See how to build a weatherproof compact high gain WiFi antenna for under fifteen dollars! This homemade WiFi antenna should be enough for most applications, since it's three times more powerful than a standard antenna.

Parents TV demonstrates how to safely bathe your baby, and features the products that make bath time a "splashing" success!

The legal travails of Magic Leap appear to have no end in sight, as a lawsuit filed by an ex-employee further threatens to dampen the startup's 2018 launch.
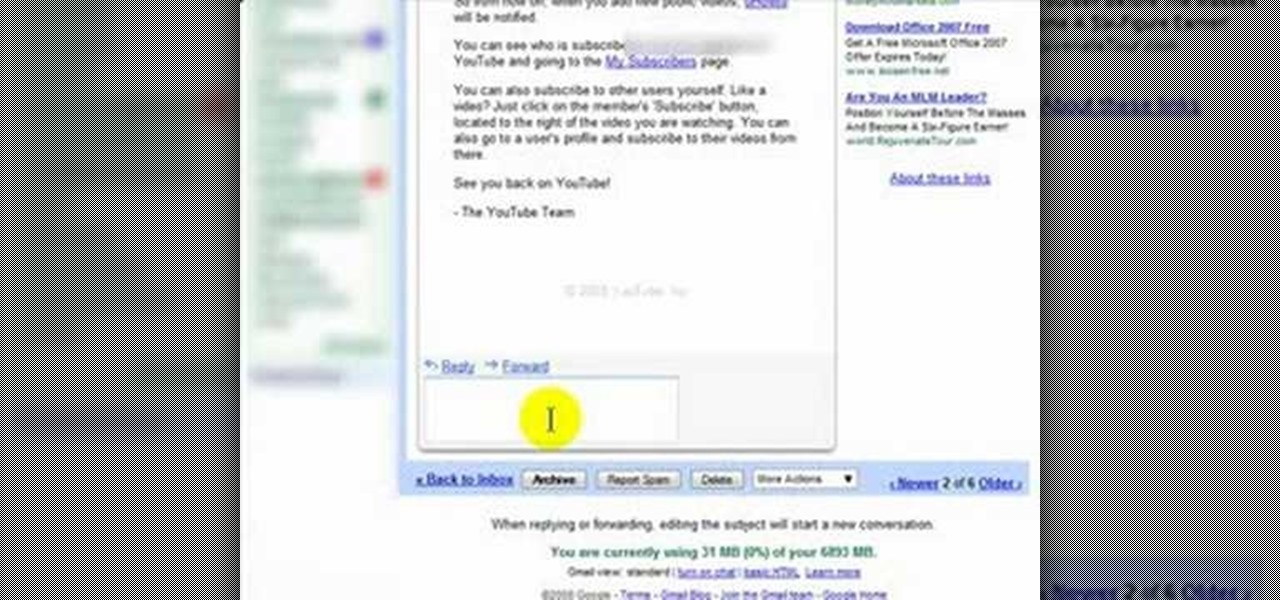
Gmail is an amazing e-mail service being offered by Google for free, and over the years it has built a large list of great, reliable features. The problem is not many have heard of Gmail, or know how to use it. In this great three part video series you will learn how to sign up for a Gmail account and also how to use some of its fantastic features to get you started on the right track.

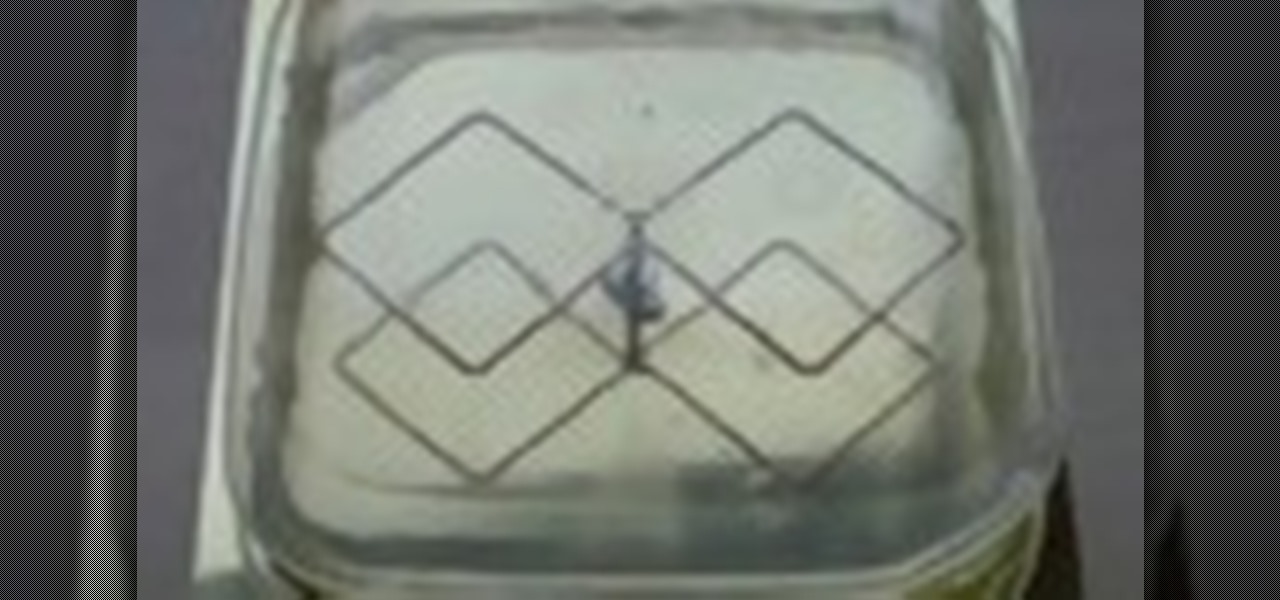
Another way to track your ovulation cycle is with a fertility microscope. A fertility microscope allows women to identify their most fertile days by testing and viewing the visual changes that take place in saliva throughout the monthly cycle. This method is reliable and effective, and can greatly increase your chances of getting pregnant. All this requires is saliva, so it is not invasive and doesn't use needles. So, check out this tutorial for advice and instructions on how to use one of th...

In this video, viewers learn about factory maintenance schedules and how to care for a vehicle. The series explains the differences between repair and maintenance, and the difference between do-it-yourself repair and professional auto repair services. Tips address choosing an auto mechanic and following factory and maintenance schedules. Increasing your vehicle's safety, reliability and longevity through proper maintenance also is discussed. This video will benefit all viewers who own a vehic...

If you like homemade light shows, this is one hell of a way to do it. AP Digital light shows you how you can hack a small fan into a special mirror used to create a poor man's PIC-based laser show. It's an experimental method of balancing a fan-mounted acrylic mirror for spirograph project.

There are many different ways to connect an iPod to an in-car stereo, however, some work significantly better than others. In this tutorial, learn how to use an FM modulator to listen to your favorite tunes. This is different than an FM transmitter which is much less reliable. The modulator is the best method of connecting an MP3 player to a car stereo without an AUX input jack. Check out this clip to get started.

In this video about choosing a web hosting company. The narrator begins by saying that web pages are hosted on servers; the files that make up a web site are hosted or stored on a server. The narrator recommends a service called Host Gator. He indicated they are reliable and provide reasonably priced web hosting services. He briefly discusses the process they charge for their different levels of hosting services. Next he shows the steps to hook your domain name to the host account. He demonst...

Netcat is a featured networking utility which reads and writes data across network connections, using the TCP/IP protocol.

Being an aircraft pilot can be frightening, but as long as you have the proper spin awareness training, you should be good. Most pilots out in the general aviation public that have never conducted spins in an approved aircraft for the purpose of developing their spin recognition and recovery techniques to become a more safe and reliable pilot.

If you've programmed a few Windows Mobile applications, you might need to perform some troubleshooting and debug the program to weed out all the problems. You can do this with AppVerifier. Marty Larson demonstrates installing, configuring and using the "AppVerifier" Application Verifier tool to debug Windows Mobile applications.

Ever wanted to build a backyard teepee? Here's your chance! In this two-part tutorial, learn how to contruct an inexpensive teepee out of a tarp. Easy to set-up, this teepee is roomy and fun to play in no matter what age you are! If in the wilderness, use this teepee for reliable shelter from cold or warm weather.

The Double Overhand Loop is a very quick and easy way to tie a loop at the end of the line. It is not a very strong knot but it is fine for attaching a sinker. For most other applications other stronger knots are better options. The double overhand loop retains around 55 percent of the line original breaking strength. A simple and yet reliable fishing knot. Watch this video knot-tying tutorial and learn how to tie a double overhand loop fishing knot.

Watch this video to learn how to cap off a water pipe with a push fit fitting within seconds. Useful for when you absolutely have to cut a pipe.

The leading platforms enabling augmented reality technology lead our headlines in Market Reality this week.

Toyota is testing blockchain and distributed ledger technology (BC/DL) for data sharing for driverless cars and other applications. This could eventually reassure buyers of its upcoming high-end cars by making sure their sensitive data is secure.

Last week, the U.S. Justice Department issued criminal indictments against seven Iranian hackers. These hackers, working for private companies in Iran, are accused of orchestrating DDoS attacks against U.S. financial institutions from 2011-2013 as well as intruding into the control panel of a small dam in Rye, New York. It is thought that these attacks were a response to the U.S. tightening financial restrictions on Iran during those years and the NSA-based Stuxnet attack on their uranium enr...

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

A new picket fence can add character to a home. Learn how to install a picket fence from a professional contractor in this free home improvement video series.

Repair, spackle, and paint a kitchen like a professional. Learn how to paint a kitchen with tips from a painting contractor in this free video on home decor.

Tax season is always stressful, especially for entrepreneurs and small business owners. Rather than wait until March to get your finances in order every year, learning how to keep track of your expenses is a valuable skill that saves you and your business time, money, and plenty of anxiety.

The augmented reality team at USA Today closed out a prolific year of immersive storytelling with a hard-hitting companion piece exploring the controversial conflict in Afghanistan.

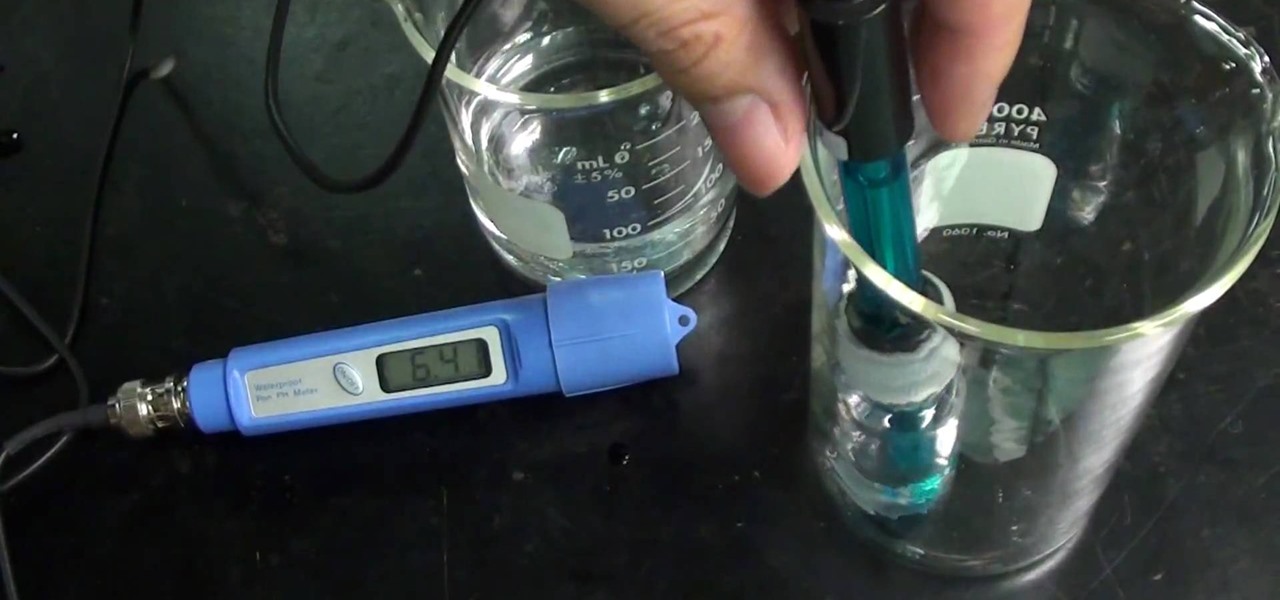
If you want to know the best way to get an accurate pH measurement, this shows the lab equipment needed and the processes used. When doing chemical reactions, sometimes the acidity or the basicity is important. This is usually defined as pH and measuring it can be very useful for getting the reaction right. There are a few ways to measure pH, and the simplest, cheapest, most reliable method is paper. But that's not all. See a whole lot of ways in this two-part video.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

If you're anything like me, every time you travel you end up in a desperate panic for a decent W-Fi connection. Whether you want to post your photos, research the best beaches, or kill time during an overnight layover, a hotel's Wi-Fi quality is of paramount significance in making a reservation.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Check out this mission on The Saboteur for the Xbox 360. The third mission in Act 2: A Whisper or a Roar is where Santos is looking for help again. When you get to the convoy, Sean points out that there are two very different ways to complete this mission. You can get a disguise, sneak up close to the convoy, and plant some dynamite, which would be the conventional route.

Tips on designing an outdoor kitchen, finding a contractor, fitting your budget, and cooking the perfect outdoor pizza.

The video presents "How to start your own Clothing Line Business". The steps include getting the financing, designing the prototype outfit/s, producing the line of clothing, promotion and sales. A good way of financing for a small business such as this is to sell your idea to family, friends and even colleagues. Research and prepare the business plan for your clothing line and be passionate about it in your presentation to convince them to fund your business. The next step is to get the produ...

This Lynda tutorial teaches how to use the Logic pro, a songwriting application. Midi sequencing and quantizing is the main focus of this video. Midi is a short name for Musical instrumental digital interface. Midi is not sound. It is a low resolution computer protocol, developed in early 80’s to enable computer to communicate each other. Midi is fast, simple and reliable. It has a intensity stream. In this project, Scot Hirsch explained how a midi file is manipulated in Logic pro. Midi file ...

First thing you should do is invest in a reliable good quality digital camera. No, you do not have to spend big bucks on one. Kodak, Sony and Nikon make inexpensive digital cameras that are ready to be bought everyday. Make sure you find a camera that fits your needs.

The witch is the blue-chip stock of Halloween costumes — reliable return, low risk. You Will Need

This how-to video quickly outlines exercises to get your dog walking on a loose leash by your side. Put very basically, teach the dog what you want them to do! And secondly, stop reinforcing them when they pull! A clicker training method is used, but if you do not have one, you can always use a verbal marker like yes. However you will get much faster and reliable results by using the clicker. If you hold the clicker in the same hand as the leash, and keep the treats in the other hand, you wil...

Remember when MITMing people to pentest webapps and log-ins you had to fire Ettercap,Arpspoof, SSLstrip, then look for credentials in the captured packets?

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

Have you ever felt like you wanted to totally annihilate someone in Minecraft with a machine gun? Yeah, me, too. Thankfully, you can!

Update: Monday, 11 p.m. ET: In a report from Bloomberg, eMagin CEO Jeffrey Lucas has contradicted what appeared to be investor information found in SEC filings that surfaced on Monday. Although Apple is listed among several other investors in the company in filing, Lucas told Bloomberg that Apple is not, in fact, an investor in the company. Offering further clarification, Lucas told the news site that eMagin "listed those companies in the filing because it had discussions with them at industr...