Magic Leap One owners, start your virtual engines, as automotive virtual reality developer RelayCars has published an app to Magic Leap World that lets users customize and test drive a 2019 Kia Stinger.

To punch up the launch of its new podcast, USA Today has created an augmented reality experience to introduce listeners to the story of corruption in Chicago.

Unsurprisingly, Google wants to be the caretaker for augmented reality on the web, and its latest move in this endeavor is a 3D model viewer prototype called Article that's designed to work across all web browsers.

After hosting millions of free 3D models online, Sketchfab is betting that augmented reality and virtual reality developers and creators will be willing to pay for premium 3D content.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.
Researchers at Disney have demonstrated the ability to render virtual characters in augmented reality that are able interact autonomously with its surrounding physical environment.

It's fitting that students at the University of Washington can catch a glimpse of the new, 135,000 square-foot computer science building in augmented reality before construction is completed.

According to Dr. Lindsey Fitzharris of The Chirurgeon's Apprentice, hospitals during the first half of the nineteenth century were known as "Houses of Death."

The Washington Post believes augmented reality adds an extra layer to stories, and they're doubling down on that belief by adding in new AR features into their already popular "rainbow" news (iOS and Android) and Classic (iOS and Android) news apps.

Five Phases of Hacking:- The five phases of Hacking are as follow:

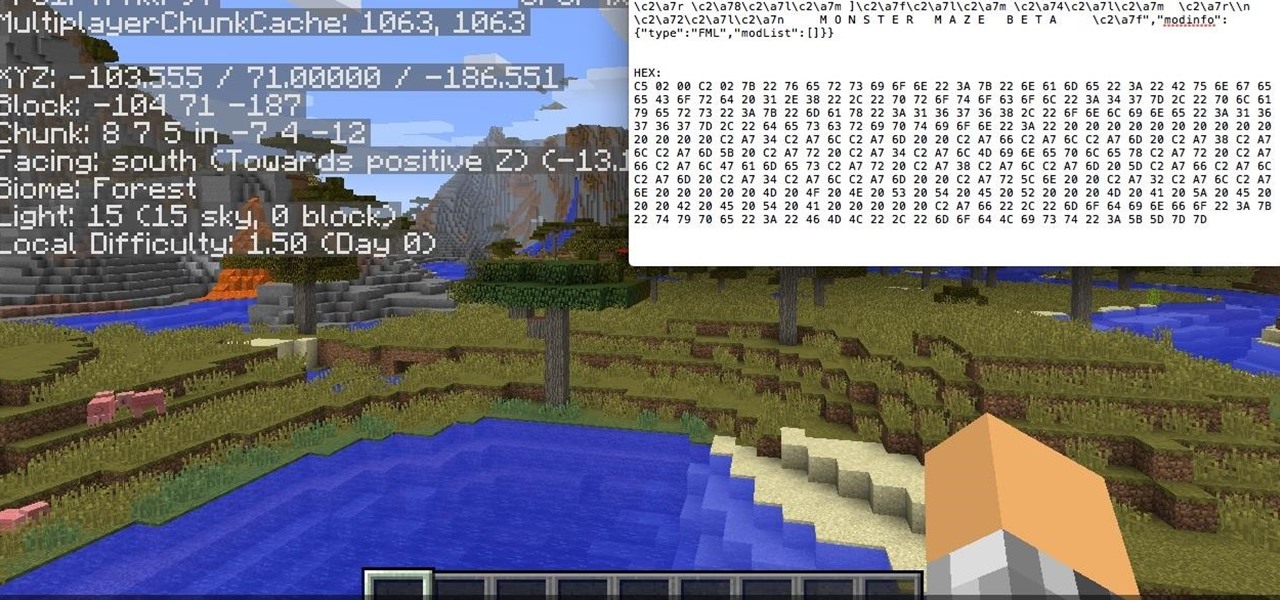
Hello, fellow hackers. I'm sure we've all seen it somewhere: the undying question of "How do I hack the game so-and-so?" And the answer usually is, "Come back when you actually know how to hack!" But how does one even go about "hacking" a game? What could that even mean?

From day to day, it can be difficult to remember everything that's required of you. I tend to forget exactly where it is I'm supposed to be during my busiest moments, and it's even easier to delete each day's events out of your brain when there's so much else that dominates your mind. Yet taking the time to remember exactly what it is that happens during each of our days can be a vital part of our memory—and with nothing more than 15 minutes, we can strengthen our brains and remember more tha...

Welcome back, my hacking friends. We use our smartphones every day, for business, socialization, and leisure. The number of iPhone users is increasing in dozens of millions every year, with a whopping 63.2 million users in 2014 alone. That's a lot of users.

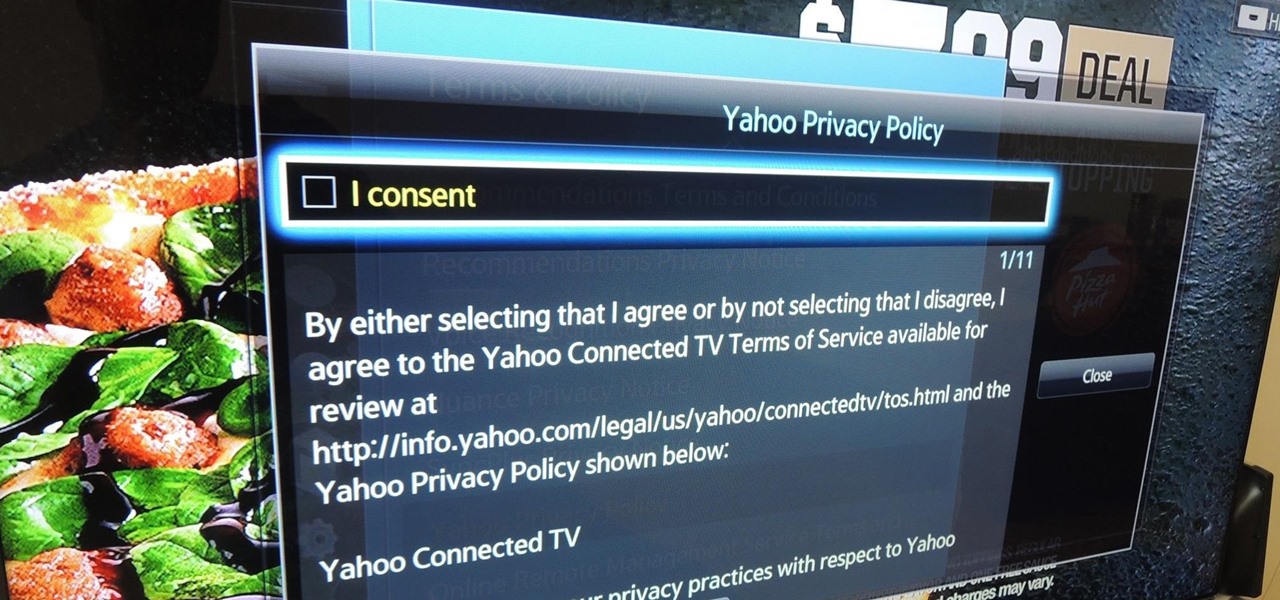
Televisions used to be great for just one thing—watching TV. But a more connected world brought with it Smart TVs, devices that can access the web, stream Netflix, and even mirror your smartphone's display. And with this level of connectivity, OEMs like Samsung saw it fit to place targeted and interactive ads on your screen.

Whether you're a serious, sweating athlete or just need to recover after a night of drinking, chances are you've replenished your body's fluids with a sports drink at some point. Those electrolytes aren't the only thing entering your systems, though. Sports drinks are sugary, sweet, and loaded with calories—but there's a way you can still recharge your body without ingesting the unhealthy additives.

Brought to you by Tomcat. Falling snow, warm fireplace, delicious hot cocoa, quiet reading time, mouse. Quick quiz - which one is not like the other? Nothing can ruin a perfectly cozy afternoon in your home like a pest on the loose. With dropping temperatures, you may have some unwelcome residents, like mice, looking for shelter from the cold.

Restrictions are inconvenient, and for this reason I've sought out softmods that loosen the constraints for many of the features on my smartphone. Things like adding favorite apps to the Pen Window drawer or choosing any app for Multi Window mode are now must-haves on my Samsung Galaxy Note 3—and should be on yours as well.

Humans clearly demonstrate altruistic tendencies towards other members of groups with which they identify.

This Animal Welfare Foundation two-part video tutorial is from expert veterinary staff demonstrating the correct procedures for handling small mammals for clinical examination and medication. Its aim is to show that the primary consideration should be for the the welfare of the animal. This video guide will show you practical animal handling for a mouse.

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.

The new Pyro FX in Houdini 10 are very impressive with improved workflow. The Pyro FX are great for creating 3D fire and smoke effects. And in this video tutorial series, you will learn the Pyro FX workflow in-depth and the parameters used to create fire and smoke effects. You will also see how volumetric data is created and recorded, and how to visualize it.

Last Friday's mission was to accomplish solving HackThisSite, realistic 4. The fourth in a series of realistic simulation missions was designed to be exactly like a situation you may encounter in the real world. This time, we are told "Fischer's Animal Products is a company that slaughters animals and turns their skin into overpriced products which are then sold to rich bastards! Help animal rights activists increase political awareness by hacking their mailing list."

Kevin Van Aelst creates witty visual "one-liners" by recontextualizing everyday, ordinary objects. With a few simple tweaks, the viewer recognizes a roll of tape as the ocean or reads gummi worms as chromosomes or understands mitosis through the use of sweet, sugary donuts.

Nearly all humans (admittedly childishly) admire the ability to emit uncannily musical armpit or hand farts, or even rarer- mouth fart motor engine aping. However, it is the rare occasion that a performer's gaseous-sounding melodic notes are indeed truly gaseous (meaning literally discharged from the butt-hole).

My father recently suffered a stroke. Now in Neuro Rehab at Cedars Sinai, he is enduring daily physical therapy, recreational therapy and occupational therapy sessions to help improve his balance, mobility and fine motor skills. I was initially worried about how I could incorporate his current PT regime in his daily life after he's discharged. That was until I saw the devices he used in the PT gym. Despite their "medical device" designations, the high tech stuff is remarkably similar to what ...

IEEE Spectrum examines the practice of cryonically freezing the dead, with the intent to "reboot" when medical advances are prepared to undo their death.

The New York Times magazine posts a fascinating feature on a Chinese cultural phenomenon known as human flesh search engines. Out of China has borne cyberposses, internet vigilantes, who target everybody from twisted individuals violating social norms to government corruption.

While IKEA will employ ARKit to help you see how that new couch looks in your living room, Redbubble wants to show you throw pillows that match.

New serious results appeared regarding the early puberty "precocious puberty" and its impact on the health of young girls. New studies in Cambridge university regarding the shows that early puberty is associated with increased risk for diabetes, Cardiovascular disease, breast cancer and endometrial cancer.

Dopamine is a neurotransmitter that motivates us to engage in rewarding activities such as eating and sex. Animals without dopamine stop eating and starve to death.

Japanese artist Motoi Yamamoto's medium of choice is none other than your simple household table salt, fragile and completely ephemeral. Yamamoto creates beautiful installations with the medium, salt being a strong symbol in Japanese death culture (as well as several other cultures around the world: Hinduism, Catholicism, Egyptian and Aztec mythology).

It’s a game, it involves numbers, it’s fun, it’s KenKen! Understanding the goals and rules of this fun, numbers puzzle will give you the skills you need to win. Have fun working your brain and passing the time with KenKen.

The worlds of augmented reality and virtual reality are closely linked in many ways. That means it's smart for AR insiders to keep a close on new developments in VR. If you have been paying attention, you know that Oculus CTO John Carmack is one one of the most important thinkers in the VR space.

The one thing that separates a script kiddy from a legitimate hacker or security professional is the ability to program. Script kiddies use other people's tools, while hackers and security pros write their own tools. To that end, we're going to see how a stack overflow vulnerability allows us to flood a variable with enough input to overwrite the instruction pointer with our own commands.

This video shows how an arthroscope is used to examine a joint and perform minor surgery. Look inside a knee and other joints.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.

Bed bugs are brown and creepy. Could you spot one in your hotel room? A new study reveals most people are freaked out by bed bugs, but only about 35% could identify one.

Welcome back, my nascent hackers! In the conclusion of the Mr. Robot television series, Elliot and fsociety successfully completed their mission of encrypting all of Evil Corp's data with AES-128 encryption and destroying the key.

Welcome back, my budding hackers! As I have mentioned many times throughout this series, knowing a bit of digital forensics might keep you out of a lot of trouble. In addition, digital forensics is a burgeoning and high paying career. Some knowledge and certifications in this field will likely help you land a Security Engineer position or put you on the Incident Response Team at your employer.