In the US, law enforcement officials can make you unlock your smartphone with a fingerprint, but they can't force you to input a password or PIN, which would violate your Fifth Amendment rights. To help you from ever being in a scenario where you're forced to put your finger on the Touch ID sensor, Apple has a built-in way for you to disable biometrics on your locked or unlocked iPhone in mere seconds.

Super Mario Run was released for iOS on December 15, 2016. Even though it debuted as a "free" app, almost all of the playable content was hidden behind a ridiculous $10 unlocking package. Despite coming with such a hefty price tag and receiving a two-star rating on the day of its release for iOS, Android users are still very much interested in giving this game a whirl.

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

Not to be outdone by the announcements of Mac OS X El Capitan and iOS 9, the Apple Watch is also getting a much needed software update. Some of the notable new features we can look forward to on watchOS 2 are Nightstand mode, additional screens for friends, email replies, and other improvements we probably should have already had.

If you keep sensitive data on your phone, you've surely considered a "lockout" app before. There are many such apps that can add an extra layer of security to other apps within Android. For instance, you can require a PIN or password before anyone is able to launch a particular app.

Welcome back, my fledgling hackers! With this first article, I am initiating a new series intended to convey to my readers the skills necessary to develop your own exploits.

Apple released the first developer beta for iOS 13.5.5 on Monday, June 1. The update comes on the same day Apple released iOS 13.5.1 to the public, which patched the unc0ver jailbreak, and 12 days after iOS 13.5, which introduced COVID-19 exposure notifications, in addition to other new features.

There's nothing quite as exciting in the beta testing world as a new update. Battling overloaded servers to download the latest update as fast as possible, just to scour through the new OS looking for the biggest features to the smallest changes. It was only Thursday that Apple seeded iOS 13.2 developer beta 2, so count us surprised that we get to experience today's release of developer beta 3 so soon.

You just brought a brand new Pixel 3 from the Google Store, and you insert your SIM card only to find the phone won't recognize it at all. No matter what you do, the SIM card won't register and your Pixel won't connect to your carrier network. That's what happened to me and several other Pixel 3 owners. The good news is a fix is coming, the bad news is Google doesn't have a date for that fix.

The updates just keep on coming. Apple released the third beta for iOS 12 to public testers Wednesday, July 18, just after seeding the fourth iOS 12 developer beta to registered developers the previous day. This update comes thirteen days after the release of the second public beta, which itself came hot on the heels of the third developer beta.

Ever since JamCity dropped the first trailer for Harry Potter: Hogwarts Mystery, fans have been eager to get their hands on the game. What Harry Potter fanatic wouldn't want to live out their own Hogwarts adventure on their iPhone or Android device? Well, we now know when the game is officially coming, as well as who will step into the shoes of our favorite, iconic Potter characters.

Now that we have our payload hosted on our VPS, as well as Metasploit installed, we can begin developing the webpage which will trick our "John Smith" target into opening our malicious file. Once he has, we can take over his computer.

If you need a little inspiration for tonight's Halloween festivities, this augmented reality magazine cover featuring the Dark Knight himself, Batman, may do the trick.

While other devices are moving away from fingerprint scanners (cough, iPhone X), for many, a fingerprint scanner provides the best balance between security and speed. Typically, the rear fingerprint scanner on the LG V30 is quick and accurate, but every so often the phone will not recognize a registered fingerprint.

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...

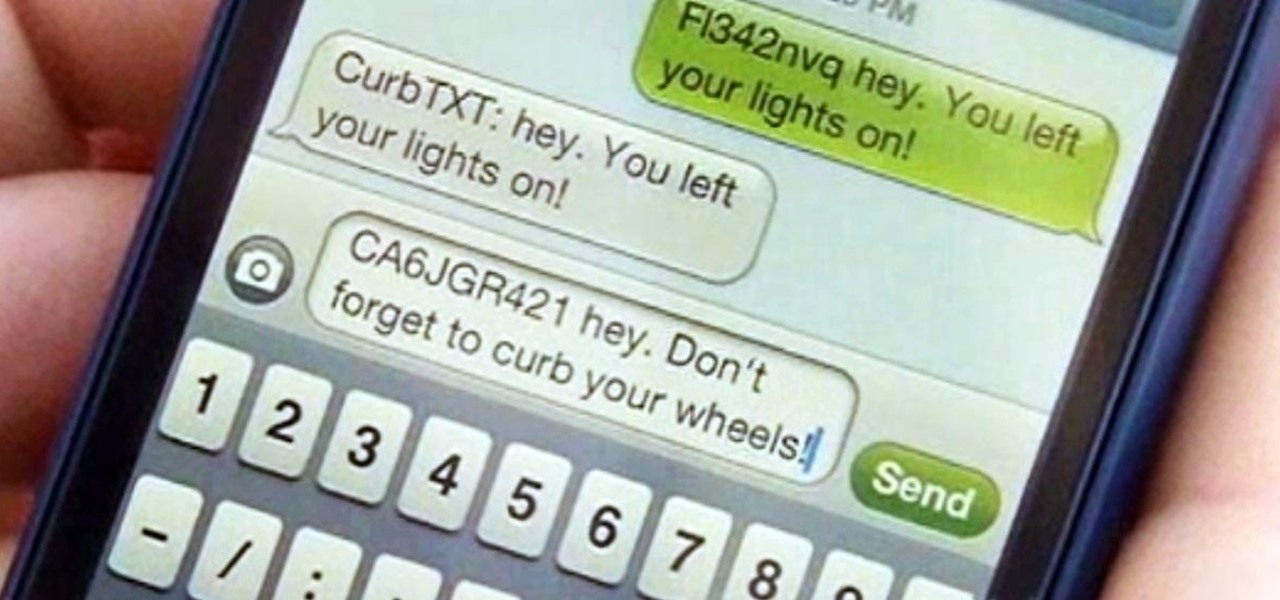
With GPS chips and Wi-Fi positioning systems, a modern smartphone is capable of tracking its user's location with pinpoint accuracy. This being the case, it's strange that the most common text message sent today is still "Where are you?"

Washington State has a history of large earthquakes, as does California. More than 1,000 earthquakes are registered in Washington State each year. More than 10,000 are recorded in California each year. In an earthquake, non-structural elements, which is anything that does not actually hold the building up, may become unhooked, dislodged, thrown about, and tipped over. this can cause extensive damage, interruption of operation, injury and even death.

Tor is an excellent obfuscation network for web traffic, and while instant messaging over the network is very useful, it can be relatively difficult to configure. In this guide, we'll look at two synchronous communications platforms (instant messengers) which can be routed over the Tor network, Ricochet and XMPP.

To test how fast your internet speed is an intermediate level skill. Start by picking an internet speed test. You can use Google or another search engine to find one. A service that is recommended in the video is DSLreports. This site does not require you to know a lot of information about your service. To test your speed start by picking a city that is near to you. Then shut down all tabs and every application that you have running. It's important to do this on every computer on your home ne...

Part of the process is to create plans to follow when making the cabinet for the arcade game. when cutting the wood you need to allow for the 1/8th of an inch that the band saw will be cutting. You will also need a piece of plexi glass to give the game an authentic feel, spray paint the piece of plexi. You will also need joysticks and buttons, which you can get at happcontrol.com. You need to cut a square hole in the plexi so that the buttons can be mounted in it. To integrate the buttons you...

Whether you're at a bar or just with a group of friends, this is a great illusion that makes it look as though you are sending a large object right through a table!

Country Story hacks, cheats, glitches. How to hack Country Story. Watch this video tutorial to learn how to cheat Country Story: dog hack (09/26/09).

Why make a flip book? Because all animation – even stick-figure Flash animation and multilayered, highly technical 3-D effects – is built on, and can benefit from, the basics of the craft first developed by artists working at the beginning of the last century. And while fancy computer programs are nice, you can teach yourself these basics using nothing more than a pad of paper and a pen, and replay them over and over without any extra technology needed.

You've written the great American novel, and you want to make sure that your story stays yours. Register your copyright and preserve your intellectual rights. In this video, learn how to copyright produced material.

While Apple has moved on from Touch ID to Face ID in newer iPhone models, there are still plenty of iPhones with fingerprint sensors — in fact, Apple's second-generation iPhone SE is the first new Touch ID iPhone in three years. With Touch ID, you can register up to five fingerprints, but it doesn't stop there. Using a little-known trick, you can sneak another five fingerprints in there for a total of ten.

Not all threats to our privacy come from hackers thousands of miles away. Often, we just want to keep our data safe from those around us, who may snoop in our phones or demand we reveal our secrets. That's where BlackBerry Locker comes in.

Last week, augmented reality startup Proxy42 released Father.IO, a multiplayer game that turns any indoor or outdoor space into a laser tag arena.

Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

In the digital age, maintaining your privacy is a never-ending battle. All sorts of companies and agencies have access to your data, and quite a few can eavesdrop on almost every method of modern communication.

Apple just showed off iOS 9 and its new features at WWDC 2015, including multitasking support for iPads (finally!), a new Low Power Mode to save battery, local area search and transit directions in Maps, a highly improved "Proactive" Siri, a better Spotlight search, new apps, and so much more.

The wait is over. The Samsung Galaxy S6, arguably the best Android phone of this year, has just launched. There was already a lot of hype about this super phone—its looks, its specifications, and its other functions have been under the microscope for quite some time. It will not be a good idea that you take this phone in your hand and use it in the same fashion as you have been using your other phones in the past.

Apple just unveiled iOS 8 at the Worldwide Developer's Conference, and it has a lot of exciting features to play around with. Unfortunately, it won't be available to the public until this coming fall—but that doesn't mean you can't get it right now.

Hey, coffee drinkers—your morning cup of joe is killing your metabolism.

Parking. Ugh. Parking is about as fun as running through a swarm of bees while being chased by a pack of wolves from The Grey.

This video tells us the method to prepare a gourmet beef stroganoff. Take 3/4lb sirloin steak tip. Cover it with 1 teaspoon of soya sauce. Cover it and put in the refrigerator for 15 to 20 minutes. Take 1/2 teaspoon of mustard, 1 teaspoon of sugar and 1/4 teaspoon of black pepper. After this, heat 1/2 teaspoon of salad oil and let it smoke at medium high. Brown both sides of the meat. Take out the meat when the internal temperature registers 125 10 130 degrees fahrenheit. Add 1/2 lb mushrooms...

This video tutorial from gogeeks shows how to install mIRC application on Mac OS X operating system.

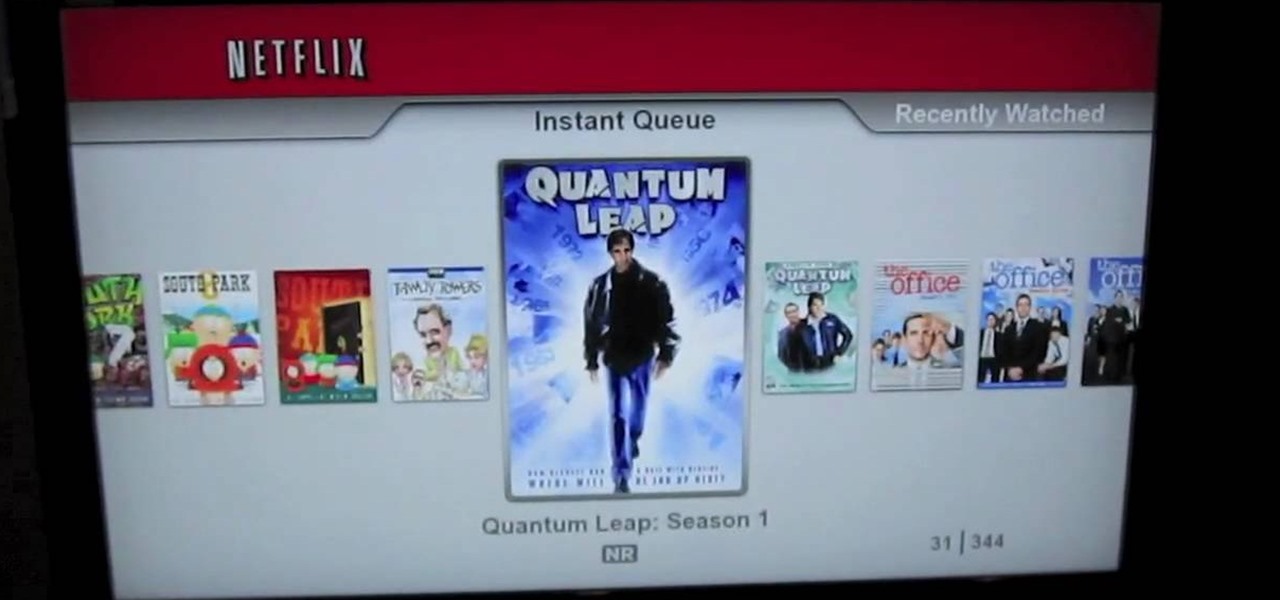
In this video Dynamite Jack from Hugegamer shows you how to get the most out of your Playstation 3 by setting it up to instantly stream movies and video from Netflix. Start by ordering your free Netflix streaming disc, from Netflix, once you receive the disk load it into your PS3 and start your system. You will also receive an activation code so that you can go online to register your PS3 with your Netflix account. Once your PS3 is booted go to the "video" section on your PS3 and bring up the...

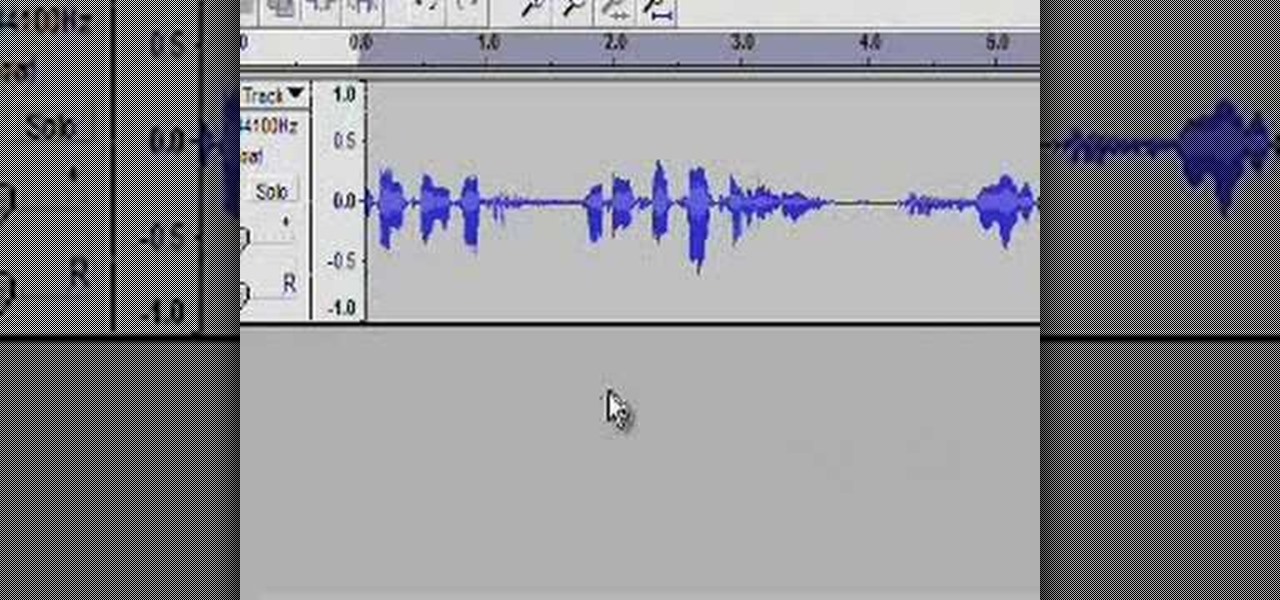
RabbidHedgeHog shows viewers how to easily make a podcast. This features how to make the podcast with the program Audacity. First open your internet browser and go to Audacity. Scroll down to download Audacity 1. 2. 6, save the file, Install and download the program. Now, open up Audacity which is basically a recorder. Connect your microphone which will allow you to record. Click edit, preference, find microphone and select the device you will use. Now, record your podcast by clicking the red...

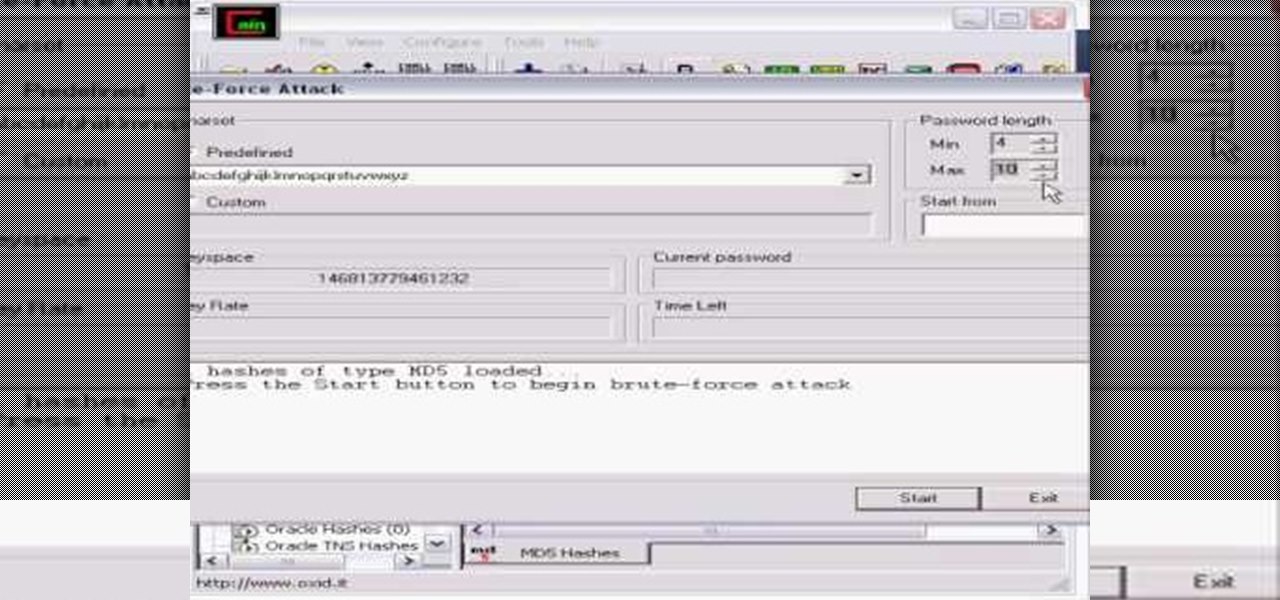
Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

Set the packaged roast on the kitchen counter. Let the roast warm to room temperature for an hour or more. This helps it to cook evenly.