Malware attacks on mobile phones are reaching an all-time high and it looks like companies like Samsung are doing all that they can to prevent any unwanted hackers from accessing its sensitive user data.

Stop me if you've heard this one before. You plop a marshmallow down in front of a kid and propose the following: You can eat this marshmallow now, or you can wait twenty minutes and eat two marshmallows. What do you think the kid is going to do? Better still, what do you think you would do? Personally, I'd eat the first marshmallow without hesitation. But now we're getting off track ...

If you relate in any way to having the need to carry your iPhone and your vaporizer in one hand, then keep on reading.

The Galaxy S8's Bixby Vision feature isn't working up to its full potential for Verizon customers, according to a recent CNET report.

Even though the Galaxy S8 and S8+ are only just now being released to the public, the software leaks have been rolling in for a while. Everyone seems to have gone crazy for the new look Samsung is pushing out with Samsung Experience, the successor to TouchWiz. As a result, there have been quite a few applications ported over from the Galaxy S8 to older Samsung phones.

NBA star Andre Iguodala, of the Golden State Warriors, got to try out a Magic Leap demo in Florida and started dishing out some pretty revealing details about the upcoming mixed reality headset to CNET's Brian Tong.

It may seem strange to find the director of engineering at a question-and-answer site all of a sudden pick up and lead a new driverless startup, but to Kah Seng Tay, both engineering tasks require building the right infrastructure to handle large amounts of AI data.

I had the opportunity to speak with the COO of Osterhout Design Group, Pete Jameson, shortly before the announcement of the company's R-8 and R-9 smartglasses models at CES in January. And while I sadly could not make it to CES to test the smart specs out right away, ODG invited me to do just that while I was in San Francisco for the Game Developers Conference.

You can get eggs and high-quality compost from backyard chickens—but you can also get Salmonella.

Xiaomi phones run a skinned version of Android known as MIUI, which, over the years, has been a popular custom ROM. One of the standout features Xiaomi has added to the mix is something called Quick Ball, which lets you navigate your phone by swiping inward from a small circle that resides on the edge of your screen.

Crayon, a free 3D drawing application by the mysteriously named arkalian, showed up in the Windows Store recently, so I gave it a try like I do all new apps for Windows Holographic. Truthfully, I loaded it up not expecting much, but wow, was I wrong. It's a simple idea, but it's executed well enough to make it a truly great experience on the HoloLens.

Yes, I know it's autumn and the trees are losing their leaves, but the seasons do not decide when I can or cannot enjoy ice cream. No matter how warm or cold is is outside right now, I will remain completely fascinated by rolled ice cream. Yes, rolled.

Halloween is this weekend, so if you're looking for a last-minute big batch cocktail that will keep your guests properly hydrated—and might turn them into mutants—look no further! (Note: This will not actually hydrate anyone, just so we're clear. Priorities, people!)

While Leap Motion and Microsoft are looking to capture natural human motion with cameras, Enflux figured out how to do it with a shirt and pants that feel completely natural.

Augmented reality allows for all kinds of experiences to happen just about anywhere, and that creates some incredible potential for entertainment. While games like Pokémon GO take you out into the world, one crowd-funded game wants to keep you inside—to scare the crap out of you in your own home.

It seems like everyone is getting in shape these days (or at least trying to improve their fitness), and as a result, there's an endless supply of fitness trackers and smartwatches hitting the market. This is all very wonderful, unless of course, you're broke and can barely afford a decent pair of running shoes.

Lens Launcher was one of the winners of 2106's Android Experiments I/O Challenge a few months ago, and with good reason—it gives us a new way to browse for apps on our Android phones. It's slightly reminiscent of how the Apple Watch does it, but even better.

When you're trying to cut some calories or just eat more veggies, it's important to enjoy what you're eating. If all you're doing is telling yourself "no" and focusing on what you can't eat, you are pretty much destined to fail at your diet.

Welcome back everyone. I apologize for the lack of training articles, but I've been rater busy lately. I've recently picked up a second job and my college courses are now back in session, so I'm a bit strapped for time.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

If you have personal information stored on a Kindle Fire tablet, be warned that Amazon has removed encryption support for Fire OS 5. So if you have stuff on these devices...maybe a risque book, or private notes, or pictures you'd rather not let out to the world, now would be the time to remove them. And unless Amazon changes its mind and re-enables encryption, don't use your device for anything personal, as anyone who gets a hold of it will be able to gain access to everything on it.

My first ever post on here was 'Keeping your hacking identity secret' and it did very well, and its not something I see here on null byte. So read along.

Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

Smartphones are almost always connected to the internet, so it stands to reason that they can be hacked remotely. Or perhaps a jealous boyfriend or girlfriend got hold of your device physically, in which case they could've potentially installed a keystroke logger, a virus, or any other type of tracking app to spy on you.

A few months ago, my friend Sarah appeared at a party bearing homemade liqueurs—amaretto, hazelnut (e.g. Frangelico), and vanilla liqueurs, to be exact. Her cool factor, which was already quite high, jumped up a few more notches—as did the overall energy of the party. (And that's why we call her 'Game Time.')

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...

What's your top pet peeve? Open-mouthed chewing? Nail biting and knuckle cracking? The sound of silverware scraping? Or perhaps it's a bigger behavior, like leaving the toilet seat up?

Task Manager got revamped quite a bit in modern versions of Windows. First introduced in Windows NT 4.0, it's become pretty popular among more advanced users. In Windows 10, Task Manager is not just a task manager anymore, it's also a system monitor, startup manager, history viewer, user controller, and the list goes on.

The art of taking secret photos is one that requires keen awareness and skill. Not only do you need to ensure that your subject remains oblivious, but you also need to make sure that no one near you notices what you're attempting to do. It's great when you buddy is acting a fool, but sucks when they stop their shenanigans when they notice you pulling out your camera phone in an effort to evade your picture.

In addition to sharing emojis and GIFs, most of us also probably share various types of links through email or text, whether it be for a Google Maps location, a bar or restaurant on Yelp, or an awesome song on Spotify.

Part 1: What is Popcorn Time? Part 2: What is a torrent?

It feels great to wrap up in a big, fluffy towel after a steamy shower, but it's frustrating when that towel isn't quite up to the job. Over time, towels lose their ability to hold water and dry as needed thanks to daily use and the biggest culprit—laundry detergent.

These last few months have been a Lollipop lovefest, and I'm not talking about the candy. Android's latest OS has been exalted for its embrace of Material Design, and we've certainly given Lollipop its fair share of coverage as well; check out all its new features and ways to make older devices get some of the new look and feel of Android 5.0.

Did you know that your face shows others how much alcohol you drink? Whether you've never had a sip of booze with those around you or you're known as the party animal of the group, the genes that shape your appearance also show others just how much you enjoy liquor. Pinpointing the big drinker in any setting is easy to determine: you just need to make eye contact.

Silencing my phone always gives me mild anxiety; while my Android is muted, my girlfriend or boss may be trying to reach me with some urgent news or task. On the one hand, I want to enjoy some peace and quiet, but on the other, I don't want to come back to a phone with 100 missed calls and countless exclamatory texts.

It's time to step up your selfie game, especially if all of your selfies tend to have the same vapid look and feel. There are plenty of techniques for better selfie-taking, and I've already shown you a few iPhone tricks, like making yourself look thinner and using hand gestures to get situated better. Now I'll show you how to give your followers something to really "like"—celebrities.

Earlier this month, John Oliver spent a segment on Last Week Tonight explaining native advertising, a practice followed by many online media outlets such as BuzzFeed, The New York Times, and VICE, which combines editorial content along with sponsored advertisements.

Unless you're someone who's terrified of social situations, chances are you love to talk. But no matter how much you want to share you life story or take over the conversation, you shouldn't. Your socially awkward coworkers that keep their mouth shut might actually have a leg up on you at work, and here's why.

Buying and drinking wine can be intimidating. There's so much to know, and so many ways to reveal your ignorance. If you're completely befuddled by wine and how to describe it, don't worry, you're not alone.

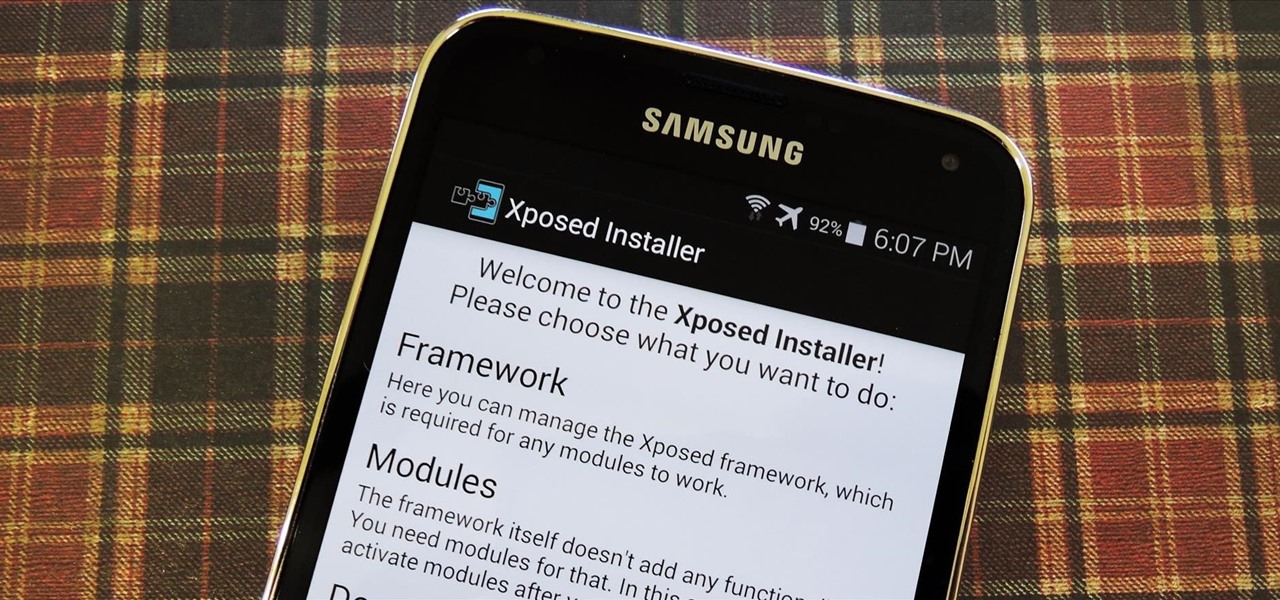
Now that all variants of the Galaxy S5 have finally been rooted, we can start exploring all of the tweaks and hacks that Superuser privileges open up to us.