One of the primary marketing tactics used by Magic Leap in promoting the Magic Leap One was selling early adopters on the "magic" contained within the device. On Thursday, some of that magic was uncovered as the Magic Leap One was completely disassembled by repair engineers, revealing the delicate innards of the device and detailing how it delivers its augmented reality experiences.

Look, we all like getting things for free. That's why we can stomach things like advertisements and optional purchases in freemium apps and games — we're willing to pay for our mobile experiences in every way but currency. Although freemium seems to be the model for the future of iPhone entertainment, it looks like a different scheme might win out in the end.

Locating and abusing files containing unsafe permissions is an easy and surefire way to elevate shell privileges on a backdoored macOS device. This time around, we'll be more aggressive and attempt to phish a user's login password by prompting a convincing popup message merely asking the target for their password.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.
Sometimes we need to share screenshots, but don't want to reveal the entire screen. This usually requires some editing that isn't typically easy to do on a smartphone. BlackBerry recognized this issue and created a tool called Redactor that makes it easy to hide your data before sharing.

The current iPhone lineup inarguably features Apple's best displays to date, but the stock wallpapers don't really do the screens justice. There are plenty of third-party wallpapers you can use, as well as ones you create yourself. However, if you want that typical Apple feeling, you're better off sticking with Apple wallpapers, and the iPad Pro has some beautiful ones that look awesome on an iPhone.

Thanks to cloud storage's increasing accessibility, permanently losing photos is becoming less and less common. Still, if you accidentally delete a picture from your smartphone without first making a backup of some sort, that data is pretty much toast — unless we're talking about photos from WhatsApp.

I've called 911 accidentally more than a few times on my iPhone using the Emergency SOS triggers, but it's also just as easy to trigger an unintentional call to emergency services using an Apple Watch. These accidental 911 calls can put a strain on local public-safety answering points, or call centers, as well as local authorities and emergency medical technicians.

Ever since 2009, you could send a photo or video that you've already taken right from the Messages app on your iPhone. You would just tap on the camera icon next to the new message box, then choose either to take a new one or select one from your library. If you're running iOS 12, that's no longer the case, but that doesn't mean the capability is gone entirely.

The misconception that macOS is more secure than the Windows operating system is far from the truth. With just one small command, a hacker can completely take over a MacBook and control it remotely.

Android has gotten significantly better at handling intrusive ads over the years. Things have gotten to the point to where these nuisances are largely a non-issue for most of us. However, there are still a few ad-laden apps that fall through the cracks — particularly the kind that bombard your lock screen with ads.

It is often said that the best hackers remain unknown, and the greatest attacks are left undiscovered, but it's hard for an up-and-coming penetration tester or white hat to learn anything unless one of those factors is actually known or discovered. But the end goal here in our SQL injection lessons is to make that statement as true as possible for us when performing our hacks.

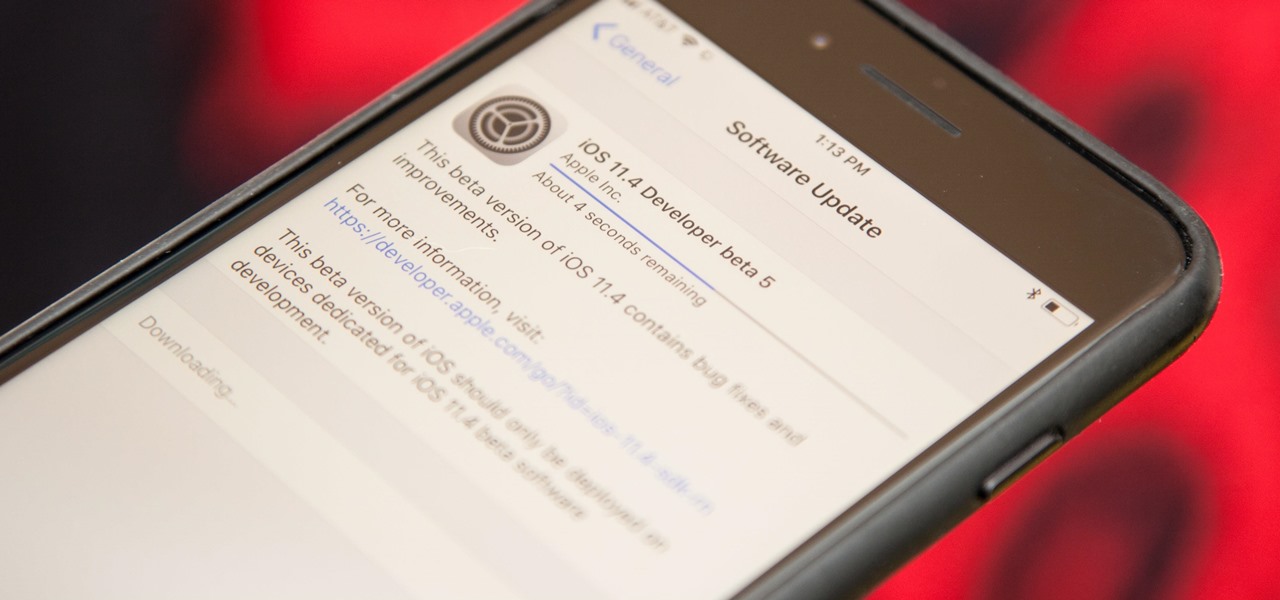
Talk about rapid-fire. Apple released the sixth beta for iOS 11.4 on Thursday, May 17. The update comes just three days after the release of iOS 11.4 beta 5, indicating that Apple is readily approaching the official release of the software. Apple has not issued an official iOS update since 11.3.1, which found its way to users over three weeks ago.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Apple is speeding things up in the iOS 11.4 development. The company released to developers the fifth beta for iOS 11.4 on Monday, May 15. Public beta testers got the update just hours later. The update comes just one week after the release of the fourth 11.4 beta, which introduced minor bug fixes and security patches to iPhone running the software. This beta version doesn't seem any different.

Despite numerous reports announcing its stateside arrival, "Final Fantasy Awakening" has yet to show up in the iOS App Store, much to the chagrin of millions of fans in the U.S. Unfortunately, the game seems to be stuck in soft-launch limbo, with no word as to when it'll land stateside. With a little hack, however, you can give this immersive game a try right now.

Know thy enemy — wise words that can be applied to many different situations, including database hacking. It is essential to performing adequate reconnaissance on a system before even thinking about launching an attack — any type of attack — and this is no different for SQL injection.

Apple released the fourth developer beta for iOS 11.4 on Monday, May 7, followed the next day with the public beta release. This update arrives just six days after the company seeded beta 3 to users, which fixed an 11.3 issue with 3D Touch, among other various bugs.

Augmented reality is expected to eventually change everything, and the prevailing view is that those changes will be for the better. The converse view, however, is that the technology will further erode privacy.

One of the better additions in the stock Android launcher is the Google Now page. Residing to the left of the home screen, this page presents a host of information based on the user's interests, which Google bases on analyzed data. Recently, the Google Now page design received a makeover which Nova Launcher users can now enjoy.

Apple released the third beta for iOS 11.4 on Tuesday, May 1. This update comes exactly two weeks after the release of the second beta, which, in addition to adding a new wallpaper, fixed issues with AirPlay, Music, and Keychain. The only noticeable change in beta 3 is a fix for unresponsive 3D Touch.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.

No matter your reasons, you might need a second phone number that's a little more disposable than your primary number — a "burner" number, so to speak. If you create this burner number using Google Voice, you'll get new functionality like call forwarding and voicemail transcripts, and best of all, it's completely free.

While the public now knows much more about the Magic Leap One: Creator Edition today than it did yesterday, there's still a quite a bit that's unknown. One of the most significant questions — with any mixed reality product — is the field of view. How much of what we see through these glasses will contain the computer's virtual creations?

Considered by many (perhaps unfairly) to be a very public failure, Google Glass can add another plot point to its comeback story, this time as a tool to teach social skills to children and adults with autism.

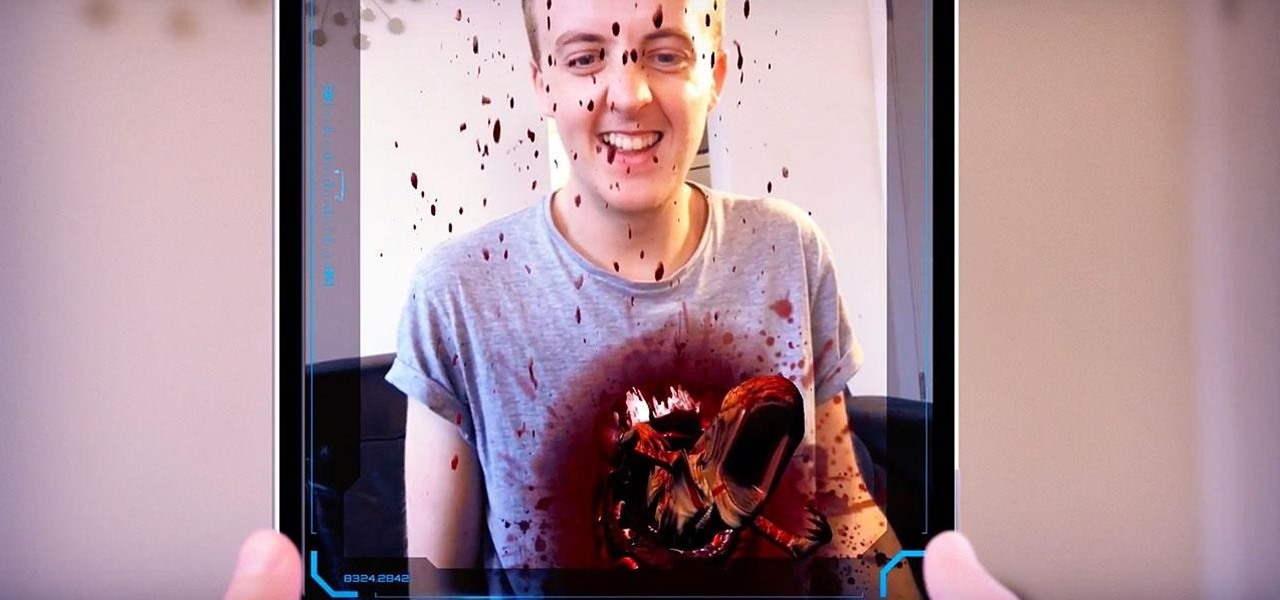
The latest installment in the Alien movie franchise, Alien: Covenant, came out many months ago, and the fan day dedicated to the franchise, Alien Day, April 26, is long past. But for many Alien fans, Alien Day is every day. For those loyal members of the xenomorph-worshipping tribe, a new augmented reality-powered book has arrived to serve their science fiction needs until the next film is released.

The iPhone 8 is just about here. If you're anything like me, you can hardly contain your excitement. Apple has been keeping its 10th-anniversary device — whether you call it the iPhone X, iPhone Edition, or iPhone 8 — as secret as possible, but this past year we've seen a waterfall of leaks. Now that all of the rumors are out of the way, we're finally going to see what's actually in store for Apple's newest iPhone.

It has been an interesting few days in developer news. The Microsoft blog has been busy with information relative to the augmented reality space. Meta 2 has also announced an interesting development this week. Here is a collection of various tidbits that have been collecting up.

The bacteria in our gut — a community called the gut microbiome — have been in the spotlight a lot lately. What we're learning about how our intestinal bacteria adapt and grow with our bodies could help athletes perform better, according to researchers starting a company focused on creating probiotics that mimic athletes' microbiomes.

Unless you're a WhatsApp pro user, you may be surprised to know that there are text formatting options that you can apply to your messages. Markdown characters can help you emphasize certain words or phrases by making them italicized or bold, and it'll even let you cross out words and change the font. It's one of those nice touches that isn't available in most other messaging apps.

OpenVAS is a powerful vulnerability assessment tool. Forked from Nessus after Nessus became a proprietary product, OpenVAS stepped in to fill the niche. OpenVAS really shines for information gathering in large networks where manual scanning to establish a foothold can be time-consuming. OpenVAS is also helpful for administrators who need to identify potential security issues on a network.

Snapseed is an app that you should definitely be using not only if you're really serious about photography, but also if you want to ensure that your online work sets the standard for social media. It's a great companion app to Instagram and VSCO, and it will save your day many times over when you find yourself on your phone, on-the-go, needing to edit an image beyond the typical everyday filters.

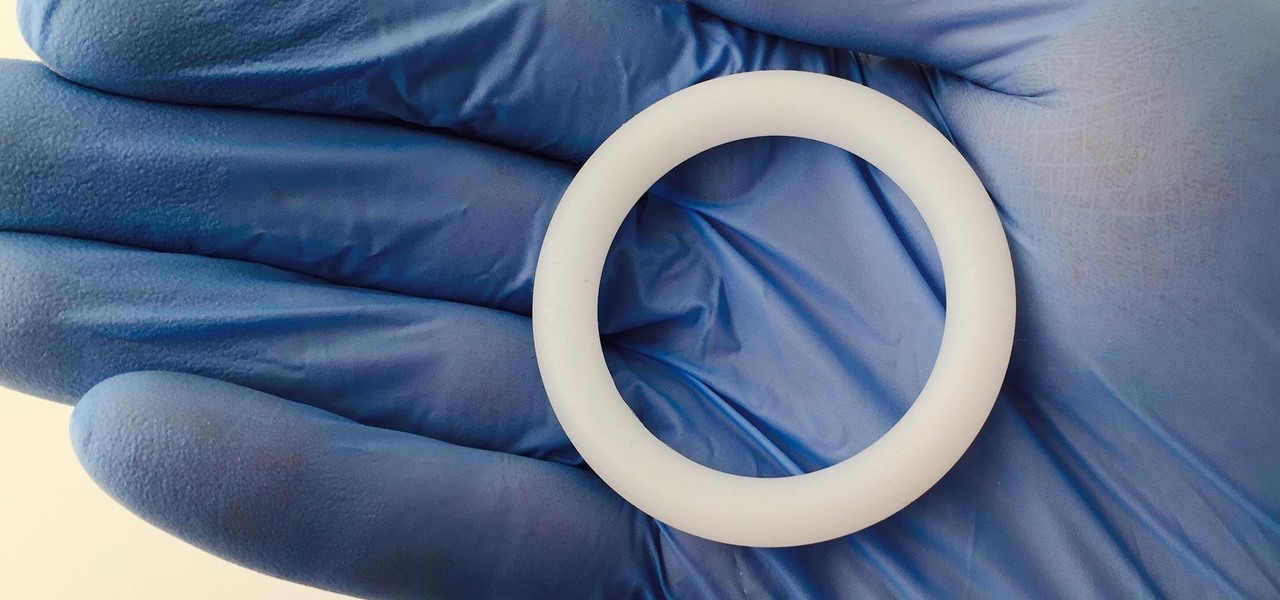
Young girls, especially those who live in areas where HIV is epidemic, like sub-Saharan Africa, are particularly vulnerable to becoming infected with HIV. A vaginal ring containing the antiviral agent dapivirine has been shown to decrease the chance of developing HIV-1 in adult women over 21 and now in the first step for use in adolescents, the ring has been shown to be safe and well-tolerated in that younger age group.

Verto Studio 3D is a 3D modeling package that has been in the works for a while now by Michael Farrell, the owner of Verto Studio LLC. Farrell has been working toward bridging the gap between XR 3D modeling and what we have become accustomed to with desktop 3D modeling packages like 3D Studio Max, Maya, and Blender.

The next time you suffer a cut or abrasion, think twice before you reach for the Neosporin. It's time, and mom, tested — you get a cut, you wash it carefully, then apply some triple-threat antimicrobial ointment. You may or may not slap on a band-aid. We won't cover it here, but so that you know, covering the wound with a sterile dressing or band-aid is a good idea.

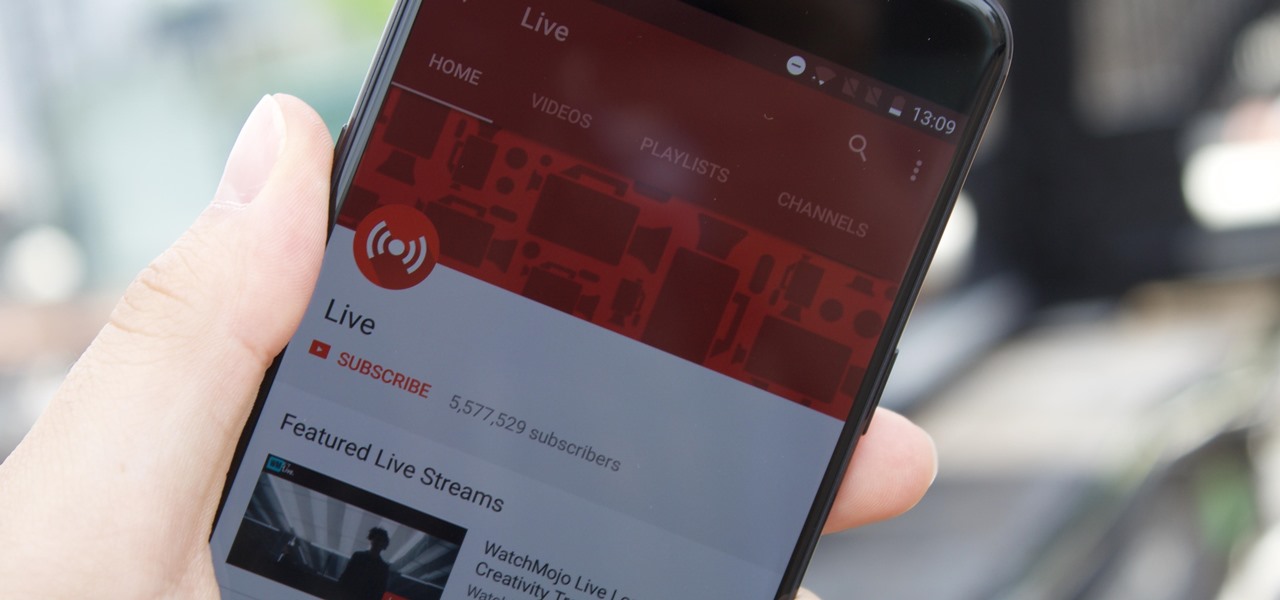
YouTube's mobile live streaming feature is great for connecting with your audience in a more personal way than traditional videos provide. Audiences can view and respond to content in real time, and creators can do the same. While unfortunately not available to everyone — you need at least 100 subscribers — live streaming is possible, even with your smartphone.

In late June, the biggest measles outbreak to strike Minnesota since 1990 seemed to be winding down. Today, public health officials announced a new confirmed measles case in the area.