What happened to please and thank you? When did asking someone to come look at your build degenerate into COME NOW or FOLLOW or sending out teleport requests to any and all currently on the server without asking?

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and root boxes, you'll need to learn how to perform the necessary reconnaissance first. In fact, you will spend far more time researching your target then you will exploiting it. In this article, I am going to show you the fi...

In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then anywhere else on the 'clear' Internet. The nature of networking and routing means your location is always known in server logs. It only takes one phone call to your ISP with your IP address to obtain both your physical ad...

I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

Amazingly, a lot of people I know haven't even heard of SOPA or PIPA. Now, every English-reading person with an internet connection will finally have those two four-letter acronyms emblazoned in their minds. For the entire day today, Wikipedia's English-language site will be in total blackout in protest against the proposed legislation in the United States. And that's not all. MoveOn, Reddit, BoingBoing, Mozilla, WordPress, TwitPic and other popular websites are down today in protest.

The Elder Scrolls V: Skyrim set off a bang in the video game world this month. It will likely be video game of the year a few times over. Skyrim is another part to a series set in the fantasy world of Tamriel, a world filled with mystical creatures, folklore, and even its own history. It's quite the beatuiful and immersive experience. If you have not picked up the game yet, please do (my fiancée even plays!). Also, make sure to buy it new, so the hard working coders at Bethesda get the money ...

I can't say it's absolutely true, but when it comes to mobile word gaming, there's Scrabble people and then there's Words with Friends people. It feels segregational. Rarely does one play both. At least, that's what I see when it comes to my family and friends.

Now that it's been a week since Google+ rolled out pages, we've gotten over our euphoria at finally getting the feature after a long wait, and reality is starting to sink it. It's not as flexible as a Facebook page, it seems to be time consuming, and you can't even get a unique URL. On the other hand, your Google+ page will show up in Google searches, and help bump you up a bit. Here's how the search stacks up when I search for "WonderHowTo" in Yahoo! vs. Google (Note: I've turned on private ...

I've seen numerous tutorials on how to create a "strong" password. This makes me laugh. These titles imply "one" password, which is wrong in and of itself. A person should have many passwords, all different, and all extremely long. People may ask how they're supposed to remember lengthy passwords and why their current password isn't good enough. Well, I'm going to show you.

If you're interested in bypassing Windows and Linux passwords, there is a great tool from the good people at Kryptoslogic. Have you ever forgotten your administrator password? Have you ever bought a used computer with a password on it? Well, Kryptoslogic have created a boot-disc call 'Kon-Boot', which allows you to bypass any Windows 32 or 64 bit OS, as well as Linux passwords. There is both a paid and freeware version available.

G+Me is one of our favorite Chrome extensions here at Google+ Insider's Guide. We love it because it's one of the most comprehensive extensions out there. It attempts to address the "noisy streams" issue, with list mode, and collapsible posts and comments. The creator, +Huy Zing, is very responsive to feedback, and he's been quick to address any issues that arise, including privacy concerns. He's even created a G+Me (Paranoid Edition) extension, for the extra careful Google+ user. And if you ...

Welcome to the Google+ Insider's Guide to all things Google+. We're dedicated to keeping you updated with all the latest news, tips and tricks on Google+, and this official index will serve as a one-stop catalog of all our How-To articles, as well as all the news & updates we've covered over time.

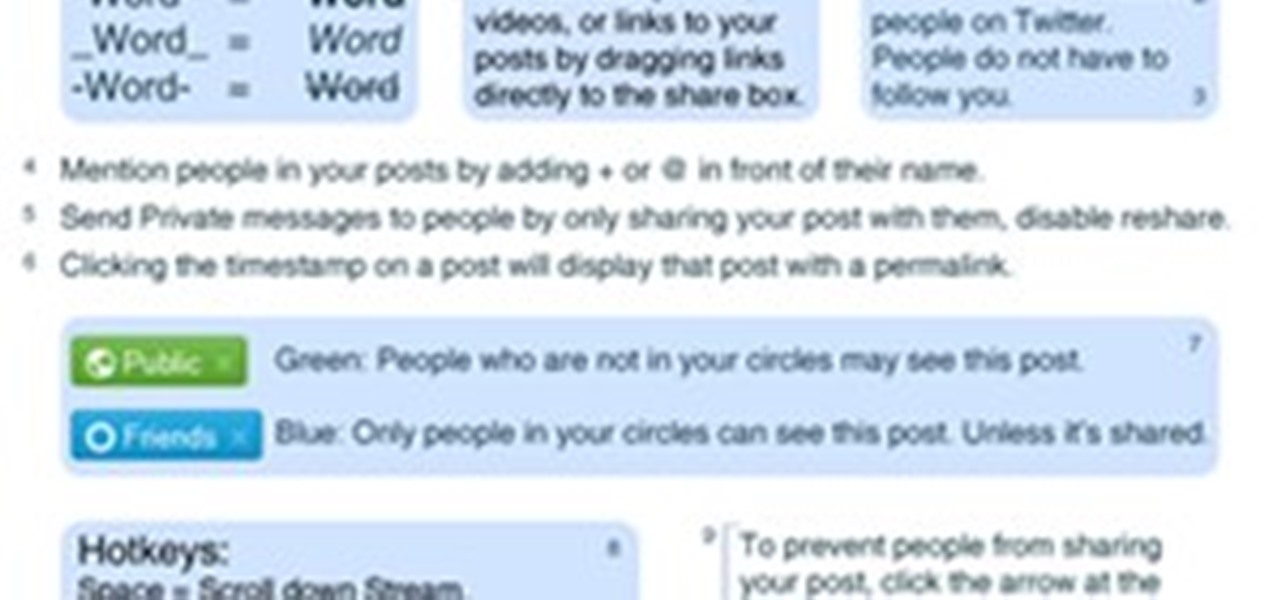
With the Google+ team members being generous and free-flowing with advice on some of the more advanced features of Google+, we'll be publishing a weekly summary of the latest pro tips. Chances are, if you've been following the Google+ team members, you've seen some of these already but you don't have them all in one handy place.

Over the past few months I've written up several helpful How-To guides to help you with various FarmVille related issues. It's about time I put them all in one place so they are easy to find, learn from and share! It has been a pleasure writing for you all and I do hope I have helped you find ways to meet your personal gaming goals!

OSPD1 In 1978, the first SCRABBLE Dictionary was conceived and published by Merriam-Webster, with the help of the National Scrabble Association (NSA). The idea was to include any word that was found in one of the five major dictionaries at the time:

Wouldn't it be nice to just sit at your buddy's house, plug into his network, and see exactly what he's doing? What if it was as easy as that? What makes packet sniffers like Wireshark such potent tools is that a majority of local area networks (LANs) are based on the shared Ethernet notion.

By Ethical Traveler As the world becomes ever more interconnected, being an ethical traveler becomes both easier and more urgent. Travelers today have access to far more information than we did even 10 years ago. We can observe–almost in real time–the impact that smart or selfish choices, by governments and individuals, have on rainforests and reefs, cultures and communities.

Facebook's mobile app lacks many features from the desktop site. Even if you open Facebook in your phone's browser and request the desktop version, all that does is basically resize the mobile app. But there's a simple workaround that will force Facebook to appear in all its desktop glory on your mobile browser of choice.

As much as streaming services like Apple Music and Spotify have dominated the music industry, radio is still alive and well. And why wouldn't it be? Free music, 24/7? It's a great deal. That's why it's so cool that your iPhone can instantly tune in to your favorite radio station, even one across the country.

I use my iPhone's personal hotspot all the time. Whether I need a connection on the train, in a coffee shop with no Wi-Fi, or when my friends don't have service, my personal hotspot is a lifesaver. But all that data comes from somewhere, of course, that somewhere being your cellular plan. Luckily, you can see how much data your hotspot has used, as well as who or what used more of it.

Apple has revealed software improvements and new hardware users can look forward to today, including a new and improved Control Center for iOS 11. This recent announcement shows that the Control Center will now be consolidated into one panel as opposed to two, and all commands will be displayed by small icons.

Notes for Gmail now allows you to insert sticky notes directly onto your email threads in Chrome. The browser extension, currently in beta, allows you to annotate your emails as a whole (thread)—or individually. You can add as many sticky notes as you would like and they all appear at the top of the webpage for easy accessibility. To download the application, go to this page and request an invitation. They add users everyday—I was added almost instantly after I applied. Once you've downloaded...

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

I absolutely loathe it, and I'm certain I'm in the majority, yet we still do this nonsense every year. Take one day and make it to where every headline you read and every link you click are completely useless. Slap a bunch of corporate logos on last year's memes and pollute feeds everywhere with astroturfed ad campaigns.

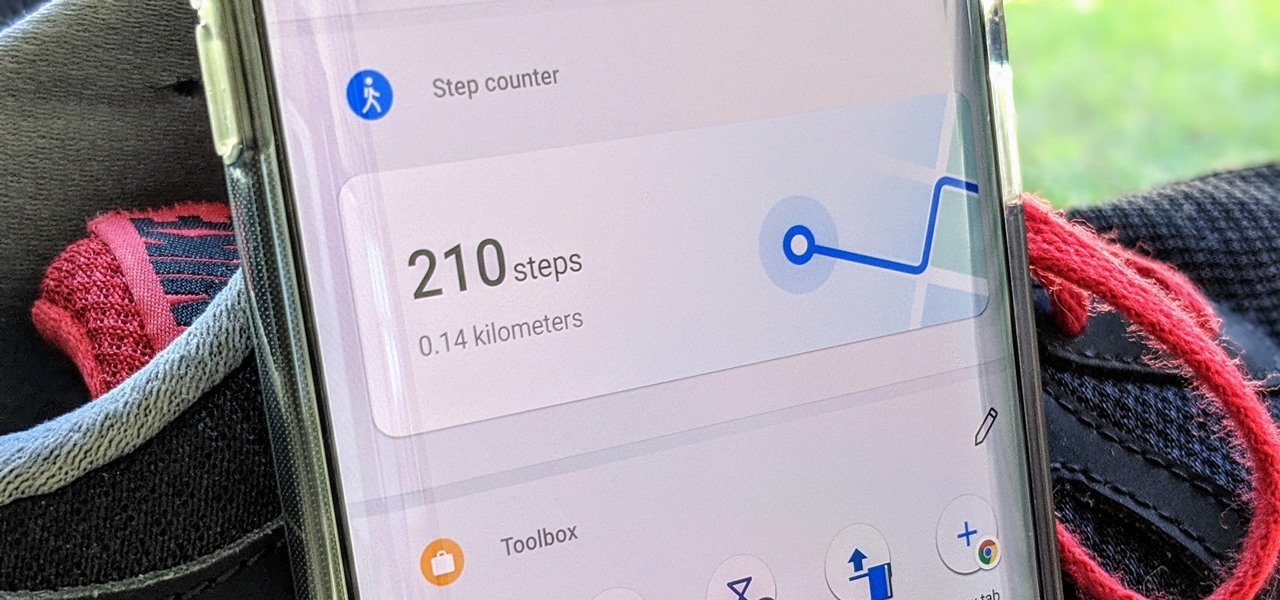
A great way to incorporate a healthy exercise routine is by taking lots of steps throughout the day. While most smartphones can track and report your steps via a third-party app, you can check them right from your home screen if you have a OnePlus phone.

The motivation for the Add Shadow command, according to sources at Macromedia, was in response to a popular enhancement request to add "perspective shadow-like" capability to Fireworks. In this Fireworks 8 video tutorial you will learn how to use distort to add perspective shadows to your objects. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Add perspective shadows in Fireworks 8.