Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.
Android comprises an entire ecosystem of apps, games, functions, and features, so it would only make sense that it has its own lexicon. Words, phrases, and acronyms that didn't exist ten years ago are now used in an off-the-cuff style by developers and support technicians across the web.

Computer crashes, fried hard drives, red rings of death, delinquent memory cards... nothing is worse than dysfunctional technology. In just a minute, your favorite and most used device has become the biggest headache of your life, frustrating you to the brink of madness. But what's worse than your electronics just giving up on you?

You've had a massive hard disk failure.. ...in your PC or laptop and like a large number of people who think it will never happen to them...you did not have a backup of those 2000+ family pictures, those hundred of important Word documents, those family videos that you downloaded from the camera then erased from the cameras disk...the inevitable "I'm Screwed!'

Move over NASA— SpaceX is taking over. Well, not really. But today, the privately funded spacecraft company broke all expectations when their Dragon capsule fell to a soft landing in the Pacific Ocean, completing an undoubtedly successful demo flight of nearly two full trips around Earth. It was the first re-entry of a commercial spacecraft ever, bringing commercial space transportation closer to reality.

Truecrypt 5.0 adds many new features, most importantly Windows system partition encryption. To put it in slightly inaccurate layman's terms, this means encrypting your entire C: drive. Even if you already write your sensitive data to an encrypted space, files are sometimes squirreled away in unencrypted temp space or in the page file where they may be recovered. Using Truecrypt to encrypt your Windows XP system partition will help eliminate this problem.

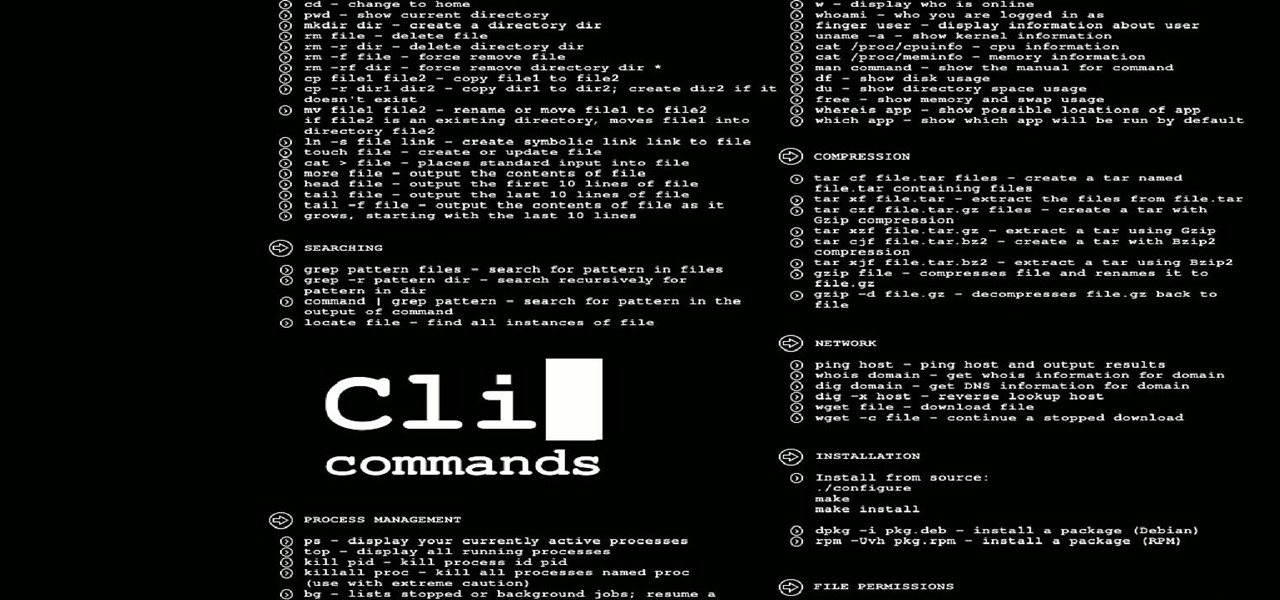
Hello everyone on null byte this is my first tutorial This Tutorial Is on Useful Lesser Known Commands on Linux

Permanently deleting files is something that a lot of people aren't aware of. Actually, most people think that once a file is deleted, it is gone forever. This is not the case. Hard drives write to the disk via magnetic charges, positive and negative correlate to 1s and 0s for binary. This is then interpreted into information for the computer to use and access.

We've only just now, a week later, recovered from our amazing trip to Austin TX! Thanks, Harry! Butt-Numb-A-Thon was an absolute blast...

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

About two months ago, the massive Gawker Media hack was a wake up call for many web denizens on the importance of proper password security. Data analyzed by the Wall Street Journal revealed the three most popular passwords recovered from the hack were downright idiotic—123456, password, and 12345678. If past events weren't motivation enough for crafting a strong password, then maybe a racy 8-bit stripper is. Naked Password is a jQuery plugin by Platform45 that rewards you with an accelerating...

This Guy Has My MacBook is a gripping tale for iOS nerds far and wide, documented via interaction designer Joshua Kaufman's tumblr. When Kaufman's MacBook was stolen from his apartment in Oakland, CA, on March 21, 2011, he quickly activated Hidden, a previously installed app that enabled Kaufman to collect photos of the thief, as well as screen shots of the computer in use.

Who dunnit? Forensic pathology is an art form we take for granted. Scientists are busy debating why a 5' 5", 5300-year-old man coined Otzi was murdered.

File recovery on Linux is a bit different than Windows. It requires different software than the Windows counterparts because every OS has their own file system. Windows uses NTFS, or FAT file systems, while on the other hand, Linux uses ext-based file systems. I personally use ext4 file system because it's the latest and greatest ext-journaling system and supports a large level of directory recursion and file sizes, but most installations still use ext2 or ext3. When files are deleted from a ...

Playing Super Mario Brothers for the NES is the first thing I can ever remember doing, at age 3 sitting on the carpet at my grandparents' house. It was a special game for an entire generation, including British youths Andrej and Adam Zamoyski. It inspired them to eventually become video game testers and designers themselves; Andrej at Lionhead Studios and Adam at Headstrong Games, and then Zynga Mobile UK (until recently called Wonderland Software, developers of Godfinger for the iPhone).

They've been at it for a few years now, but the crazy group of amateur rocket scientists who call themselves Copenhagen Suborbitals have triumphed over adversity, successfully launching their DIY rocket nearly 2 miles into the sky last Friday. The privately funded, non-profit aims to one day send human beings into suborbital space on the cheap, without the need of government budgets and administration.

Whether you're upgrading to the Windows 10 Insider Preview or the official build of the operating system, you'll notice a significant hit on hard drive space—up to 20 GB taken away from you. For those with older or even solid-state hard drives (SSDs), this can be a substantial hit.

More password cracking action from Null Byte! Today we aren't going to be cracking passwords per se, rather, we are going to learn the basics of generating rainbow tables and how to use them. First, let's go over how passwords are stored and recovered.

Posted with permission via HereComeTheYanks.com Have you recovered from that heart attack inducing, hell of a game?? I am still riding high and, as such, may ramble a bit on here. But stay with me...I'm a die-hard fan!! What else do you expect??

Hey now! Brazil, Paraguay, Chile, Argentina and Uruguay are doing very well in their respective groups. The are all expected to qualify to the final 16. In fact, they are doing better than any other continent. Europe's top flight teams are disappointing, as are the host African nations.

The dreaded moment you hope never happens—someone has stolen your laptop. You could have private information, pictures, or even private information belonging to the company you work for, all lost forever. It can cause you pain, money, or even a job.

Do you need to email your wife your Social Security number? Send confidential business plans to your partner in Thailand? Send your hacker buddies the recovered hashes from last night's breach? Try using GPG, a valuable and easy to use open-source encryption program.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

The Jackass crew are now jewelers. In this idea, you would have to get 8 jewels or stones or medallions, gumball size, and a very thick gaudy gold chain. The chain would be divided into 8 parts and cut. All at once, the Jackass guys would each swallow the jewel and their segment of the chain. In a day or so, or sooner with the help of laxatives, each guy would poop out the stone and the piece of the chain. As soon as all of the parts and pieces have been recovered from each guys poop, the cha...