Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.
Welcome back, my eager hackers! In recent blogs, I've demonstrated how to grab password hashes remotely using Metasploit's meterpreter and pwdump. Once we have the Windows passwords from the SAM file, we can then crack these hashes using tools such as Cain and Abel.

Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.
Our attention spans have vastly shortened thanks to the Internet and our subsequent procurement of information from it at a rapid pace. It's tough to pay attention to something for a good amount of time, unless it's ridiculously interesting and stimulating. It's gotten so bad for me that I keep checking my phone every ten minutes—I even did it during a midnight showing of The Dark Knight Rises.

Everyone listens to music. I've got over 3,000 songs in my iTunes library, but am always looking for more, and I'm sure you are too. You can never have enough tunes to rock out to, right? If you're using Windows 8 like I currently am, these are some of the best apps in the Windows Store right now that will help you find new jams for your collection.
A Steampunk's Guide to Sex was the subject of a recent successful Kickstarter campaign, and I now hold the finished book in my hands. As such, I can say (mostly) unreservedly that you should buy this book. Allow me to tell you why, before I get into the nitty-gritty about the book itself. Sex is something of an odd topic in America because it's perfectly legal, and yet taboo. Unlike things that are illegal and not taboo, like drug use, murder, theft, etc. What this means is that children can ...

Once you have the skills to bring your ideas to life, the hardest part is coming up with ideas. What do you do when you can't think of something to make? What happens when your well of inspiration runs dry?

Your entire life has been a lie. Mario does not hit blocks with his head, footlong subs are never really 12 inches long, and those paper ketchup cups at fast food joints aren't just little cups. And that's not the worst of it. What I'm about to tell you next is the revelation of all revelations.

Last week, we rolled out a major site-wide update on WonderHowTo, making it even easier to follow the subjects you're passionate about—and easier to share your creations with people who'll give you the kudos you deserve!

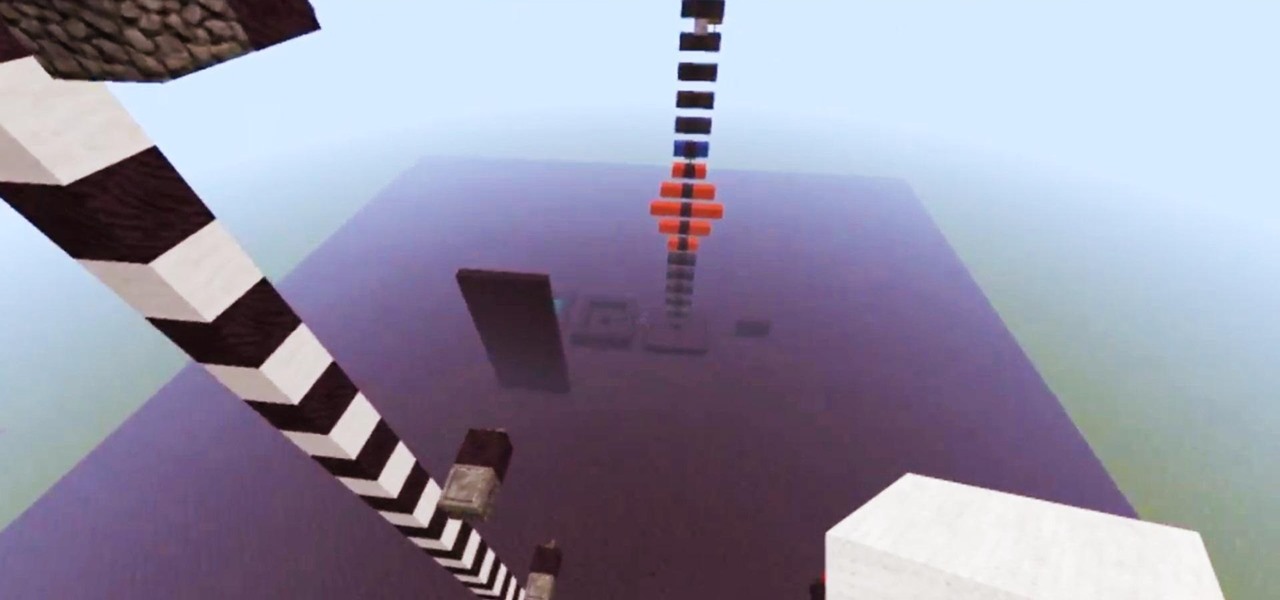
Introduction So today and yesterday I was playing with TNT (as we all do at one point or another) and I was curious about a few things. From this curiosity, I went on to discover some of the science behind some things you may or may not have known.

Introduction So, today and yesterday I was playing with TNT (as we all do at one point or another) and was curious about a few things. From this curiosity, I went onto discover some of the science behind some things you may or may not have known.

It's official. Vajazzling is out, Vatooing is in. Just when you thought there couldn't be something trashier than vajazzling, a new season brings about vatooing. You can now treat your vagina to a temporary tattoo.

Ready to stop going threw life blind? Try to get a glimpse of the future or at least a use these as a reflection of what’s happening in your life with your own tarot cards. Tarot cards can provide endless hours of entertainment.

If your in college or just want to be prepared for an unfortunate situation, it is important to know how to tell if someone is suffering from alcohol poisoning. Binge drinking can lead to long term health problems but with vigilance, immediate death can be prevented.

Learn how an overnight nurse prepares for the late shift with expert nursing tips from an experienced night nurse in this free online late shift related video series.

This video slide show tutorial gives a step-by-step guide to scissoring a poodle topknot. 1. After clipping the face against the grain with a close blade, the line is first scissored from the outside corner of the eye to the top of the base of the ear.

In this video series, watch as jazz musician Ryan Larson teaches advanced bass guitar lessons in all twelve keys. Learn how to read tab and relate it to scale names, how to walk through various bass lines, and how to play a Latin walking bass line.

In this video series, learn some beginner tips on how to play classical music on the piano. Our expert pianist will give you a few pointers related to practice methods, including how to tackle complicated passages, how to build your skill level by starting small, keeping tempo, what to do if you make a mistake, where to focus your eyes, and even a few suggestions for the best types of pianos suited to classical music.

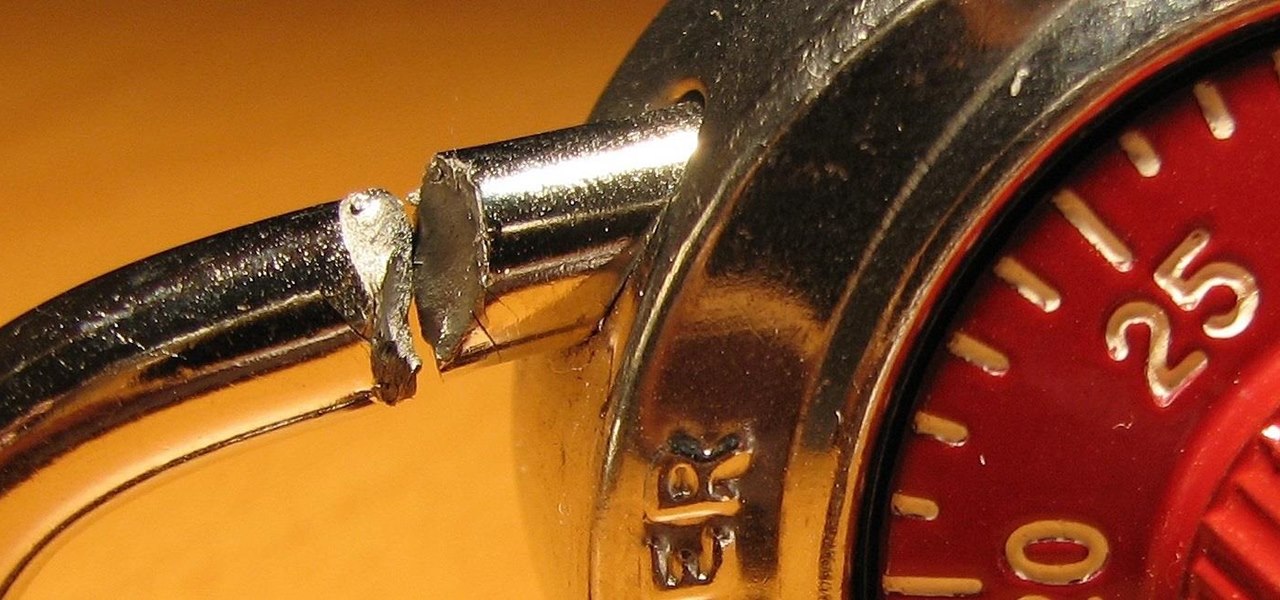
In this online video series learn from expert professional mechanic Nathan McCullough who graduated from Nashville Auto-Diesel College with a Grade Point Average of 3.5 and received their craftsmanship award and honor seal. Learn important automotive Serpentine belt topics including: what is a Serpentine belt, locating the Serpentine belt, replacing the Serpentine belt, when to check the Serpentine belt, types of wear to look for, Jacking Screw Tensioner, Serpentine belt removal, checking the...

In these lion dance video instruction clips, learn about the music of the Southern style Chinese New Year Lion Dance and how it influences and directs the ceremony. Listen to the cymbals and drums as the Buddha puts the lion through its paces, taunting him with his fan. Learn how the different instruments create emotional soundscapes related to the narrative of the lion dance. Get an in-depth look at Chinese lion dance drum music in this video series, a thousand years in the making.

In this video series, watch as jazz musician Ryan Larson teaches advanced bass guitar lessons in all twelve keys. Learn how to read tab and relate it to scale names, how to walk through various bass lines, and how to play a Latin walking bass line.

In this video series, watch as jazz musician Ryan Larson teaches advanced bass guitar lessons in all twelve keys. Learn how to read tab and relate it to scale names, how to walk through various bass lines, and how to play a Latin walking bass line.

The emergence of Microsoft's HoloLens 2 as a cutting-edge US Army tool has focused a spotlight on the marriage between augmented reality and the military.

On Friday, the Tokyo Olympics finally kicked off after massive delays and complications due to the pandemic.

End-to-end encryption makes WhatsApp chats private and secure. However, if someone has access to your iPhone, they can easily open the app and browse through all of your personal conversations. Luckily, there's an easy way to block any would-be intruders at the gates — just lock the app behind Face ID or Touch ID.

Facebook Messenger's user base has grown so much that it has taken over text messaging as the primary contact method for many people. However, sometimes you might want to hide your online status from specific contacts and appear offline to others. There's a neat little trick you should know that can help you achieve this.

Apple just released iOS 13.6, and while there aren't a ton of new features here, there are some pretty amazing ones to be on the lookout for.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

TWRP is the premiere custom recovery for Android because of how many devices it supports and how simple it is to use. But installing it in the first place hasn't always been the easiest thing to do — until now. With the help of a Magisk module, you can finally use one Android device to flash TWRP on another.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

It's not hard to let the new SARS-CoV-2 strain of coronavirus put pressure on our minds. Fear of catching COVID-19 is never far from the topic of conversation. But it doesn't have to be that way. If you're struggling with anxiety, stress, depression, or any negative emotions due to the virus's effect on our lives right now, you might find some solace in meditation.

There are times when leadership is tested. This is one of those times. As government and business leaders around the world are grappling with the unfolding coronavirus pandemic, the real-time responses to the crisis from many leaders have been great and, at times, less-than-optimal.

MIT artificial intelligence researcher Lex Fridman recently asked SpaceX and Tesla founder Elon Musk possibly the best question he's ever been asked: What would he ask a hypothetical AGI system (an AI system with human-level intelligence and understanding) if he only had one question?

With the whirlwind of noise surrounding the COVID-19 virus sweeping the nation, it's not hard to default to panic mode. One of the best ways to avoid panicking, however, is to follow trusted sources of information and avoid all of the opinions and trolls that don't reflect reality.

We've been so worried about volumetric scans possibly robbing celebrities and performers of their agency and right to control their image that, somewhere along the way, we forgot that scans may not always be necessary to produce passable holographic performances.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

There are times when physically interacting with your iPhone is less than ideal, like when you're cooking or driving. Fortunately, iOS 13 has you covered regardless of the circumstance you may find yourself in. With the new Voice Control feature, you can control pretty much everything on your device without even touching it.