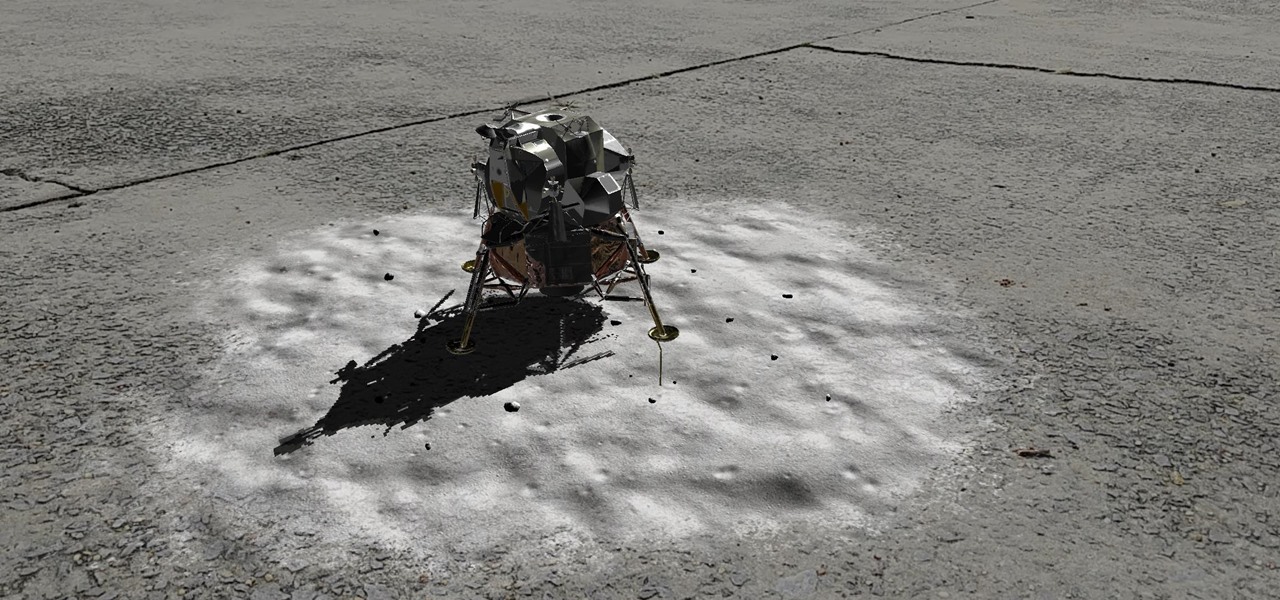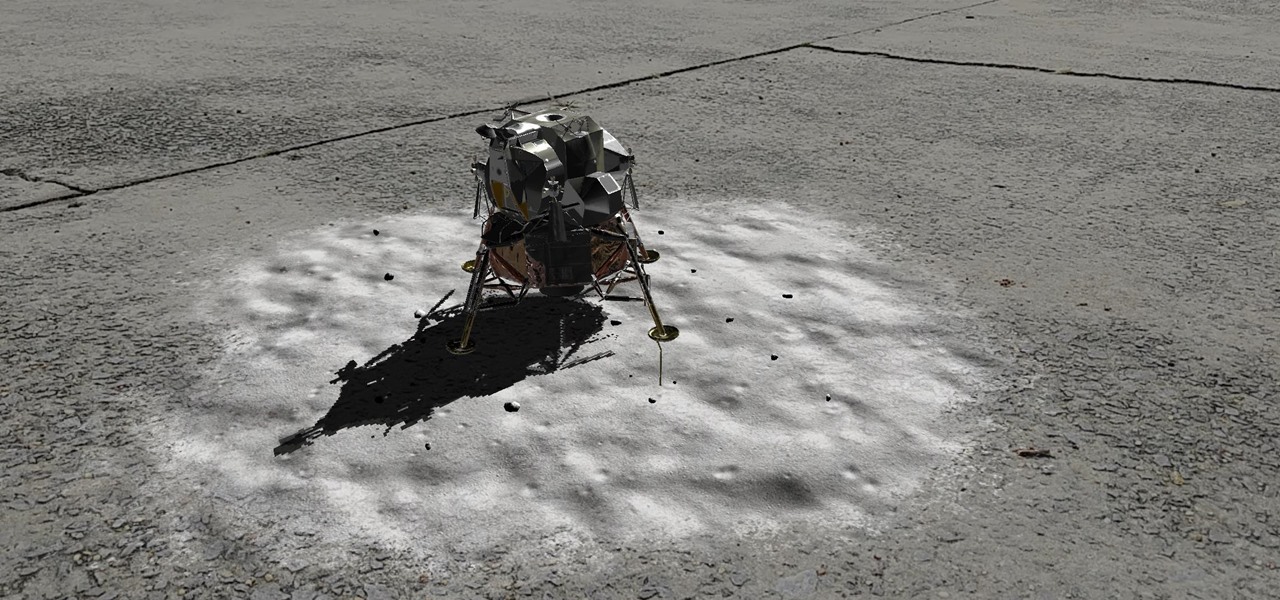
Unless you've been hiding under a (moon) rock for the past month, you already know that Saturday, July 20 is the 50th anniversary of NASA's Apollo 11 lunar landing.
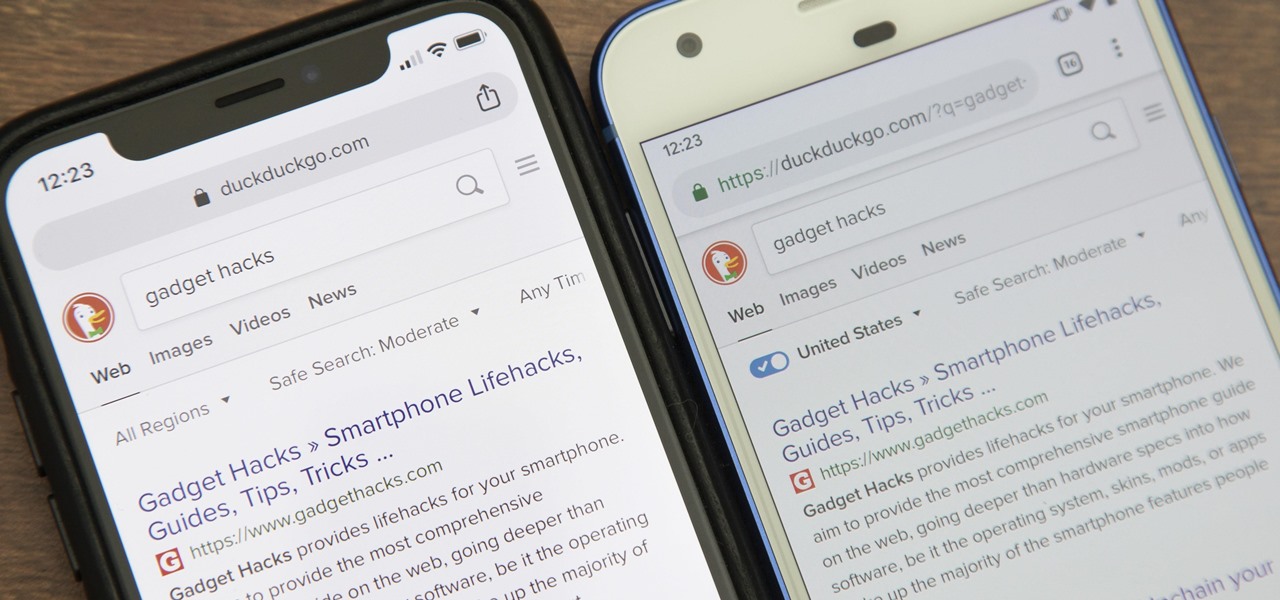
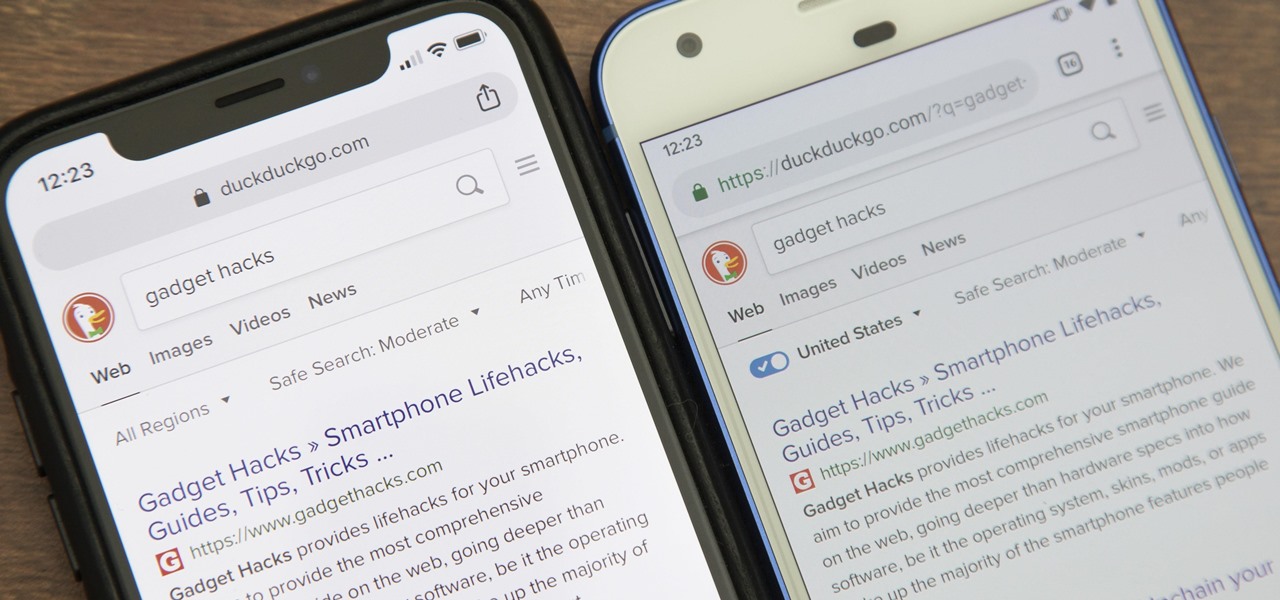
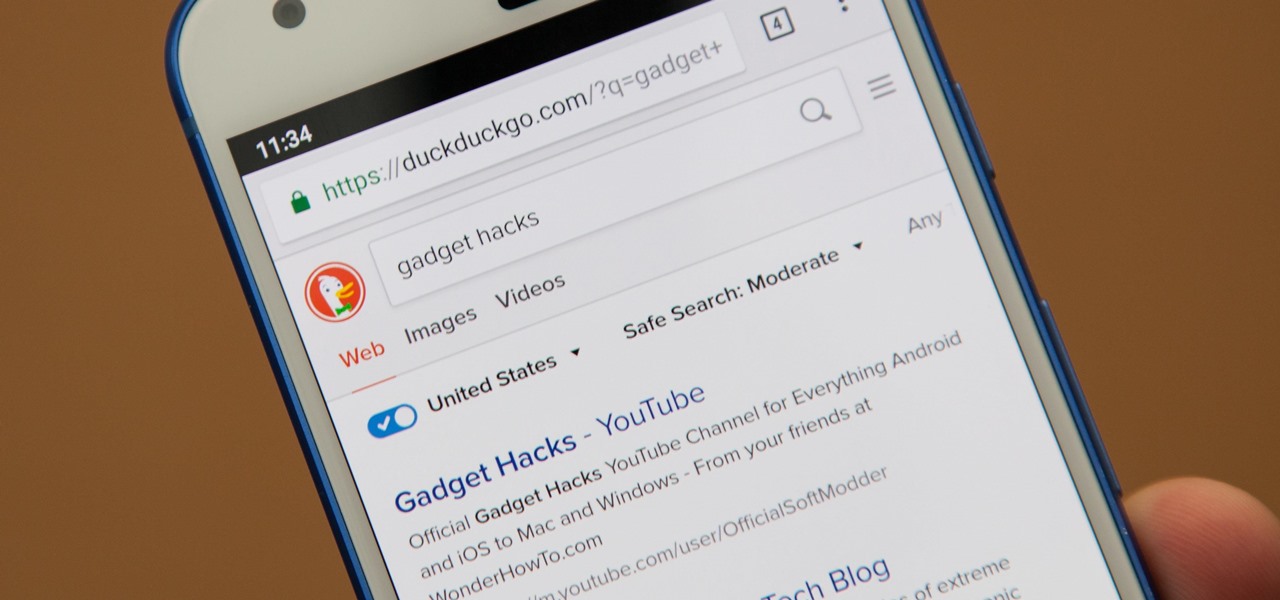
While Google would rather you use Google as the default search engine in Chrome, there's a way to switch to the more privacy-geared DuckDuckGo search engine for all your web browsing needs. With DuckDuckGo, the company does not track anything you search or allow anyone else to track it, so you can effectively search from your iPhone or Android phone anonymously.
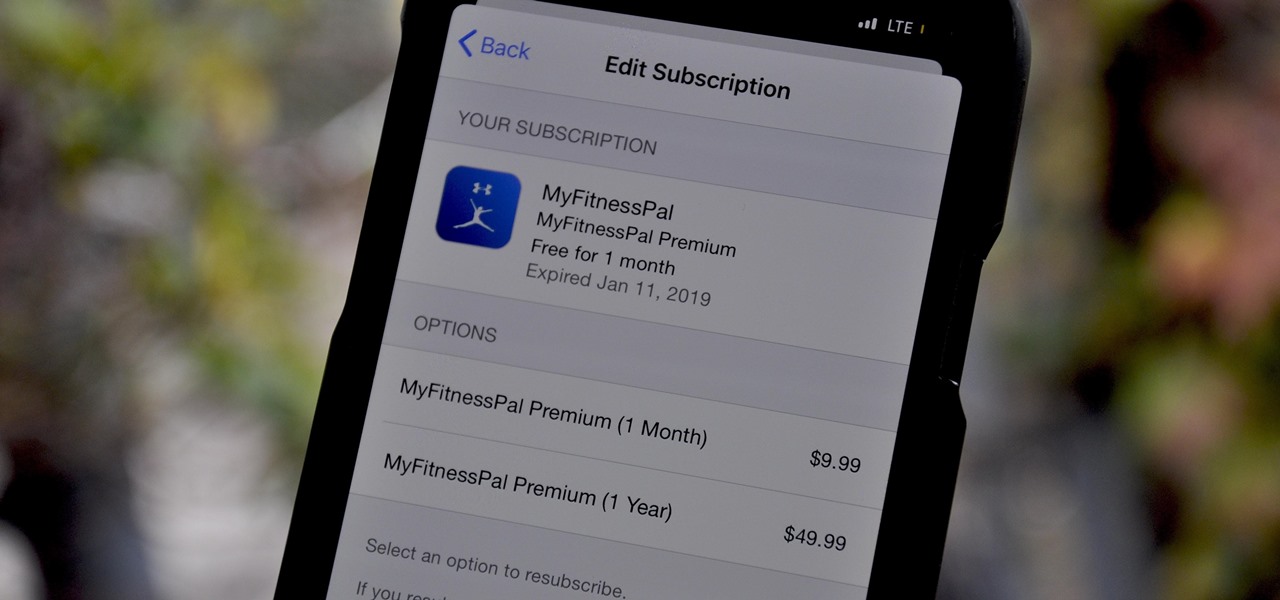
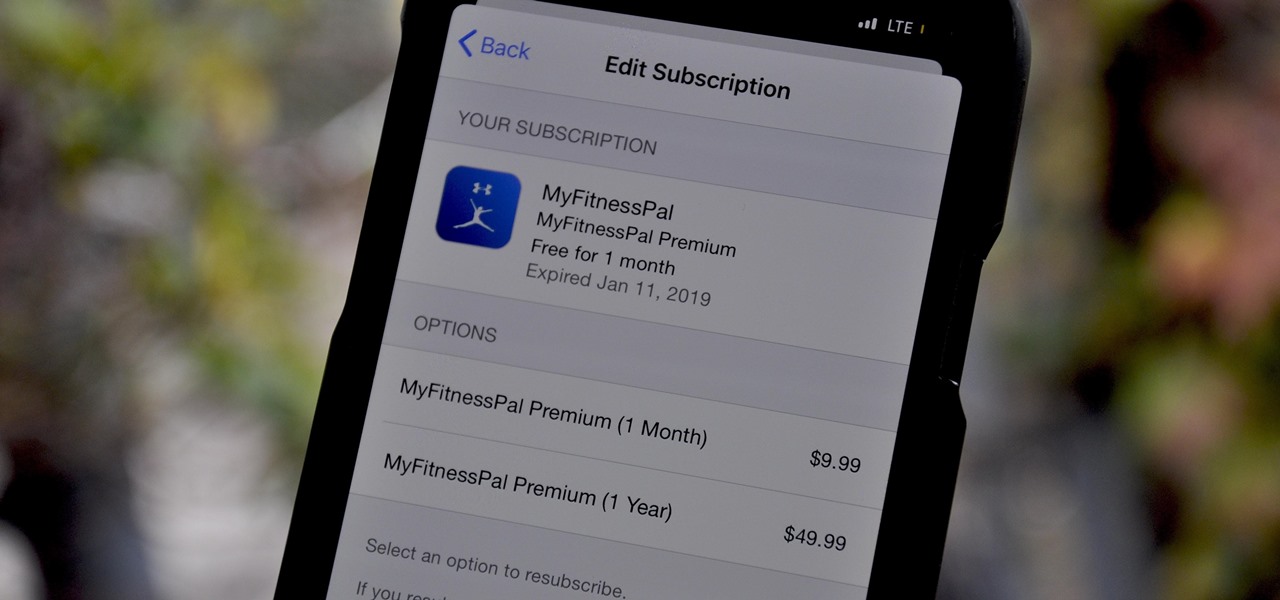
In 2015, MyFitnessPal launched its premium service, an ad-free subscription for $9.99 a month or $49.99 a year which provides food analysis, deeper nutrient tools, more goal options, and exclusive content. After giving MyFitnessPal Premium a shot on your iPhone or Android phone, those perks may be unnecessary to your end goal, but you'll find that canceling your paid membership isn't very easy.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

As Android bug bounty hunters and penetration testers, we need a properly configured environment to work in when testing exploits and looking for vulnerabilities. This could mean a virtual Android operating system or a dedicated network for capturing requests and performing man-in-the-middle attacks.

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.

Over the years, we've seen security breach after security breach, as well as high-profile data scandals where collected personal information was misused by companies. Apple makes customer privacy a priority, so there have been few issues to worry about when it comes to its services on your iPhone. However, there are still plenty of privacy settings to explore and change, especially within Safari.

If you're looking for a new Reddit client on your iPhone, look no further than Apollo. Launched with iOS in mind, Apollo is a free app that offers an exceptional Reddit experience, but some of its excellent features — as well as some necessary ones — are hidden behind its "Pro" paywall. Are these extras worth your money?

Even if your default mobile browser is Google Chrome, you may not want Google to also be your search engine. Maybe you're not impressed with Google's search results all the time, maybe you want a more private search experience, or maybe you just don't want Google's hands over everything in your life. Whatever the case, it's easy to switch from Google to another default search engine.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

To celebrate its tenth anniversary, PornHub has just exposed all of our porn habits. All. Of. Them. Before you panic, no individual information has been released. Instead, PornHub has exposed the adult video trends and preferences of a variety of demographics.

We're all guilty of a little social media stalking now and again. Or ... every day. Who's keeping track? Everyone secretly wants to know what their ex/arch nemesis is doing for the weekend via Snapchat or Instagram Stories.

If maintaining privacy is an ongoing battle, the front line is your smartphone. Apple included several new security features in iOS 10, but at the same time, some of the best new functionality comes with potential privacy trade-offs that everyone needs to understand.

You may not know what HTTP is exactly, but you definitely know that every single website you visit starts with it. Without the Hypertext Transfer Protocol, there'd be no easy way to view all the text, media, and data that you're able to see online. However, all communication between your browser and a website are unencrypted, which means it can be eavesdropped on.

While it may not sound scary right off the bat, Blue Coat Systems now has an intermediate certificate authority. If you don't know what a certificate authority (CA) is, or who Blue Coat is, who cares, right? But you should... whether you use Mac or Windows.

Apple has stepped up its emoji game lately, and as a result, there are several iPhone emojis that don't show up on Android devices running older firmware. However, Google responded by adding a next-gen set of Unicode 9.0 emojis to its Android Nougat preview build, meaning that soon, Android will have more emojis than iOS.

Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA did embed a backdoor on those devices.)

Mobile payment systems have been around for almost 5 years now, starting with Google Wallet. But when Apple got into the game last year with their new Apple Pay service, things really started to take off. Around this time, Samsung responded by acquiring an up-and-coming mobile payments company that owned the rights to an incredibly innovative technology called Magnetic Secure Transmission (MST).

Let's be real, browser histories are virtually useless. Trying to find something you passed up a week ago is like, pardon the cliché, finding a needle in a haystack.

Apple announced the successor to Mac OS X Mavericks at their Worldwide Developer's Conference 2014, and it's called Yosemite. Named after California's Yosemite National Park, it will be available as a free upgrade from the Mac App Store for everyone this fall.

Most people keep their ungodly sexual desires deep inside, only to be indulged in private on their computers. It makes you wonder... what secrets do your neighbors have? What kind of porn are they watching? And how much and for how long? Thanks to some public (and anonymous) data, you can now find out.

Welcome back, my tenderfoot hackers! So many readers in the Null Byte community have been asking me questions about evading detection and hacking undetected that I decided to start a new series on digital forensics.

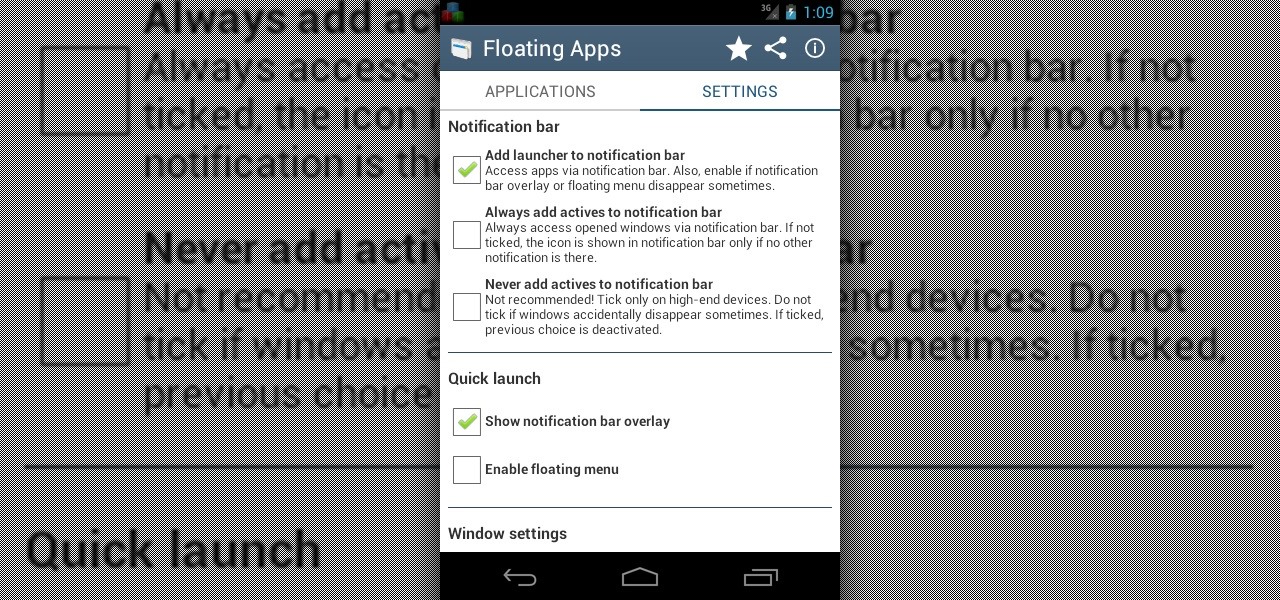
Sometimes, it's very useful to be able to use more than one app on Android phone or tablet. For example, if you want to watch a movie while surfing or if you need calculator, find some contact, write a note, search web or wikipedia for some facts, etc.

Grill Guru Ted Reader cooks up a quick grill recipe using "Honey Garlic & Fig BBQ Sauce", Prime Chicken Wings, and some Gorgonzola Blue Cheese. Learn how to prepare and grill this fig'n delicious chicken wings recipe by watching this video cooking tutorial.

Grill Guru Ted Reader cooks up a quick grill recipe using Saki Teriyaki Marinade, a cedar plank, crab, and dill. Get together with some friends and family & have a really delicious time. Learn how to make this Kama Sutra Saki Teriyaki Salmon recipe by watching this video cooking tutorial.

This tutorial shows you how to read text from a text file into a C# application. Use the stream reader object found within the system IO name space.

Remember summer camp? Remember the smell of the log cabins? The feel of the treated wood? Well, you can create something for your home that's perfect for a nostalgic summer camp aesthetic. Meg Allen Cole (recently of Threadbanger) was inspired to make this mid-century modern wall hanging piece made from a small wooden log (or branch) when she was at a relaxing, wooded vacation spot in Maine. And she shows you how to make one, too!

Step1. Make sure you get your facts straight. Note down the dates, names, and numbers, what was said etc while talking over the phone. It is also essential that when you present your letter of complaint that it is chalked full of facts so that when it reaches a decision maker you may get justice properly. Do not write a novel that is 30 pages. Keep it short and write in bullets. Remember that they are interested in facts only.

Open up Cheat Engine and be prepared to hack Restaurant City! This is a new level hack that will help you gain levels fast.

How to hack Pet Society! Pet Society cheats, tricks, hacks. Watch this video tutorial to learn how to poop in Pet Society (09/05/09).

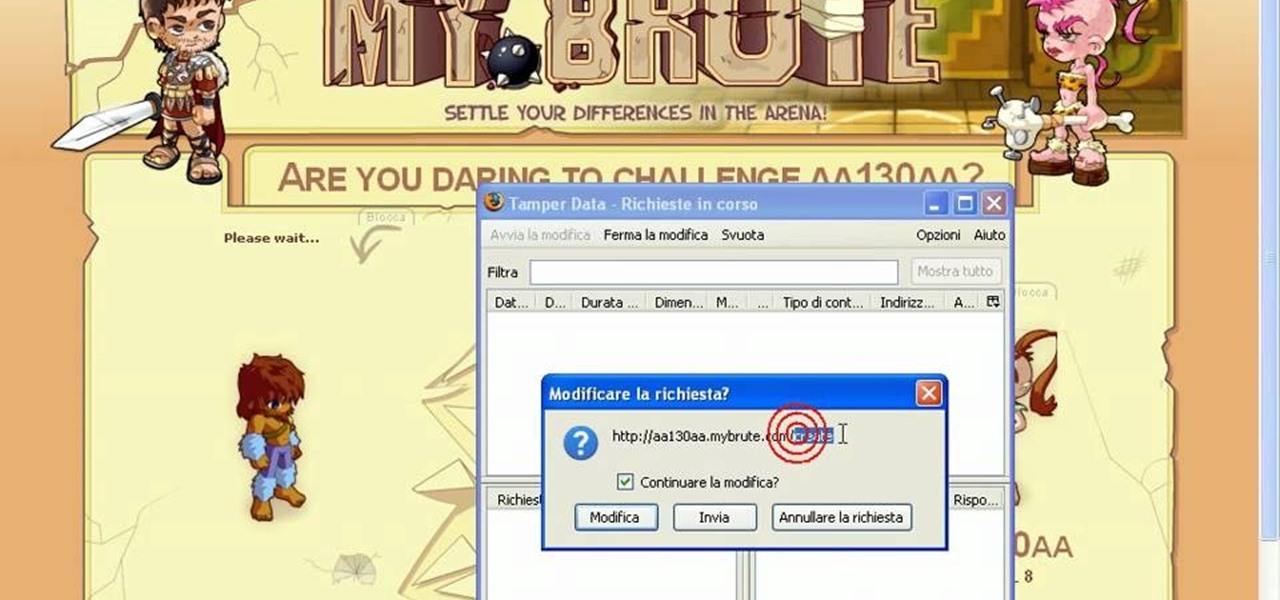
Hack mybrute with this mybrute cheat. MyBrute hacks, cheats, tricks. Watch this video tutorial to learn how to cheat MyBrute for a bear (05/08/09). This is the easiest way to get a bear!

Check out this video tutorial on how to make cheap dragon wings, controlled by body posture. You can do this project for $18 if you use plastic garbage bags and Scotch tape for the membranes. You'll see how to make very light and strong costume wings. How strong? That strong.

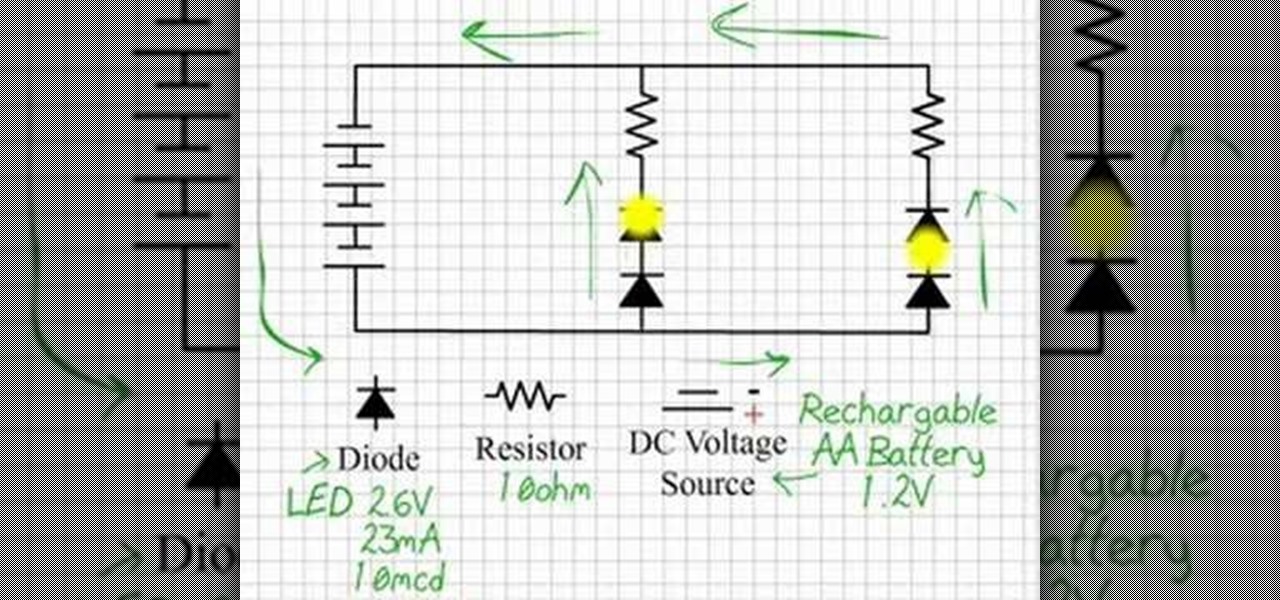
By using LEDs that only put out a little light the eyes can be lit in dim room light but still appear white, the moment the eyes are in shadow they glow bright red. Watch this video tutorial to see how to make glowing LED creature costume eyes for your film or costume project.

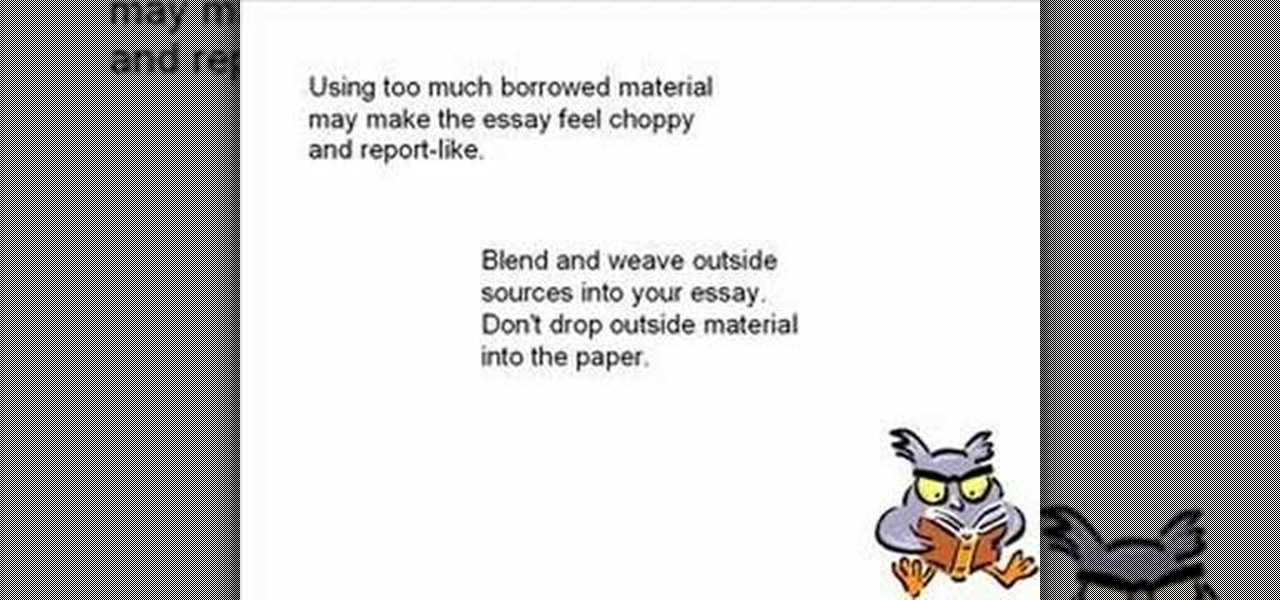
This is working about working with sources: Quotation, Summarizing and Paraphrasing. Quotation: When directly quoting an outside source, the author's words should be taken verbatim. Quotation can lend the essay credibility. Too much quotation makes it sounds like you, the writer don't have anything to say. Quotes should be used only when the writer needs to be precise, clear, and powerful. You should use the quotes when the person you are calling said in a unique way that really can't be put ...

Computer crashes, fried hard drives, red rings of death, delinquent memory cards... nothing is worse than dysfunctional technology. In just a minute, your favorite and most used device has become the biggest headache of your life, frustrating you to the brink of madness. But what's worse than your electronics just giving up on you?

Try "unfocusing" your photographs for some dreamy, evocative and somewhat abstract takes on life. Check out the two tutorials (here and here) from Michelle Geoga of Lights! Camera! Photoshop! for tips on unleashing the blur-power of your camera. You can see plenty of example images there to help you out.

Fight through Fortune City with Chuck Green and kill some freakin' ZOMBIES in Dead Rising 2 on the Xbox 360. This walkthrough series shows you the gameplay of this video game, as you and Chuck kill the undead and struggle to survive. For more information about this walkthrough, visit Mahalo.

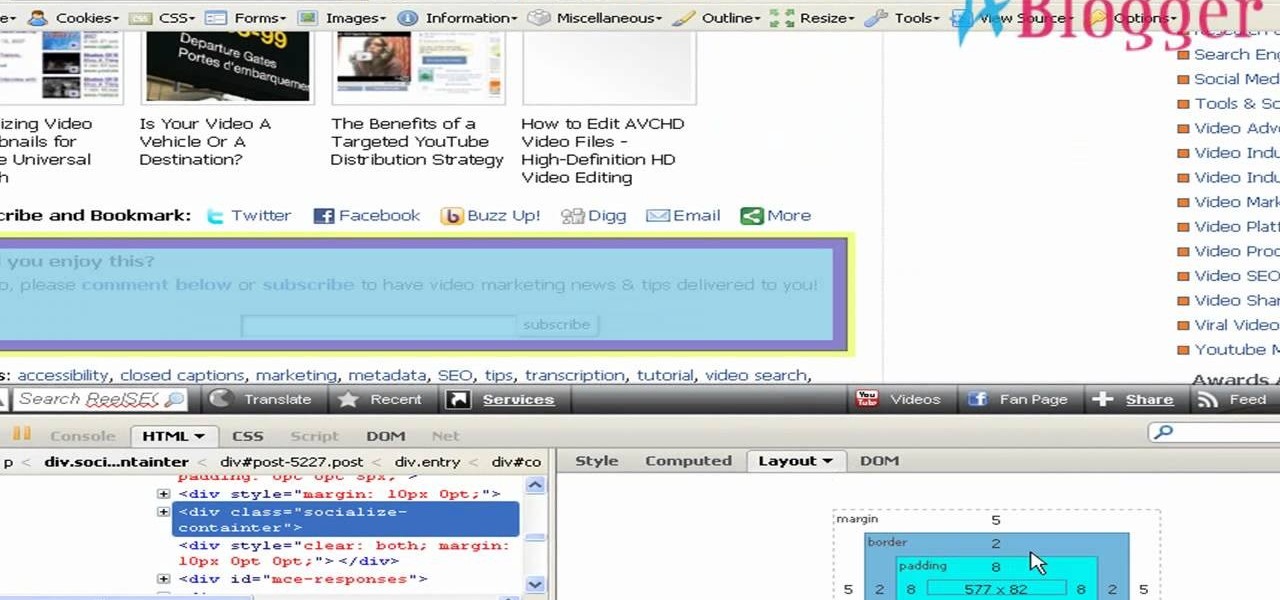
An easy way to view your CSS code of your website is through the Firefox plugin called Firebug. It's really helpful, especially if debugging your code. Just remember, you cannot save anything with Firebug, it's only for viewing code and adding codes for previewing webpages.

Big business is on the web these days and you don't have to build a shopping website or blog to get involved.