Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers with over 60% of the market. In addition, Linux and Unix servers are the operating system of choice for major international corporations (including almost all the major banks) throughout the world.

Contrary to what you may think, clearing or swiping away apps in the Recent Apps view on your Android device does not necessarily stop app activity or running tasks—and these running processes can actually be eating away at your battery life. Depending on the app or process, it may only be a small percentage, but every little bit helps these days.

A musical hiccup during a DJ's set can completely ruin the mood, and that same feeling can definitely translate to mobile listening as well.

What if someone asks you to do a Nmap scan but you left your pc at home? What if a golden opportunity shows during a pentest but you were walking around the building, taking a break?

This past year, Facebook spent $19 billion purchasing the popular messaging app WhatsApp, and for good reason. Mark Zuckerberg isn't going to spend that type of money on just any application. WhatsApp is widely popular and frequently used by more than 500 million users worldwide, which is almost twenty percent of the Earth's population.

If you want to try out some of the new features in Android L, but can't run the developer preview on your Nexus—or simply don't want to—there's still hope. You don't actually need to be running Android L to try out some of the new improvements.

It's been over three months since iOS 7.1 came out, but your wait for jailbreak is now over. If you're still running iOS 7.0 iterations to maintain your jailbreak, you can now finally update to the latest and greatest thanks to a Chinese team of developers, who recently released their untethered jailbreak for Apple devices running iOS 7.1, 7.1.1, and even 7.1.2.

You send out a lot of emails, but probably get very few responses. How can you be sure those emails are even opened?

When our Nexus 7s upgraded to KitKat, one key piece of functionality was lost in the mix—Flash support. Of course, even before that we never had official support on the Nexus 7, but hacks seemed to do the job just fine. As it stands now, Google remains on the warpath against Flash, opting instead for HTML5 use, specifically in Chrome (where Flash never worked anyway), and of course Adobe stopped supporting Android long ago.

Welcome back, my greenhorn hackers! Earlier in this series, I showed a you a couple of different ways of fingerprinting webservers. Probably the easiest way, is to use netcat and connect to port 80 and pull the webserver banner.

We've always been able to switch between running apps pretty easily, but iOS 7 beefed up the multitasking menu significantly by incorporating app previews in lieu of just icons.

The latest iOS 7.1 update is going to be coming out soon, but from what we can tell, there are still a lot of basic options and settings missing that we iPhone users should have. Some of them are pretty obvious, like being able to delete all of something at once, like notifications, running apps, and messages.

When lending our iPhone to our kids, siblings or friends, it's not uncommon to have it returned with what seems like a million apps open in the background. What's worse is being too lazy to close all those open apps, in turn having our battery drain much faster than normal.

Welcome back, my hackers apprentices! To own a network and retrieve the key data, we only need to find ONE weak link in the network. It makes little sense to beat our heads against heavily fortified systems like the file and database server when we can take advantage of the biggest weak link of all—humans.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

It's fairly easy to switch between running apps on the Nexus 7 by hitting the Recent apps key in the Navigation bar at the bottom of your screen, but for me—it's just not good enough. I don't particularly like leaving the app I'm currently in to see this menu, and the menu itself is kind of clunky, and overall, not as fast as I'd like it to be.

Want the best view of Los Santos in Grand Theft Auto 5 without having to purchase a plane or steal a chopper? You can enjoy the sights of the Los Angeles replica by hopping on one of the trains rolling around the city—and forget about riding in one of the cars, we're going straight into the cockpit.

Quickness and efficiency should always be a fundamental aspect of the experience when using any Android device. Anything less, and we've got a problem. As app development continually progresses, these adjectives become much more refined and polished, making the use of a smartphone a flawless affair of swipes and gestures.

Welcome back, my greenhorn hackers! I recently began a series on scripting and have received such positive feedback that I'm going to keep this series going. As I've said before, to graduate from the script kiddie to the pro hacker, you'll need to have some scripting skills. The better you are at scripting, the more advanced your hacking. Ultimately, we are leading up to developing the skills to build your own zero day exploits.

As the protectors of all things good, the Federal Communications Commission is usually busy behind the scenes pissing off Slim Shady, giving out fines for indecent nipple exposure at certain halftime events, and warning the NSA about losing any "confidential" phone information they steal from us.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

Old people are usually perceived as wise and enduring, whereas an old smartphone, like my iPhone 4, becomes the butt of a joke every time I take it out of my pocket. I mean, come on, it's not like I'm still rocking one of these... And if I was, I guarantee you wouldn't beat my score on Snake.

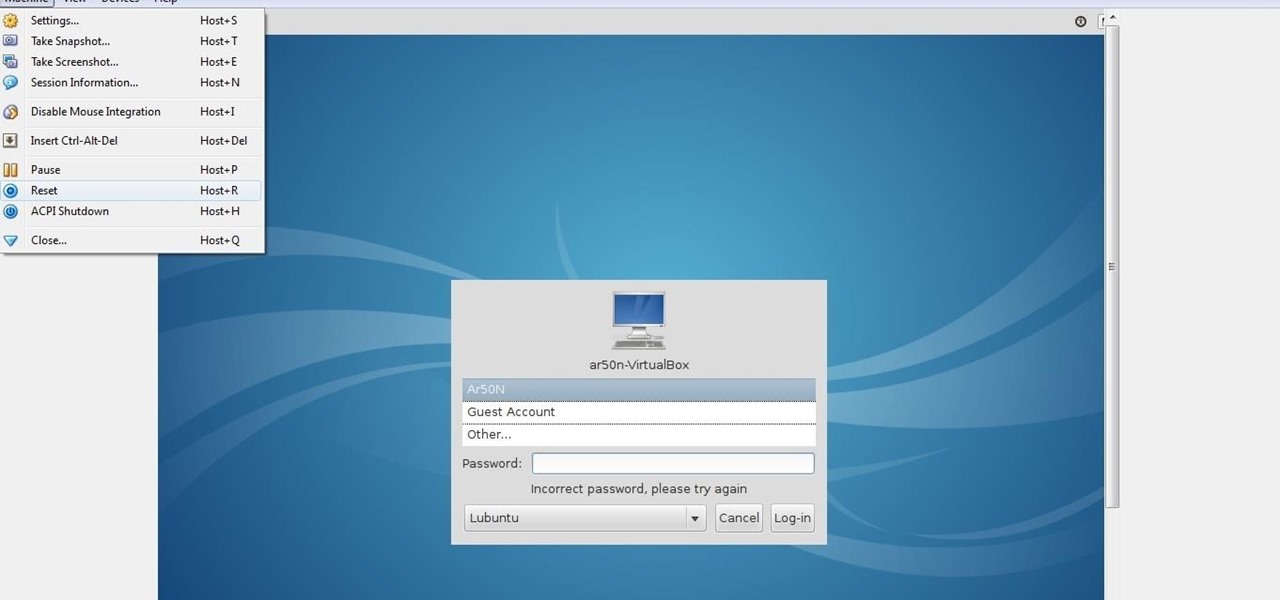
lubuntu is a is a lightweight Linux/Ubuntu that makes it suitable to virtual environments, that you run with VirtualBox to add a secondary machine to your computer or laptop. With this program you can run a number of operating systems upon the same platform.

You don't need to be a robot to be overly concerned with battery life, especially if we're talking about Terminators, which have nuclear or hydrogen fuel cells that keep them running for years straight. It will be a long time before smartphones get that upgrade, so in the meantime, we have to figure out how to make them last more than a couple hours in a single charge.

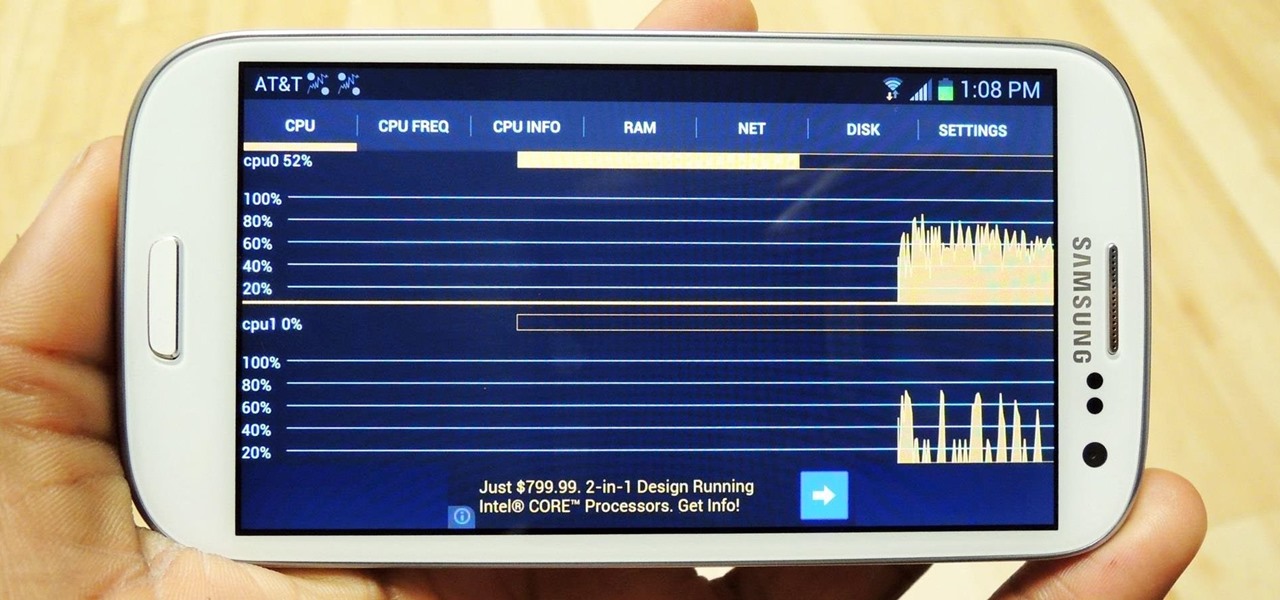
Anyone who uses a computer on a regular basis probably knows how to access the task manager to check system resources and usage stats. However, on a Samsung Galaxy S3 or other Android device, it may not be so obvious. There's no equivalent to Control-Alt-Delete, but it's still fairly easy to monitor running processes and battery usage.

Welcome back, my nascent hackers! Earlier, I wrote a guide on finding operating system and application vulnerabilities in Microsoft's own security bulletins/vulnerability database. In this tutorial, I will demonstrate another invaluable resource for finding vulnerabilities and exploits by using the SecurityFocus database.

Microsoft released a preview version of Windows 8.1 today, notably adding an updated Start screen, the ability to run several Windows 8 apps side by side in a number of configurations, fully integrated search, better HiDPI support for multiple monitors, and for those who miss it, options to bring back the Start button or boot straight to the desktop.

Welcome back my fellow hackerians, Today i'm going to tell a bit more about the famous DDOS thing. And on top of that we're going to DDOS a website.

Remember that PSP you had? I pretty much dropped mine when smartphones became more prevalent in the mobile gaming scene. Why would I want to carry around a huge PlayStation Portable when I've already got an Android in my pocket?

I've never been much of a runner. I've tried running alone, with a partner, on busy sidewalks, and back country roads, but I just never got it. There are a few other forms of exercise I genuinely enjoy, but have yet to experience that "natural high" that avid runners are always talking about.

If you're an avid PC gamer, then you're probably well familiar with the term overclocking, which is basically just tweaking your computer hardware to run faster than it was originally intended.

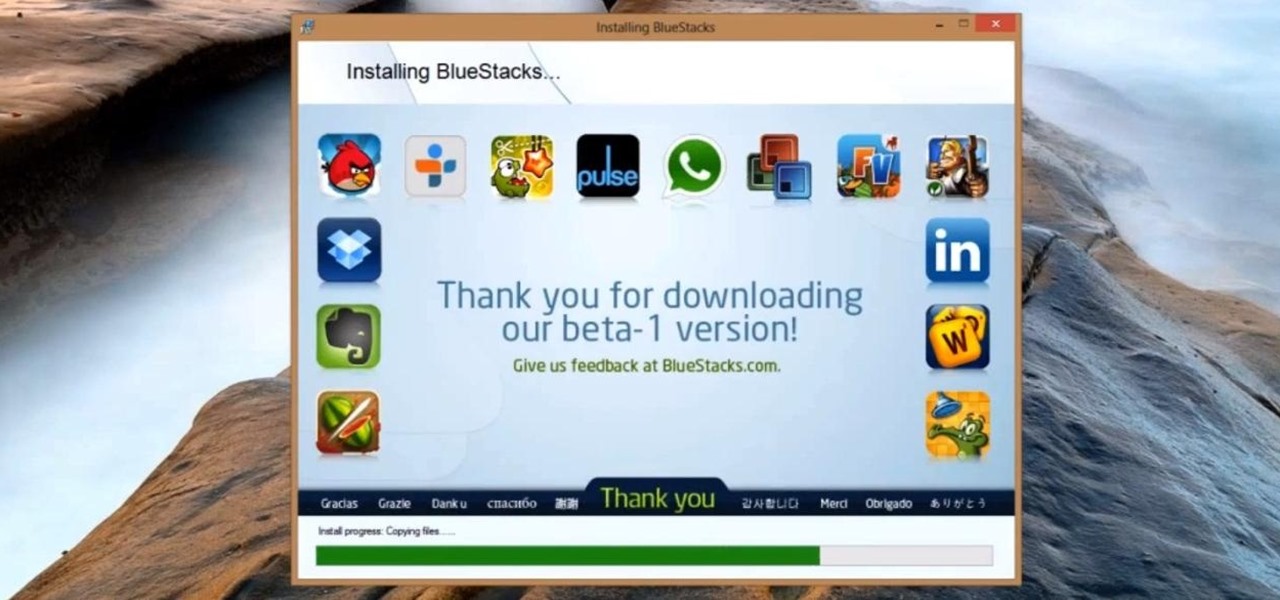
Now that the Surface Pro is out, you can game your heart out and get down with some serious Minecrafting. You're not just limited to downloading apps in the Windows Store anymore, like with the Surface RT. You can install a lot of Windows-compatible programs on the Surface Pro, but still, with this being a mobile device, it'd be nice to have some more mobile-feeling apps. And thanks to BlueStacks, you can. BlueStacks has helped people without Androids and iPhones get popular apps on their dev...

Welcome back, my greenhorn hackers! Several of you have you have emailed me asking whether it's possible to install a keylogger on a victim’s computer using Metasploit. The answer is a resounding "YES"!

While the majority of America was watching the Super Bowl yesterday, the crew over at the evad3rs was finishing its work on their untethered iOS 6.1 jailbreak called evasi0n. Well, the wait is finally over!

It's good to password-protect your PC to make sure that your personal files, folders, and important documents are safe and can't be modified without your permission. Though, entering the password all of the time before using your computer might frustrate you.

If you've ever mistakenly moved your music files around without relinking them in iTunes, you might now be noticing that you have a long list of tracks asking you to relink them. You could go through them one by one, redirect them to the new file location, then delete any copies. Or you could try to track them all down and delete the old references. But come on, who wants to spend that much time when you can clean up your library using this clever method using only Notepad on your Windows com...

Taking screen captures is a standard feature on iPhones and newer Android smartphones, but for some reason it's not very intuitive. Screenshots allow you to share your phone's screen with your friends, document technical problems for customer support, and even make how-to guides easier to follow. So, it's definitely worth remembering. Here's how you do it.

Ugh, the dreaded shin splints. Almost any habitual runner has experienced it: a sharp, tight pain in your shins that jolts you uncomfortably every time you move. And for those who are on their feet regularly, like runners and dancers, shin splints can be a big pain in the ass.

If you don't want to go through the hassle of setting up a formal network between two Macs, but still want to transfer files between the two, take a look at Airdrop. Airdrop is a built-in utility found in Mac OS X Lion (10.7) that will allow you to easily drag and drop files to another computer belonging to you or a friend.

As a guitar player one thing that you may find yourself running into is your guitar, over time, will start to lose its intonation, especially if you never set it up after you purchased it. You could take it to a tech to have him set it up and fix it for you, but that's expensive, and who wants to spend money when you can do it for free right!? In this video you will learn how to adjust the bridge of your guitar among other things to help get your guitar back into tune!