How To: Add Full Body Motion Tracking to the HoloLens with a Kinect
Thanks to Project-Infrared, there's now a pretty straightforward way to add motion tracking to the HoloLens: Connect it to a Kinect.

Thanks to Project-Infrared, there's now a pretty straightforward way to add motion tracking to the HoloLens: Connect it to a Kinect.

Video: . This video will show you how to connect the positive and ground wire on the battery of your RV or camping trailer.

Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

Very often we have processes in Linux that we want to always run in the background at startup. These would be processes that we need to start at bootup and always be available to us.
This video will show you what to look for if you dishwasher stops turning on or filling with water.
Fugu - a simple virus in bash. I once told a friend of mine I'd written a virus in bash and he scoffed - "You can't write a virus in bash!" - he sniggered, like an ignorant idiot.

Let me share some great information on stair climbing and how it can provide many health benefits. Burn more calories stair climbing that jogging or running. See how in the video. If you enjoy the video and would like to see more, please hit the subscribe button. I hope this helps!!

Welcome back to a tutorial on malware. We'll be discovering a method to beef up our little trooper. Without further ado, let's jump right in!

Hello NullByte! This will be my first How To series.

Welcome back to another C tutorial, this post covering the first part of control structures, if statements. Let's get right into it.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.
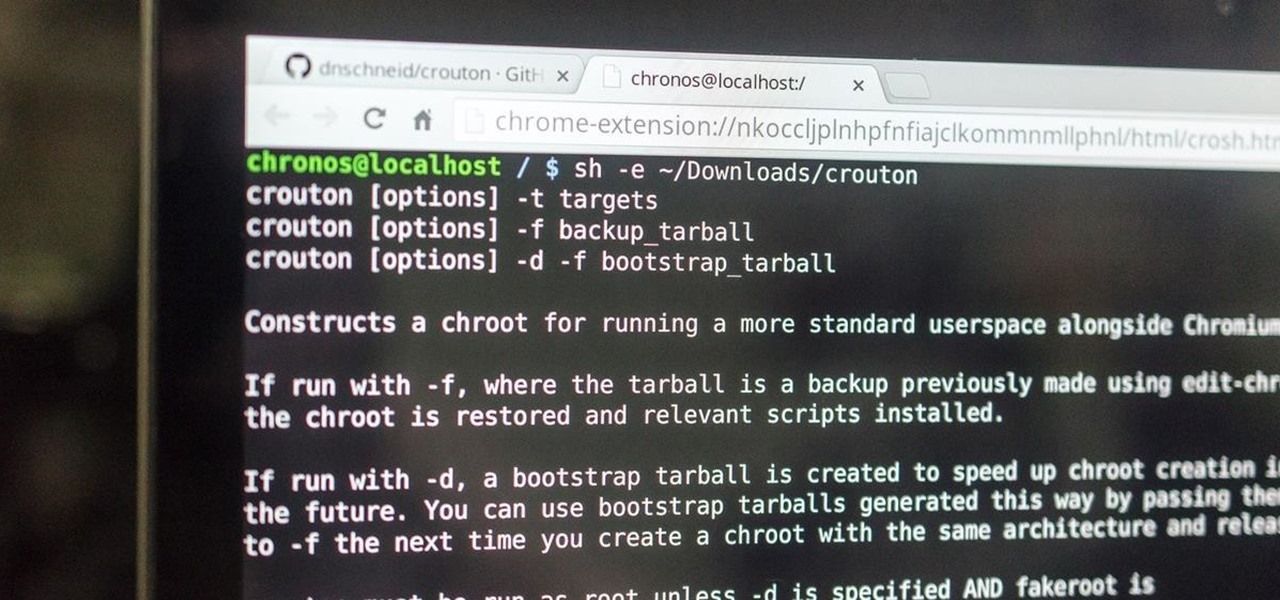
This is my first how-to for this site so feel free to let me know if I can somehow improve! Inspired by the great Jailbroken iDevice and Rooted Android PenTesting tutorials I decided to share how I use my Toshiba Chromebook 2 with Kali Sana.

Welcome back, my tenderfoot hackers! WordPress-based websites are among the most numerous on this planet (maybe other planets too, but I can't vouch for that). According to WordPress's own website, WordPress powers 23% of the top 10 million websites. That's approximately 2.3 million sites using WordPress!

While password cracking and WPS setup PIN attacks get a lot of attention, social engineering attacks are by far the fastest way of obtaining a Wi-Fi password. One of the most potent Wi-Fi social engineering attacks is Wifiphisher, a tool that blocks the internet until desperate users enter the Wi-Fi password to enable a fake router firmware update.
Do you remember my last article on how to hook any web browser with MITMf and BeEF? Well, we are using the tool once again, but this time for auto-backdooring....

Welcome back, my fledgling hackers! Let's continue to expand our knowledge of digital forensics, to provide you the skills necessary to be a digital forensic analyst or investigator, as well make you a better hacker overall. In your attempts to enter a system or network undetected, it is key to understand what a skilled forensic investigator can learn about you, the alleged hacker.

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

Now that we have our vulnerable server, it's time to start up BeEF. Getting Started

This ship is over 4 ft. long with many moving parts all run from a live steam engine. There are two videos, one more detailed about the story and one blog showing how it was built. Hope you enjoy.
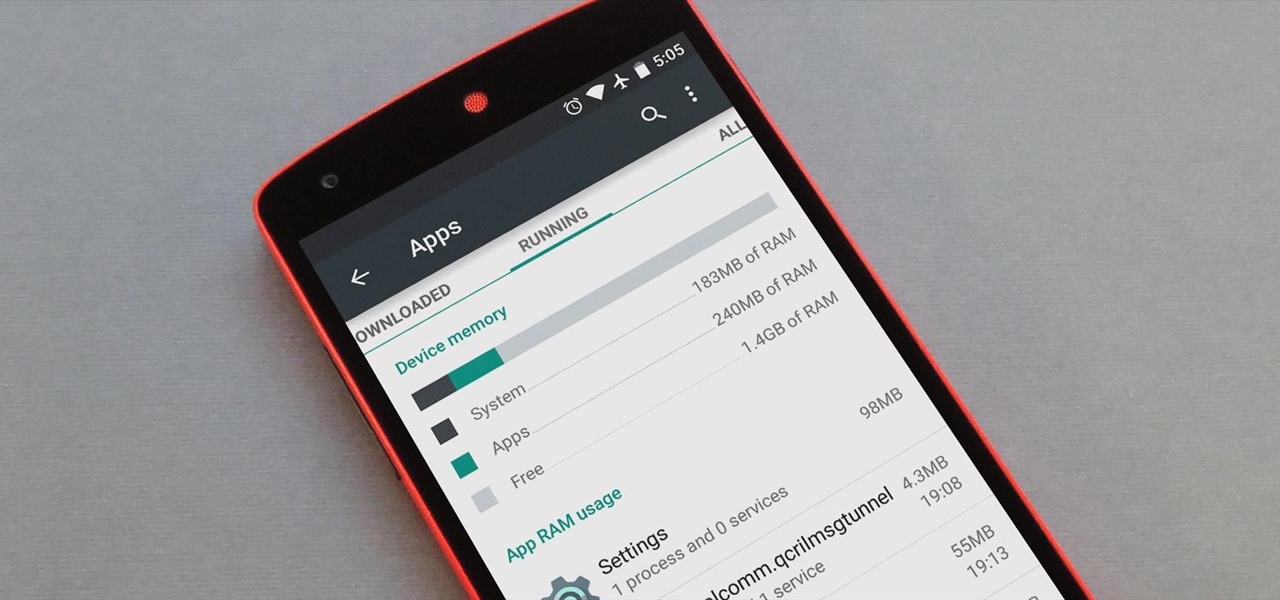
Android version 5.0 Lollipop introduced a ton of changes to the OS—and of course with new features, there's always a new set of bugs. One of the biggest bugs of all was a massive memory leak caused by the new screen-off animation, which loaded its assets into memory but never cleared them away.
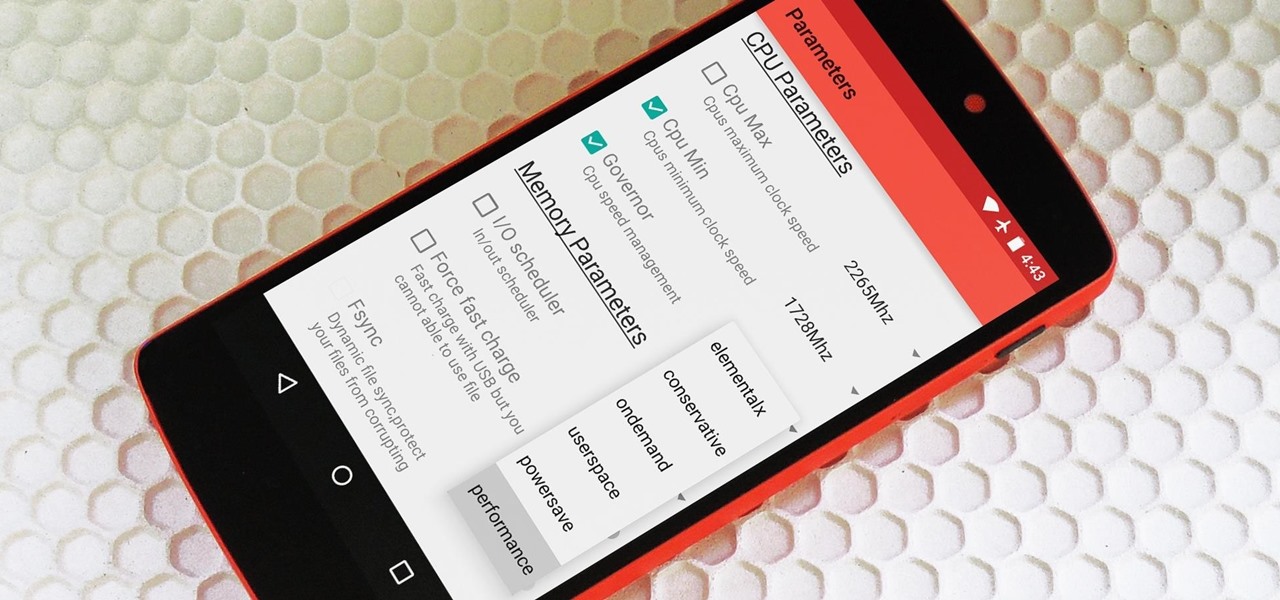
Deep down at the core of Android lies the system kernel, which serves as a bridge between software and hardware. Custom kernels can be installed in place of the stock offering, and these are generally optimized for better performance or increased battery efficiency.
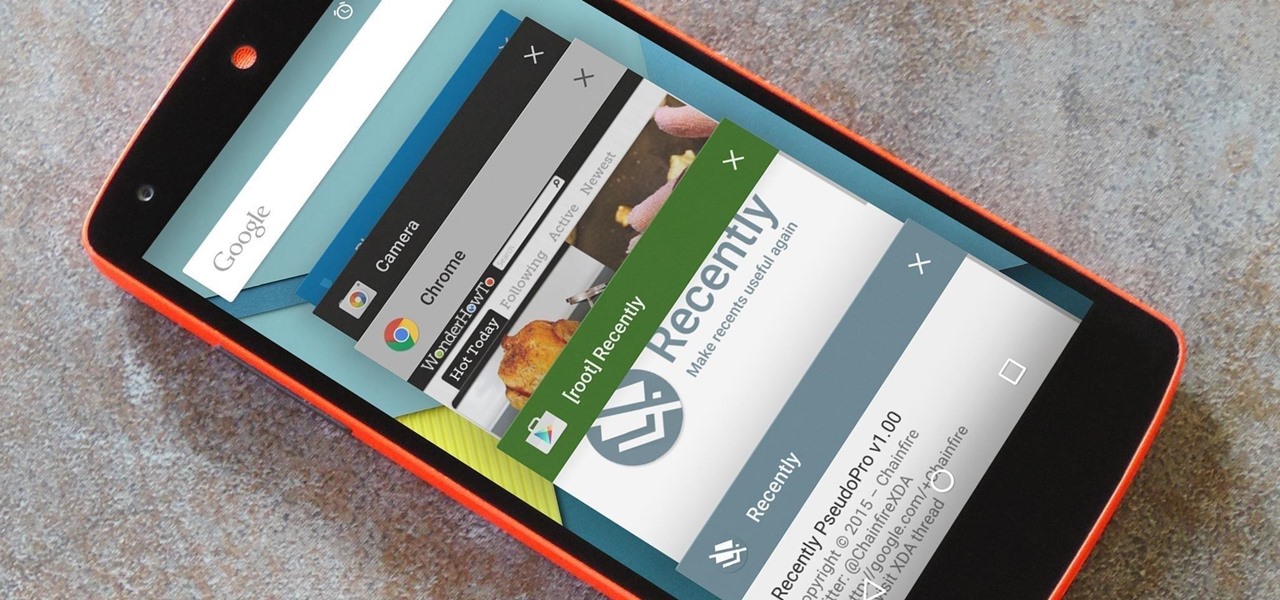
As is the case with most software updates, Android 5.0 brought changes that were viewed by users as somewhat positive and somewhat negative. This generally happens because we're accustomed to the old way of doing things, and changes, no matter how useful, can slow us down.

When Yosemite was released, a more detailed boot screen came to your Mac. So now, just like on Apple's mobile devices, you will see a loading bar telling you how far into the startup process you are. Apple also decided to add a black version of this boot screen to newer Macs, leaving those of us who purchased a computer before 2011 out of the loop.
Want to get even this Halloween? Want to scare somebody with nothing but a few lines of code? Here's how it can be done...

Linux may not be the most popular consumer operating system out there, but what it lacks in consumer app variety, it definitely makes up for in flexibility and security. And if you've ever tinkered with a Linux distro, you know how easy they are to install—most of the time, I skip standard installation and boot directly from a CD.

This video will show you handy tips and tricks about Google search engine. These tips will help you to speed up your computing or browsing experience. This video contains tricks like Search by location, Filter image search, how to see sites that aren't online, movies running in a city theaters etc. This video is the 2nd part of the serial. You could also watch the part 1 here vimeo.com/104089915.
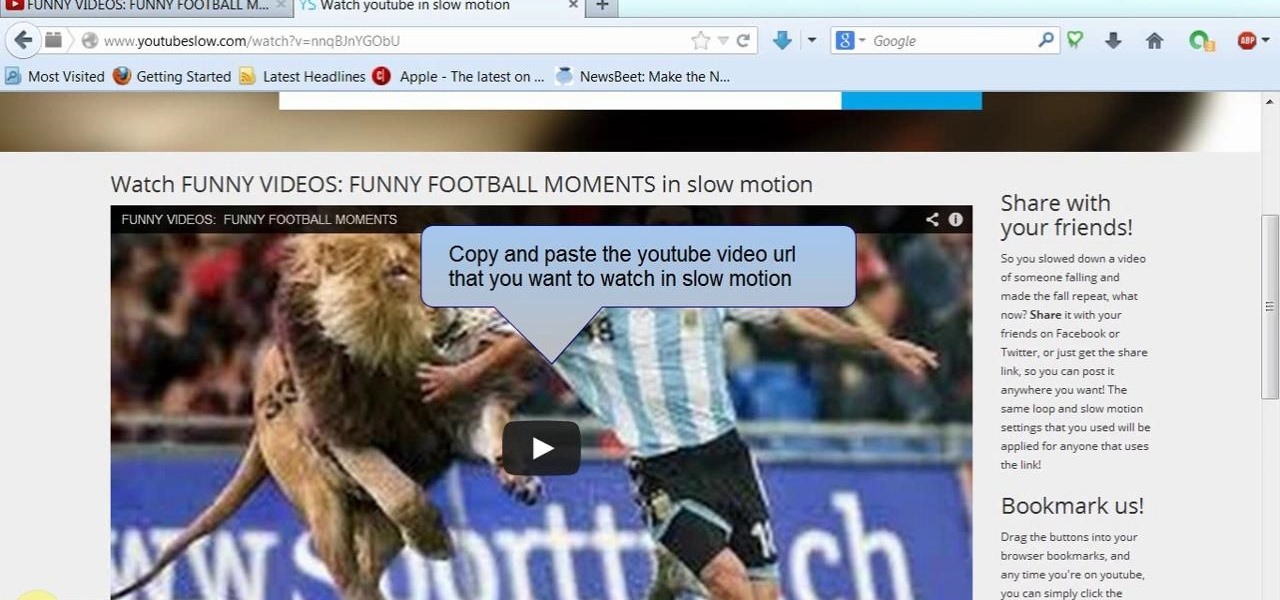
This video will show you how to watch YouTube video in slow motion as compared to normal speed. You could reduce the speed of a YouTube video to .25, .50. You could also make a video run faster than normal speed. So please watch the video and employ it in your computer.
A full run down of how to grow all the crops in minecraft Video: .

Video: . Ever had a bad hair day and didn't know what to do with it? This video shows you how to quickly do something cute with your hair especially if you're running out of time.

Video: . This video shows you how to set up your Lowrance unit to optimize it for ice fishing. This will also apply to Lowrance Elite and Mark series units as well as the X-67c Ice Machine.

With AirPlay for iOS, Chromecast Screen Mirroring, and even third-party PC-pairing apps to play around with, getting your devices to interconnect could not be any easier than it is today.

Not much work goes into setting up this pen prank. You will however need to get some party snaps and you will be loading the pen with a one or two.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

Here's a quick easy way to quiet down a loud squeaky hamster, mouse or gerbil wheel. This will enable you to finally sleep at night!

Once you unlock your bootloader and root, you're left with one more hurdle to overcome, and that's getting S-Off.
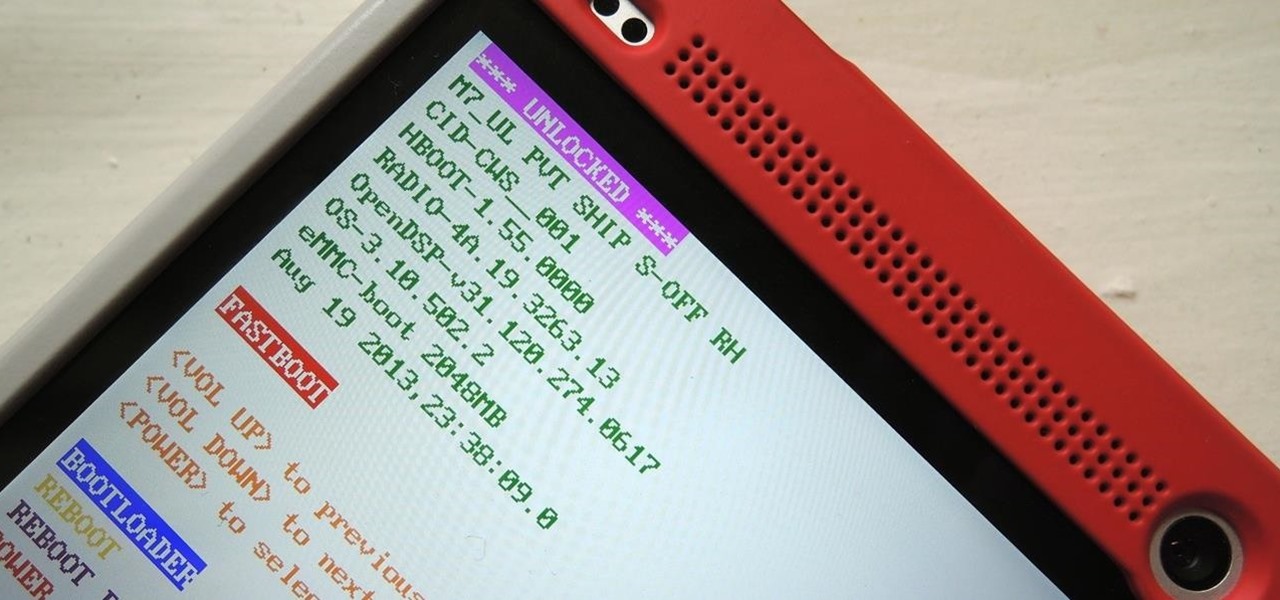
You've unlocked your bootloader and rooted your HTC One running KitKat, but there's still one lingering aspect of security you've yet to rid yourself of—S-On—the extra security measure HTC implemented into Sense.
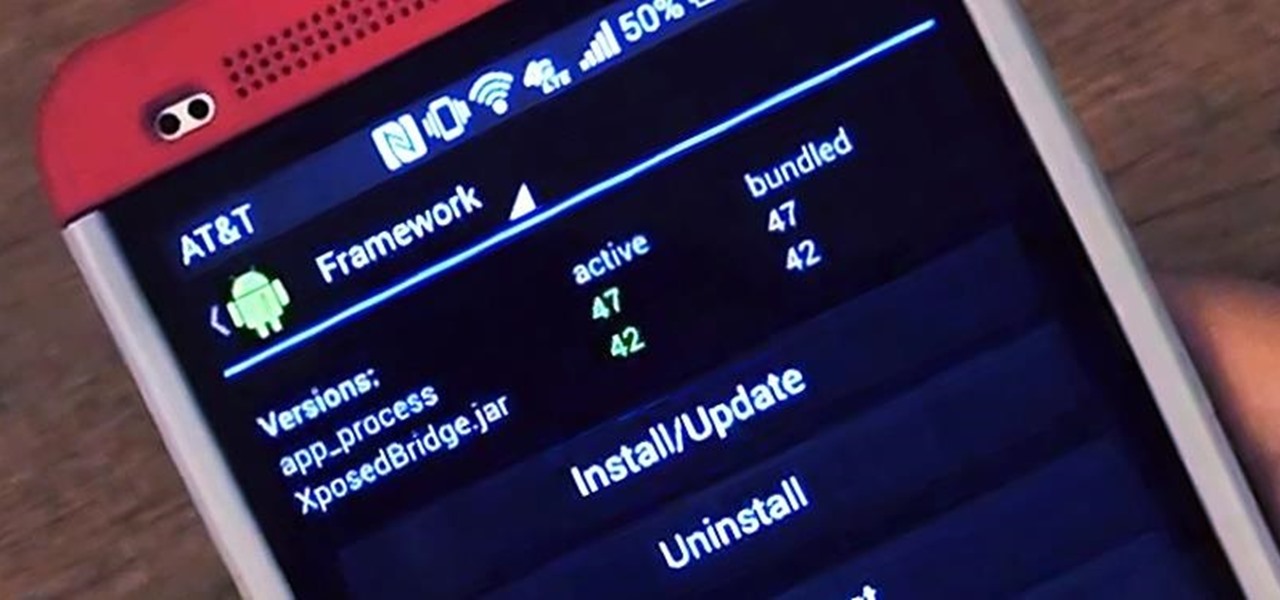
There are plenty of ways to customize your stock HTC One (or any Android device), from playing retro games to adding rotating live wallpapers. But to get the most out of your device, you need root access.
Whether you have the original Nexus 7, or the 2013 Nexus 7 tablet, rooting it will give you access to tomorrow's features, today.

Is the water dripping or running in your bathtub shower? This video will show you how to remove and replace the shower valve stem and also how to replace the seal that on it. Usually the seal deteriorated over time causing your shower to leak.