I rarely receive spam mail, but every now and then I’ll get an email from Cat Fancy Magazine. I’ve never read an issue of Cat Fancy Magazine or been to their website. Actually, I’m allergic to cats. So how did they manage to get my information?

The procedure involves downloading a program called "hand brake". Hand brake is free to download. You can find it by searching for "hand brake" on Google. The direct website is Handbrake. You have to install this program on your computer. You must also download a program called DVD43. That program can be found the same way as hand brake, by using Google. DVD43 is also a free program to download. You use the DVD43 program to by pass copy protection on a DVD. You can use hand brake to change th...

Dying leather is a great option to revamp or change the look of an existing leather piece. Choose a dye that provides the qualities you are looking for, be it flexibility or depth of color. The possibilities are endless.

What is a cataract? A cataract is the clouding of that internal lens of the eye which is normally clear. That internal lens helps focus light as it comes through the pupil that when a lens starts becoming a little cloudy, patients sometimes complain that their vision seems a little foggy. There are certain risk behaviors that you can avoid to reduce the risk of getting cataracts. Get professional tips and advice on cataracts in this medical how-to video.

Organic parsley gardening can be a fun and healthy source of nutrition if you know the right gardening procedures. Learn some tips for growing organic parsley from a professional organic gardener in this free video series.

Bake some delicious chocolate chip muffins that your kids will love. This how to video shows you a quick recipe for chocolate chip muffins that are supper easy to prepare.

There are a variety of ways to speed up your body’s ability to heal. Things like keeping the incision clean, resting, nutritious foods and physical therapy will get you feeling strong quickly. Avoid negativity, as it may actually slow down your recovery. No one likes to be laid up in bed after surgery. Follow the advice on your “get well soon” card and be back to your old self in no time.

This video illustrates how to repair a Ford F150 with a Triton V8 park plug thread. Get it into the garage and check out the engine. The Noise is all about the spark plug thread is blown out of the cylinder head. This problem is very common in the Triton V8 engines. To repair this spark plug thread the materials you need, Materials: 1. Cylinder head repair kit from Napa. 2. RED Thread locker. Procedure: Before the repair, remove the negative cable from the battery. Fit the adapter to the sock...

Wondering how you can get rid of acne and blackheads? Watch this tutorial for the answer! First you take a lemon and slice it in half, and then slice it into quarters. Take a quarter of the lemon and rub it on your face in the affected areas. This procedure will help you get rid of blackheads, acne, and acne scarring. The acidity in the lemon works as an astringent and will dissolve and loosen the blackheads and acne. The young lady in this video claims to have done research on treating acne ...

Learn what to expect when receiving acupuncture therapy, its methods, procedures & techniques, and information on the ancient medical practice of acupuncture from a Chinese medicine expert in these free video clips.

In this video, Michael Novelli explains what materials you need and the procedures you should follow to pack a mountain bike and ship it without damaging it.

In this series of video clips, you’ll learn tips and techniques for using various types of metal shears, including how to use hand-held and foot-operated types of metal shears, and how to use a metal press and metal hole punch. Expert Jon Olson offers advice on cutting procedures, the proper clothing and precautions, and advice on maintaining and cleaning metal shears. Jon also covers the electrical requirements for operating an electric shear, the various points of danger when operating the ...

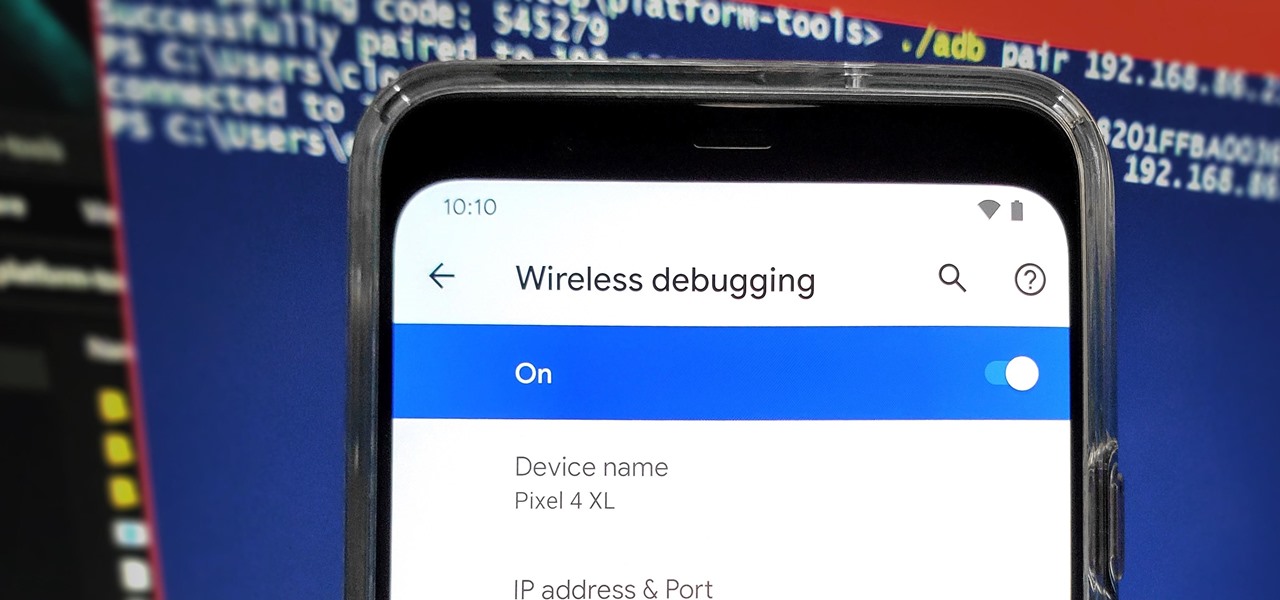
From booting into Fastboot mode with a single command to installing mods without root access, there's no shortage of reasons to use ADB. The catch, though, you had to be tied to a computer with a USB connection. However, a new feature in Android 11 finally allows you to run ADB commands over Wi-Fi instead of being tethered.

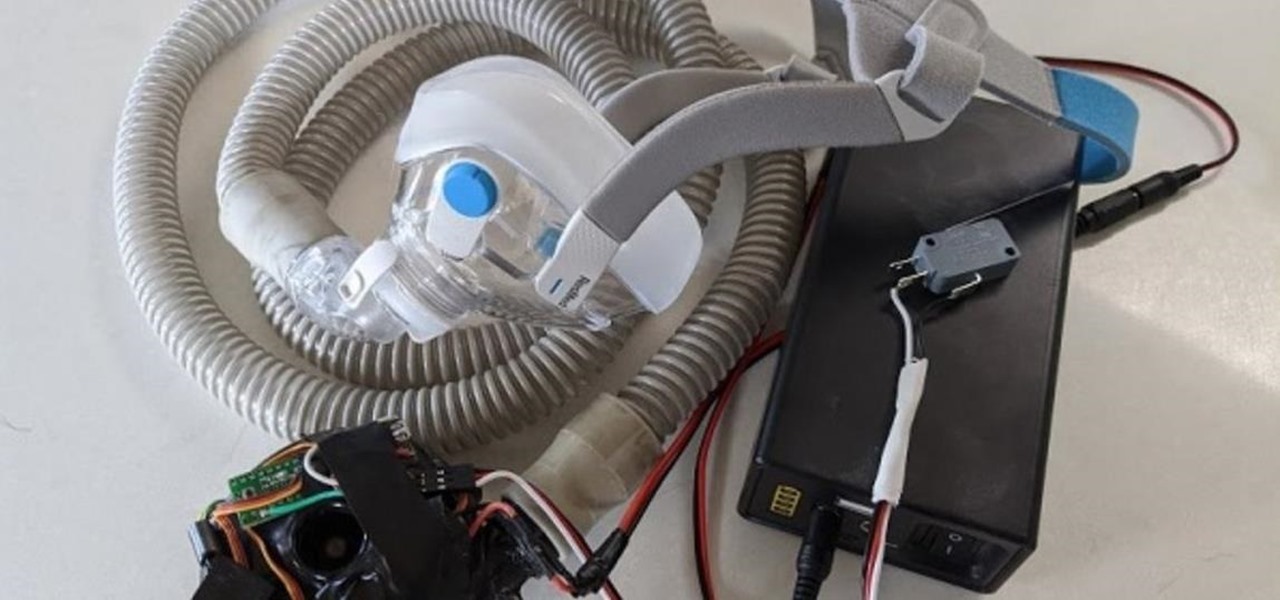
With the nation facing a shortage of ventilators for COVID-19 patients and no apparent ramp-up in the production of new ones, engineers, medical resistents, and do-it-yourselfers are sharing plans for homemade versions.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

With any password manager, the only password you need to remember is the master password that locks the vault from both hackers and the company. This makes the master password very important. But what happens if you forget this password? Well, LastPass has you covered.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

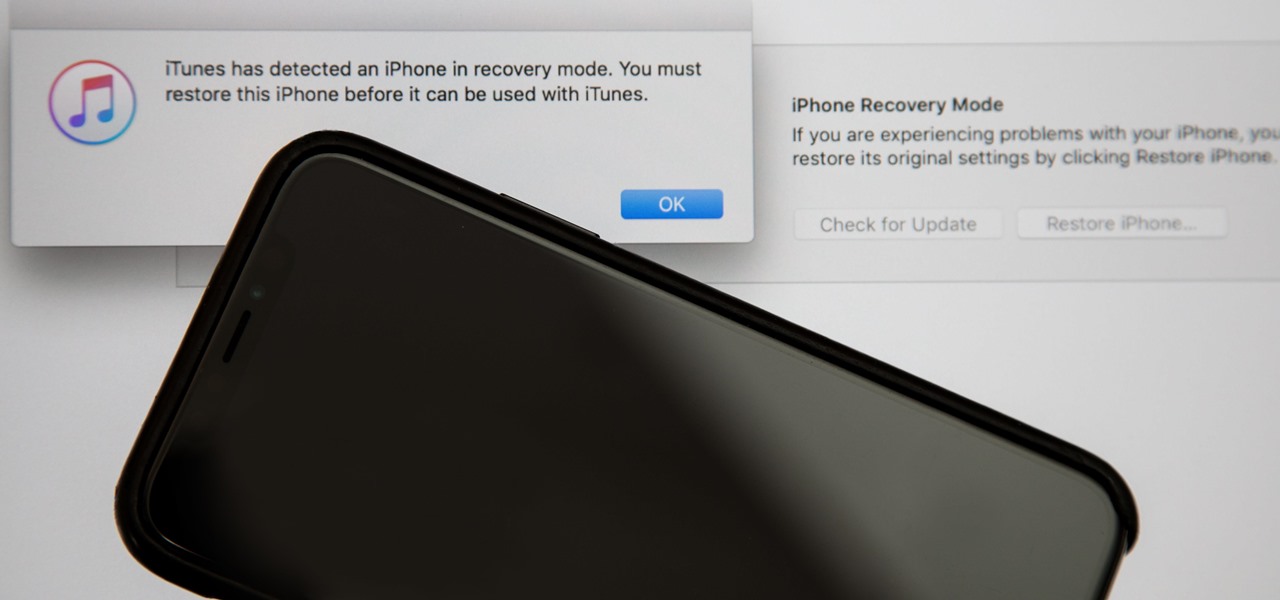
Following in the iPhone X's footsteps, the iPhone XS and XS Max, as well as the iPhone XR, have all ditched the iconic Home button last seen on the iPhone 8 and 8 Plus, which is one giant leap toward Jony Ive's ultimate vision of an iPhone that's a clean slab of glass. However, without the Home button, a lot of tasks have changed, most notably, entering and exiting DFU mode in iTunes.

One of the main reasons Authy was able to top our list of the best two-factor authentications apps was its ability to transfer access to a new device. This feature ensures that whenever you get a new phone, you don't lose all your tokens. However, if the process is done incorrectly, you can leave your account vulnerable.

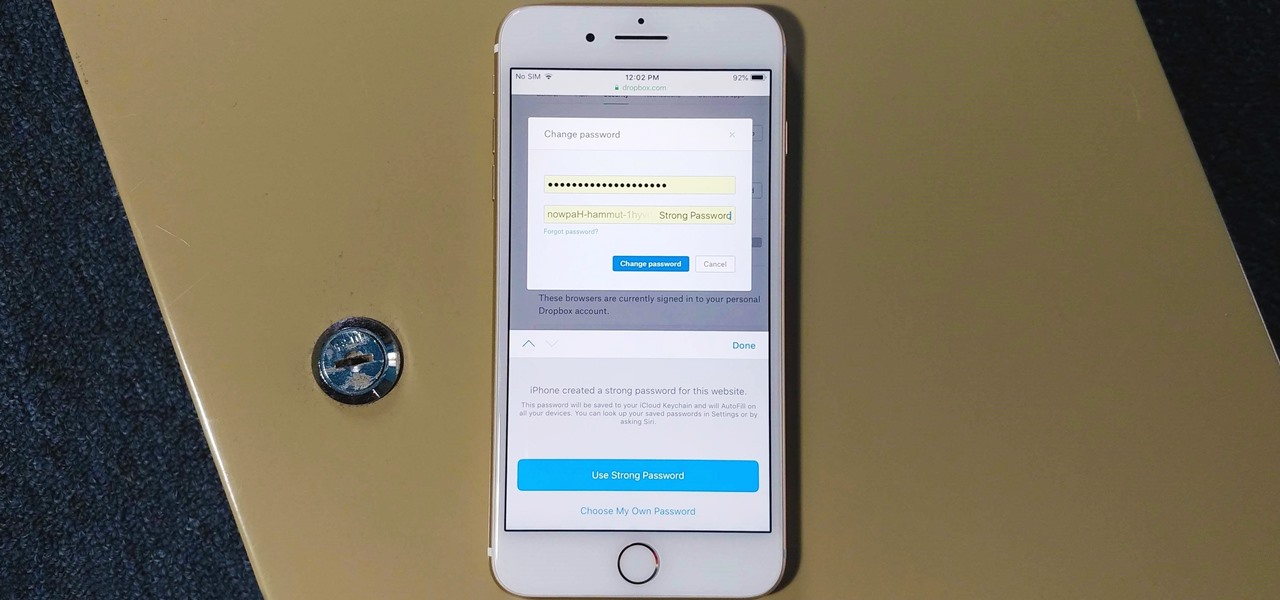
The option to auto-fill passwords on your iPhone has been around a while now, but iOS 12 improves on it by suggesting strong passwords when first creating an account online in Safari or within apps. Apple has also added "password reuse auditing" for your iCloud Keychain, where all your logins are housed, which will find and change your weak passwords to strong ones.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

If you ever want to root your OnePlus 6, install TWRP, get Magisk and Xposed, or flash a custom ROM, the first thing you'll need to do is unlock your bootloader.

Getting an insider view of the goings-on at Magic Leap is hard to come by, but occasionally, the company lets one of its leaders offer a peek at what's happening at the famously secretive augmented reality startup. One of those opportunities came up a few days ago when Magic Leap's chief futurist and science fiction novelist, Neal Stephenson, sat for an extended interview at the MIT Media Lab.

The Galaxy S9 is full of minor improvements and revisions that come together to make it a worthy upgrade over the Galaxy S8. One such improvement is facial recognition, which Samsung has fortified with machine learning and the inclusion of another sensor. The result of these efforts is called Intelligent Scan.

When it comes to applying augmented reality to various business functions, as the saying goes, there's more than one way to skin a cat.

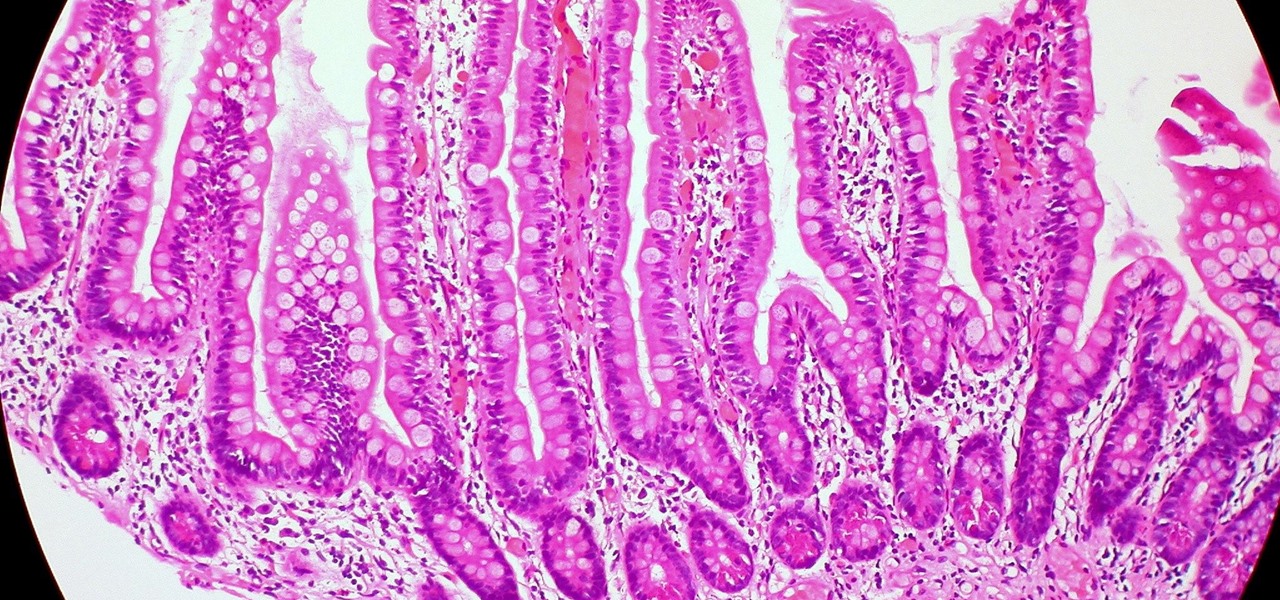
Several recent research studies have pointed to the importance of the microbes that live in our gut to many aspects of our health. A recent finding shows how bacteria that penetrate the mucus lining of the colon could play a significant role in diabetes.

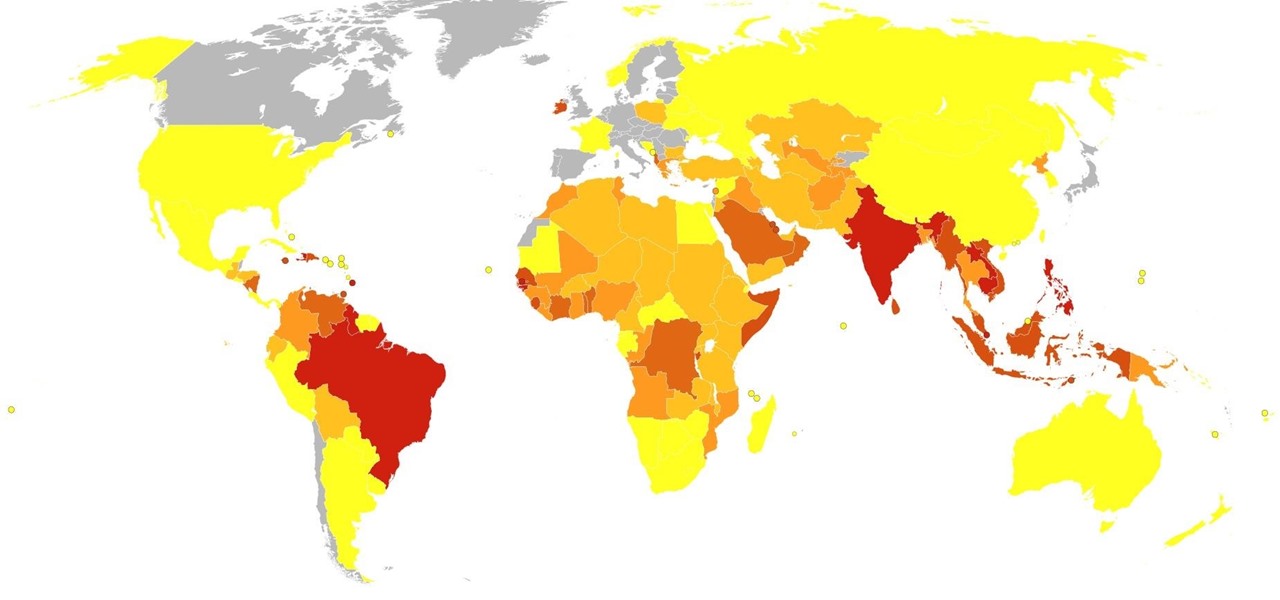
Dengue fever is a danger to anyone living or visiting tropical or subtropical regions. It can be hard to detect the infection in its earliest and most treatable phase, especially in children. Luckily, new research highlights better techniques for triaging the disease in infected children with more severe symptoms, potentially saving lives.

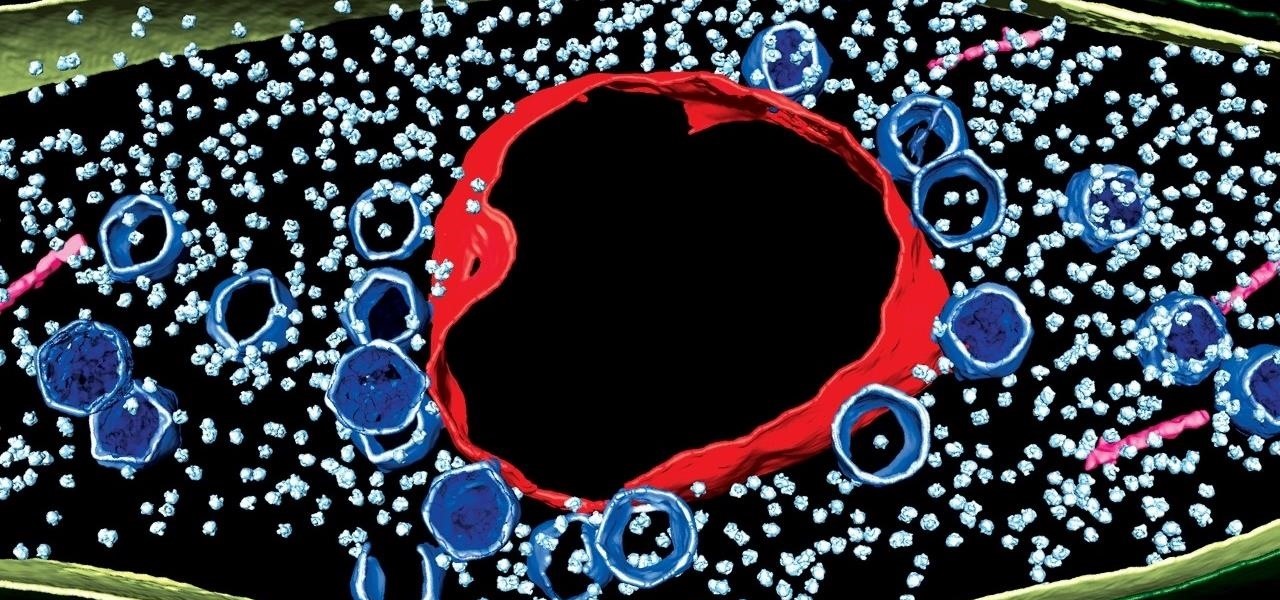
We fight cancer in a variety of ways, but no matter whether drugs, biologics, or our immune cells are part of the battle, they can do a better job fighting back cancer if we can help them find the tumors.

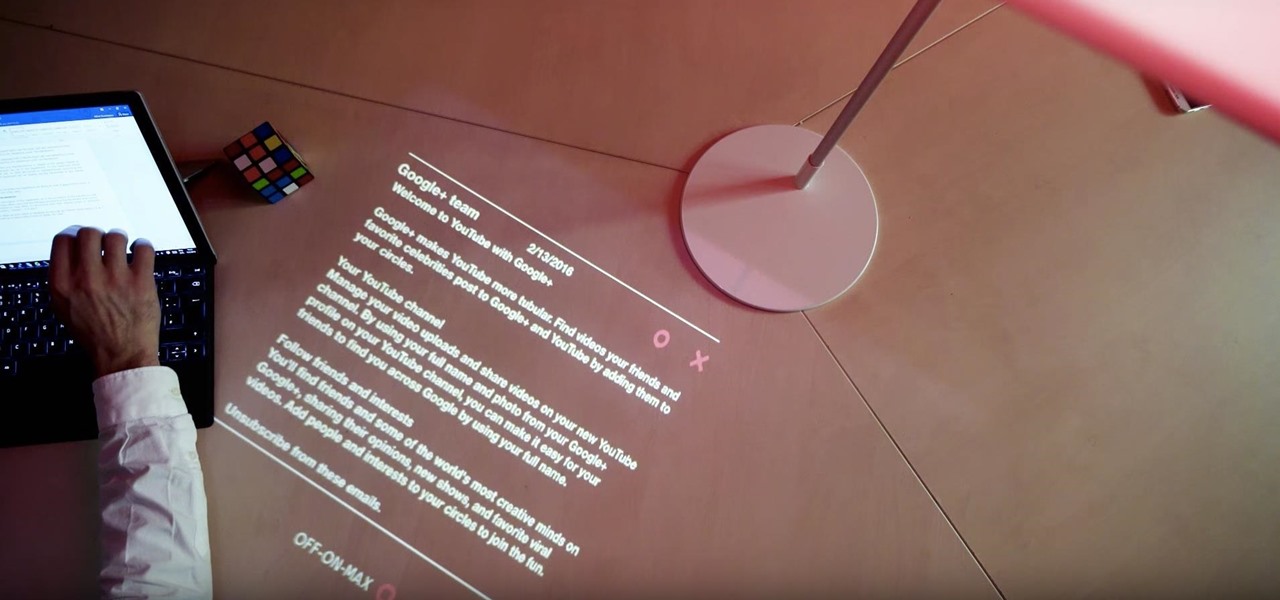
If you ever imagined turning the surface of your desk into one large augmented computer, well the future might not be far off, my friends. Lampix, the company that transforms any surface into a smart surface, is currently working on a portable and quite fashionable lamp to project an augmented computer onto any surface that you can interact with using your hands.

A new study just out reveals that HIV takes hold in the human body with the help of cells that usually work to heal, not kill.

Using extreme time-lapse microscopy, scientists watched a virus take over a bacteria to create a cell that looked and functioned more like a plant or animal cell. True story.

What do Leo Tolstoy (writer), Beethoven (composer), Paul Gaugin (artist), and Adolf Hitler (politician) have in common? They are all considered to have suffered from the sexually transmitted disease syphilis.

GitHub is an extremely popular site that allows developers to store source code and interact with other users about their projects. Anyone can download public, open-source files on GitHub manually or with Git, and anyone can fork off someone's project to expand or improve it into its own project. It's a really great site for programmers, developers, and even inspiring hackers.

Chris' Outrageous Cheesecake, a decedent combination of chocolate cake, brownies, cheesecake, and coconut-pecan frosting, is easily one of The Cheesecake Factory's most popular desserts. But, the price of fulfilling your cravings for this addictive treat can get up there (at about $8 a slice), and when you eat it at the restaurant you likely are limited to only one small piece.

Very often we have processes in Linux that we want to always run in the background at startup. These would be processes that we need to start at bootup and always be available to us.

Whether you are sending your phone in for repairs or finally selling it to upgrade to a new flagship, you are going to need to make sure all of your personal data is removed from your device.

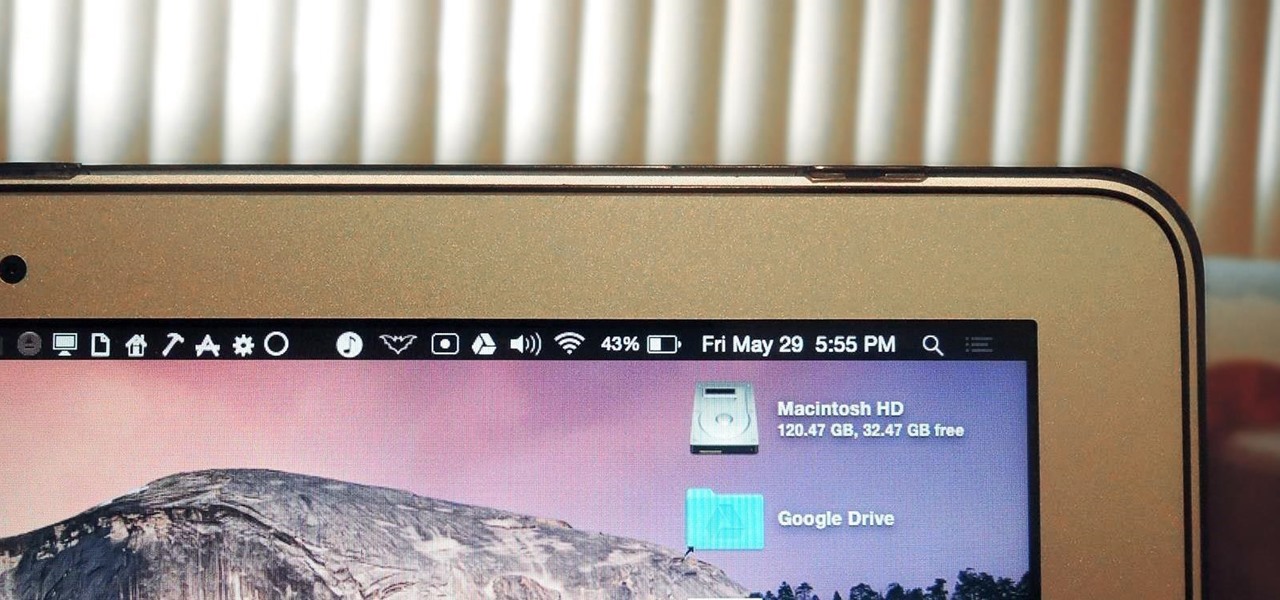
The menu bar is a great place to perform quick searches, track battery life, and switch Wi-Fi networks on your Mac, but it can do way more than that if you let it. I've rounded up some menu apps below that not only have features that will boost your productivity, but are lightweight enough to run entirely from the menu bar.

The gag reflex: it can interfere while in the dentist's chair, upon seeing another person throw up, or even just getting a whiff of a disgusting, stomach-twisting scent. Every time this reflex kicks in, it stops us immediately, inducing a choking, gagging, coughing fit.

Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way for computers to communicate over the LAN by just using computer names rather than MAC or IP addresses.

Complete silence or a non-stop Pandora playlist? People are often divided on what type of work environment they prefer. Whether you're a frequent loud music listener or you can't stand any kind of background noise, chances are you're pretty set in your ways.