Who is the hottest animated female character of all time? We're sure there are lots of differing opinions on that, but we think Jessica Rabbit must be at the top of the list of viable options. With curves so, well, curvy, that they enter the room before she does and eye-catching red hair, the seductress is one hot lady.
Enter the Jurassic Period with this drawing tutorial on the dinosaur commonly referred to as the brontosaurus (or just brontosaur). It's actual genus is called apatosaurus, which is a sauropod dinosaur, one of the largest land animals ever! This how-to illustrates the step-by-step details to drawing the mighty brontosaurus. "Brontosaurio" is the Spanish translation of brontosaurus.

Need to protect a section of your overall flash content (say movie or slideshow) from unauthorized access, learn how to do so in this video.

Google loves their little Konami Code Easter eggs. The Konami Code is famous among gamers for letting you cheat in video games. The latest one they come up with lets you try it out on Google Docs. All you have to do is open up Google Docs, and type in with the following keys: up, up, down, down, left, right, left, right, B, A, and then enter!

If you've ever been taking pictures and have suddenly noticed an odd white line in your pictures, it's called "Spray Light" and it happens when light enters into the viewfinder while the picture is developing. This video teaches you why it's important to use the viewfinder cover or curtain to avoid this serious problem!

After 12 years Starcraft 2 is finally here to blow your mind. If you're looking for help with the game, you've come to the right place. We have tons of videos about how to do just about everything in the game. We have strategies for winning campaign and multiplayer games. We have guides to using the immensely powerful level editor. We'll even teach you how to build a Terran Barracks out of Legos. This video will show you how to you can make a mobile wall of supply depots on your Terran base's...

In this video tutorial, viewers learn how to quickly troubleshoot memory problems in Windows. Begin by clicking on the Start menu. Type "mdsched" into the search bar and press Enter. The Windows Memory Diagnostic window will then appear. Click on "Restart now and check for problems". Your machine will then be rebooted and will run its memory diagnostics tool. It will look for any issues that may cause problems for your system. Advanced users can press F1 when it starts to specify certain opti...

Are you in college? Too lazy to make a proper meal? Too cheap or poor to go out to dinner? But, still have that sophisticated pallet, this video will show you exactly how to eat like your in beautiful Mexico and make tasty fish tacos in the microwave, to enjoy any night of week. Don't be afraid to enter the kitchen, after watching this video you'll be eager to have dinner guest.

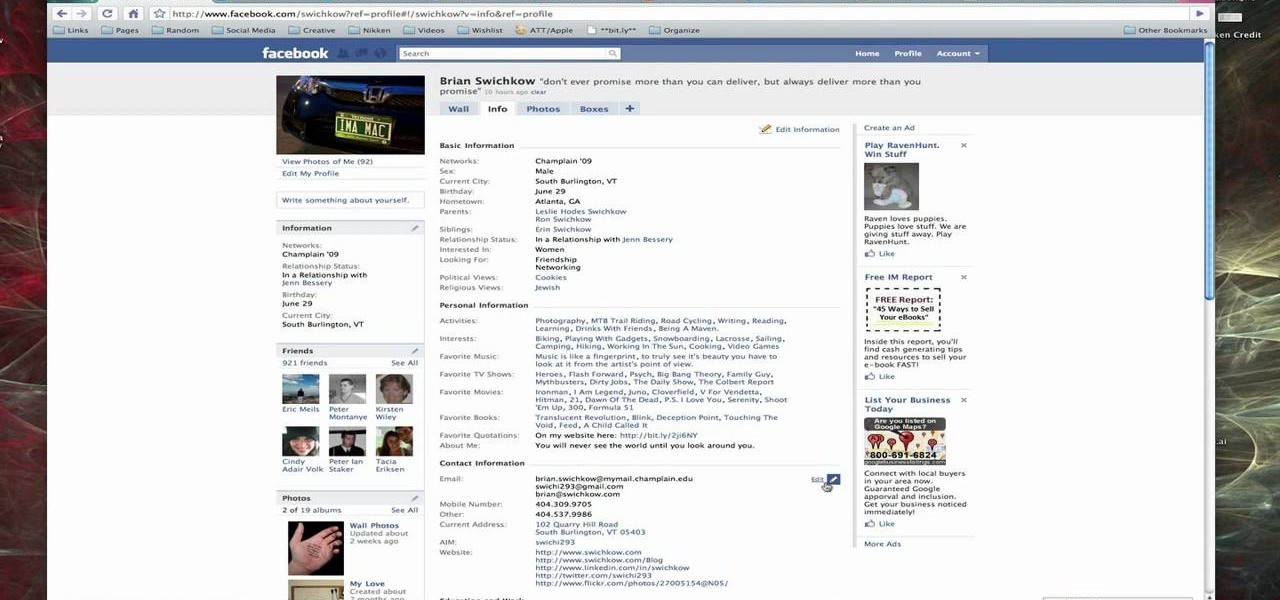
When you register for a new Facebook account you enter your profile details. How ever these profile details can later be changed by editing them. To do this go to your Facebook home page. Open the link that says view my profile which is located beside your picture. You can also click on your name or your picture. This takes up your profile page. At the top you can see boxes which are links to various pages like info, photos etc. Open the info box and there you can see your profile information...

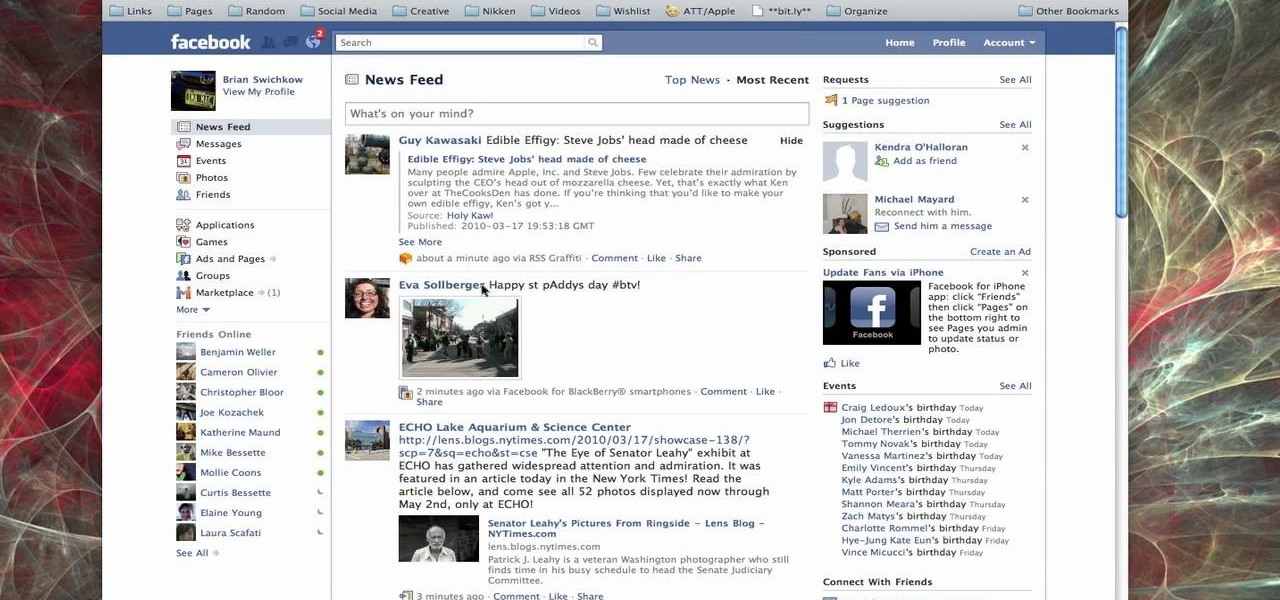
In this how-to video, you will learn how to send an update to the fans on your Facebook fan page. First, go to your fan page. Go to the top and press edit page. Now, click send an update to fans. Now, click edit to change who will receive this update. This includes sending it according to gender or location. Enter the subject and message of the fan page. Click send to complete the process. This update will be shown in the sub category in the messages page called updates. Click it to read the ...

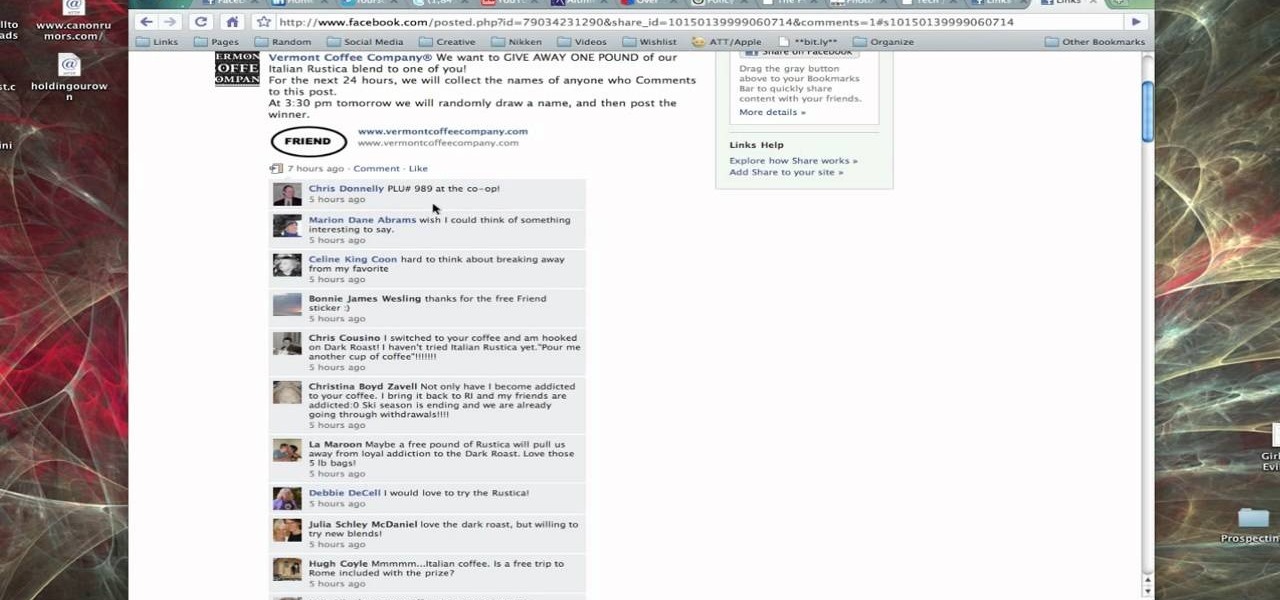
In this tutorial, Brian from TruTricks shows us an example of what Facebook can do to promote your business! One of the best ways to do this is to do micro giveaways on your Facebook. You don't have to give away something big, just something small that gives people incentive to post on your page and become a fan of your business! You will be able to see what people are posting on the page as well as everyone that is entered in your contest. This giveaway has given all the fans reason to parti...

In this video, Brian from Trutricks shows us how to create a new Twitter account. First, go to Twitter and click on the "sign up now" button. You will now be brought to a new page where you can choose your user name and enter your email, password and full name into the information boxes. Once finished, click "create account". After this, you will be able to follow people you want as well as have other people follow you. Once you are ready to tweet you can type whatever is on your mind in 140 ...

Link shortening is the process of cleaning up the URL link which is long and converting it into a short URL. You can use bit.ly to do link shortening. Using bit.ly you can not only shorten the link but also track the users who are using those links. To use this service go to the http://www.bit.ly website. There in the home page you are provided with a text box. Enter your long link in the text box and submit it. Now the website converts the long URL and provides you with a short link which ca...

In this video, you'll see how and why wax can be a deadly. This is how it works,When the test tube is submerged in cold water, the glass forms tiny cracks. The Water enters gets into the tube and vaporizes causing a micro explosion. The hot wax is then ejected from the tube quickly as oxygen is displaced from the tube itself. Be careful, and make sure to be as safe as possible when trying this experiment at home.

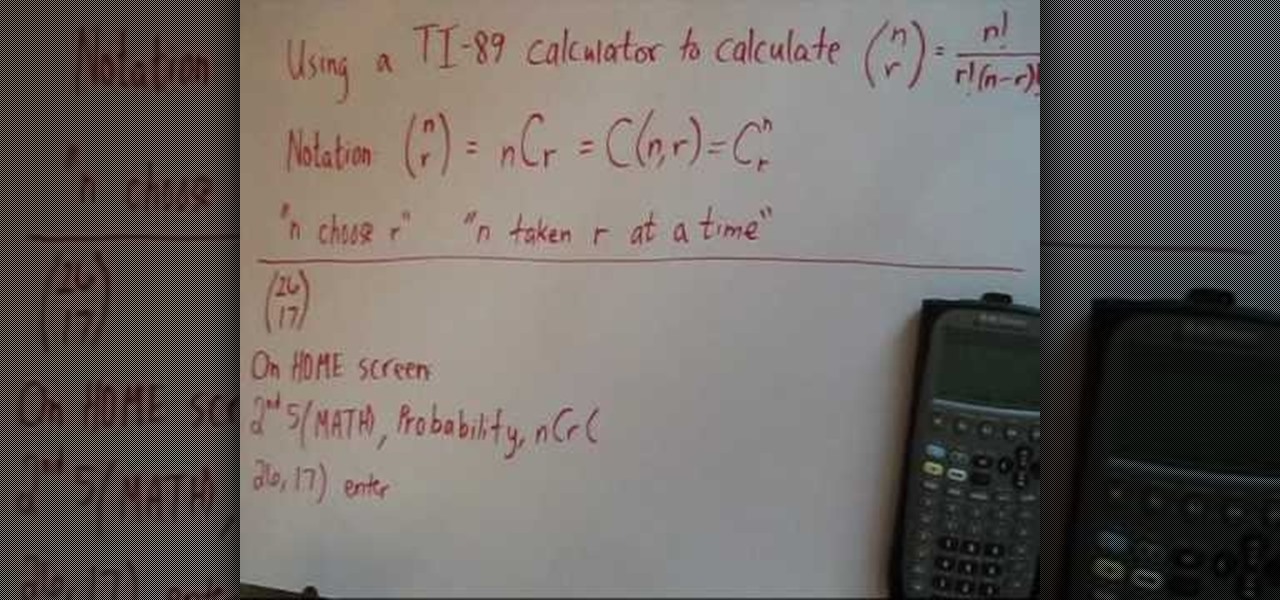
This video shows you how to do a mathematical representation on computing the nCr function using a TI-89 calculator. You can write the nCr notation in different forms. It can be simplified from nCr to C(n,r). The symbol can either be read "n choose r" or "n taken r at a time" which are from it's probability applications. On the example to find "26 choose 17", go to the Home screen of the TI-89 calculator and then go 2nd 5 which is Math. Go choose probability and then to nCr to type in (26,17)...

Installing a peephole in your home's front door can give you and your family a sense of security knowing who comes to your door before they enter. In this video Barbara K will show us exactly how to install a peephole on your door.

Learn how to create shiny, reflective and vector text in Adobe Ilustrator. Open a new file in Illustrator. Select pixel dimensions and orientation. Select the text tool and enter desired text. Ungroup the text. Select a portion of the text. Use the gradient editor to select a swatch and change the angle. Adjust the drop shadow. Create a reflection of the text using the horizontal reflect command.

By using the mirror glitch, it's possible for Link to enter the Dark World earlier than the game intended. Take a look at this instructional video and learn where and how to perform the mirror glitch to travel to the Dark World early on in Zelda: A Link to the Past. Note that this glitch works on the Game Boy Advanced and the SNES emulator, but doesn't work on the Super Nintendo console.

The BBC Focus magazine team enter the 2008 Woolacombe International Sandcastle competition applying the laws of science to build the ultimate sand castle. This tutorial video will give you some tips and tricks on applying science to sandcastles.

Watch this electronics tutorial video to learn how to enter a secret code and see a lot of interesting info on how your iPhone connects to the network. Field testing your iPhone is easy with the tips in this how-to video.

This video is a how-to demonstration of Eastern European Knitting, the purl stitch. Please note, this is not continental knitting, as here we enter through the back of the loop in both the knit and purl stitch. The resulting fabric appears exactly the same as both English and Continental knitting styles. As a note to the purl stitch, notice that the yarn is still held at the back of the work.

This video is a how-to demonstration of Eastern European Knitting. Please note, this is not continental knitting, as here we enter through the back of the loop in both the knit and purl stitch. The resulting fabric appears exactly the same as both English and Continental knitting styles. Great thing to love about ribbing using this method is that the yarn is held at the back of the work the whole time.

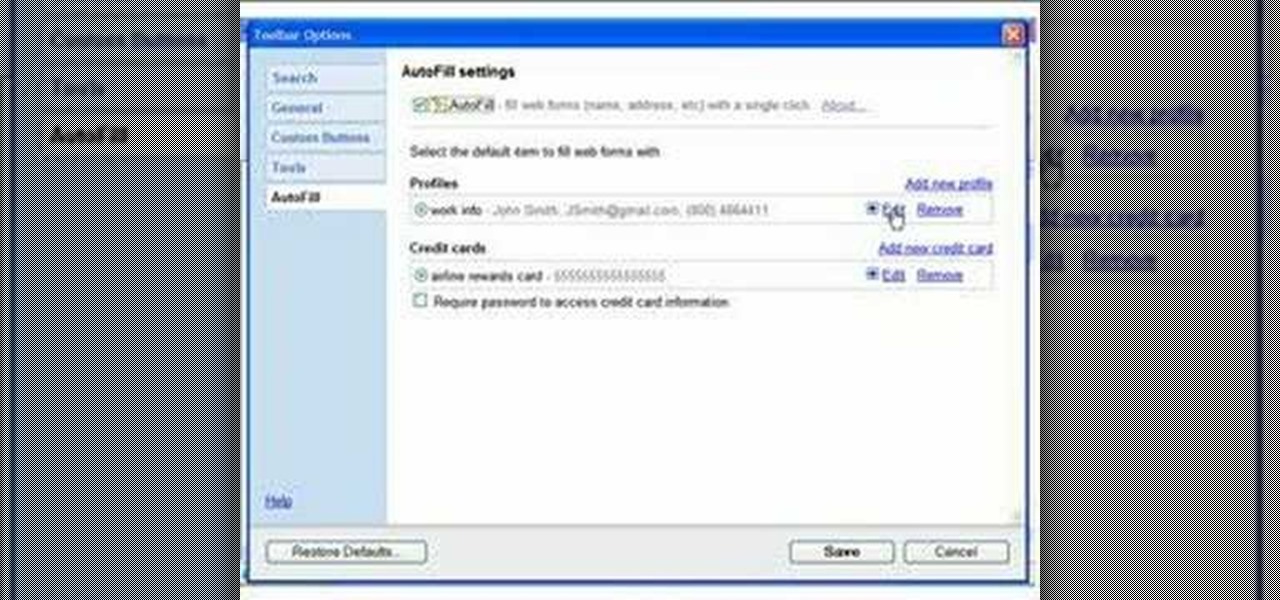
A simple video showing how to add an auto fill profile so that when you have to enter all your contact information it will do it automatically using auto fill.

If you've ever entered a lot of data into an Excel spreadsheet before, then you know that putting together even one spreadsheet is a pain in the butt. So if you are required to place all the data on one spreadsheet onto another spreadsheet, don't slave away for hours copying and pasting.

The move order 1.d4 d5 2.e3 Nf6 3.Bd3 e6 4.Nd2 c5 5.c3 Bd6 is very annoying because it discourages the key move f2-f4. Instead, White should play a different opening. He can enter a reversed Meran Defense with 6.dxc5, or a Colle System with 6.Ngf3.

This tutorial gives tips on how to properly enter corners when go-karting for the fastest times possible and while being safe.

This video demonstrates an easy way to create natural transitions. The key is to have the subject enter and exit the frame during different shots. This keeps a level of continuity that makes your movie easier to follow and easier to edit!

Male instructor explains how to create new contacts in the BlackBerry 8700 mobile device. Going to the BlackBerry's address book, it is a matter of entering in all the information for a new contact to be created. Step-by-step process makes it very easy to understand and complete the contact.

In Numbers '08 you can enter data dynamically with interactive buttons and sliders known as cell controls. This tutorial goes over using check boxes and sliders.

This simple technique to creating a bang when people open a door is sure to scare the daylights out of your friends. Using party poppers, you can take them apart and tie them across a door entry. When a person enters, the poppers explode. There are great reaction shots on this video as welll.

The iPhone's autocorrect feature is wonderful and convenient, but it doesn't always work with informal language like profanity. If you've ever used the F-word, there's a good chance you've had your curse words "corrected" to other words that don't ducking make sense. And with the release of iOS 13, swearing in your messages and on social media could get a little harder.

With new iPhone models out, you'll have updated cameras to try out, a faster processor, and new colors to choose from. The only thing that could stop you from picking one up yourself is, well, your current iPhone. Here's how to check if you're eligible to upgrade to iPhone 11, iPhone 11 Pro, iPhone 11 Pro Max, or any other iPhone still being sold.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

NMAP is an essential tool in any hacker's arsenal. Originally written by Gordon Lyon aka Fydor, it's used to locate hosts and services and create a map of the network. NMAP has always been an incredibly powerful tool, but with it's newest release, which dropped mid-November of last year, they've really out done themselves.

It has been a while since my last Raspberry Pi tutorial , but now I am back with another tutorial. This one I should note isn't your typical tutorial, but as always lets boot up our Pi and wreck havoc.

Social Engineering was mentioned a few times here on Null Byte, but not very many explained what it is, or how to do it. I love this quote because it's true: Social Engineering is the key to carrying out client side attacks, and all you need is a little creativity!

Master Lock combination padlocks have been known to be vulnerable to an attack that reduces their 64,000 possible combinations down to 100. I've devised a new attack for cracking any Master combo lock that simplifies the process and reduces the amount of work down to only 8 combinations.

When Google Play Music launched a few years ago, I ditched iTunes and began using the service as my one and only source for listening to my personal music library. While All Access is great, I still prefer the radio feature on Spotify, so I still use that to discover new music.

These days, phone calls aren't always the best way to communicate with others. Maybe you need to reach people out of the country, or you simply want to have a more visual conversation. Either way, there's a reason why video calling has become so popular.

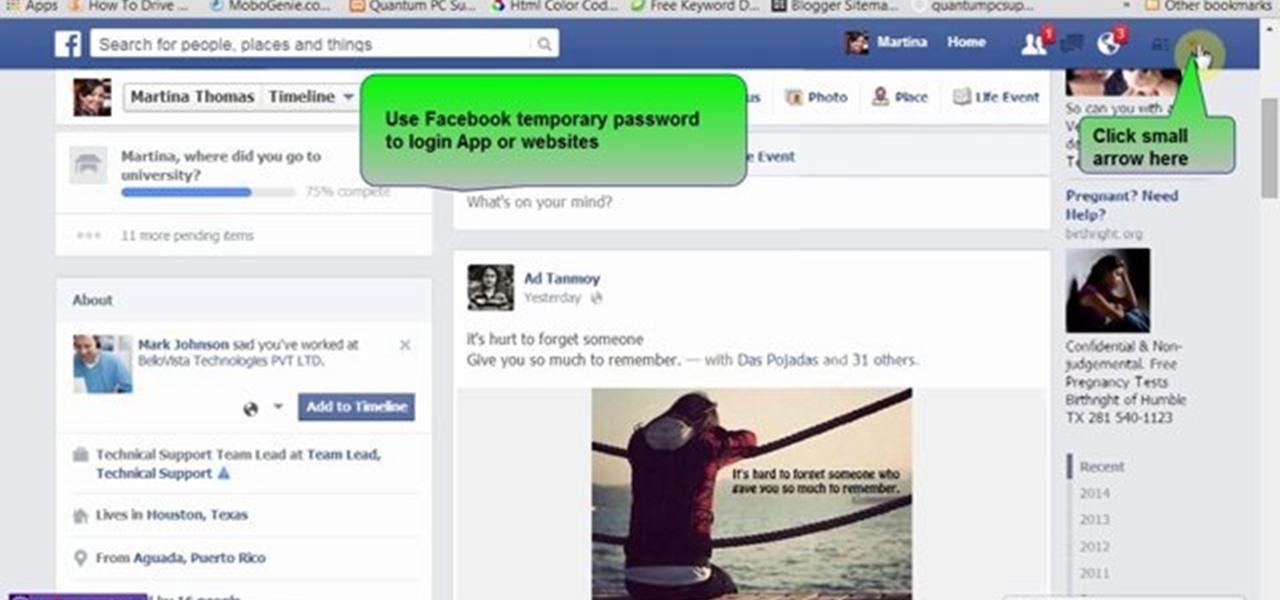
Many people use Facebook login detail to enter different apps or websites. This is somehow dangerous because unethical websites or apps may use your Facebook detail. So to avoid this warning Facebook is generating a temporary password for you. Now you could use this detail to login app or websites. You don't have to use your Facebook original login detail.