In the dojo, what ISN’T said is often as important as what IS said. To most of us who’ve been raised in the USA, the reticence we encounter in the dojo can be off-putting. American society is very “content” oriented. Our legal contracts, for instance, run for pages and pages. Everything needs to be spelled out. In “context-oriented” societies there is far less reliance on such a literal approach. Much more importance is placed on the relationship between the two parties entering into an agree...

HTC is developing the latest Nexus phones for Google, according to a recent tweet from Evan Blass, a well-known phone leaker. Blass reported that the new Nexus phones will run Android N, and are being referred to as the M1 and S1. Android Police backed up Blass's tweet and added that a source told them the new handsets will be named "Marlin" and "Sailfish."
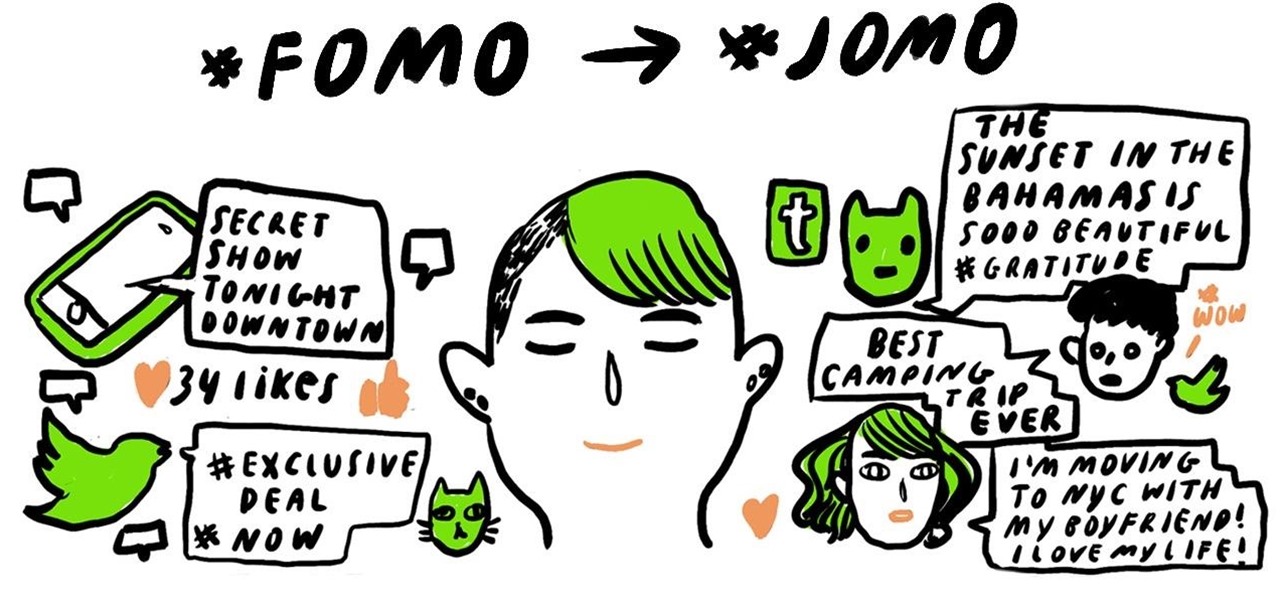
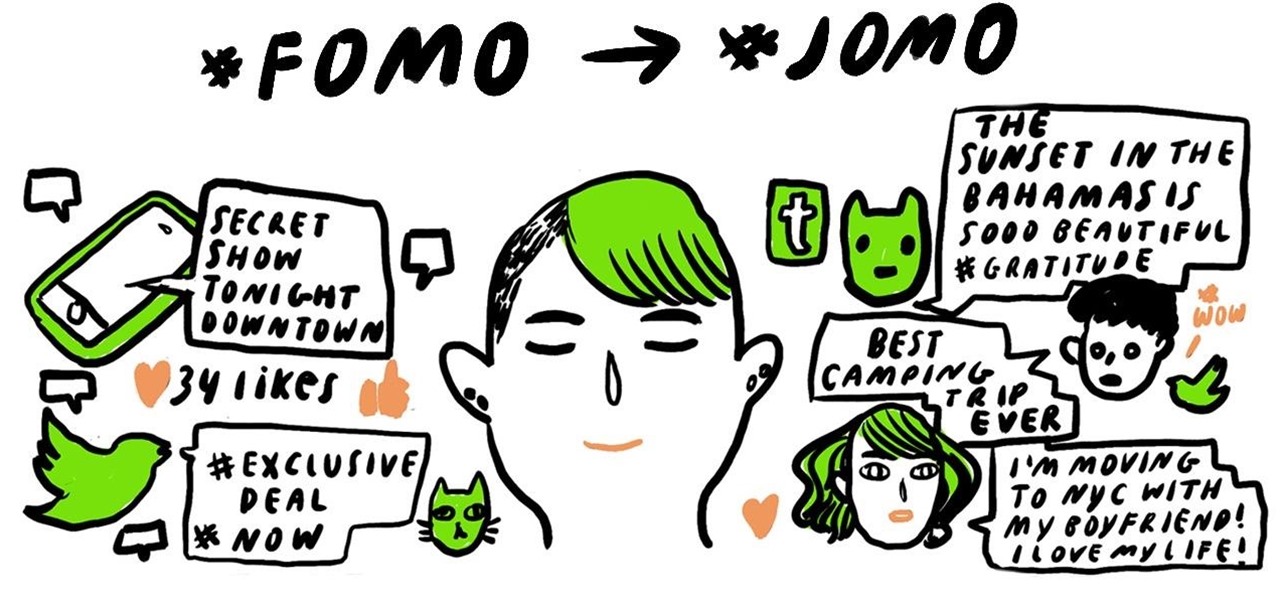
Do you experience a pang of envy when you scroll through your Facebook news feed, Instagram home, or Twitter timeline and see all your friends doing super-awesome things that you weren't a part of? If you are like most people, then the answer is probably yes.

In 1859, 22-year-old chemist Robert A. Chesebrough accidentally discovered petroleum jelly when he visited a working oil well in Titusville, Pennsylvania. Oil workers complained of a gooey substance referred to as "rod wax" which kept getting into the machinery and slowing them down. Chesebrough noticed that oil workers also smeared this same substance on their burn marks or dry skin to help speed the healing process.

Do you have an excess of empty yogurt containers? Do you also happen to have a green thumb? Put two and two together to make a DIY self-irrigating planter for your next tomato plant, herb garden or whatever green growing thing suits your fancy.

You know that tingly spidey feeling you sometimes get urging you to make a crazy career change or warning you against trusting a smooth-talker with your money? Commonly referred to as your gut instinct, intuition or sixth sense, your ability to subconsciously know something or suspect something beyond the realm of conscious reasoning can help you in all aspects of your life, from interpersonal relationships to big life decisions.

With Facebook and Twitter dominating the world, playing chess opposite a real, touchable person is no longer necessary. With the ChessBot, you can now play on a real chessboard remotely - the next best thing to in-person play.

Pen Spinning lives in a similar world of the unassuming arts of Cup Stacking and Dice Stacking. All three performing arts truly require a great deal of practice and skill.

NK5 is a genuine wizard with an old monitor. He's hacked together everything from an electric kitty fence to a Halloween hologram using the guts of an old CRT.

Check out this lesson in KhoeKhoegowab, the Namibian language commonly referred to as Click

Last time, we looked at archaic cryptography, so you should have a basic understanding of some of the concepts and terminology you'll need. Now, we'll discuss one of the most important advances in computer security in the 20th century—public key cryptography.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

GRAMARYE n pl. -S occult learning; magic 64 points (14 points without the bingo)

CREMAINS n/pl the ashes of a cremated body 62 points (12 points without the bingo)

XSS stands for cross-site scripting, which is a form of web-based exploitation that uses client-side vulnerabilities in a web page to execute malicious JavaScript codes. JavaScript is referred to as "cross-site" because it usually involves an external website containing the malicious code. That code is most commonly used to steal cookies with a website that the attacker created and hosted on another server. The cookies can then be used to escalate privileges and gain root access to someone's ...

Bingo! No, this isn't the game where balls fly around in machines and players dab their cards with daubers. In a game of Scrabble, bingo refers to the bonus a player receives when emptying their rack in one turn, which gets them an extra 50 points on top of whatever their play was. Even if you had two blanks on your rack and didn't utilize any premium squares on the board, you'd still have an impressive 56-point turn (at least) by using all 7 of your letters.

Oktoberfest is the world's largest annual beer festival located in Munich, Germany! The festival starts in late September and lasts until early October -approx 16-18 days. Oktoberfest is an important part of the Bavarian Culture and has been going on for over 200 years. Each year the festival is held in an area called Theresienwiese, but often referred to as Wiesen for short. Wisen is located near the center of Munich. Oktoberfest is held as one of the world's largest fairs with over 5 millio...

Japanese people are into many things Americans find weird—like YouTube's beloved canine-hosted cooking show or Daito Manabe's light up LED grills or even more insane, a vending machine that distributes live crabs. In light of these cultural oddities, the Japanese phenomenon of visual novels (NVL, or bijuaru noberu), seems relatively normal. A meeting place of books and video games, visual novels are a sort of "Choose-Your-Own-Adventure" for the new generation.

In the wake of the recent tragedy in Japan, Southern Californians have been hyper alert to any news regarding dangerous levels of nuclear radiation drifting over from Fukushima. At this time, official statements from the California Department of Public Health and the EPA are assuaging the population that there is nothing to fear. While there has been some detection of radiation in the air, the current levels recorded are "thousands of times below any conservative level of concern". But despit...

How is it possible that Iron Man is not yet a reality? DVICE reports that super-powered exoskeletons are indeed within our grasp (if not quite as flashy as Hollywood SFX just yet). Real life exoskeletons fall into the realm of not-too-distant futuristic warfare.

Professionally and academically speaking, I am a computer scientist, but I also enjoy lock picking as a hobby, so I thought I would share what knowledge I have with this. Before we start doing anything, first we need to understand the fundamentals of how locks work and then acquire and familiarize ourselves with basic lock-picking tools.

Yes, you read the title correctly. GameStop has problems, and if you're lax in morals, you can take advantage of them for free games and cash. I'm bringing you all yet another exclusive Null Byte that falls into the fascinating category of life hacking.

Since its release three years ago, Canon's EOS 5D Mark II has been the most sought out digital SLR for photographers everywhere. But it's also becoming a favorite amongst cinematographers, thanks to its compact size and high-def video recording mode, seeing action in everything from independent features to Hollywood blockbusters and even big network TV shows.

People ask me all the time, "Nick, what are the best blinds for my home in terms of Wood vs. Faux Wood?" Well the answer to that question is not so cut and dry. However, I can help steer you in the right direction. In this post, we will examine the pros and cons of both wood and faux wood blinds to help you make your decision.

It was brought up a while back in a Community Call to Arms that *math* is handy for encryption (and let's face it, everything) so let us go over things you just have to know. "In its simplest meaning in mathematics and logic, an operation is an action or procedure which produces a new value from one or more input values."[source]

WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most popular communities. Users can join and participate in any World they're interested in, as well as start their own community.

Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying various SQL injection vectors over and over. This is especially so if they are using an automated framework like sqlmap that can spam a ton of requests in a short time. More often than not, the access logs are what most amate...

Introduction The 3 major anonymity networks on the Internet are Tor/Onionland, I2P and Freenet. If you feel confused on which one is the "best" one to use the answer is simple. Use all three!

Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and root boxes, you'll need to learn how to perform the necessary reconnaissance first. In fact, you will spend far more time researching your target then you will exploiting it. In this article, I am going to show you the fi...

Spam is everywhere and Facebook is no exception. In fact, spammers are constantly stepping up their game by tricking unsuspecting Facebook users to participate in quizzes, games, apps, or "new features" that are actually dangerous computer viruses, spyware, or other trojan horses in disguise. Their attempts even trick people into unknowingly becoming spammers themselves.

Gaming with augmented reality just keeps getting cooler and cooler.

A new model of Google Glass has appeared on the FCC website, along with a handful of high-res pictures.

Many people get so discouraged by their failures with redstone that they give up using it entirely, or never progress beyond using simple switches. However, by incorporating logic gates into your redstone designs, the applications are nearly limitless. The ability to add multiple switches to your machines is just a small part of what logic gates can do. Most importantly, they give you control.

Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use your network as a spring board for who knows what. When the police come a few days after, they are coming to your door—and not to talk about how nice your lawn is. Don't be that guy.

Anna The Red is the greatest Bento artist I have come across on the web. She's so highly regarded she even did an ad for Google. Check it out: For those of you who don't know, Bento is a "single-portion takeout or home-packed meal common in Japanese cuisine". When bento is arranged in an elaborate style (such as people, animals, characters, plants, etc.) it is referred to as kyaraben or charaben (a shortened version of character bento).

tell if she is a hooker or a cop. His arrogance too great. Above the law. Not even this tutorial would have slowed him.

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

The holiday season is here, and if you didn't already pick up a SCRABBLE set during Black Friday or Cyber Monday, then you still have time to buy the perfect gift for your lexical-minded friend. There's sure to be deals out there over the next couple of weeks, you just need to browse the web and search store shelves for the best deal.