There are few things that make me smile more than ice cream… or bread! So why not combine them for double the happiness? We've discussed the art of making ice cream bread before, but not everyone has the time (or, let's face it—the patience) to bake bread in the oven, no matter how few ingredients the recipe may take.
To be twentysomething is an awkward time for entertaining. As we graduate college and begin to work in “the real world,” there is a yearning to transition from keg parties into dinner soirées. However, though the desire is there, often the bank account is not. Here are some ways to do in the kitchen what twentysomethings do best: fake it until you make it. (In other words, host a fabulous dinner party for four and still be able to make rent this month!)

In my opinion, there is nothing in the culinary world as satisfying as cutting into a steak, and seeing that you've cooked it to perfection. Even if you're one of those bizarre people that prefers their steak medium or well done (hey, no judgement... okay, fine, a little bit of judgement), it's culinary heaven when you realize that you achieved the perfect doneness on your steak.
When I was a little kid, I was obsessed with shells. And while most of my shell collection came from combing the beach for treasure, some of it came from a different source: dinner. Whenever my parents had fresh clams or mussels, I would take the leftover shells, soak them overnight in soapy water, and add them to my collection.

hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.
Make no bones about it—having an "undo" option is a freaking godsend. Whether you accidentally deleted an entire essay, screwed up the shading on a Photoshop job, or sent an email that wasn't quite ready, having the option to undo a click or button-press can definitely be a lifesaver.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

We've all been there: we're enjoying a nice cob of corn, happily covering our face in butter and salt, when suddenly we realize that there's a thread of corn silk stuck in our teeth. We try to dislodge it with our tongue; no luck. We pick around with our fingers; still no luck. That silk is staying there until you return home to your toothbrush and dental floss. And if you think that corn silk is bad for most people, try having braces!

I've always had an affinity for pretty wine bottles. When I was younger, my parents and my siblings would give me their empty wine bottles so I could collect them, and I loved every single one.

When I was in college, I invited a girl over for a date. It was a glorious spring day, and I thought it would be the perfect time to fire up the unused barbecue that had been sitting on my patio all school year. I prepped all the food, chilled all the beer, and then I realized I had no way of lighting the coals for the barbecue.

I'm a firm believer that a sandwich is the ultimate food. It's filling, but not heavy; it has carbs, protein, veggies, and sauces; and it's easily customizable. Add that all up and you've got the absolutely perfect lunch.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

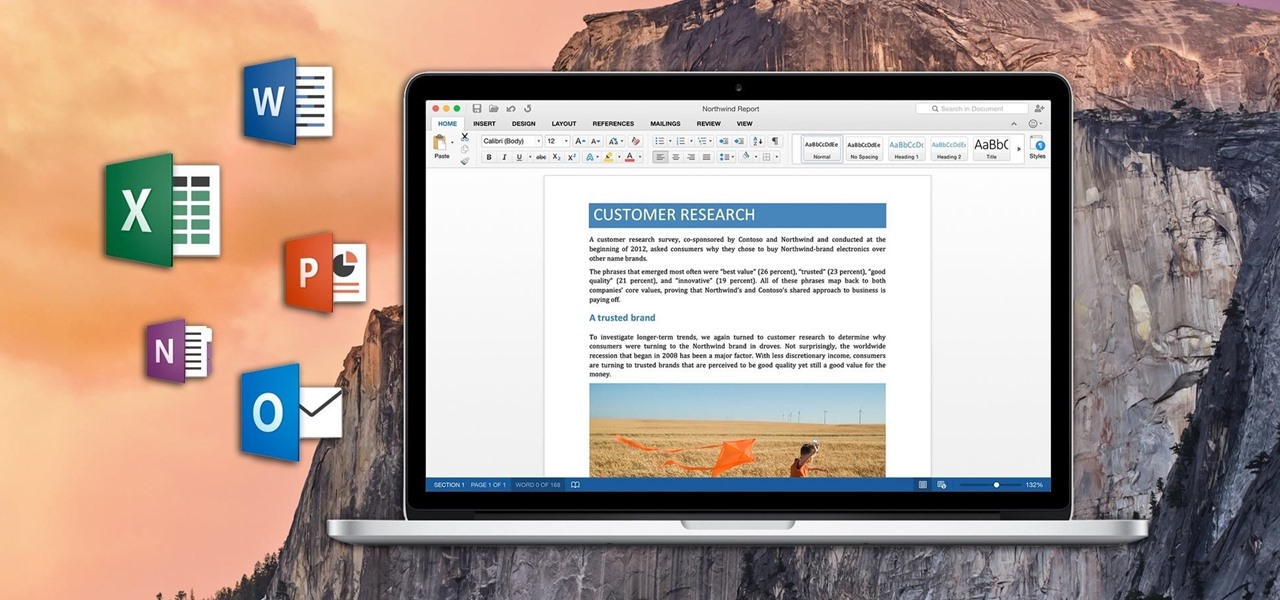
If you've ever attended school or held a job, you're probably well familiar with Microsoft Office, whether you used it or not. It's the most popular office suite available, and has been for some time. Apple does have its own suite of productivity apps (iWork), but Microsoft Office has always been the industry leader for word documents, spreadsheets, and presentations.

Cast-iron cookware breeds a strange kind of obsession. When I got my first pan, I spent untold hours seasoning, cooking, researching the best non-soap methods to use for cleaning, and re-seasoning that thing. Finally, I became exhausted by the whole process and realized that you can skip seasoning a cast-iron pan as long as you use it regularly and clean and oil it properly in-between uses.

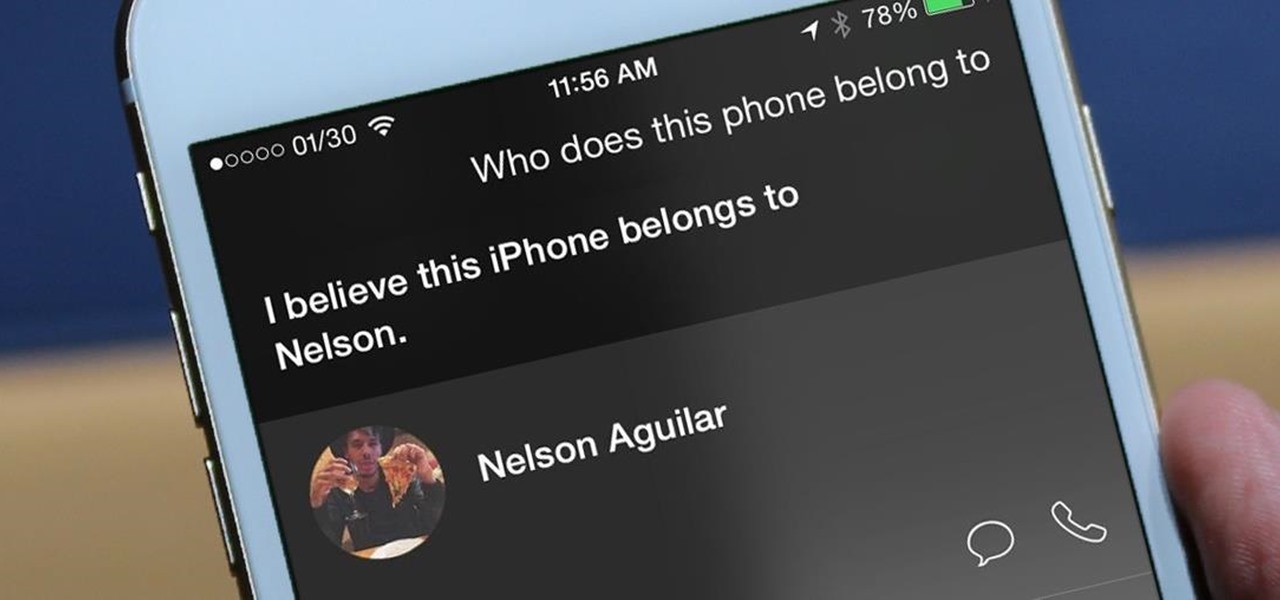
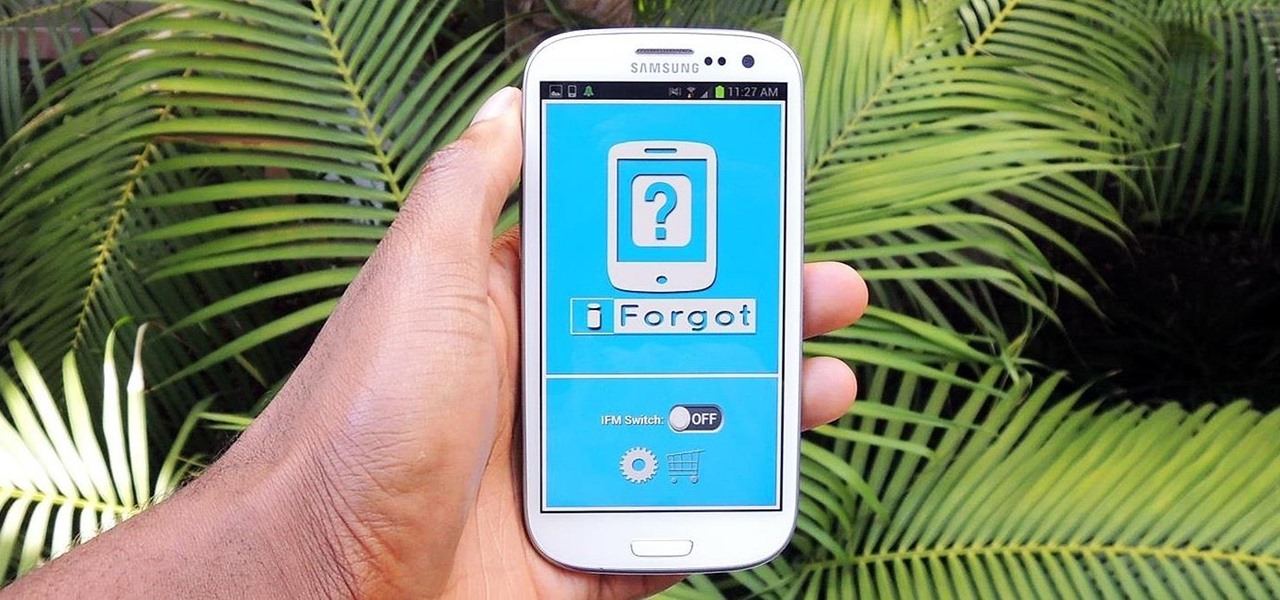
I misplaced my iPhone 6 just a few weeks ago, so I know firsthand that losing an iPhone sucks. Luckily, my tale didn't have a bad ending.

After utilizing Spotify's My Year in Music tool, I came to realize that I listened to over 30,000 minutes of music in 2014. Most of that was played while working from my Mac using the desktop version of the service.

Garlic: almost every cuisine in the world considers it a staple, and for good reason. Its pungent flavor gives depth and character to food. Dishes made without it seem bland and forgettable. And on top of all that, it's been studied for its potential anti-cancer properties (and don't forget: it's been mythologized for warding off vampires).

Whenever a new Android device is realized, the first thing I figure out how to do is to get it root access. Generally speaking, rooting has never been easier, with many one-touch methods like Stump and Towelroot available. But as manufacturers and carriers increase security with each new product, there is one tried-and-true root method that continues to work on most Samsung devices—Chainfire's CF Auto Root.

So, you're scanning the internet for some cool articles to read during your lunch break and you come across something pretty interesting—"The 50 Most Incredible Things Every Person with a Brain Should Know." That sounds interesting, so you click, and boom, you are hit with the utterly obnoxious Page 1 of 50. Really?

If you are having problems playing your sweep picking arpeggios fast and clean then you are not alone. Many guitarists have the same problem. I suffered from the same problem, years ago. In fact, playing sweep picking arpeggios with poor technique is one of the most common problems that I encounter with my guitar students. After helping them overcome these challenges I have discovered 2 different approaches to improving your sweep picking technique. The first will keep you frustrated with bad...

Naps provide some serious mental and physical benefits, but not if they last too long or occur too late in the day. Ideally, you want to awake from a nap feeling alert and refreshed enough to attack the rest of your tasks with renewed zeal, but not energized to the point where you can't get to sleep at night. Alas, most of us don't know these tricks and end up messing with our sleep cycle (guilty).

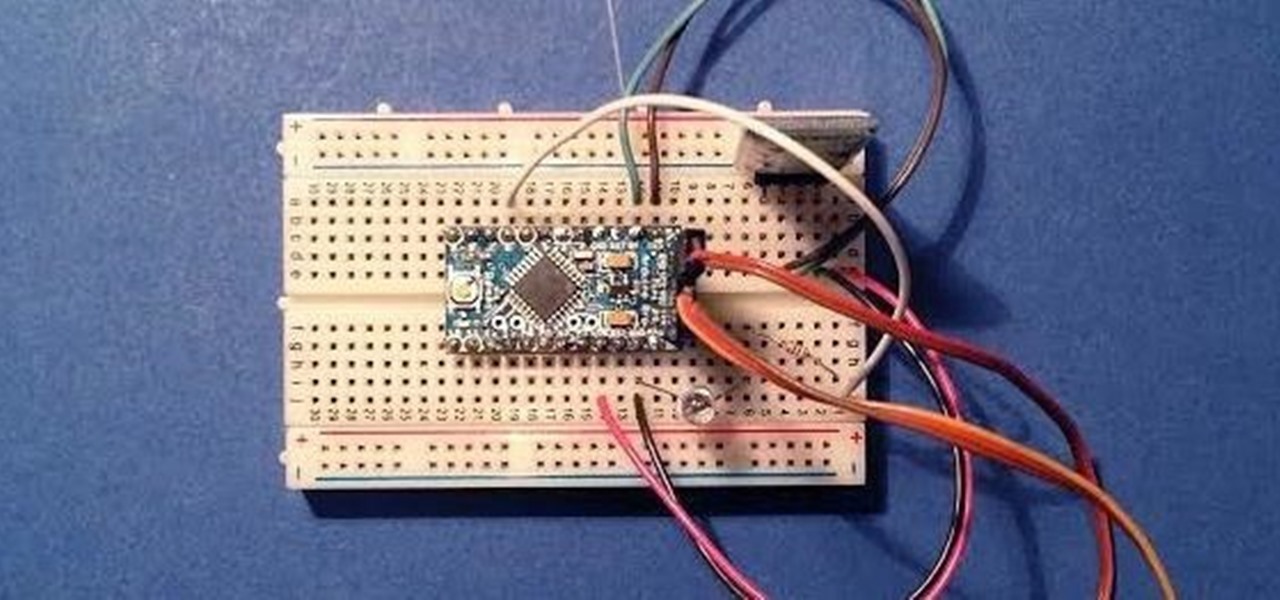
Since its creation, Arduino has been growing exponentially more popular as DIY enthusiasts and Makers alike realize its potential. As new versions of the device are released, many easy-to-use peripherals are showing up on the market also.

Many game developers have finally realized that in order for their games to be successful, they have to support Android. To really win Android users over, they should also accommodate us hardcore gamers who have OTG cables with the ability to hook up controllers to our devices.

Over the course of covering the Nexus 5 for the last 6 months, I've come to realize that almost every hack out there will work for this device. I also cover the Galaxy S5, and let me tell you—hardly any of the cool mods I come across work for that phone. In this regard, we are downright spoiled as Nexus owners.

As the largest wireless service providers in the United States, AT&T and Verizon Wireless carry some serious clout. Sadly, they use some of this power to heavily modify the Android phones that they offer.

Ginger root is one of the most underappreciated and versatile spices around. It's simultaneously hot, sweet, and piquant. It's also a pain in the tush to peel, thanks to its thin, fragile skin and the thick, knotty rhizome that contains all the flavor.

Not too long after getting a new device, you probably start installing any and all apps that seem fun and interesting. But after having used the device for a considerable period of time, those extraneous apps begin to take their toll.

In early-2014, Facebook had the brilliant idea of auto-playing all of those annoying videos in your news feed that you never wanted to see in the first place. Fortunately, they realized their mistake and have provided a way to disable auto-play, which means you can now get rid of some of those plugin-blocking browser settings you have enabled.

It's a modern day nightmare to accidentally reveal too much information on Facebook. I've inadvertently told the world my location more times than I can laugh off, and my friends haven't fared too well either. Just take a look at the requested app permissions next time you're about to click install and you'll quickly realize how much that app can reveal about you.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"

As I've said before, slowing down is not an option for me. At one point, I realized that there were plenty of files on my Mac that I didn't need any more, but too many to delete individually. In other cases, your Mac can be experiencing some major malfunctions: constant crashing, locked controls, slow boot times, missing files, etc.

While their merger with Microsoft has lead to a seemingly complete halt of new device development, some Nokia employees are still hard at work to bring new software to the table.

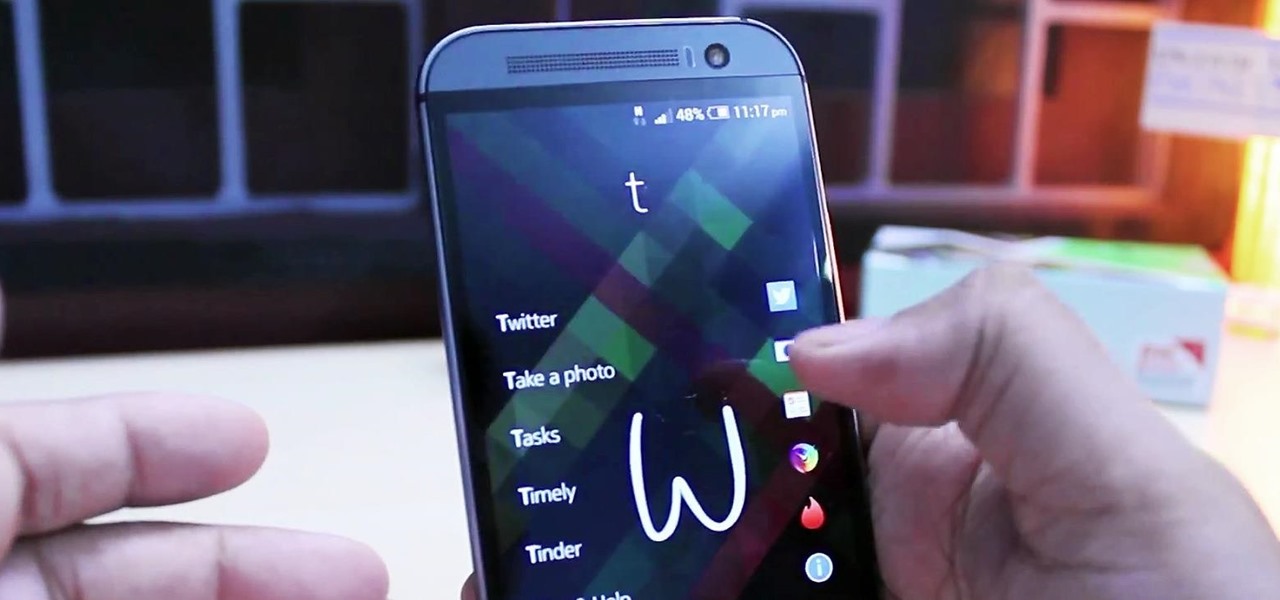
One of the most frustrating things about full touchscreen phones, especially for those coming from one with a physical keyboard, is typing and editing text. Whether it's a quick text message, or Swyping out a full e-mail, it sucks realizing you've messed up a few words and have to go back and fix them.

Whether it's because you want to make a quick tutorial video or want to show off your gameplay skills, recording the screen your Nexus 7 tablet isn't an easy feat. At least, until now. Hidden inside Android 4.4 KitKat is a built-in screen capturing feature, but it takes a little effort to dig it out.

There are some calls you really don't want to miss. Whether it's "I'm going into labor" or "We have some questions about your résumé," not being able to answer or respond to certain messages can cause some serious problems.

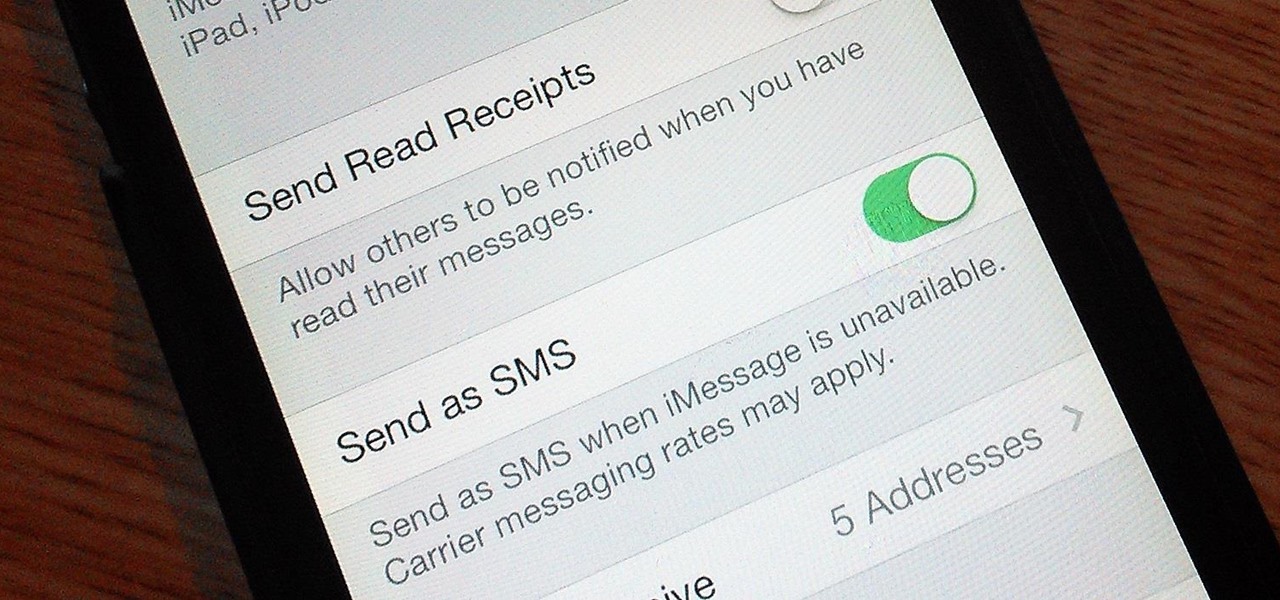
If you're an iPhone user, iMessage is great for cutting down on SMS costs from your carrier, but it doesn't always work right away.

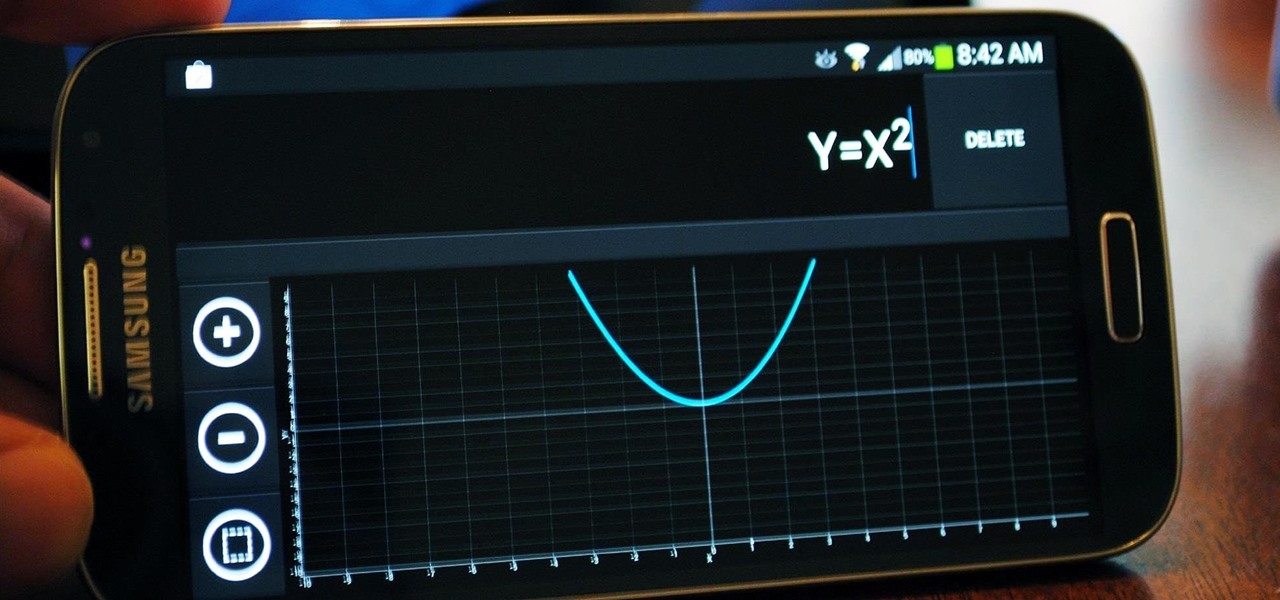
It's that time of the year again when scores of students are flocking to stores for school supplies. Pens, pencils, books, and for math students, calculators.

Privacy has been a heated topic in recent months, with everyone now up in arms over unauthorized leaks and exposures. And guess what—tablet and smartphone users are just as vulnerable.

"Ahoy-hoy." If telephone titan Alexander Graham Bell had his way, we'd all be answering phones like Mr. Burns. Thankfully, frienemy Thomas Edison had enough sense to realize we weren't always on the briny. He preferred "hello" as our standard telephone greeting, which he is credited with coining in 1877. Fellow American pioneer Davy Crockett actually used it as a greeting first in 1833 (as compared to an exclamation)—but in print, not over the phone.

I spend practically all day surfing the web and writing on my laptop, and just as much time texting and checking emails on my smartphone. So, it's only natural for me to charge my iPhone using the USB port on my MacBook Pro.