A long-standing request for the iPhone has been a way to quickly browse and connect to available Wi-Fi networks and Bluetooth devices without having to dig through the Settings app. With iOS 13, Apple has finally built this essential feature into Control Center, giving you quick access to wireless settings from anywhere, including the lock screen.

After years of user complaints, Samsung is finally letting us remap the Bixby button without the need of a third-party app. The new feature requires One UI a simple app update to Bixby, but there's one major downside: Samsung won't let you remap the button to open other digital assistants like Amazon Echo, Microsoft Cortana, and Google Assistant. Luckily, there's an easy workaround.
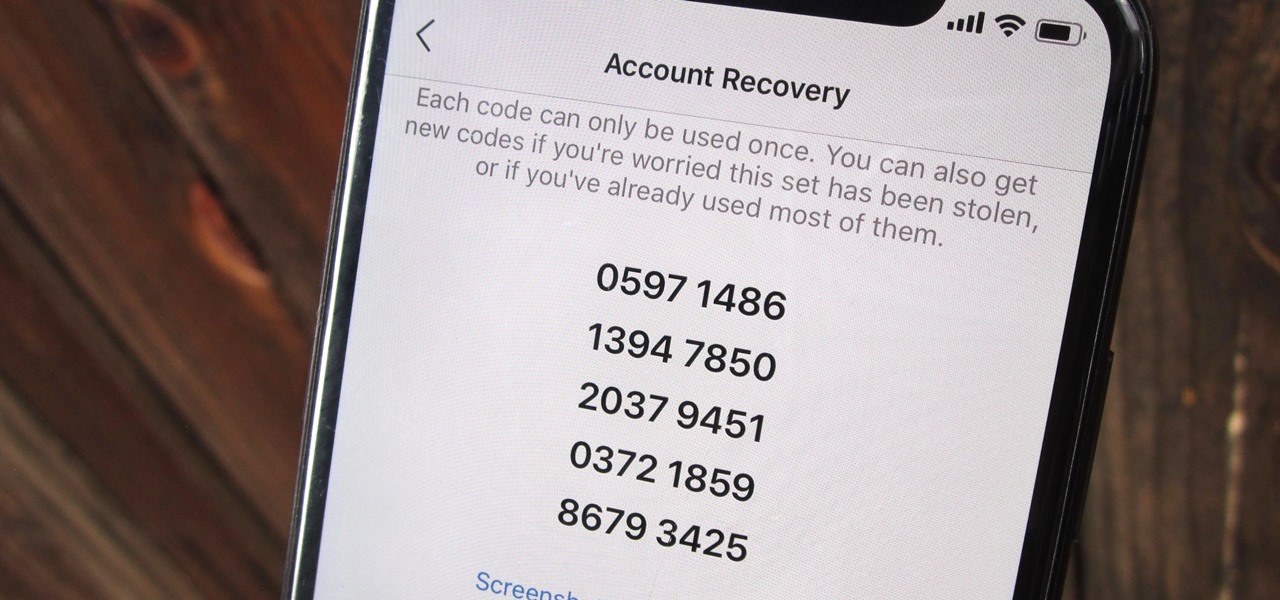
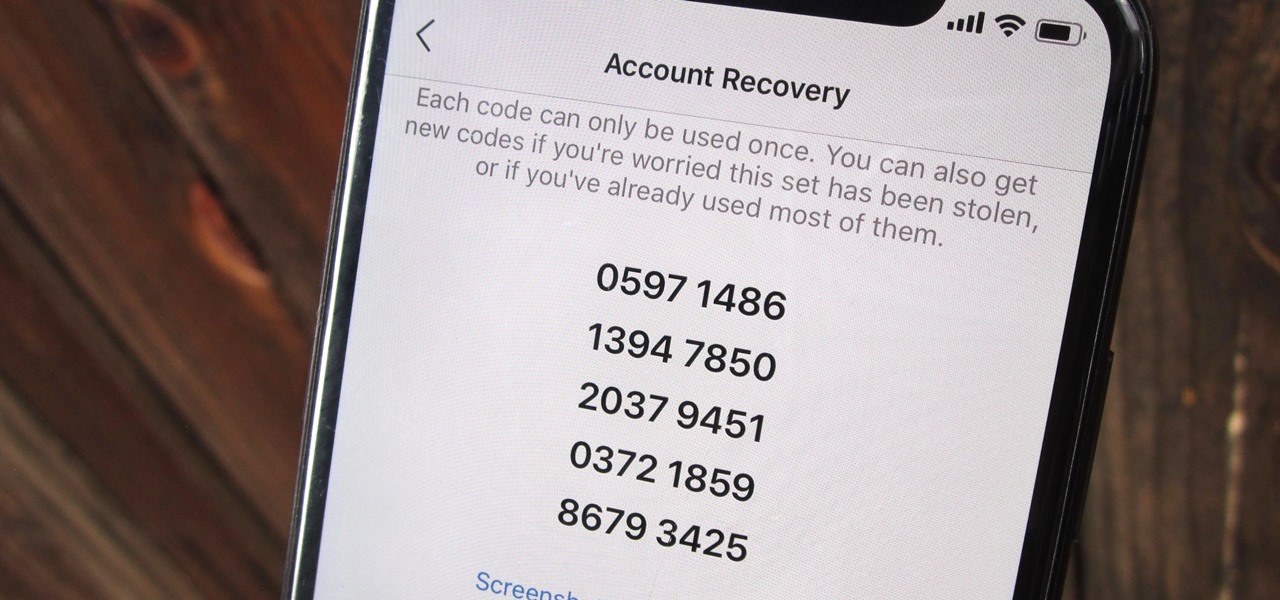
Two-factor authentication (also known as 2FA) adds a necessary additional layer of security to your username and password in many important apps. On Instagram, 2FA requires you to confirm it's you attempting to log in, with a special code sent to you via text message. Enter the code and you're in ... but what happens when you need to log in and don't have access to your phone?

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.
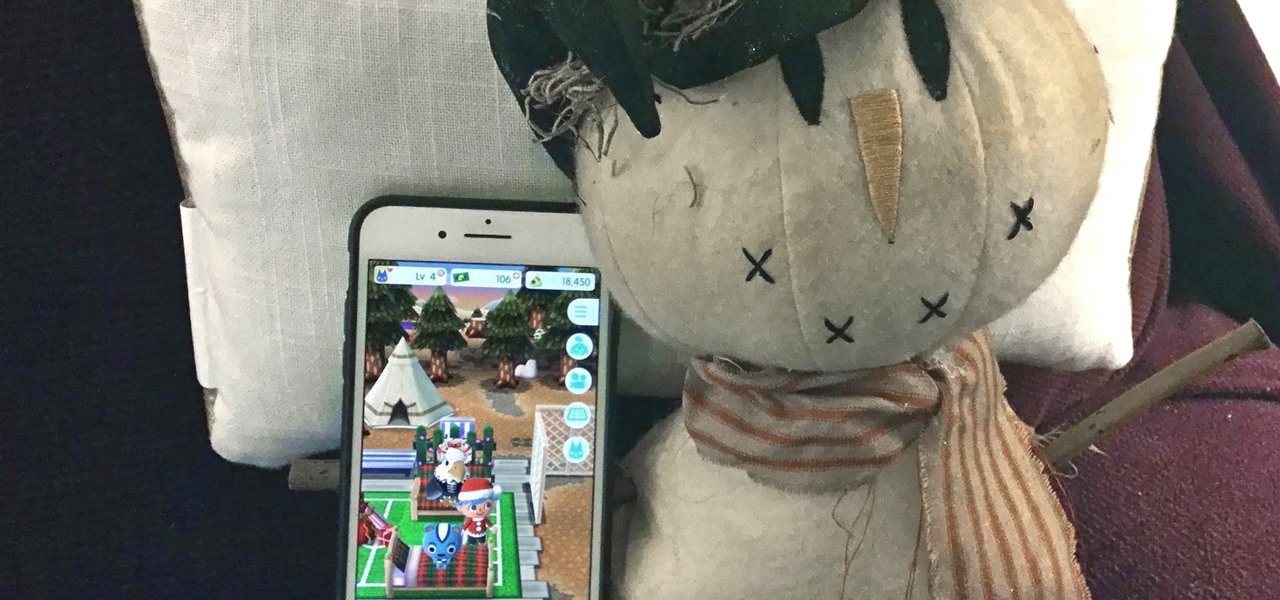
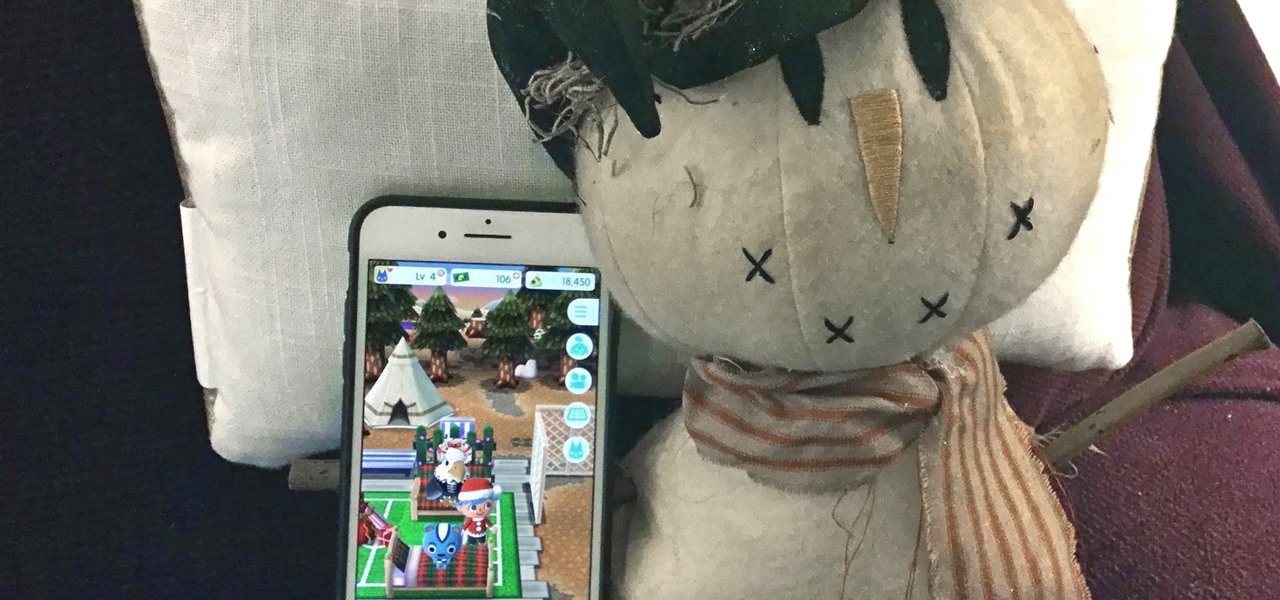
Just over a week after debuting, Animal Crossing: Pocket Camp received its first-ever event geared toward the winter holiday season. With the ability to craft Christmas-themed goodies and own a full Santa suit, it's the perfect time to jump into Nintendo's latest hot mobile game.

Crafting is an important aspect of Animal Crossing: Pocket Camp, as it helps you get animals to come to your campsite. However, it's also one of the best ways to get ahead in the game, and there are a number of reasons for this.

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

The iPhone 8 is just about here. If you're anything like me, you can hardly contain your excitement. Apple has been keeping its 10th-anniversary device — whether you call it the iPhone X, iPhone Edition, or iPhone 8 — as secret as possible, but this past year we've seen a waterfall of leaks. Now that all of the rumors are out of the way, we're finally going to see what's actually in store for Apple's newest iPhone.

Elon Musk's SpaceX is launching the world's most powerful rocket. The Tesla founder and CEO says the company is about to go through "manufacturing hell" to make delivery schedules for its new Tesla 3. Somehow, Musk says Tesla will offer Level 5 driving (so you can take a nap while your car drives you to and from work) within two years.

When you think of AR experiences, you typically think of something that either involves a headset or a handset. Augmented reality without either of those things has seemed impossible in the past. But if anyone is going to try to find a way to have an augmented reality experience without electronics, it's Disney.

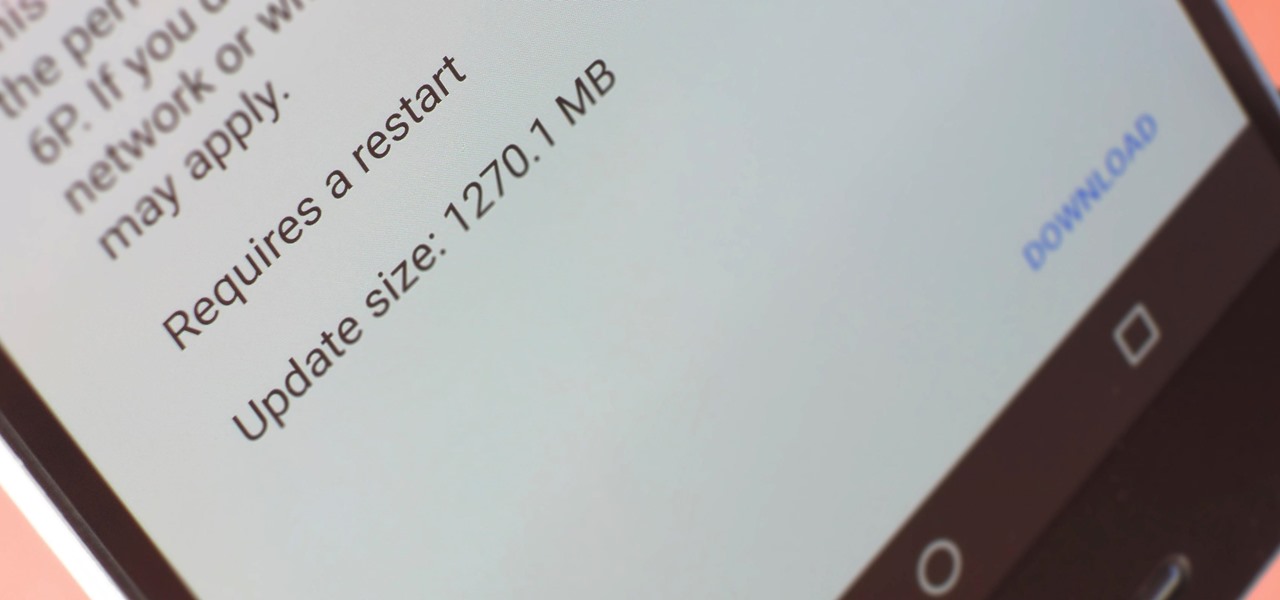
A groundbreaking new Android feature called seamless updates was announced at Google I/O 2016. No longer would we have to wait for updates to download and install — instead, they'd be applied silently in the background, and the new Android version would be waiting on us the next time we restarted our phones.

The latest iteration of the gaming classic, The Sims, has arrived as a soft launch for both iOS and Android in Brazil. Aptly named The Sims Mobile, this free-to-play game seems to be very faithful to the PC-based version that won it so much acclaim. There are plenty of things to do in The Sims Mobile besides the usual home and character customization, and the game also lets you interact with real life friends to fully experience its virtual world together. Maintaining relationships, whether r...

If you've seen, heard, or even tried the latest virtual reality headsets, you've probably heard about something called "room scale." It's why the HTC Vive suddenly usurped the reign of the Oculus Rift while no one was looking, and it's exactly where Oculus hopes to catch up. Here's what it is and why it matters.

Microsoft enjoyed a few months in the spotlight after releasing the developer version of the very first mixed reality (MR) headset, but now we're starting to see the competition jump in.

Vacuum sealers keep food fresher longer by first removing the air from plastic food preservation bags and heat sealing the bag to keep air out. They have rapidly become a popular way to keep your frozen food fresh.

How's it goin'? In this tutorial, we will learn about the security issues of the popen and system functions. I've seen a few people attempting to run command line utilities or whatever it is they require with calls to these two functions but may not know the security implications which come along with it. I will show you using an example from the wargame IO Smash The Stack.

Welcome to a tutorial on crypting technology. In this article, we will be discussing types of crypters, how they work and why they work. After defining these, we will then make our own basic crypter using the function I gave to you as a task to complete by yourself in the previous tutorial.

I saw many people asking for a Tutorial about writing their own Remote Administration Tool, so I now introduce you in a basic kind of RAT. This program is not for real use, but for learning how you could write this kind of tool. It will be basicly coded and not very refined. I used Python 3, so you have to install it if you want to use this program unchanged. Also this RAT is for Windows and almost all features won't work under Linux.

This is my first How-To on Null-Byte, so I hope it's not too complicated written, because I am not a native english speaker. I don't use pictures, but this Tutorial is a good supplement for my updated Tutorial here.

Simmering or poaching food is a total pain sometimes. The problems are numerous: a layer exposed to air often dries out and creates a gross skin that can ruin the texture of the sauce, the poaching liquid evaporates too quickly and causes the poached protein to burn, and so on.

There's only one day that can top the aftermath of Easter and its copious amounts of leftover candy, and that is November — the day after Halloween. As you come down from your sugar rush and realize you now own more chocolate than your stomach can physically hold in one sitting ... fear not! Here are several ways to turn your Halloween chocolate into delicious snacks and desserts that you can enjoy at your leisure.

Many home chefs are deterred from whisk-intensive recipes such as mayonnaise because they seem to require more than two hands—which is obviously the maximum number we possess. One hand is required to stabilize the bowl, another must be whisking constantly... and a third hand is needed to pour a steady stream of oil.

If you ever need to spice up a party, drinking games can really get things started quickly. The objectives are generally to complete tasks or challenges, but it's really all a thinly-veiled excuse for increasing everyone's alcohol intake in a hurry while testing levels of inebriation.

If your Android device wasn't manufactured by Samsung, chances are it uses on-screen navigation buttons. Colloquially referred to as "Soft keys," these have become commonplace due to their flexibility, as well as the fact that manufacturers don't have to include extra hardware buttons with a propensity to fail.

Most mobile games have moved to an online-only format, meaning you need to be connected to the Internet in order to get any kind of multiplayer action going. This is great when you're at home on Wi-Fi, but when you're out and about, slow and inconsistent data speeds can cause serious lag. Or worse yet, you may be nearing your monthly data cap!

Whether it's terrorism or brain-hungry zombies you're neutralizing, first-person shooters are an awesome way to immerse yourself within a new world and kill some time with your iPad or iPhone. And with so many games available in this genre, we wanted to show off ten of our absolute favorites.

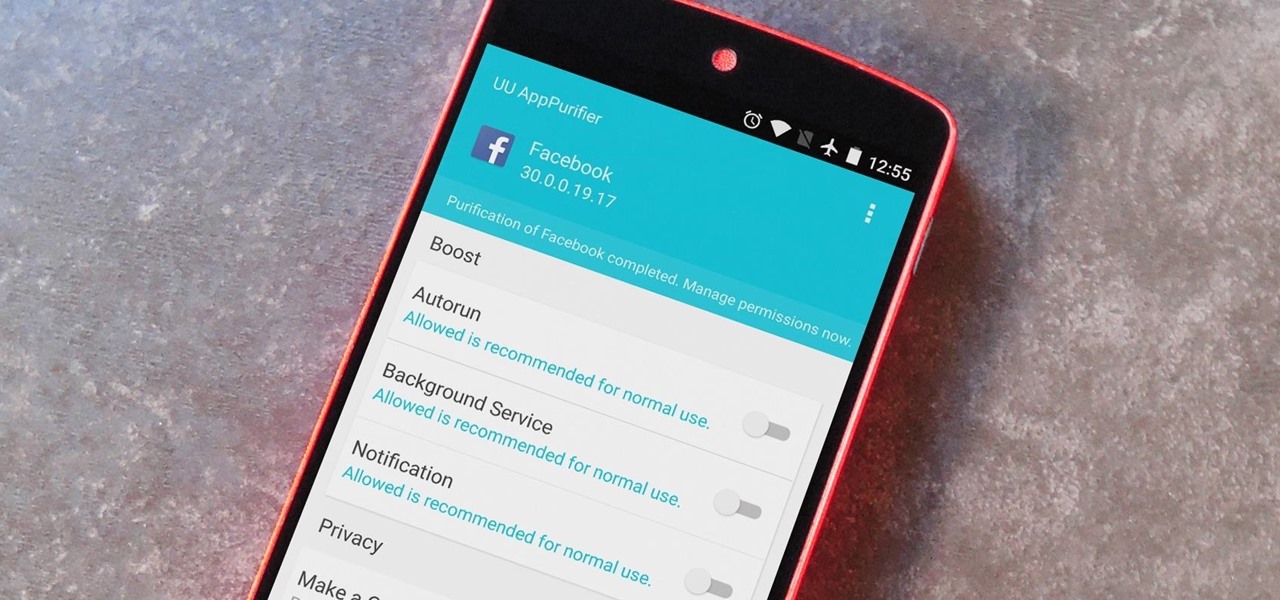
When it comes to app permissions, Android takes an "all or nothing" approach. You have no granular control over what data apps can access, so the only way to prevent an app from seeing your location or starting up on boot, for instance, is to not install the app in the first place.

So you've fallen for many pranks on April Fool's day and surely you feel like a "fool" well it's time to dust yourself off and start pulling pranks of your own on those that got you earlier. Here are 5 pranks you can set up on your enemies on April Fool's Day.... Most require the use of household items which you might already have. Check out the video tutorial provided for further instructions!

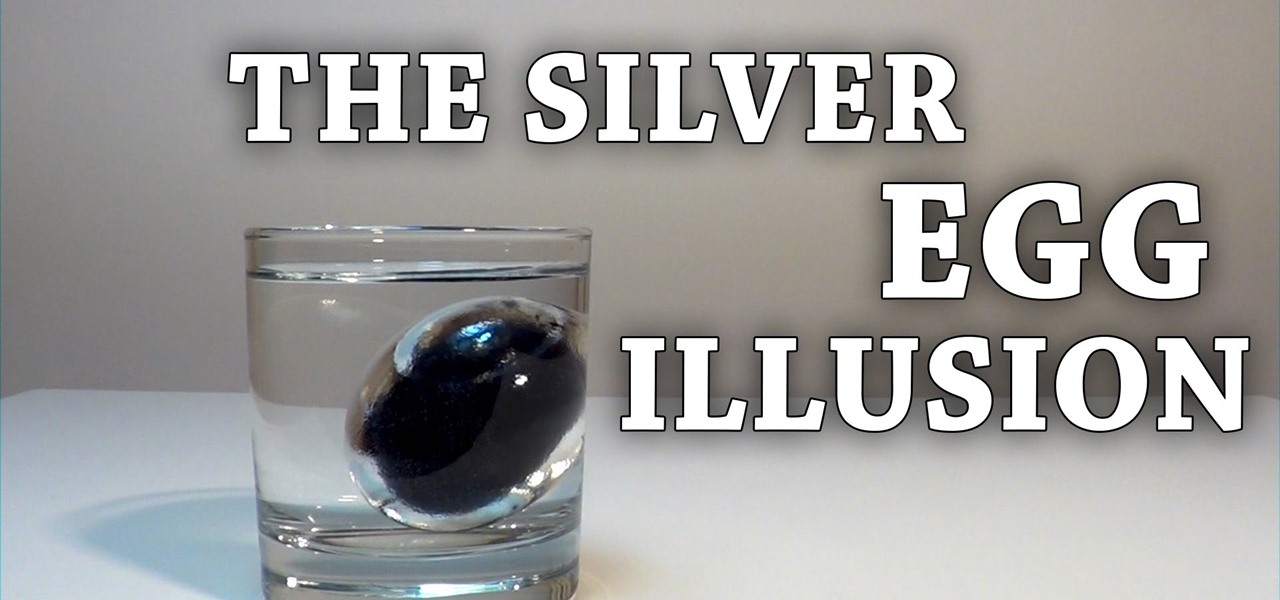
This requires a dry hen's egg at room temperature. Hold an egg near a candle flame to cover it with soot. It will need to be completely covered. This is tricky, because if the egg is a tiny bit damp the soot will easily flake off on to your fingers as you turn the egg. Once the egg has a nice black sooty coating, gently immerse it in a bowl of water.

Willpower is a pretty significant word. It's the difference between sticking with a clean eating diet and diving face-first into a plate of brownies. It's what drags you out of bed on Monday mornings and into work rather than letting you stay snuggled under the covers asleep. And, most importantly, it's the kick in the butt we all require to both accomplish goals and make changes.

Making a cool leather wallet is easy. Just get yourself some scrap strips of leather ant you are good to go. No special tool required. You can see full process of making this simple wallet in the video.

To play Minecraft with mods you will need to install Forge. Most people think this is hard to do, not so. It is very simple and in less than 5 minutes you can be playing Modded Minecraft.

Alas, I have never tasted an authentic cronut (croissant-doughnut hybrid) from Dominique Ansel's NYC bakery, only its Los Angeles knock-offs. Ansel is also the guy who created a chocolate chip cookie shot glass and the flambéed ice cream s'more, so clearly he has some sort of dessert-perfecting gene the rest of us lack.

Instagram is not only a great platform to easily share some of your favorite moments with friends and family, it's a useful service for peering outside of your physical location. While you share a picture of your dog in Los Angeles, you can almost instantly view and like a picture someone posted of their breakfast in Tokyo.

The use of smart phones is not limited only as a mode of communication now-a-days. There are many things that can be done with the help of a smart phone.

Much like the built-in screen recording tool on Android 4.4 KitKat, hidden features like the new battery Status bar icon must be manually unlocked on your Nexus 7 tablet. This is both exciting and annoying.

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

If there's one way to get a visceral response from someone, it's bringing up the DMV. Regardless of the reason, whether it's the long lines, disgruntled employees, or just general inefficiency, I have yet to meet a single person who doesn't mind the trip. Just look at all those happy faces.

This is a video by Tinkernut on How to Make a Chrome App in 5 Minutes. Making a Chrome App and an Extension is actually a fairly simple task. All you have to know is a few required fields and the JSON syntax.

Internet slowing down, requiring you to Press F5 several times to refresh a web page is one of the irritating thing a computer user can come across. It needs to be fixed asap.