The pandemic has forced a number of public-facing businesses to either temporarily close or permanently cease operations, with one of the biggest victims of this trend being the movie theater business.

Who had Lil Nas X, blood-drop Nikes, and satan worship on your 2021 bingo card? In a story that's stranger than fiction, the "Old Town Road" rapper has ruffled some feathers with the video for his new single, "MONTERO (Call Me By Your Name)" filled with demonic imagery usually reserved for death metal bands.

With NFTs taking the art world by storm, it's a bit refreshing to know that you can enjoy world famous masterpieces in the comfort of your own home via augmented reality without emptying your cryptocurrency wallet.

After years of testing and modifications, the US Army is moving forward with its customized version of HoloLens 2 from Microsoft.

Mobile augmented reality gaming pioneer Niantic is chomping at the bit to get games like Pokémon GO out of smartphones and onto smartglasses, and it appears to be taking matters into its own hands.

With non-fungible tokens (NFTs), particularly those that are 3D in nature, holographic displays are becoming more indispensable for those looking to show off their valuable works of art.

What is old is new again. In this case, a classic arcade game gets the augmented reality treatment. In a new promotion playing off its ad campaign featuring actor Craig Robinson (The Office, Hot Tub Time Machine), Pizza Hut has turned its pizza boxes into a virtual Pac-Man game via web-based AR technology.

Google Poly, a repository of 3D objects for use in AR and VR experiences, is the latest Google offering to fall victim to the company's habit of axing products and services, regardless of popularity.

The moment many of the crypto savvy insiders in augmented reality and VR have been waiting for is here: we're finally getting our first big auction of NFT art that exists purely as a hologram.

In response to Apple's implementation of LiDAR sensors in iPad Pro and iPhone 12 Pro models, Google is looking to leverage the dual-camera setups in recent flagship devices as depth-sensing components.

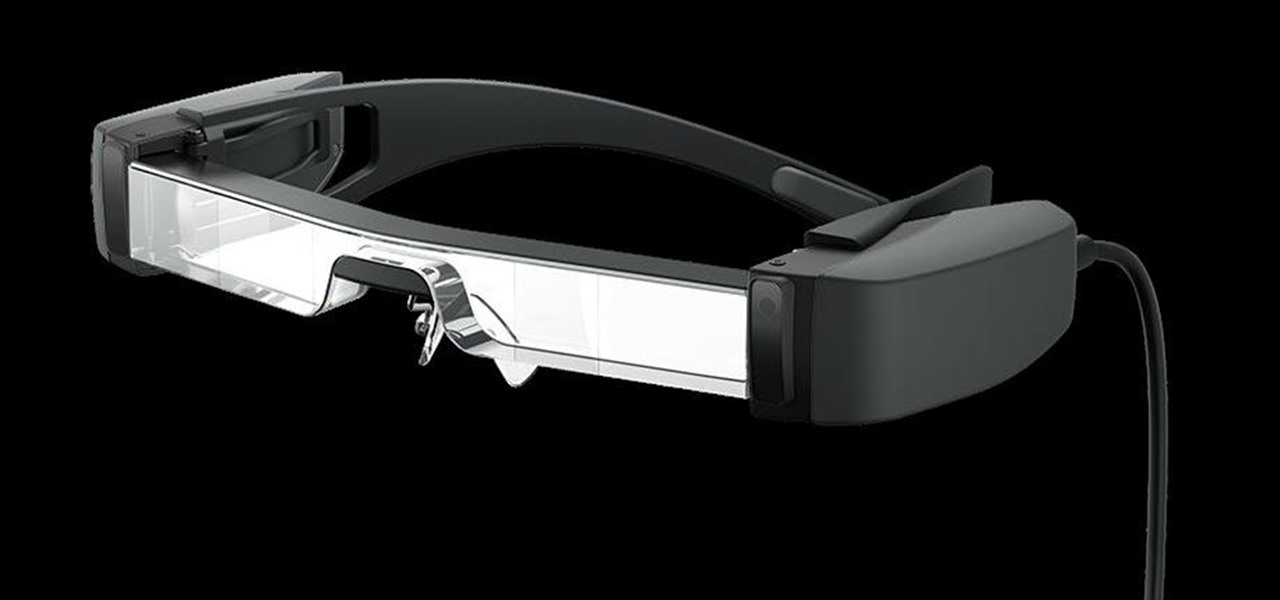
The average business person likely recognizes Epson for its printers or even its projectors, not the futuristic AR wearables.

The new WandaVision series is perhaps the hottest TV show on the Disney Plus streaming service since...well, its own The Mandalorian wrapped up its second season late last year.

Roughly a year ago, Samsung demoed its AR smartglasses prototype on stage at CES 2020. Now, videos showing off a new smartglasses model along with the company's imaginings of future AR experiences have surfaced through unofficial yet reliable channels.

A year and change into its shift towards enterprise customers, Magic Leap has updated Lumin OS and the corresponding Lumin SDK with some key prerequisites for the business sector.

Two years ago, the 50th anniversary of the moon landing gave flight to a handful of Apollo 11 augmented reality apps and experiences, including one from the Smithsonian Channel.

The realm of science fiction isn't all lasers and cute green toddlers, sometimes alternate science history is sci-fi, too, as exampled by the Apple TV Plus series For All Mankind.

In the three years since Snapchat launched Lens Studio, developers and artists have created more than 1.5 million AR camera effects with the desktop tool.

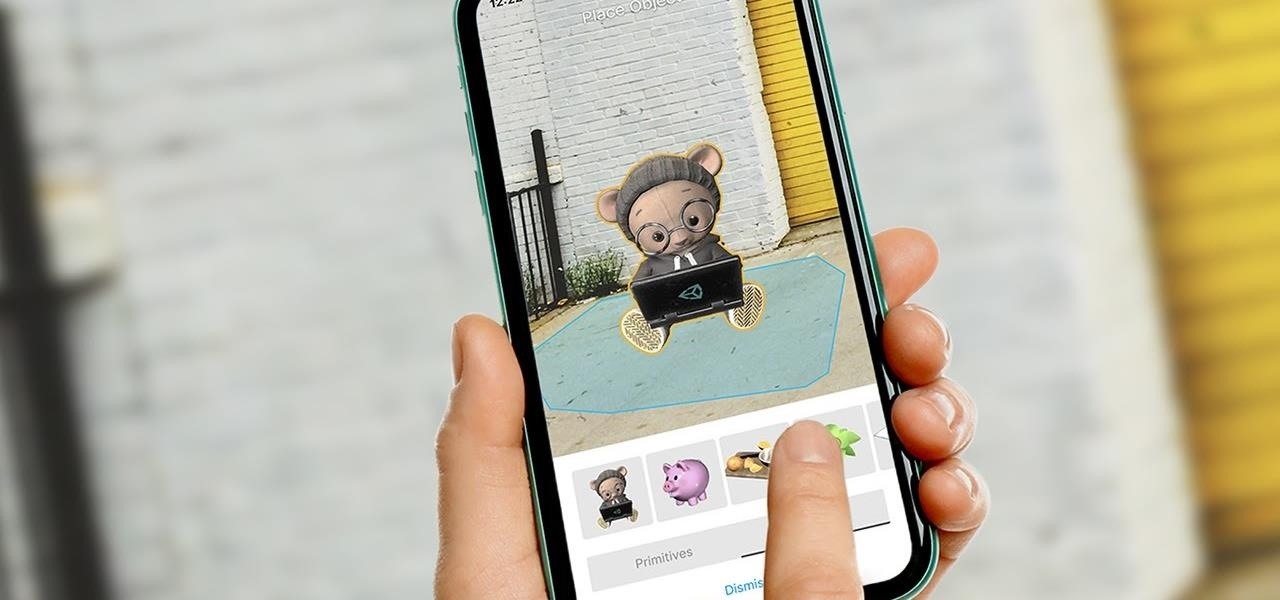
Unity often reminds us that the majority of AR apps and experiences are built with the Unity 3D engine, and now the Unity MARS service, which facilitates easy AR creation for seasoned coders and newcomers.

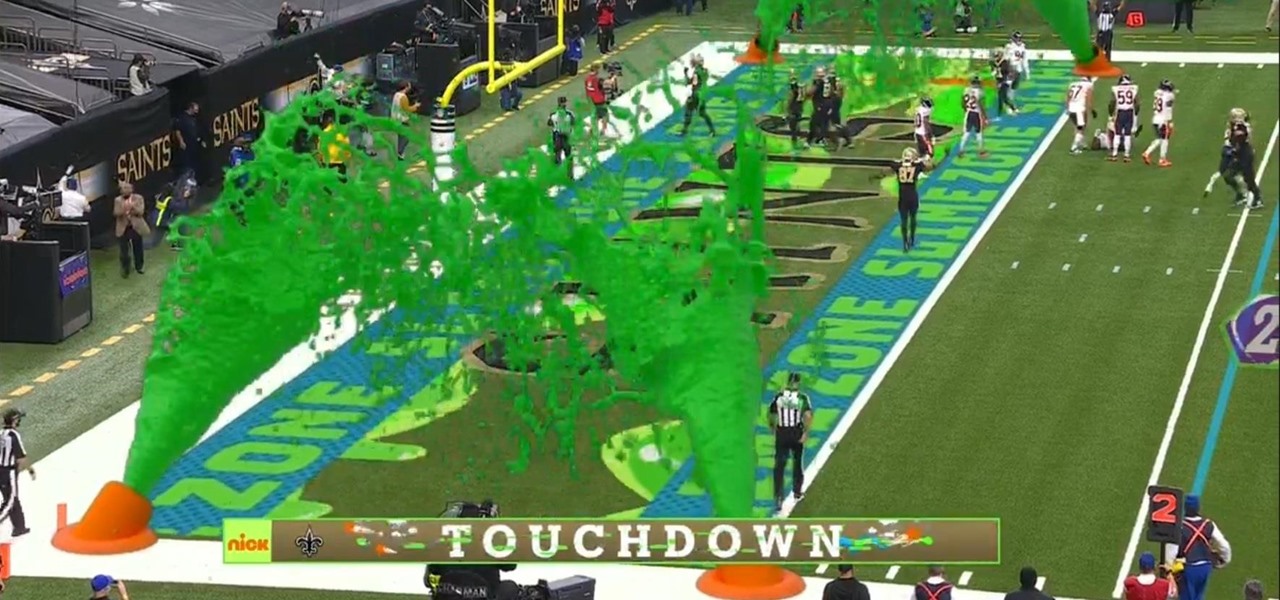
I must admit, upon learning that the NFL was broadcasting the contest between the New Orleans Saints and Chicago Bears on CBS, Amazon Prime Video, and Nickelodeon, the latter was the only option I wanted, purely for the novelty of the experience.

The past year has revealed a gaping hole of opportunity in the world of business called virtual meetings. Some existing players like Zoom hopped on that opportunity, while others like Skype seemed stuck on the sidelines, and Google Meet just managed to catch up in time to snag some of the shift in remote work.

Now that 3D display maker Looking Glass Factory is closing in on $2.2 million raised in its crowdfunding campaign for the consumer-grade Looking Glass Portrait device, the company now has a 3D content generator to go with it.

A lot of digital ink has been spilled heaping scorn on Magic Leap. Much of that media schadenfreude was due to what some believed were unmet promises versus some of the early hype around the product. Others just seemed to be rubbed the wrong way by the startup's Apple-esque secrecy and penchant for attempting to coin new terms and frameworks for things that were, mostly, already in play.

The economic impacts of the COVID-19 pandemic have been felt in practically every business sector. Now, as we look back at the top augmented reality investments of 2020, the AR industry has been no exception.

At the opening of its virtual Lens Fest, taking place Dec. 8-10 and open to the public, Snap is furthering its facilitation of AR development with new tools for Lens Studio version 3.3 and a planned investment into its AR creator community.

With the new season of The Mandalorian underway, Google has launched a new AR app that enables some Star Wars fans to connect with virtual characters in between new episodes.

Niantic recently added a new Field Research task type called AR Mapping that challenges players to capture video footage of PokéStop landmarks and upload them. In return, players receive rewards in the form of in-game items.

This week, developer Niantic began rolling out a new feature called AR Mapping to Pokémon GO that has bigger implications on the realism of augmented reality in mobile gaming and beyond.

For the most part, new features for Google Maps, such as Live View augmented reality walking navigation, come to Android first.

With protests springing up across America, there's a chance you may have your first interaction with law enforcement. Many demonstrators will have their phones in-hand to film the action, which, sadly, could prompt an officer to demand the device and any self-incriminating data it may contain. Before this happens, you should know there are tools at your disposal to protect your data in such situations.

If you're considering purchasing Apple's new 2020 iPhone SE, which brings many modern components into the compact body of an iPhone 8, you should know what its dust and water resistance rating means. Just how dirty and wet can the iPhone SE get without breaking any functionality?

The response to the COVID-19 pandemic means that social distancing has become the new normal. It also means that more Americans are using video conferencing to connect with colleagues working from home or friends and family in quarantine because of the new coronavirus.

There are times when leadership is tested. This is one of those times. As government and business leaders around the world are grappling with the unfolding coronavirus pandemic, the real-time responses to the crisis from many leaders have been great and, at times, less-than-optimal.

We've been so worried about volumetric scans possibly robbing celebrities and performers of their agency and right to control their image that, somewhere along the way, we forgot that scans may not always be necessary to produce passable holographic performances.

Whether you call it the foot shake or foot dance, videos of people tapping their feet together have been and still are blowing up all over TikTok. If you want to get in on the action but can't follow along with all of the fast-paced TikToks, we'll slow it down a bit for you and a friend.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

While MacOS computers have been spared from some of the most famous malware attacks, there is no shortage of malicious programs written for them. To keep your computer safe from some of the most common types of malware, we'll check out two free tools. These tools can automatically detect ransomware encrypting your files and watch for unauthorized access to your microphone and camera.

The latest immersive production from Magic Leap Studios finally got its debut on Monday at Siggraph, during which the company also released the app to the general public, so we took it for a spin.

Why do you need augmented reality? Because enterprise, they say. And while that's certainly true for several disciplines, there's still that mainstream use case hanging out there waiting for users to discover beyond the realm of enterprise and gaming.

Despite newer phones having larger batteries, after a few months, my battery life drops significantly. I started researching solutions after my third phone. No matter who I asked, the most recommended solution was always Greenify. And unlike other solutions, you don't need root to use it.

With the new navigation gestures in Android 10, you reclaim a lot of screen real estate that used to be occupied by the back, home, and recent apps buttons. But there's still a small bar on the bottom edge of the screen, and in most apps, it still sits atop a black background. Thankfully, an easy hack will give you true full-screen without breaking the new gestures.