It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

Not content to just be a provider of rugged smartglasses for enterprise users, DAQRI has made the jump into the AR software side of the industry with its new Worksense productivity suite.

As part of its ARCore release announcement, Google also revealed a forthcoming app that's sure to excite those who celebrate '80s pop culture.
In a LinkedIn post published on Tuesday, Microsoft's leading advocate for the HoloLens made a prediction that the mixing of immersive technologies will define augmented reality in 2018.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

Many people think antivirus apps are useless — why pay a subscription fee when most malware can be avoided with common sense? But the thing is, there were an estimated 3.5 million malicious Android apps discovered last year, with many of them making their way onto the Play Store. As this number continues to rise, can you truly depend on common sense to protect you?

Perhaps in tribute to the season premiere of Game of Thrones, Google Glass is demonstrating that what is dead may never die, as Alphabet's X (formerly Googlex) has revealed that the Enterprise Edition of the smart glasses are now available to businesses.

3D Touch is only available on the 6s and 7 series iPhones right now, and likely future models, so those with older devices are missing out on all the cool "Quick Actions" available for app and settings icons. But the new iOS 11 is finally bringing some of those helpful shortcuts to iPhones without 3D Touch built in.

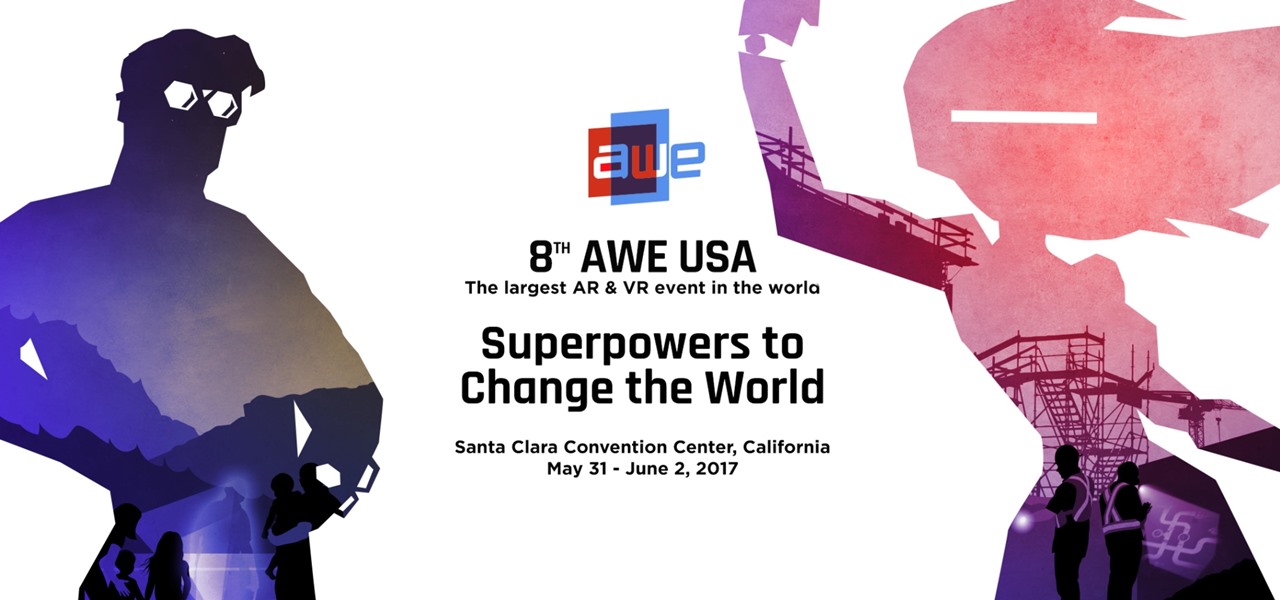
The Augmented World Expo (AWE), the biggest event for augmented, virtual, and mixed reality companies, developers, customers, and connoisseurs, is happening right now. You know what that means for us here at Next Reality? Companies presenting and exhibiting at AWE are releasing news like crazy.

In February, the popular Facebook-owned WhatsApp Messenger service jumped on the "stories" bandwagon and replaced their in-app, text-based "About Me" status (you know, those lovely little messages where you can say "Sleeping" or "Not Sleeping" under the tiny nub of your profile picture). Taking its place was a clone of Snapchat's Stories feature, continuing the social media giant's recent trend of shamelessly copying Snapchat.

If you were a particularly good little girl or boy this year, Santa might have finally brought you that cool new smartphone you've been wanting. Or perhaps you just took advantage of a great sale and treated yourself to a new gadget this holiday season—totally justifiable, and surely a well-deserved gift.

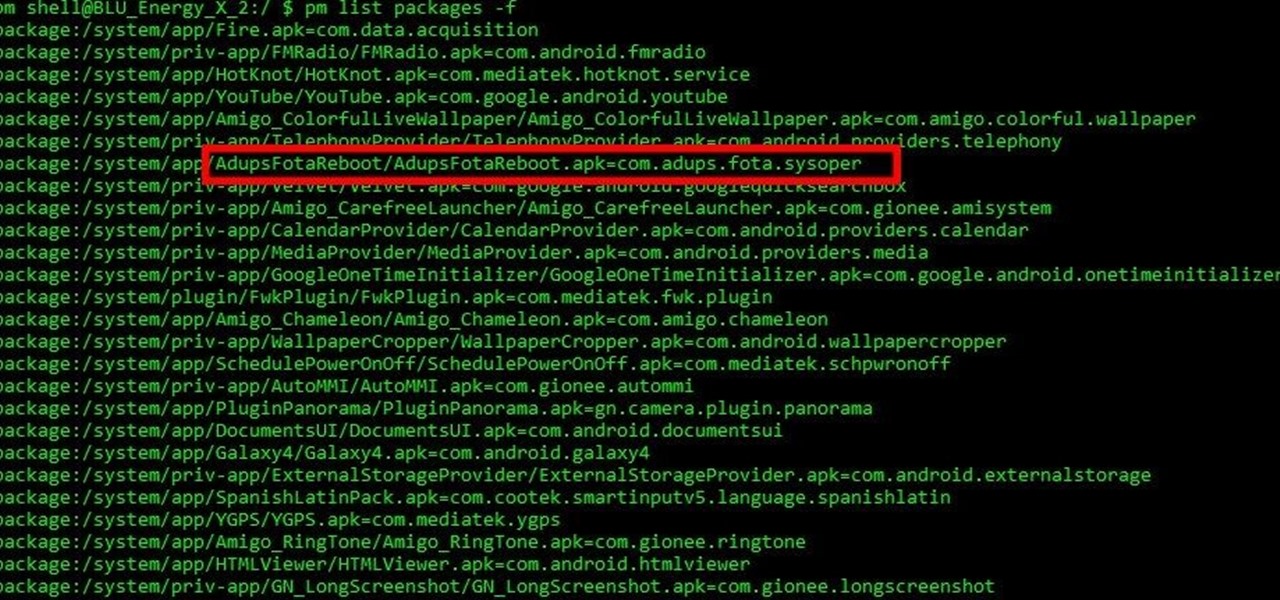
Mobile security researchers at Kryptowire recently uncovered spyware preinstalled on hundreds of thousands of Android smartphones by FOTA provider Adups which was gathering personally identifiable information (PII) such as call logs, app usage data, and even the full contents of text messages and sending these to a third-party server—all without the users' knowledge.

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

This technique goes with a project that I have already made - This shows how to make a paper weaved background for your cards, scrapbook books etc as shown in the picture below.

Although lots of the bigger hotel chains are lessening the restrictions they put on their room TVs, some smaller ones are still taking measures to prevent you from plugging in computers or streaming devices into an HDMI port. However, there are a few steps you can take to bypass these restrictions and watch your own media in a hotel that has restricted TVs.

NMAP is an essential tool in any hacker's arsenal. Originally written by Gordon Lyon aka Fydor, it's used to locate hosts and services and create a map of the network. NMAP has always been an incredibly powerful tool, but with it's newest release, which dropped mid-November of last year, they've really out done themselves.

You're at your friend's house. All you've heard about all day is his new laptop. He's got a brand new top-specced MacBook Pro, and he won't stop going on about it. It particularly annoys you as all you've got is a 4 year old cheap laptop, even if it is running Linux.

Apple's special September event just wrapped up with the company unveiling several new products, including the iPhone 6S, iPhone 6S Plus, iPad Pro, and the new Apple TV set-top box. In addition to hardware, Apple also discussed a couple of its latest software platforms, iOS 9 and watchOS 2. Check out everything that Apple unveiled below.

You can find a plethora of tennis games on the Google Play Store, but if you're a true tennis fan and gaming enthusiast, you should check out Tennis Racketeering by Core Aplikacije. The game lets you use an additional Android device as a racket, giving you Wii-like abilities without Nintendo. It's simple to set up and extremely fun to play, so follow along below to see how it works.

The weather outside might be frightful, but heating bills are downright scary this time of year. Heat is absolutely essential during the winter season, but it's also really expensive. If you aren't blessed with a fireplace or unlimited disposable income, fear not, because you can still heat your home on the cheap using flower pots and tea lights—even if the power goes out.

Welcome back, my hacker novitiates! As you know by now, the Metasploit Framework is one of my favorite hacking tools. It is capable of embedding code into a remote system and controlling it, scanning systems for recon, and fuzzing systems to find buffer overflows. Plus, all of this can be integrated into Rapid7's excellent vulnerability scanner Nexpose.

This video talks about how one can create a burger from a simple play doh set. This video is for kids and for everyone who loves playing with playdoh.

Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.

This video will explain how to safely weight down and secure a basket ball hoop with a water filled base that has a hole in it.

Welcome back, my greenhorn hackers! Sometimes, we don't have a specific target in mind, but rather we are simply looking for vulnerable and easy-to-hack targets anywhere on the planet. Wouldn't be great if we had a search engine like Google that could help us find these targets? Well, we do, and it's called Shodan!

How to make a Lego key holder with note board. Tired of loosing your keys? Well keep them safe and in one place with this fun Lego key holder.

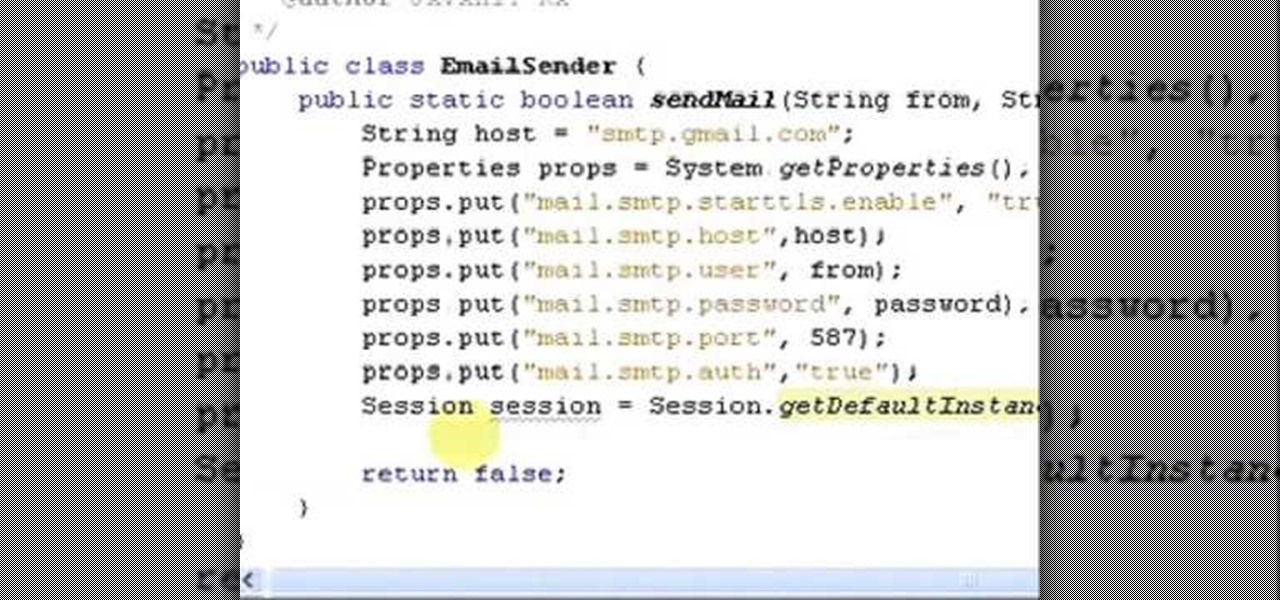
It uses JavaMail API, NetBeans IDE 7.0.1 First download the JavaMail API as shown in beginning of the video then follow the video to send email dynamically from your Gmail account. No need to open your inbox.

For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swiss Army knife of hacking tools." We'll look at the capabilities of Netcat and how the aspiring hacker can use it.

Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

This video demonstrates the steps to take using Chip Foose's signature bronze base coat. Once the base coat is sprayed, we'll spray clearcoat.

In this tutorial we learn how to install a toilet bowl for your bathroom. First you will apply the ring around the bottom of the toilet and on the floor where the toilet base will go. Apply plumbers wax to make sure this is sealed. Then, flip the toilet over and line up the holes. After this, slowly let it down and push it when you know the holes are in place. Next, you can push down and screw the bolts onto the base of the toilet. When finished, you will be able to connect the water and get ...

In this tutorial, we learn how to make a pair of great looking earrings. To start, you will take the base of your earring that has the hook on it and then take the wire for your beads. Pick out any beads that you want to attach to the wire, then string them onto it. You can add different colors and any type of bead you want to make these unique. From here, use wire cutters to bend and cut the excess wire from the bead. From here, you will bend the extra piece into a loop that you will hook to...

In this tutorial, we learn how to divide numbers with exponents. The quotient rule states that we can divide two powers with the same base by subtracting the exponents. With the same base, you can subtract the exponents to get something that would be the answer. For example, if you have 6(to the fourth) divided by 6(to the second), this would come to equal 6(to 4-2). This would break down to equal 6(to the second power). Once you have this, you will be able to do the math for this and figure ...

In this video, we learn how to set up the mast on the Open 570 single-handedly. First, look to see where the mast is going to fit on the boat. Pick the mast up in the middle so it balances out on each side, it's very long. Turn the mast around and place the edge facing the foyer. Put the base of the mast into the mast step, then let it rest on a step ladder. From here, get into the boat and add the safety pin into the base of the mast to keep it locked. Now take the mast and push it up into t...

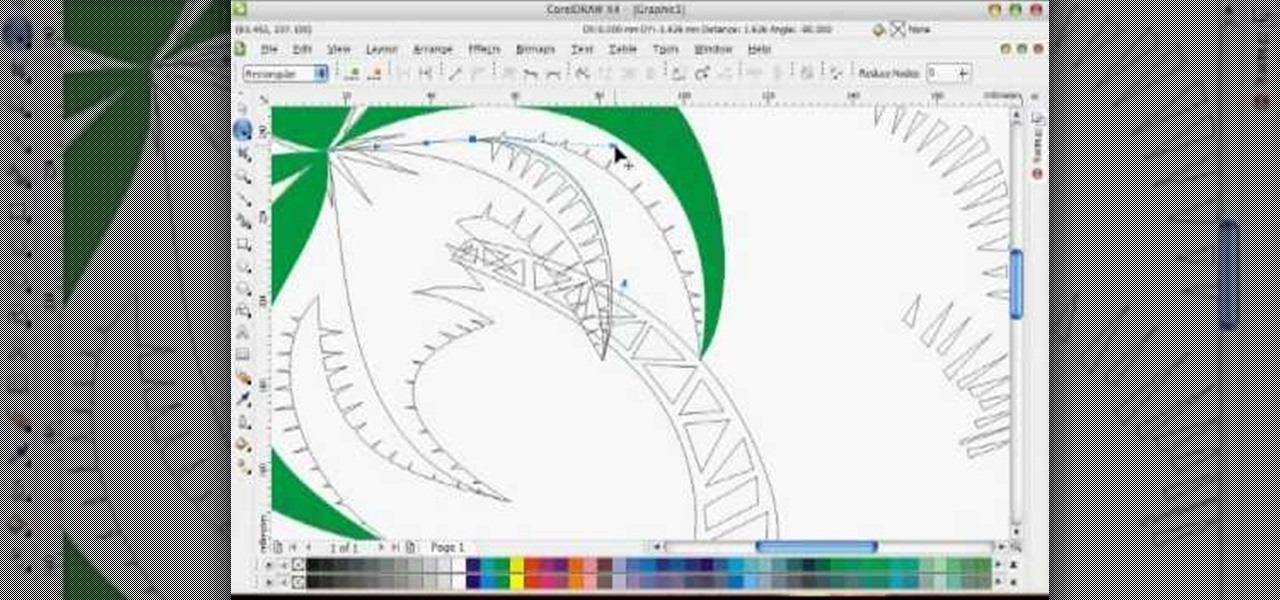
In this tutorial, we learn how to draw a vector art palm tree in CorelDraw X4. Start off in the CorelDraw program and create the base of the tree with a drawing tool in black. After this, draw small triangles inside of the base of the tree and then draw the leaves and branches of the palm tree. Fill this in with small spikes and then erase the middle nodes. From here, use a shaping tool to make the spikes on the palm tree more rounded and lifelike. After you do this, start to color in the ent...

This makeup style was inspired by the Irish folklore creatures called Leprechauns, with their greens and pots of gold. Marinshe shows you this green makeup look that's perfect for Saint Patrick's Day, with a little bit of gold to top it off!

In order to paint nails with funky hot pink design, you will need the following: a base coat, a purple nail polish, a nail plate, stamping nail polish, a stamp, a top coat, gold glitter nail color, and a scraper.

In order to create a Jennifer Lopez inspired makeup look, you will need the following: a base for your eyes, blush, a bronzer, Maybelline quad eye shadow, false eyelashes, liquid liner, and a moisturizer.

In order to paint a geometric, tribal, ornamental design for your nails, you will need the following: base coat nail polish, hot pink nail polish, a gold/brass/copper nail polish, a dark nail polish, and a clear top coat or a shimmer.