I've always wanted to get a bunch of people together to hit up various drive thru restaurants in reverse. I know it's not the most creative our outlandish thing, but I am sure it would turn a lot of heads and muster up plenty of good laughter!

Technology: The Less You Know the Better?

Well i have this friend everyone is always saying he acts gay looks gay he really isnt but i think it is funny that everyone thinks he is so my idea was to buy a penis and when u put the penis in water it grows lol then am going to put it on his pillow by his mouth when he is sleeping im really doing this and then im going to take a pic with him laying there with the penis by his mouth i really did buy one and got it into water now waiting for it to get bigger so i can play it out it will be ...

So you get Spike Jonze or anyone really from the cast to dress up as a woman (maybe Ehren McGhehey cause sometimes he acts like a little girl) Get them to go to a store, walk slowly to the return desk while having squeaking noises following them . have them place a box of open tampons on the desk and tell the cashier the tampons squeak when they walk , how am i to pick up when my Vagina is making noises . Have the cast member walk back and fourth see did you hear that, that's my vagina becaus...

This prank is a prank to pull on the public. What you do is two of the members of the Jackass crew dress in heavy gothic cloths, chains, leather, dyed hair anything that would definitely catch the publics eyes, and even powder your face white (a lot of makeup). Ok once this is done u go to your local pet shop or animal shelter and say you want to adopt a kitten. I am most definitely guarantee that the people there would give you a hard time adopting it or won't let you, but you just keep piss...

If you're like me, you were always jealous of the kids with rich parents who got to ride around in their own Power Wheels cars. Now that I am tall enough to sell my body and time, I find myself attaining childhood dreams like buying my own Power Wheels car. I would not have chosen the Barbie Jeep given the choice, but 40 bucks on Craigslist is an amazing deal.

Facebook unveiled a lot of changes last week, and, as usual, it's causing a lot of consternation and controversy. People within my Facebook, and on Google+, keep asking how to remove the ticker, and are trying, and mostly failing to make sense of the changes.

I was looking around on this site and this article caught my eye. It was about hiding text in ADS or Alternate Data Streams. While this is nothing new in the tech world, it seems that more and more people are looking at ADS for one reason or another.

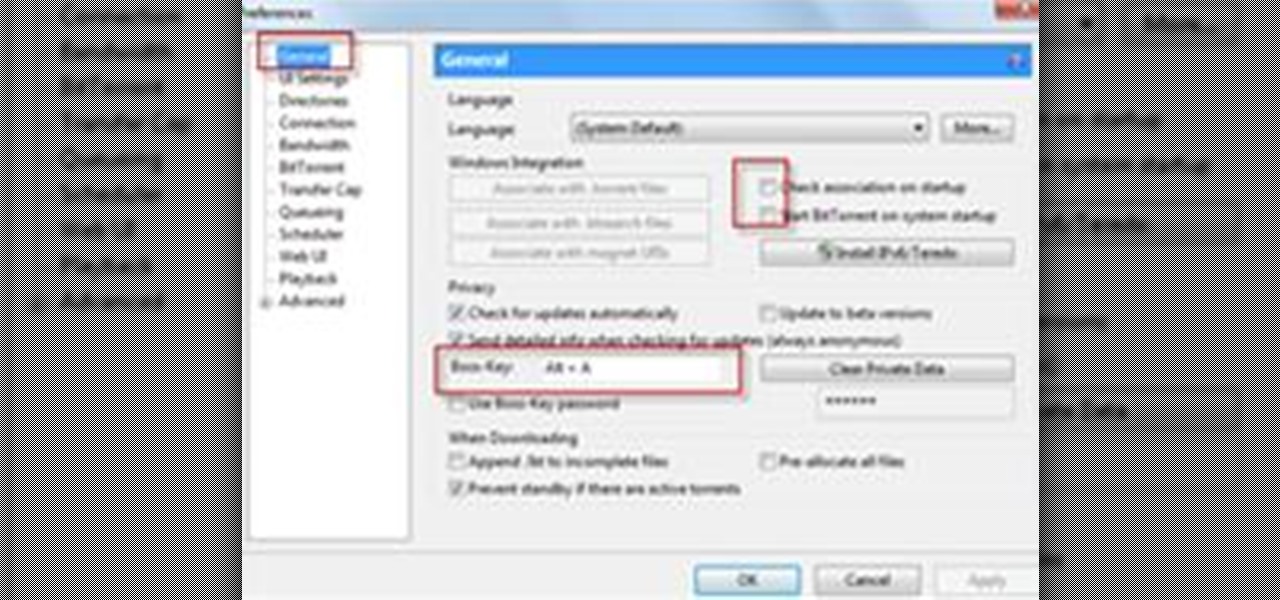
Completely Hide UTorrent and Bittorrent Software in Your PC While It Is Still Running!.

Social Profile Change the privacy settings on your social profile (Facebook, MySpace, Friendster, Twitter, etc.) so that the following information can't be found by a random person who you didn't accept you as a friend:

it would be wonderful if you pick my idea! I am from Lithuania, I love jackass.

SCRABBLE. To some it's just a game, but to me it's life or death. Well, not really, but it feels that way anyway. On a normal weekend, a game becomes much like Jon Thomas' "friendly game of death Scrabble."

Would you like to create ghost flames or other custom paint effects, but don’t know how? Here is a quick, easy, and inexpensive method. This method does not require a paint gun, airbrush, or even paint. Follow this step-by-step procedure and watch the video tutorial and you’ll be able to do this to your own car. Best of all, if you don’t like it, I’ll even show you a method for removing it. All it takes to do this is 1/8 inch fine line tape, 3/4 masking tape, a piece of 3000 grit sandpaper, a...

Have you ever noticed that whenever you setup your voicemail account after getting a new cell phone number, it asks you to create a security pin to access your voicemail from other phone lines?

Obesity has ballooned into a worldwide epidemic. The World Health Organization estimates that 2.3 billion adults will be overweight and 700 million will be obese by 2015. Over 20 million children are overweight today. The reasons for these distressing figures are common knowledge: The international switch to high sugar, high fat, low nutrient processed junk foods prompted by global fast food chains and their advertising; the increasingly sedentary nature of jobs; children playing video games ...

Etching your own circuit boards is tons of fun, but etching requires strong chemicals to dissolve the copper plating on blank circuit boards. The normal ferric chloride solution works well, but can be expensive and leaves permanent stains. Luckily, we can whip up our own etchant at home with everyday chemicals! Better yet, our new etchant will turn an eerie green color rather than the dull brown of ferric chloride.

I have an absolutely wonderful time making projects and writing articles for all of you mad scientists! Today, I will bring you behind the scenes for a look at the workbench, tools, and software that make the Mad Science World possible.

The agents of empire do not always arrive with warning. When you are besieged, surrounded, and infiltrated, imagination is often your best weapon against the oppressors. If all you have at hand is some duct tape and a disposable camera, fear not, you have the makings of a powerful taser!

If you're a frequenter of Null Byte, I bet you have at least some interest in information security. Furthermore, you have a hobby that if applied in certain ways, will get you arrested. I've received quite a few messages from the community here about federal cybercrime law and how it applies to them, so I decided to get together with my lawyer to come up with some answers.

Social engineering is described as the clever manipulation of the natural tendency of human trust. All of the passwords, locks, and encryption in the entire world are useless against a good social engineer who can charm or trick you into giving it up.

This is a two-part series to locking down the computer to provide maximum protection. Even though this guide will sound intrusive, we are talking about reality here. Extreme measures must be taken to protect our computers, especially when we have confidential documentation or do internet banking, which many people do. We all have to use electronic devices at some stage, whether it be for business or personal use.

The Stun-Gun In this article, I'll show you how to make a small, weaponized highlighter. Before I get into how to built this device, let me warn you. This device is harmful! When used, it can cause burns and/or serious muscle spasms. The voltage is potentially deadly! DO NOT attempt to build this device unless you are experienced with safety, electronics, soldering, and understand circuit schematics.

Some people are what is labeled a power user. I am one of these people. No matter how fast I get my system, or how quick of programs I have, it is never good enough. There is always at least one program that I could swap out for a more advanced, text-based counterpart that increases performance just a bit. Luckily, you don't have to use text-based programs without graphical user interfaces to get blazing fast speeds on Linux. There are tons of open source alternatives to the mainstream progra...

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.

Pumpkins, murderers, vampires, zombies, ghosts, witches, death… these are all the subjects of last week's Scrabble Bingo of the Days, which focused on words associated with Halloween and horror movies. Did you know there was actually a name for someone who suffocated another person? Did you know that Frankenstein, vampires, and ghosts can all be considered one thing? Did you know that there was actually a word for rotten dead flesh?

No matter what word game you're playing, whether it's Scrabble or one of its near-homogeneous counterparts like Lexulous, Wordfeud or Words with Friends, one of the easiest ways to stay on top of your opponent is knowing all of the legal two-letter words you can play. You're not going to win by only playing two-letter words, but there are definitely occasions when the game could slip from your hands by not playing them.

In 1988, John Langley created COPS for the fledgling FOX network. 23 years later, the show is still running. It is the Energizer bunny of prime time television. Since John has followed more police officers and witnessed more crime than any human being on earth (absolutely no question), I had to ask some advice for hypothetical unwanted encounters with the men in blue.

Mark Burnett is, financially speaking, perhaps the most successful television producer today. While I had launched America's Most Wanted and COPS a decade earlier, Mark exploded onto network television with Survivor, the glossy and fantastical innovation to reality television. With Survivor now entering its 11th year, I recently interviewed Mark at the Los Angeles public radio station KCRW, where the podcast will be made available. Below, Mark's 10 steps from soldier-to-nanny-to-premiere-Holl...

Dear Jackass Guys well i am John Fears and i am 27 years old and i already met some of you guys but it would be nice to meet the whole cast on the epic event. That is why i am trying out for this contest. you are rock and i have been a fan from the start of your quest for being a the best jackass. i am a film student and i want to be in show business myself and be like John Knoxville but it s hard to get in to the film industry. i have been trying since i was 14 and still nothing. you can che...

OnePlus will be releasing a new phone in the second half of 2018, specifically, an upgrade to their T-series. Over the past two years, #T versions have come out about five months after their predecessors and have included small updates that fix any problems from the previous OnePlus device. While we do know a bit about OnePlus 6T, what it could be is much more exciting.

As smartphones become more accessible, billions of people have come to depend on their features for daily life. One of the most important aspects these days is the camera. OEMs have been working for years to improve camera quality, and they seem to have finally figured it out — the best way to achieve DSLR-quality photos wasn't just with better sensors, but with better intelligence.

After previously learning how to make the material of an object change with the focus of an object, we will build on that knowledge by adding new objects through code. We will accomplish this by creating our bounding box, which in the end is not actually a box, as you will see.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

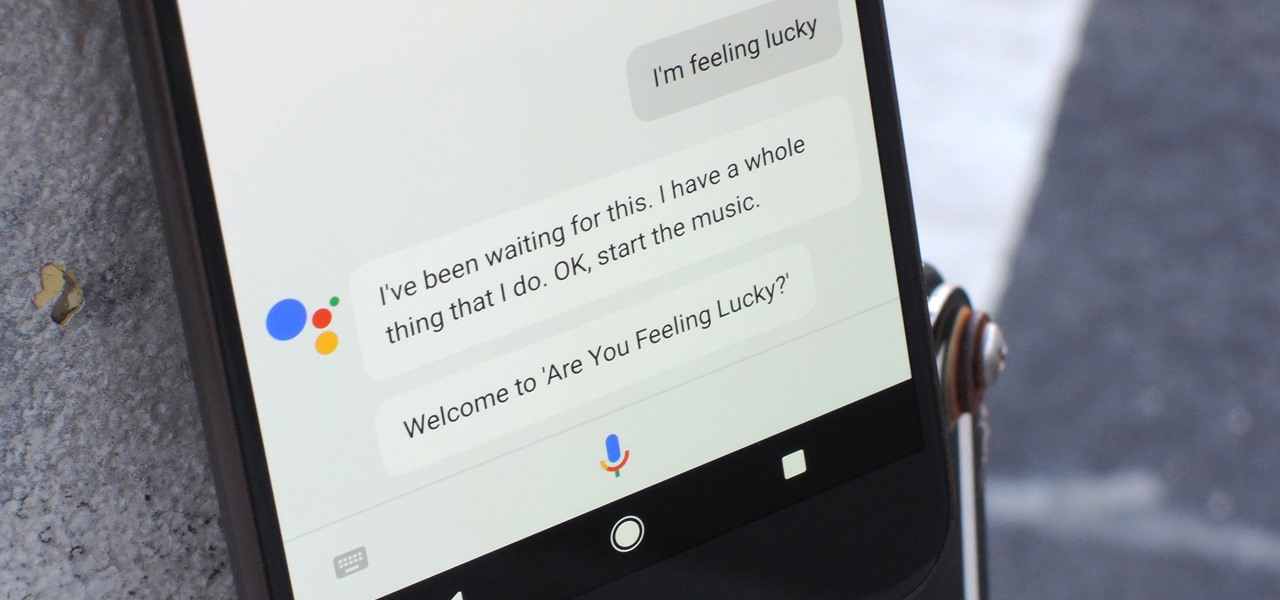
Despite a rocky start with plenty of feature disparity, the Google Assistant now provides a pretty consistent experience regardless of what device you're using it on. Be it Android, iPhone, or Google Home, the AI behind the Assistant is virtually identical — including its quirky commands and funny responses.

I don't know about you, but I'm tired of hearing some of the same old jargon from people online who claim that all you need to make it on Instagram is to take good pictures and post consistently. Yes, for sure, but do you really think it's that easy?

Beginners luck is a phrase I have always hated. But really, beginners luck comes down to not letting your experience in something get in the way of the idea.

Greetings my fellow hackers, In the previous article, I discussed briefly about ransomwares and their devastating capabilities. Devastating in a way that ransomwares are not only known to encrypt files but to also lockout some specific functions of the system and hold it up for a ransom.

Even the most seasoned cook is always looking for ways to make cooking easier and cleaning up after meal prep a breeze. There are a million and one tricks and tips out there to simplify your kitchen routines, but some of them are more valuable than others.

Greetings to all geeks, hackers, nerds, and explorers of Null Byte. Welcome to my brand new tutorial, "Using BASH for Computer Forensics". This tutorial will give you a look at how the computer programming language, Bash, can be used to find out details on apple devices for later use.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords