
News: Artists Transform Brooklyn Light Installation into Instagram AR Filter That Doubles as Dimensional Portal
What if you went to an art installation at one of the coolest venues in New York that you could then take with you anywhere in the world?


What if you went to an art installation at one of the coolest venues in New York that you could then take with you anywhere in the world?

The tradition of using cutting edge technology to prepare for missions in space, in this case, augmented reality, continues with a new team of international astronauts slated to board the International Space Station (ISS) later this year.

The new iPhone XS and XS Max have more issues than just their hefty price tags. Customers have only had the phones for a handful of days, but some are already complaining of cellular and Wi-Fi connectivity issues on both models. If your experience is the same on your XS or XS Max, there are steps you can take to get your iPhone reliably back online.

Some of us woke up at the KRACK of dawn to begin reading about the latest serious vulnerability that impacts the vast majority of users on Wi-Fi. If you weren't one of those early readers, I'm talking about the Key Reinstallation Attack, which affects nearly all Wi-Fi devices.

Take one down, pass it around, 99 bottles on which to play classical music? As someone who has studied music extensively, I've seen many interpretations of famous pieces of music played on glass bottles, but hearing these four interpretations of famous pieces (not all classical) completely blew my mind.

What you probably don't know is when you remove a file on your system, it is actually still saved, and not entirely removed. Let me tell you how to get rid of it completely.

Early last year, Google purchased Quest Visual, acquiring the immensely popular augmented reality translator app Word Lens in the process. While Google did put the feature on the Google Glass, they spoke more about implementing Word Lens into their Translate app sometime in the future.
An amazing amount of news this week; new proposals and new agreements have sprung up. But so has our "need" to spread our presence. The military warns of another war, while 26 congressmen decry the use of drone strikes. Read on:

Card tricks are among some of the most popular and infamous illusions used by magicians. In this free online video series, learn about card forcing. Our expert illusionist will reveal the secret to this magical technique with tips on how to use force cards and how to perform magic tricks based on forcing.

Teach your students about centripetal force with this science video tutorial. It will show you how to use some masking tape and a ball to demonstrate how centripetal force works.

The wonderful tastes of jello and yellow cake combine forces into a dessert that packs a powerful punch of flavor— a jello cake. Using yellow cake mix and a box of jello (any flavor), you can create a wonderful dessert the whole family can enjoy. Plus, it's two desserts in one! What could be better than that?
The football season is almost here, and what better way to celebrate it then by playing Madden NFL 11. The newest version of the popular franchise, claims to offer better run blocking for players, faster gameplay, and much more.

In this tutorial, we learn how to throw a crazy gyroball in wiffle ball. You will first stand still with the ball in your hand grasping it lightly, when you go to throw the ball, throw with force and spin your body around. This should make the ball go straight into the target almost every time you throw it. Keep practicing this until you have the hand placement correct. Try moving your hand in different positions around the ball so that the grasp makes the ball move in the right direction. Af...

In this tutorial, we learn how to eject devices from the use of the terminal for Mac. First, go to the terminal of your computer where you will see a notepad sort of page. Next, type in "df" and then press return. You will now see a list displaying processes on your computer. On the bottom will be your public zoning device, which is your USB device. Next, type in "hdiutil eject -force (the code under "mounted on)- volumes-publiczone". This is not case sensitive, but don't forget or add in any...

Unless you're tightrope walking, stability is quite a fun killer. Relish in the unknown by learning how to do bicep curls with an exercise ball incline. By forcing your core and your back to deal with the bouncy, unstable nature of the ball, you'll have to work those areas in addition to the biceps.

This video workout is aimed at skinny guys who want to get ripped. Some tips for weight training are to train less than 45 minutes at a time, focus on compound movements, try to get 5% stronger every two weeks, don't do more than one or two forced reps, and split your workout into 3 days for various body parts. To gain muscle mass, eat about 15 times your current body weight in calories, including 1-1.5 grams of protein per pound. Eat twice as many carbs as protein, high quality fats, and nut...

Linuxjournalonline teaches you how to use GRUB to dual-boot Linux and another operating system. You need to go to etc/default/grub and edit that file. Here you can configure the time it needs to start booting a system and what OS to boot. You need to be root to edit this configuration file. Don't forget to run update-grub to force an update of grub.cfg. And this is the end of the short process needed to configure Grub 2 for Linux.

In this video, harrymedan offers a do-it-yourself remedy to fix an iPod that has the "sad face" warning screen on it. As you follow along, he explains all the tools and supplies you will need to get started on this project. He demonstrates how to force the iPod into disk mode, leading you through, step by step. Once you achieve this he tells you how to connect the iPod to your computer and "Restore" the iPod back to factory settings, which usually fixes the problem.
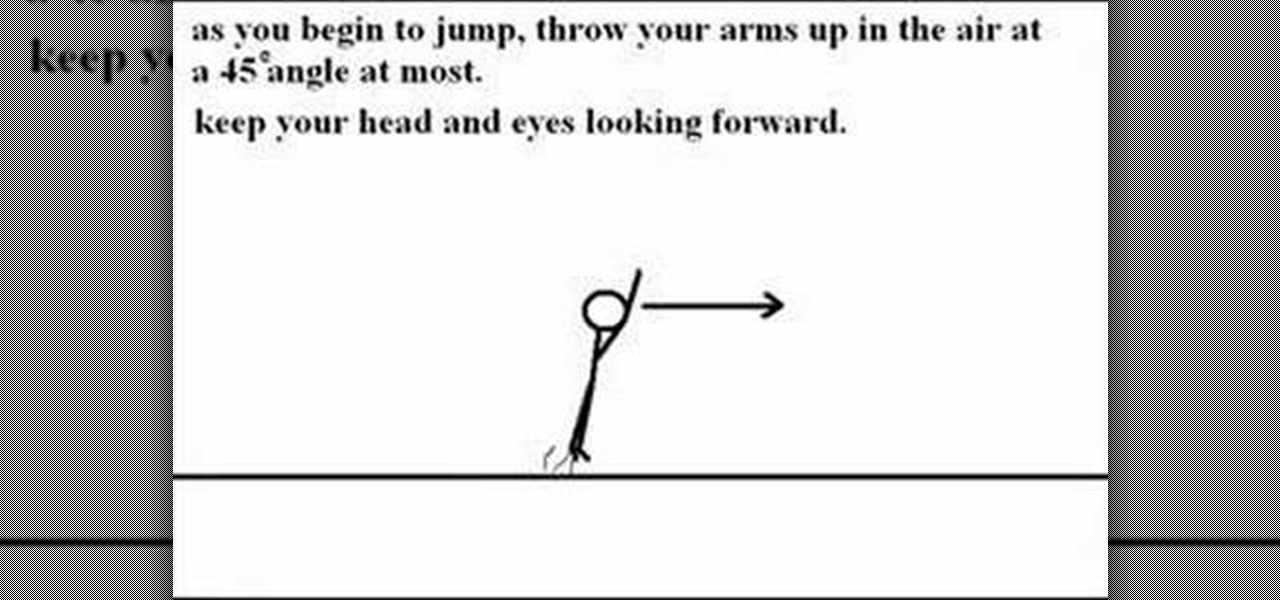
Are you into parkour? This video will show you how to do one of the many tricks that are used by athletes - the front flip. Demonstrated via stick figure drawings, you are shown how to get speed and rotate properly. This type of trick can be used with freerunning, but be sure to perform a PK roll after landing to mitigate the force of your landing.

Birds don't generally wear collars, but to give a bird an identity tag, leg bands can be used. This video demonstrates the way to put leg bands on baby pigeons. This is usually done between 5-7 days of age. When pulling the back toe through, make sure not to force it if the little claw gets caught on the inside of the band. Watch this video pet care tutorial and learn how to band the leg of a baby pigeon with an ID tag.

Those looking to begin making pottery, will benefit from the instruction provided by this video pottery tutorial. Center the clay, force the clay to mold to your hand rather than molding the clay, and start throwing pottery. Learn how to use a potter's wheel and begin working with ceramics by watching this instructional video.

See in these two videos, how to dye your radio controlled vehicle's parts. You'll see how to properly dye many plastic parts on your RC vehicle like Revo 2.5 or 3.3 rockers, high down force Ofna wings, pro-line rims, and many more parts. The project uses RIT dye that comes in many colors to include black, light and dark blue, green, and more. This will allow you to take any color of part (especially white) and make your RC into something that is customized with little effort.

It seems impossible. Ripping one piece of paper is effortless. Ripping a small stack of papers takes a little force. But ripping a book? No way! Actually, it can be done, but only with a telephone book. This tutorial will show you how to rip a phonebook in half, quickly and easily. This is a great trick to perform at parties to impress your friends.
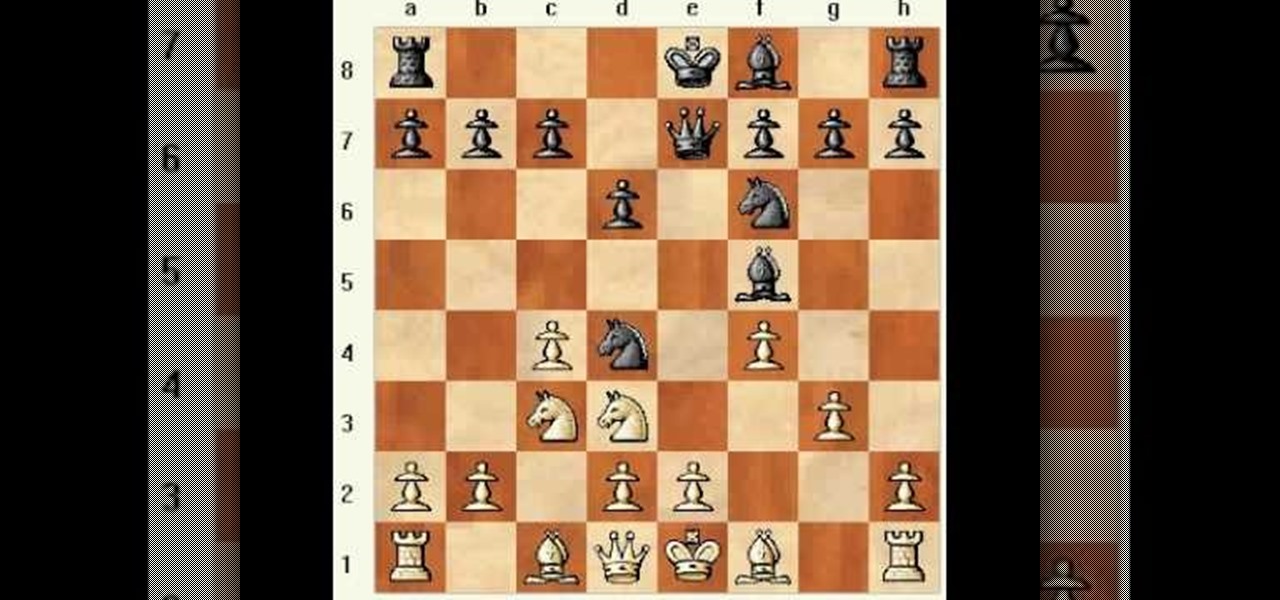
In this video, Matt explores a gambit line for Black in the Four Knight's English: 1.c4 e5 2.Nc3 Nf6 3.Nf3 Nc6 4.g3 Nd4!?

In these two videos, Matt discusses 1.d4 d5 2.e3 Bf5, preventing White's Stonewall setup by beating White to the d3-h7 diagonal. The only way White can play for an advantage is to play 3.c4 with the goal of an early attack on b7. Some of these positions can also be reached via the Slav Defense.

One vital part of Android 10's new navigation system is the "QuickStep" gesture. Swipe up from the bottom of your screen, then pause. You'll see your recent apps along with a dock containing a handful of icons for quick access. This dock is provided by the phone's launcher, which means your home screen is now integrated into the multitasking UI. So what happens if you change your home screen app?

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.

There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture handshakes from both attended and unattended Wi-Fi networks, we'll use two of Bettercap's modules to help us search for weak Wi-Fi passwords.

Router gateways are responsible for protecting every aspect of a network's configuration. With unfettered access to these privileged configurations, an attacker on a compromised Wi-Fi network can perform a wide variety of advanced attacks.

In recent years, the US military has been utilizing augmented reality as a training tool, giving officers and soldiers an opportunity to train and hone their decision-making, tactical efforts, and weapons accuracy via virtual scenarios.

Ratings and reviews apply everywhere, from a restaurant you want to try to a new camera you're thinking of buying and games you might want to play. Podcasts are no different. Reading reviews of shows can help determine which are worth listening to, and your opinion is valuable to other people too. In Apple Podcasts, there are a few different ways to read, rate, and review shows.

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

While there is a lot to be excited about when it comes to iOS 12 in general, iPhone X users will not just get the same new features and tweaks that all other iPhones will get — they'll get a few unique ones that will make the device even more desirable to those who don't have one yet. Also, iPhone XS, XS Max, and XR users will also see these benefits out of the box.

When it comes to security, Apple is usually at the top of the pack when it comes to your personal data, minus a few embarrassing flaws here and there. However, a new iOS security concern has been discovered that protects your data less than it did before — and Apple designed it like that.
In this Tutorial I will show you how you can use the frequency of letters to decrypt the famous Caesar cipher. I hope it is easy to understand and helpful for getting in touch with basic cryptanalysis. If you find any mistakes or have questions feel free to ask me. Finally I ask you to give me feedback which I will take into account for the next part.

NMAP is an essential tool in any hacker's arsenal. Originally written by Gordon Lyon aka Fydor, it's used to locate hosts and services and create a map of the network. NMAP has always been an incredibly powerful tool, but with it's newest release, which dropped mid-November of last year, they've really out done themselves.

As glorious as a good drink (or five) can be, the aftermath of alcohol on the body is one of life's least enjoyable features. A few hours of fun can come at the expense of a day or two of feeling dead to the world, with an upset stomach, an aching body, and a headache that makes it feel as though your friends used your head for a piñata.

On the Apple Watch, along with the conventional emojis we've grown to love, there are new animated emojis that add a new dimension of fun for you and your friends. Unbeknownst to many, these animated faces also include a feature that allow you to change their color.

From time immemorial, human beings seem to be at odds with one another. When these differences become so heated and unresolvable, it eventually erodes into physical violence. This violence has manifested into some of the most horrific exercises in human history, things which every school child is aware of and none of which we have to recount here. Although humans have been cruel and violent for a very long time, the 20th century may have epitomized that behavior. With two World Wars and many,...

In the aftermath of the unindicted police killings of Michael Brown and Eric Garner, we've been told that the system worked as intended. When our legal system's outcome is at conflict with what a majority of Americans believe is just, it's clear that some changes are needed. But what specifically needs to change? And what can an average citizen with a moral and just cause do to prevent these kinds of tragedies from repeating themselves again and again?