
How To: Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
Welcome back to control structures, part two featuring the three types of loops. Here we go! What Is a Loop?


Welcome back to control structures, part two featuring the three types of loops. Here we go! What Is a Loop?

WPA Enterprise is widely used in large corporations as it offers individual and centralized control through a server that authenticate the users (RADIUS server). In this tutorial I will show you how to break the barrier and obtain the user credentials.

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.
As Android's de facto virtual assistant, Google Now lets us speak directly to our phones in plain English to answer our questions and perform many basic tasks. With the app open, just say "Okay Google," then wait for the beep, and ask almost any question.
Hello and welcome to my article. I have made this article for anyone who wants to become a hacker, and wants to know how to get started.

If you've read any health news in the past year or so, you've probably been bombarded with headlines announcing that frequent sitters face certain death, even when you're just relaxing and watching TV at home.

Welcome back, my novice hackers! In a recent tutorial, I showed you how to use shikata_ga_nai to change the signature of a payload to evade detection by security devices (firewalls, IDS, etc.) and AV software.

Android enthusiasts have their own opinion as to whether you need antivirus software on an Android device. This debate will never end, provided that Android malware is in existence. This guide is not here to say, "Yes, you need antivirus," or "No, you don't." It's to give you all the facts, so that you can make a decision as to whether or not you need antivirus on your Nexus.
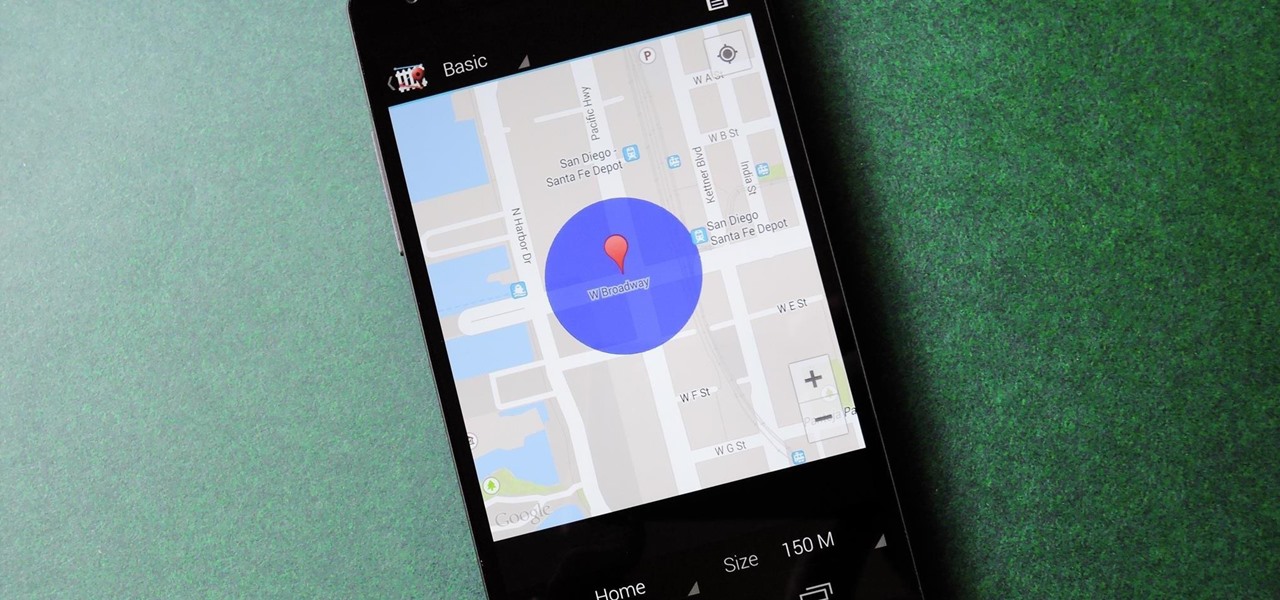
We live, work, and play in drastically different environments, so it only makes sense that we'd want our Nexus 5 smartphones to automatically adapt to our needs when in certain locales at certain times.

It may seem impossible to win an argument against an irrational person, but it turns out the tried-and-true techniques that hostage negotiators use against hostage-takers work surprisingly well in everyday situations. You may not ever deal with a real hostage situation personally, but life is full of negotiations with unreasonable people, and those conversations don't always have to end in rage or disappointment. The mental techniques that professional hostage negotiators use can help both pa...
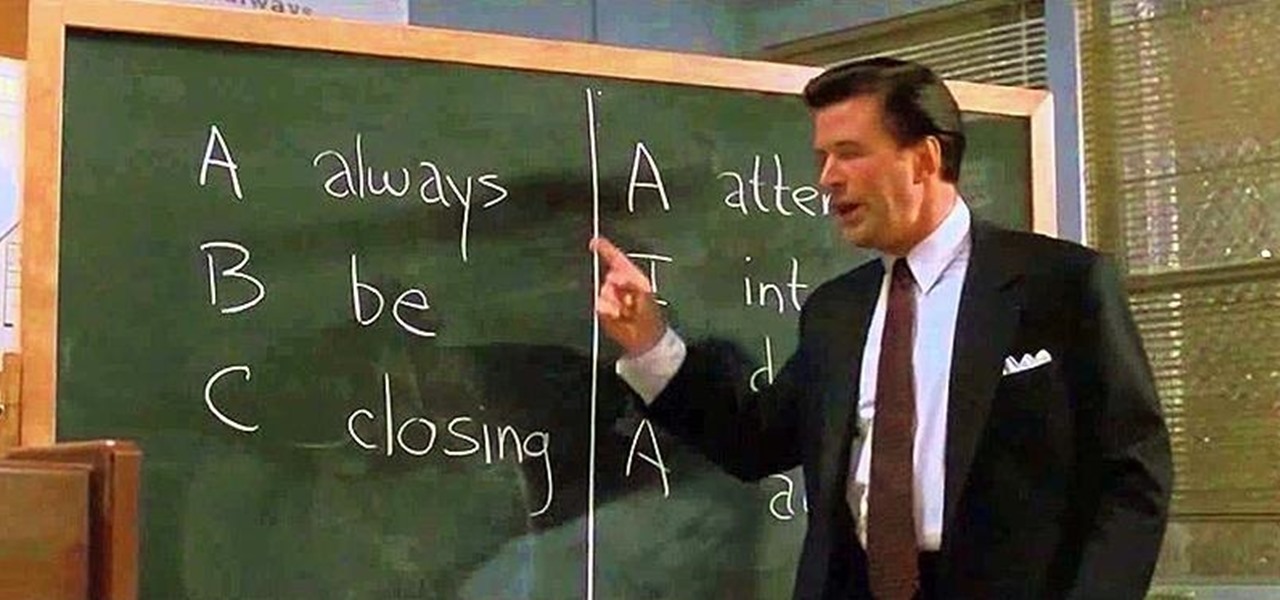
Have you ever fallen victim to a clever Jedi mind trick? Don't worry. It happens. There are evolutionary reasons as to why our brains sometimes give into the oldest tricks in the book. Fortunately, the more you understand the tricks of a salesman, the easier it is to avoid their gripping psychological influence. Clue #1: Too Much Specificity

As the Chromecast becomes more and more popular (it's even available overseas now), the market has seen an avalanche of Chromecast-compatible apps. We can play games, cast TV stations, and even mirror our screens, but today I'm going to show you a multifaceted tool that'll do everything from broadcasting your camera to displaying your documents.
What is Programming? Why need to learn? How to get started? Which language to choose? While surfing web, you must be encountering various softwares, games, etc. and might be thinking to make one, but don't know where to start. Here, I am starting series in Programming.

KitKats? Toast? Sorry if that headline made you hungry, but no I'm not talking about Nestlé's chocolatey wafer treat, nor the crunchy slices of bread you have with your eggs in the morning.

While Siri has never been my favorite, after using her in the new iOS 7, I have definitely become a fan. If you want to know why, check out the newest cool features that Siri has to offer!

Below are the official rules and guidelines for submitting content to WonderHowTo. Please look over them before publishing any articles. Ignoring the rules could result in deletion of your article or being flagged as a spammer. Most of these rules apply to comments as well.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.
Welcome back, my fledgling hackers! If you're like most aspiring hackers, at one time or another you've probably spent too much time playing Call of Duty and not enough time preparing for your final exams.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Welcome back, my novice hackers! Most of my tutorials up until this point have addressed how to exploit a target assuming that we already know some basic information about their system. These include their IP address, operating system, open ports, services running, and so on.

Not having internet sucks! We do a ton online these days, from working, shopping, studying, and collaborating, to watching fail videos and endlessly clicking through memes.
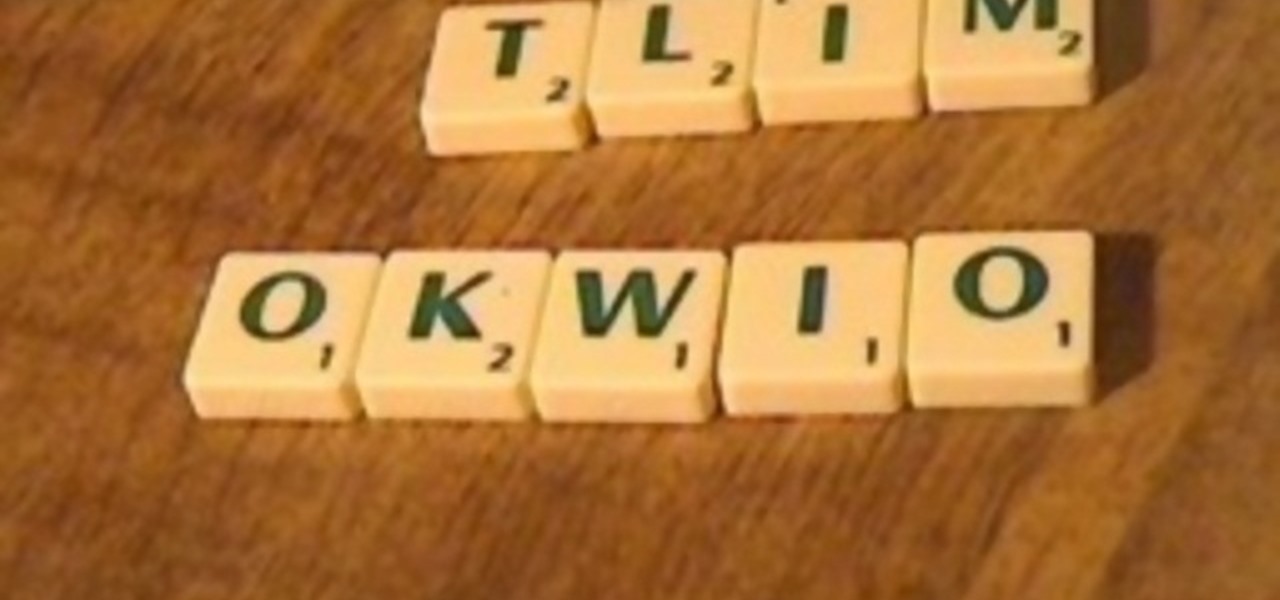
This will show you how to arrange the word "CIVIC" using only the letters T, L, I, M, O, K, W, I, and O. What? No C's? Well, that's what makes it a riddle, right? Why do the letters not look like Scrabble tiles? Well, sometimes there's just too many questions, and sooner or later you're just going to have to stop asking them.

Jnana yoga refers to wisdom and discernment in meditation. Learn how to practice Jnana yoga in this video lesson. To practice Jnana yoga you should center on a question, reject all knowledge, and meditate on intuitive knowledge. With the steps from this how to video you will be able to practice Jnana yoga.

Pharmacist Sue Brenan answers common health questions.Watch this video to learn how to tell if you're dehydrated.

Quick and Impressive coin trick with how to explanation. Can you do it? Any Questions? Leave a comment.

This should probably be called the three phase of water. It all started as a students question, "Can you show us the triple point for water? Can you boil ice water?"

Tim Carter explains how they work and how a central vac is installed. Tim asks the question why lug around a heavy vacuum when central vacuum systems can do the work for you? Lenghty project, but esy-to-do with Tim's instructions.

Want to impress your doctor? Check out this video and learn a few fancy names for common problems and soon your doc will be in awe of your smarts.

Wondering what cat is best for you? If you’ve decided to adopt a cat, learn what different breeds can offer so that you can give your new feline a forever home.

Tired of losing your shirt playing poker? How about a fun game for couples instead? You Will Need

Got school spirit? The cheerleading squad's the perfect place for you. Here's how to make the team. Step 1

It was bound to happen with all those numbers floating around in your brain – you've forgotten your Windows password. Here's how to recover it.

Help yourself win that must-have item with these tips. You Will Need: a computer with internet access, money, & patience. Create an account. Browse the categories to familiarize yourself with the site, especially if you don’t have a specific item in mind. If you know what you want, start searching by using broad terms and synonyms to yield the most results. Add quotes around your search terms or qualifiers, such as a specific color or size, to narrow the field. You can also post on the “Want ...

It's already easy, but we'll help you make it even easier. Watch this video for tips on getting guys to buy you drinks in a bar. If the guys are going to hit on you, might as well get some free drinks out of it.

Learn how to play "Mad" by Ne-Yo, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:

Learn how to prepare for a job interview with expert tips and advice on job interview questions, dress, and skills in this free video series.
When you look at the top corner of your phone, what do you see? Upon upgrading to Android 11 or iOS 14, you'll see either "5G," "5G+," or "5G E" if you're connected to the right network. But what exactly do these symbols mean? They indicate not only if you're using 5G, but also what type you're connected to.

How much screen time is too much for a child? Should you let your children have a smartphone or tablet? What age is appropriate to introduce them to technology?