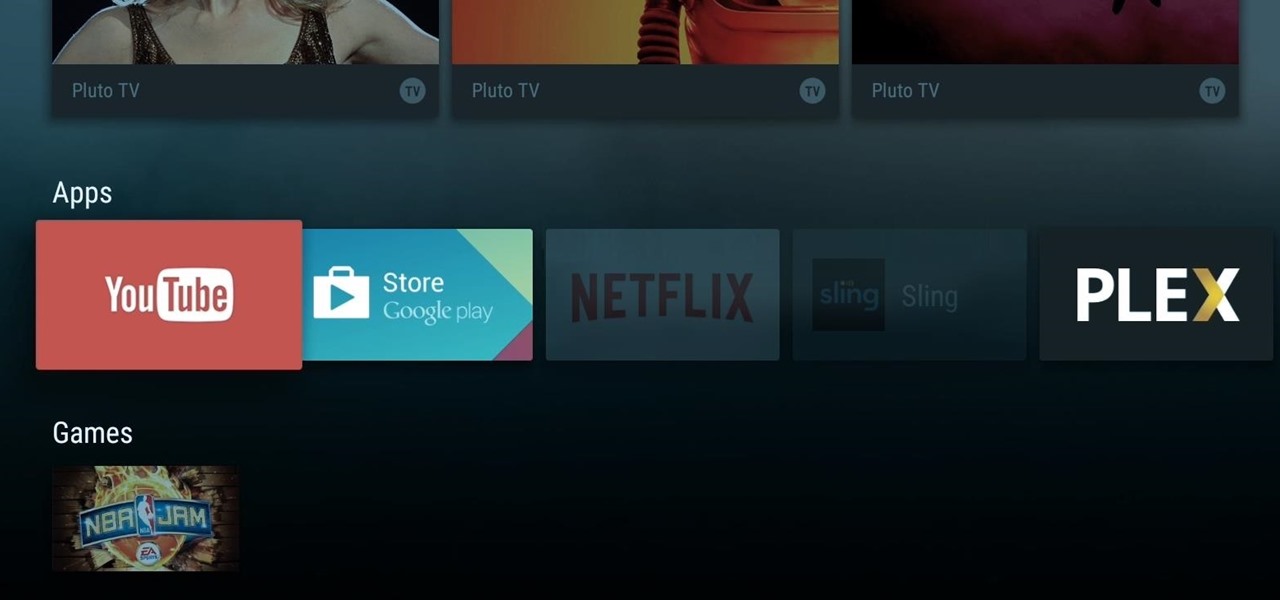
When Google announced its new Android TV platform, one of the features they advertised was a home screen that automatically reorganized your apps based on how frequently you used them. Unfortunately, this feature either didn't make the cut, or is still under development, since the home screen on the Nexus Player always remains static.

YouTube and the National Football League have announced a partnership that should greatly improve the online experience for gridiron fans. In a posting on their official blog, YouTube outlines a deal that will bring NFL video clips to their immensely popular site while bumping official NFL pages up to the top of relevant Google search results.

Using a combination of my phone, laptop, and an arsenal of apps and plugins, I can send pretty much anything to my Chromecast. However, nothing is ever perfect, and the file type that was still giving me headaches were torrent and magnet files.

While CNN, FOX News, and MSNBC are valuable sources of information for what's going on in the world today, they may not be the best news stations to watch if you actually want to learn something. They, along with local news stations, are great at grabbing your attention, but if you truly want to learn something about recent events, you're tuning into the wrong channel.

A great Halloween party depends on the right spooky ambience. Having some shrunken heads in strategic locations is an easy, fun way to get your guests in the right (frightened) frame of mind, and they require items you can easily find in your kitchen or at the local grocery store.

If you have a custom recovery installed on your Android device, the first thing you should have done as soon as you finished installing it was to create a Nandroid backup. But if you didn't, I'm not here to judge—I'm here to show you a much easier way.

Greetings, my friend. Welcome to Null Byte. I am Dr. Crashdump. Linux will be talked about a lot in Null Byte. It's used in most tutorials on this site, actually. You should learn how to use Linux as soon as possible, but where do you start? No worries. Let's figure that out.