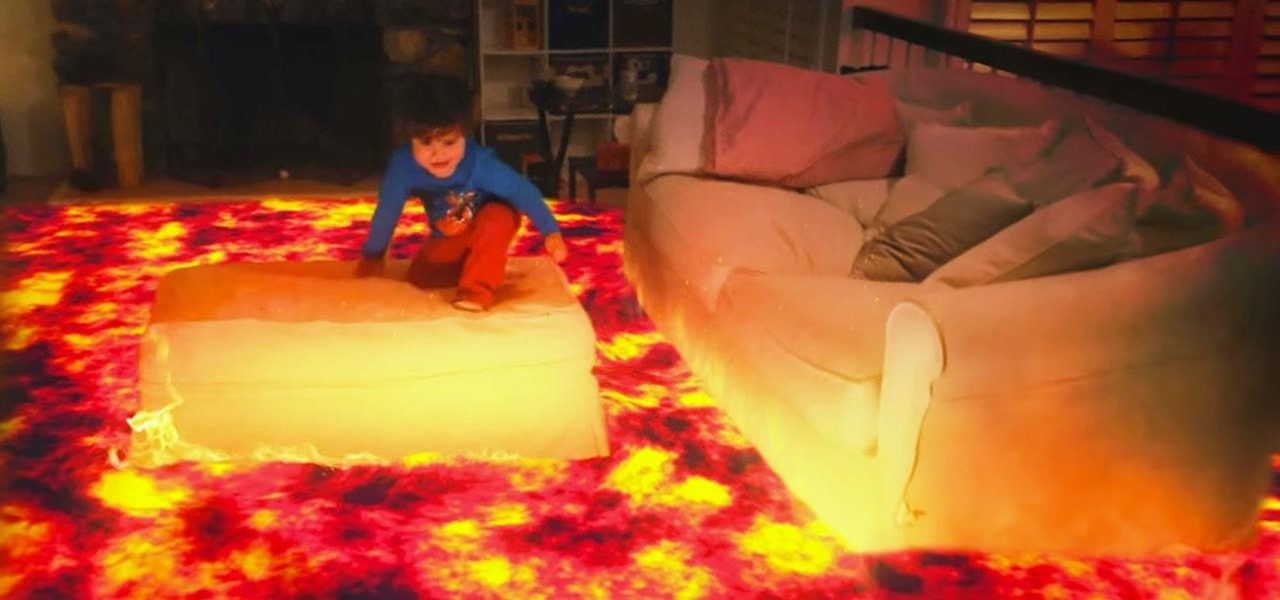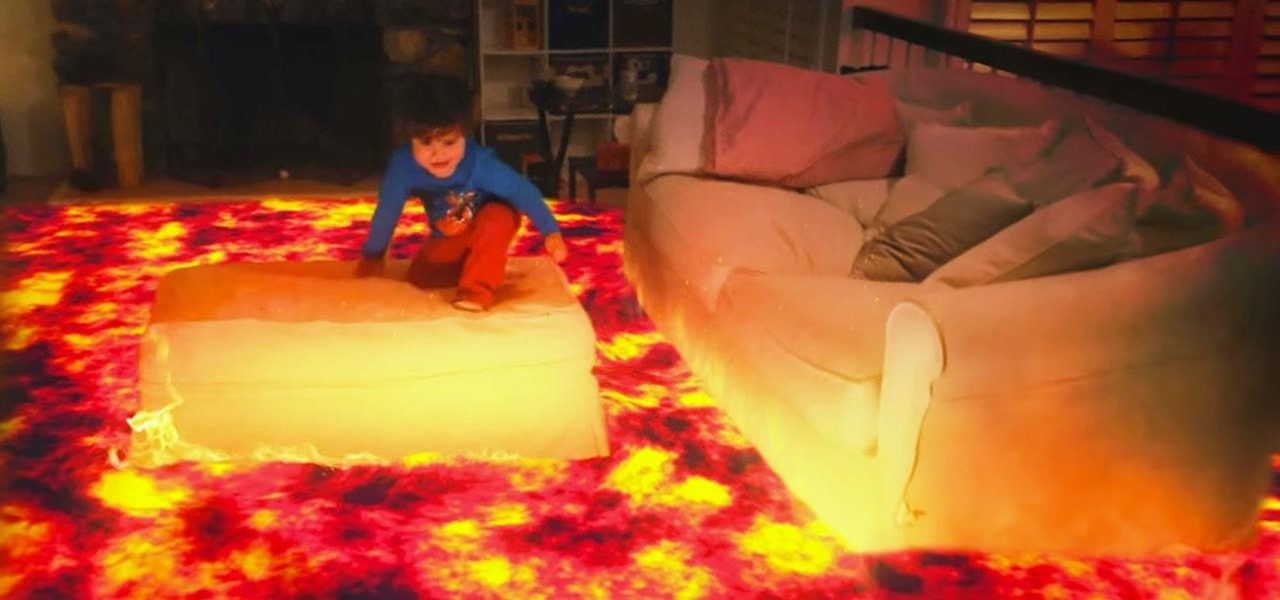
Unless you had a master of visual effects for a parent, you had to imagine the floor was actually lava when playing the classic furniture-hopping game. With a Microsoft HoloLens, however, you don't have to imagine anything.

Returning your device to stock, whether it is because you need to sell it or just want to receive OTAs again, is not always a simple process. Since HTC has released countless variations of both the M7 and M8 HTC One, it can be a pain in the ass finding the right files and tools to get your phone back to stock settings.

Even if you're lucky enough to not be injured in a car accident, it's rare to escape without some sort of damage to your vehicle. It goes without saying that there are some things you shouldn't try to fix yourself, but if it's just a scratch or dent, DIY can be a cheaper way to go.

Puff and Po and the Empress's Treasures, is an inspiring indie game that stays fateful to the arcade single screen plat-former style and game-play.
The movie Her is getting a lot of love from viewers and critics alike. While I find it kind of creepy to fall in love with a computer program, if Scarlett Johansson talked to me every day, I'd probably fall in love too.

Welcome back, my budding hackers! One of the most time-consuming, but necessary, activities in hacking is reconnaissance. Before we can hack a system, we need to know what operating system it's running, what ports are open, what services are running, and hopefully, what applications are installed and running.

As most everyone knows, Android and Apple don't get along so well. Even the users don't get along well, with Android and iPhone users constantly berating and insulting each other online—any chance they get. I should know, since I was one of them, but I'm now rare breed who's learned to appreciate both. People just need to realize that they have their own unique strengths—Android with its customization and Apple with its simplicity.

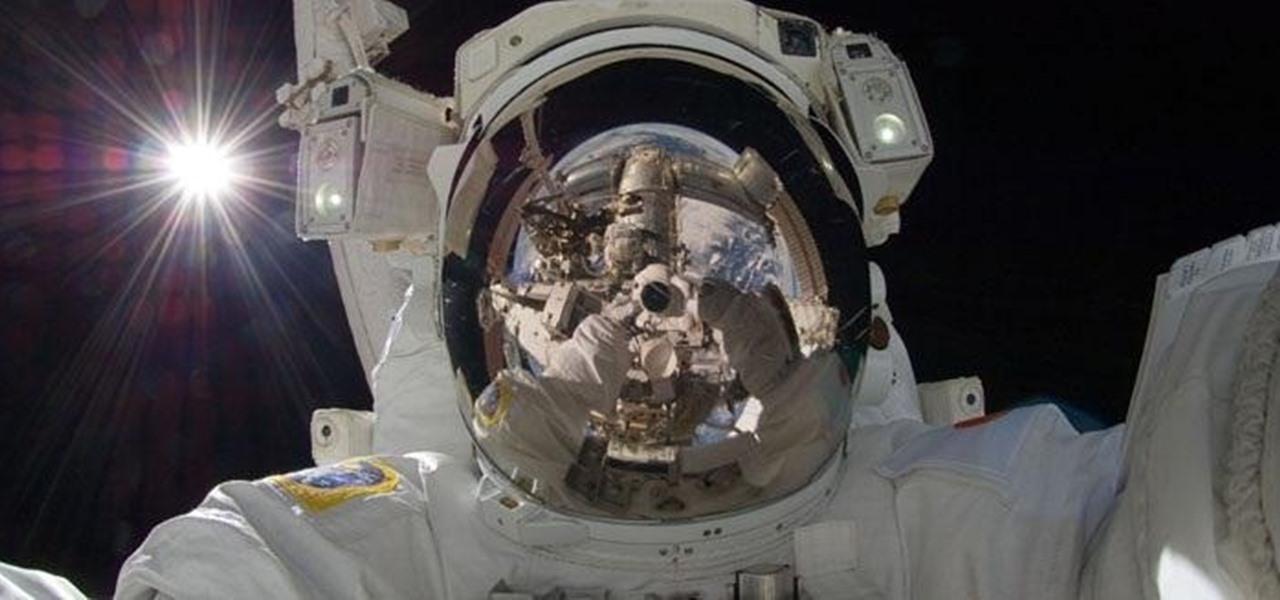
There's nothing more inherently awesome than looking up into the stars and wondering WTF is really out there. Outer space is one of those rare items that a Google search cannot provide all of the answers for.

Need to break out of the restrictions your school or workplace have on internet browsing? Maybe you want to waste some time on YouTube, check out some gaming action on Twitch, or simply just browse Facebook or Twitter.

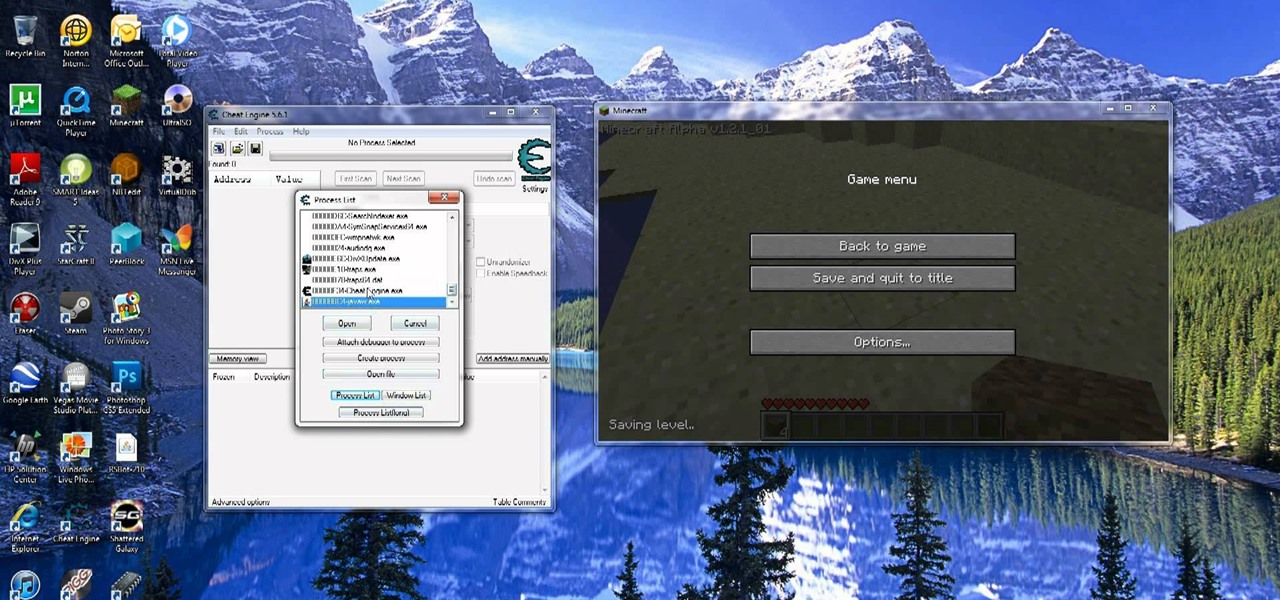
If you have already downloaded the latest version of Cheat Engine, you can use it when you play MineCraft to hack and edit your inventory. Give yourself rare items, or unlimited items, using the simple steps outlined in this tutorial.

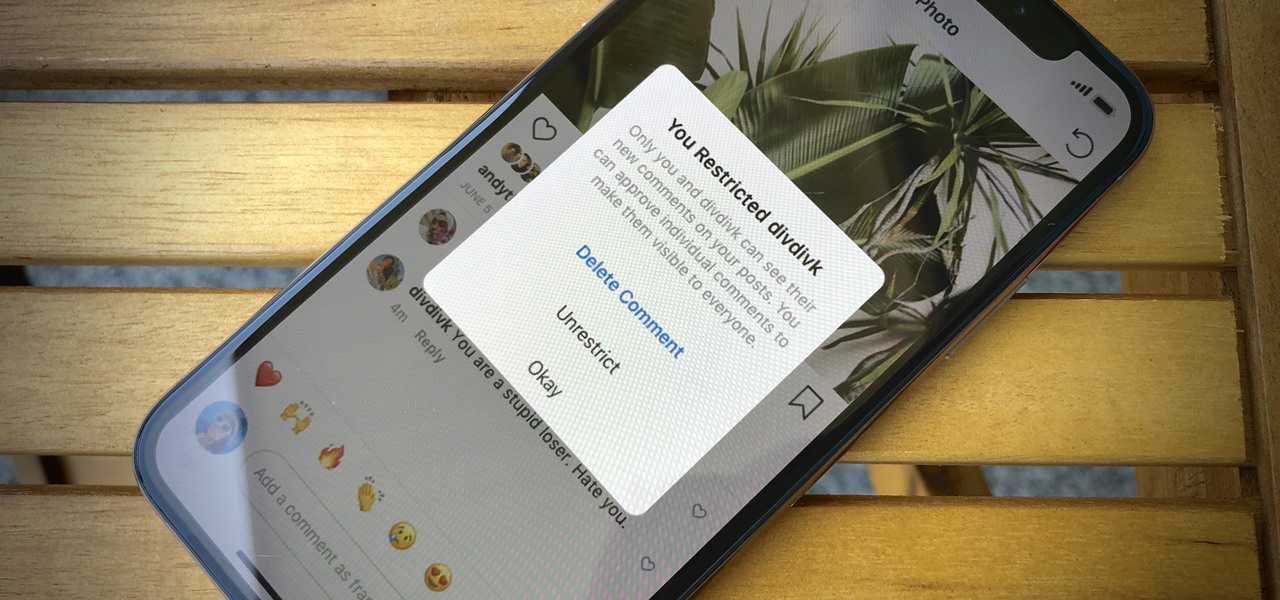
In general, the internet can be a cruel place, and Instagram is no exception. Most of the time, the platform is a fantastic way to share and view unique and creative content, to reach an audience of both fans and friends. People can step out of line and harass or bully others on posts to the detriment of the entire community. However, this type of commenting won't be sustainable for much longer.

If we're being honest, very few people go on Tinder to fall in love with someone's personality. Oftentimes, the only reason they'll look at your bio is to make sure there are no red flags.

Universal Studios and Cinemark Theaters have enlisted mobile augmented reality game Seek to promote The Mummy, a reboot of the action-adventure film franchise starring summer movie mainstay Tom Cruise.

Disney Chairman and CEO Bob Iger has out and out rejected Virtual Reality (VR) as a component of any Disney Theme park. While Knott's Berry Farm, why-hasn't-this-chain-shut-down-yet Sea World (seriously, RIP Tillikum), and Six Flags have all invested in VR to help spice up their parks in this theme park depression period, Iger has "ordered his team not to even think about it." Iger instead is very much onboard the Augmented Reality (AR) train.

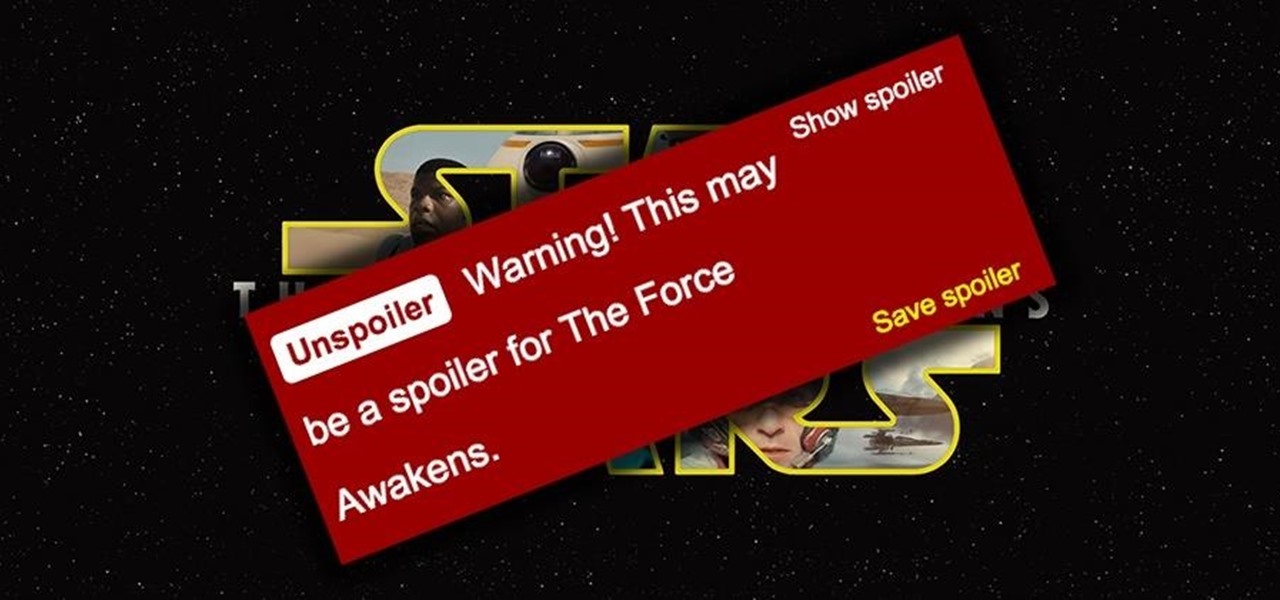
Unlike in the physical world, on the internet you're actually able to shut people up and block spoilers of newly-released movies, your favorite TV shows, or a sports event you've yet to watch on your DVR.

Many reminder apps offer various bells and whistles that make them overly complicated to use when all you want to do is one or two things. If the only things you care about doing are setting quick reminders and adding timers, you probably don't care about cloud syncing or calendar integration features.

I may not be a well-traveled man, but one thing I've learned from my few excursions across the world is that currency exchange rates are a serious pain to keep up with. With global markets seemingly in a continuous flux, I started looking for anything to make staying on top of them easier, and thats when I found Price Helper.

Some people hate cold weather, but there are also plenty of things to look forward to in the wintertime. The holidays, building awesome snow sculptures (or igloos), and hot chocolate, to name a few. But with all the good also comes one gigantic downside—more people get sick during the winter than any other time of year.

I use Google Chrome every day for my browsing needs, and I had no idea they were hiding something from me. So, I was pretty surprised to see that Chrome has an entire hidden experimental add-ons section. There are add-ons that work for Mac, Windows, Linux, and Chrome OS, so there's something for everybody.

Drinking games just got a little more sophisticated (kind of). Startup SmartThings built this awesome Arduino-based machine that automatically pours a shot whenever the US wins a medal in the 2012 Summer Olympics. Goldschläger for gold, Cuervo for silver, and Jack Daniels for bronze.

Yes! soon I will be able to log in more as I untie the shackles this map has placed on me in the time leading up to its eventual release and log in once in a while!

Chef Gordon Ramsay will show you how to make a really terrific steak with out all the guess work. He will help you take your steak cooking skills from amateur to professional grade steak, or at least help improve your result with some professional tips.

Champagne is great, rare champagne is even better in The Saboteur for the Xbox 360. Prove yourself and find the bottle in the second mission in Act 1: Bottle Shock. Luc needs antibiotics for his wounds. Luckily, Santos can provide them if you do him a favor. You'll need to steal back a bottle of champagne for him. Leave the new HQ and hop in a car. Now follow the GPS to the location of the champagne bottle. A pair of Gestapo agents will be guarding the front gate of the courtyard the bottle s...

When joining a new network, computers use the Address Resolution Protocol to discover the MAC address of other devices on the same network. A hacker can take advantage of ARP messages to silently discover the MAC and IP address of network devices or actively scan the network with spoofed ARP requests.

There's nothing worse than biting excitedly into your indulgent restaurant-style burger only to find a soggy mess of a bun on your plate. The conundrum of keeping a patty moist but bun dry has perplexed home cooks and chefs alike, and even top burger joints are guilty of soggy-bun syndrome.

The video shows us how to cook a delicious beef steak. First, preheat the frying pan on a highly seasoned surface with a bit of salt. Then, sear the meat at high temperature. Doing this helps in lock the juices. If you are using a marinated cut of steak, searing will also improve flavor by caramelizing the meat a golden brown. After the searing is done, reduce the temperature from high to medium/low. In this video, cooking will be done at medium, until slightly pink inside, fully cooked and w...

Don't toss that old LP! A few minutes in the oven and you can have a bowl that will be a real conversation piece. Watch this video to learn how to turn a used vinyl record into a bowl.

A little-known setting on your iPhone gives you the power to change the color of certain contact names and email addresses when drafting an email. Customizing the color works well for visually separating contacts at a glance, and it can even help you from sending an email to the wrong person.

Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/WPA2 password, we'll use it to play a Wi-Fi hacking CTF game anyone can practice for less than $10.

While you might suspect your MacOS computer has been infected with malware, it can be difficult to know for sure. One way to spot malicious programs is to look for suspicious behavior — like programs listening in on our keyboard input or launching themselves every time we boot. Thanks to free MacOS tools called ReiKey and KnockKnock, we can detect suspicious programs to discover keyloggers and other persistent malware lurking on our system.

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

Getting an insider view of the goings-on at Magic Leap is hard to come by, but occasionally, the company lets one of its leaders offer a peek at what's happening at the famously secretive augmented reality startup. One of those opportunities came up a few days ago when Magic Leap's chief futurist and science fiction novelist, Neal Stephenson, sat for an extended interview at the MIT Media Lab.

There are over 3 million apps in the Google Play Store, all optimized for the small screen in your hands. While that number sounds staggering, there are still many online tools and websites that require you to use a mobile browser since app development is expensive. However, that's where Progressive Web Apps (PWAs) come into play, a cost-effective way to turn websites into mobile apps.

Networking is built largely on trust. Most devices do not verify that another device is what it identifies itself to be, so long as it functions as expected. In the case of a man-in-the-middle attack, we can abuse this trust by impersonating a wireless access point, allowing us to intercept and modify network data. This can be dangerous for private data, but also be fun for pranking your friends.

More bad news for patients who have undergone heart surgery in the past five years. A new study suggests about one-third of heater-cooler units used in cardiac procedures remain contaminated with a slow-growing, potentially fatal bacteria.

An outbreak of anthrax from contaminated meat in Tanzania sickened dozens of people and moves the danger of this deadly bacteria back into focus.

Every year, 100-200 people in the US contract leptospirosis, but usually 50% of the cases occur in Hawaii where outdoor adventurers are exposed to Leptospira bacteria found in freshwater ponds, waterfalls, streams, and mud. That's why it's so alarming that two people in the Bronx have been diagnosed with the disease and a 30-year-old man has died from it.

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

While password cracking and WPS setup PIN attacks get a lot of attention, social engineering attacks are by far the fastest way of obtaining a Wi-Fi password. One of the most potent Wi-Fi social engineering attacks is Wifiphisher, a tool that blocks the internet until desperate users enter the Wi-Fi password to enable a fake router firmware update.