Here, you'll be shown how to revert your Windows Vista computer back to its factory settings, if you get stuck with a bad virus or anything else like that. Make sure to back up all of your important data before you decide to go back to the original factory settings, as you don't want to lose that precious data. After a quick backup, we'll run through the options from start to finish. We will run through a few restarts of the system, and then show you the easy path to getting your system back ...

This is a Slide Tutorial for the Melbourne Shuffle. Start with the Running Man. You are doing the Running Man & you slow down/ change your movements. This tutorial demonstrates by mixing the slide with the Runningman & T- Shuffle.
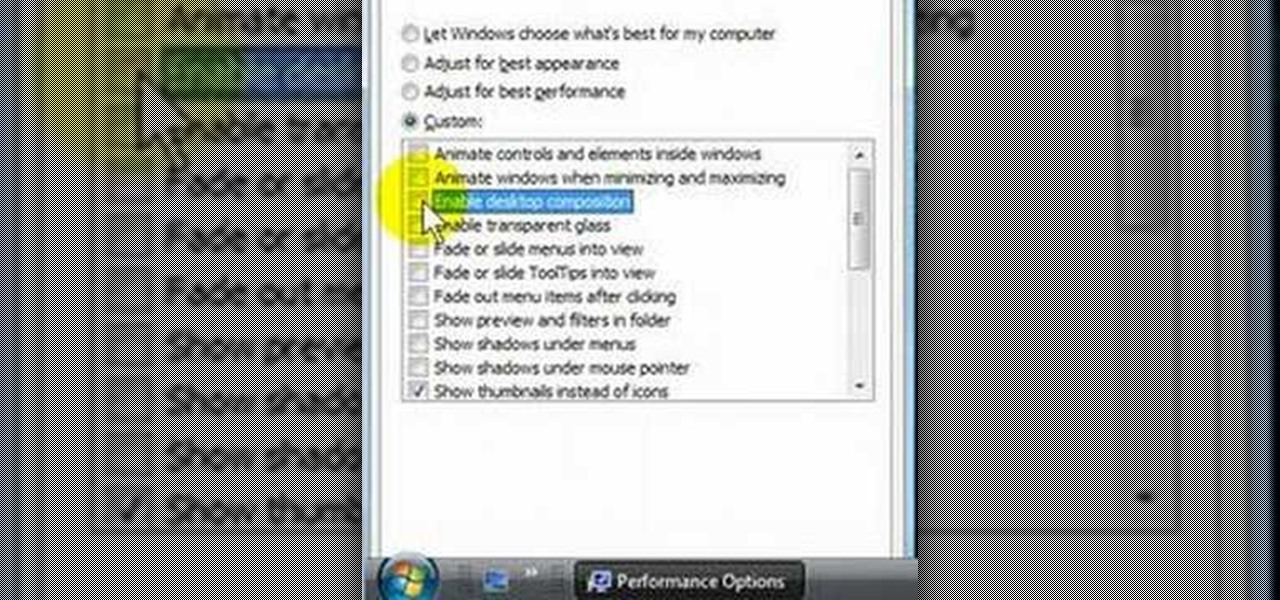
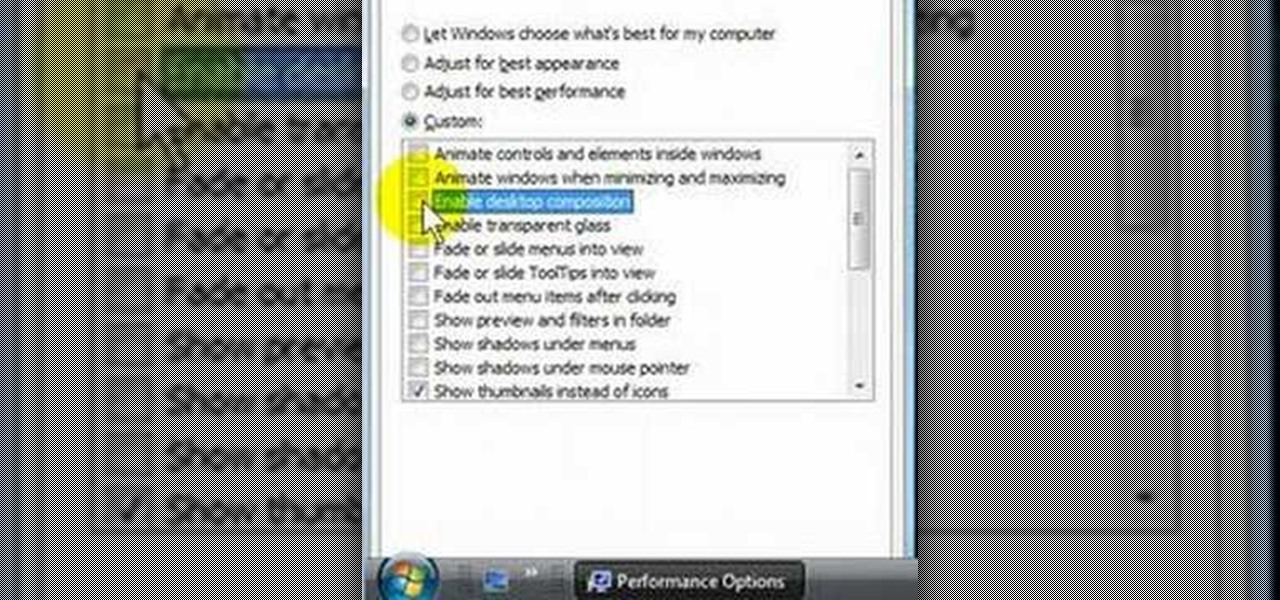
Are you disappointed with the sluggishness of Microsoft Windows Vista? In this Windows video tutorial, you'll learn how to use the Performance tool in Windows Vista to disable senseless features you don't need and to make Vista run more quickly in the process. For more, or to get started speeding up your own Windows Vista machine, take a look!

This tutorial Korean cooking video will show you how to make "gye ran mal yee" (rolled omelette) and "gye ran jjim" (steamed egg) some basic Korean egg side dishes.

In this how-to video you will learn to do a frontflip. This is very helpful for gymnastics and any activity needed to do a front flip. The running front flip is used in Parkour and freerunning for tricks and flips.

Do a running backward drill to improve your biomechanical form. This drill works your glutes and hamstrings. Check out this how-to video for advice on improving your marathon and cross country performance.

Stun run through is the ability to put the right spin and speed on the cue ball that allows you to move the cue ball between 3 and 12 inches.

Parallels Desktop 3.0 for Mac makes it easier to run Windows and Mac OS side-by-side on Intel-based Mac hardware. It adds support for 3D graphics, which lets you play some but not all PC games.

Learn how to modify the IDE cables in your PC to get your PC to run cooler. You'll also get a more functional look inside of your computer as well.

Run-in-place is another great defense drill geared at conditioning your players and increasing their overall skill on the basketball court.

Learn the correct form for running the "Back Pedal" drill around half the basketball court, then learn the correct way to warm up with this backward running drill.

Learn how to employ simple plyometrics with box jumps and box runs in order to build up speed, power and athletic ability on the soccer field.

Learn the art of running whilst in downhill conditions during a cross country race.

Here's how to install and run a Gameboy advance emulator to play GBA games on your PC. Please note that downloading ROMs for games you do not own is illegal.

This Pamie Demo shows how to setup, install and run a simple automation script. It shows you: how to install Pamie, how to create a Pamie test script to Automate a form using PythonWin IDE, how to write the script and how to run the test. The volume is really low so crank your speakers way up and make sure you have the proper Python and programs downloaded.

This video demonstrates how to run a scandisk in Windows XP. To do this, just right click on your c: drive and select properties, click the tools tab, hit check disk and click ok.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

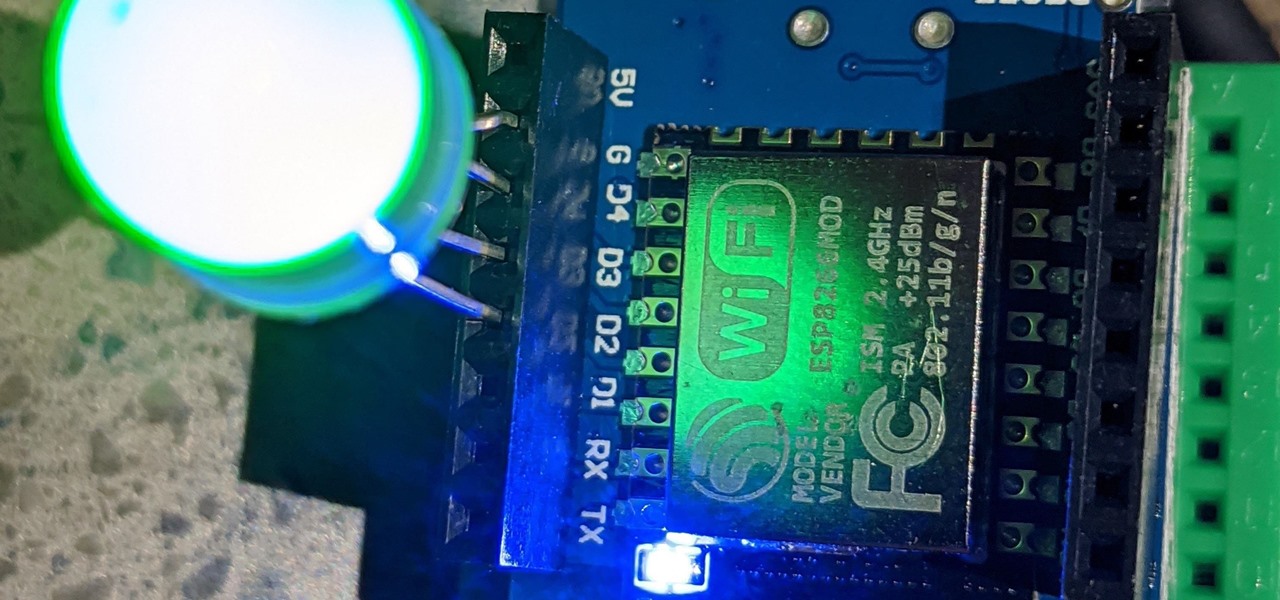
For anyone interested in using cheap, Wi-Fi-connected microcontrollers like the ESP8266, the Arduino programming language can be a barrier to entry. Based on C++, Arduino requires knowledge of more computer science than languages like Python. Fortunately for beginners, setting up MicroPython on an ESP8266 allows anyone to write Python on affordable microcontrollers in a matter of minutes.

One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform the brute-forcing process, but not all are created equally.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

Starting Nov. 1, 2018, Google got a lot tougher with Android app developers. New apps being uploaded to the Play Store already had to target Android 8.0 Oreo or higher as of August, but now, every update to existing apps has to do the same. It may seem like a simple rule, but it will have some serious repercussions.

While fully closing apps on your iPhone can keep it running at peak efficiency since it frees up memory and stops background refreshing, it's most critical when dealing with unresponsive apps. If you have an issue with a certain app, you can just force-close it instead of rebooting.

RouterSploit is a powerful exploit framework similar to Metasploit, working to quickly identify and exploit common vulnerabilities in routers. And guess what. It can be run on most Android devices.

The Operative Framework is a powerful Python-based open-source intelligence (OSINT) tool that can be used to find domains registered by the same email address, as well as many other investigative functions. This reconnaissance tool provides insight about your target through examining relationships in the domains they own.

Great news, zombie killers! Zombie Gunship's long overdue sequel, Zombie Gunship Survival, has finally arrived for iOS and Android devices as a soft launch available for download in the Philippines—which means that with a little tinkering, you can play the new game in any country.

Super Mario Run has been one of the most insidiously addicting iOS games to come out in recent years for iPhone. And now, as of March 22, Android users can get in on the fun, too.

In the first part of my containers series, we learned how to install Docker on our local machine, pull down "hello-world" and Ubuntu containers, SSH into containers, and install software when in a container. Now, we're going to work on building, customizing, and storing our refined hacking Ubuntu container. Before we dive right in, though, let's make sure we still have a functional Docker installation.

Some manufacturers, like Samsung and LG, have had split-screen multitasking on their custom versions of Android for years. But starting with Android Nougat, Google added this functionality to AOSP, which means that all phones and tablets running Android 7.0 or higher will now have a new multi-window mode.

Hello Friends … My name is Suresh Senarathna and this is my first “How-To” post,

Welcome back, my budding hackers! Digital forensics is one of IT's most rapid-growing disciplines. All hackers should be familiar with digital forensics if for no other reason than to protect themselves. More than one hacker has been apprehended because they were unaware of the evidence trail they left behind.

Although they're often times the primary source of income for websites, on-site advertisements can annoy even the most tolerable reader. That's why ad blockers have been some of the most popular downloads on Firefox and Chrome for some time now, demonstrating that when it comes down to it, most people just want nothing to do with ads shoved in their face.

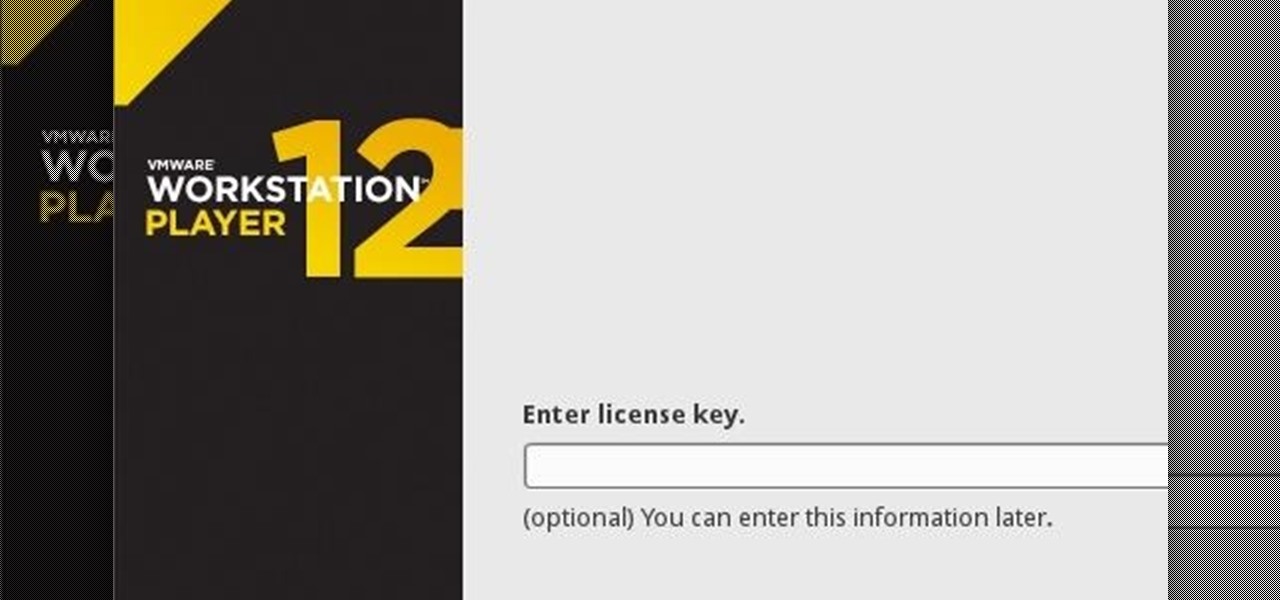
If you have never heard of a Virtual Machine (VM) before you might think it to be some new kind of gamers virtual reality system, and that would be incorrect. A virtual machine is a Virtually a real computer that exists inside of your own computer. You can run Kali inside of a Windows environment via your VM. Not quite the same as an actor portraying an actor on TV. A virtual machine will have it's own IP address and you have the ability to network to it from your Real (Host) computer and bac...

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

OTW's great Tutorial Hack Like a Pro: How to Save the World from Nuclear Annihilation gives me the inspiration to try this on Win7 sp1.

Today we are pleased to announce the end to the Apple vs. Android war. About a year ago, our Gadget Hacks team started working on a top-secret project to dual-boot both Android and iOS on the same phone—and we couldn't be more proud to announce that we've finally succeeded! Your phone can now run both iOS and Android—whenever you want. Right now.

One of the best features of Android is the fact that it's open-source, giving developers the ability to use it on pretty much any device they can think of, like on a Windows PC using Andy. That's what drove the creators behind the Android-x86 project to port over the mobile OS to any computer running an Intel processor.

Say "hola!" to the independent Finnish phone company, Jolla, and its new eponymous smartphone of the same name.

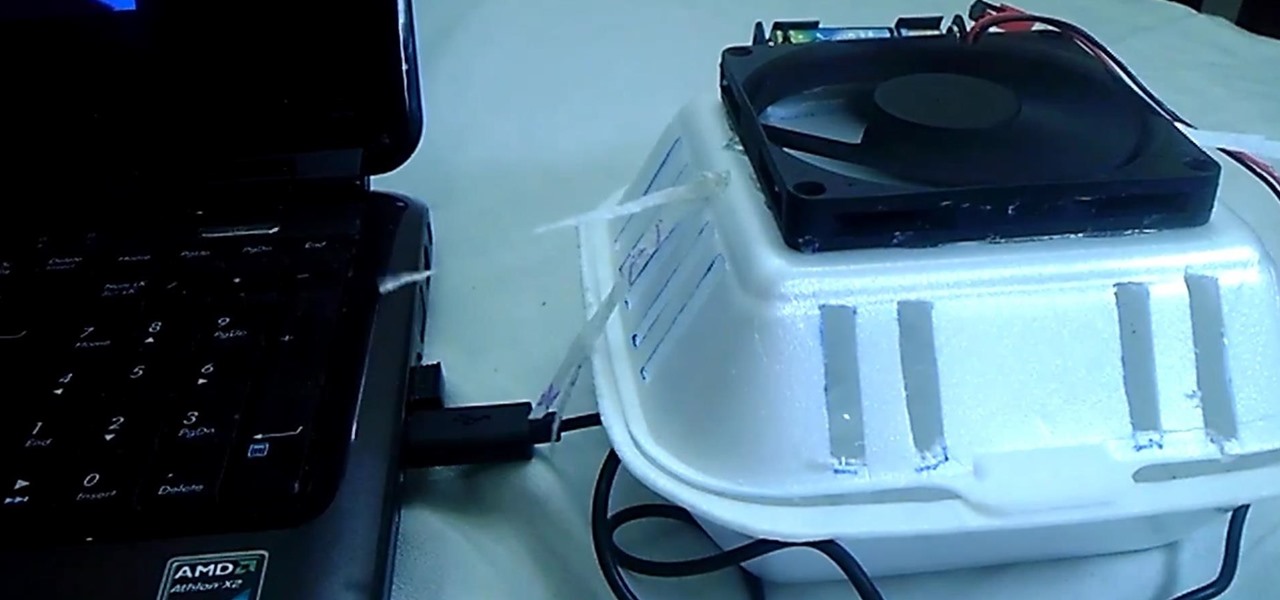
Hand made air conditioner made of a foam lunch box, 5 volt DC fan, 4 AAA rechargeable batteries, and some ice. This homemade AC can run on batteries and you can plug directly into any USB port.