In this video Special Guest Lynn Grillo from Adobe will show us how to create and use GoLive page templates. Templates in GoLive allow you to define the page design and placement of your objects. By using Templates if you ever decide to update/change the design of your site, all you have to do is modify the Template page that your site pages are based on.

Perceiving Reality answers that if you just believe in God, then you can't live a spiritual life. What is spirituality? According to Kabbalah, spirituality can't be defined as a belief or philosophy, but only as a clear perception and sensation of reality.

To really make your eyes stand out you may want to emphasize the crease in the eyelid with eye shadow. Dramatic eyes are great for going out at night and by using your darker shadow in the crease you will be sure to be noticed.
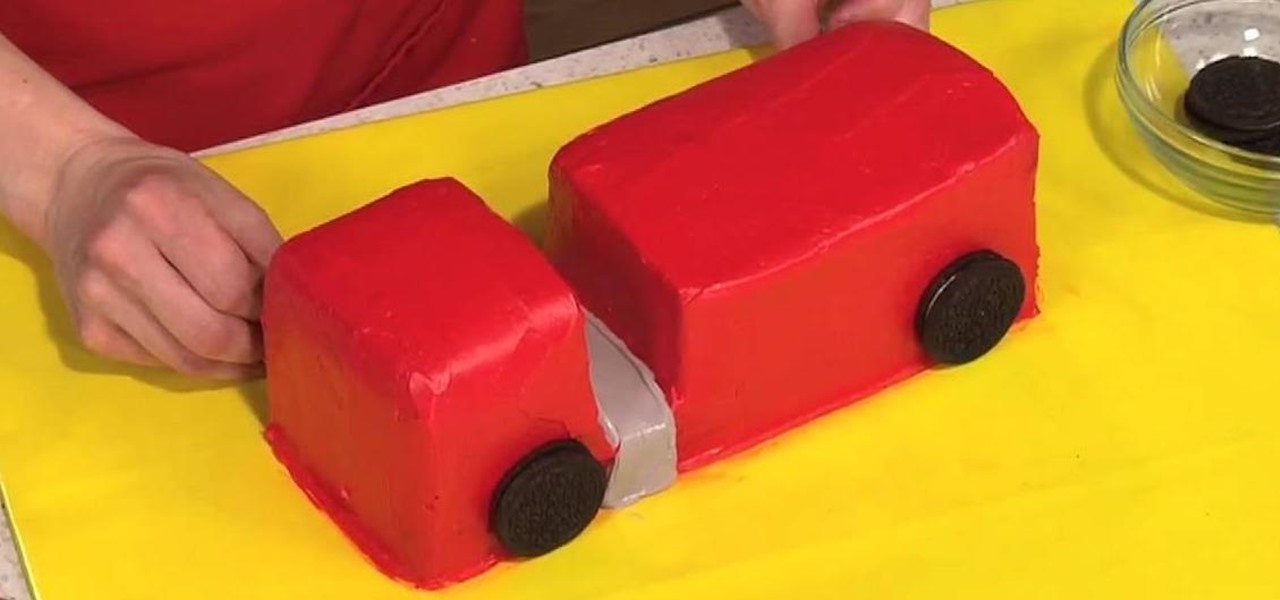
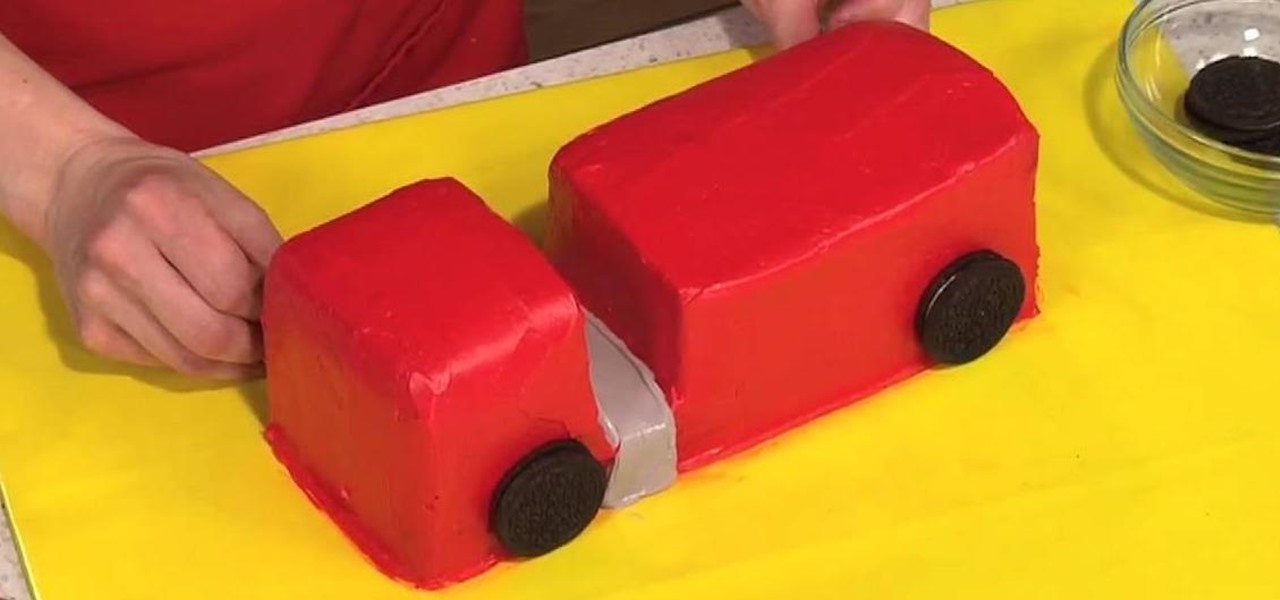
To decorate a fire truck birthday cake, you will need the following: three chocolate cakes baked in loaf pans, Oreo-type sandwich cookies, candies, and brightly colored icing.

This series of videos focuses on a typical UV workflow in Houdini 9. Learn how to create projections, edit UVs with a variety of tools, save out UV maps, and apply textures. Please download the project files below to follow along with these Houdini 9 texturing lessons.

Home cooks are often quite intimidated when trying to reproduce the delicious ethnic dishes they enjoy at various restaurants. Thankfully, there are definite flavor profiles and spice/seasoning/herb combos that are very specific to various regional cuisines and cultures; with a little guidance, you can create dishes that are tasty homages to the cuisines you love to eat. In this two-part article (second part here), I'll cover both categories and sub-categories of some of the most popular ethn...

Developing GUI apps in python is really cool. I ask those who understand the language to help convert some of the command-line or console programs or apps ( I mean programs that are useful to a hacker ) to GUI. I know GUI makes us lazy and not wanna learn but we should all know its fast. Today's tutorial is on p2p chat app I developed last week and decided to share it with the community since its kinda cool.

I've tried my hand in the past at defining Steampunk, but as anyone else who has made a similar attempt will tell you, there's a significant backlash from the community against working to create a real definition of what Steampunk is. That may sound ridiculous to some, but it's a very serious matter to others. With the recent announcement that TeslaCon 4 will be called the Congress of Steam, I think it's appropriate to talk about why all of this stuff is worth it. In this article, I'm going t...

What's one of the defining golf skills that sets amateur and professional golfers apart? Putting. In this video golf tip, Mel Sole provides key strategies that will help you putt like a pro.

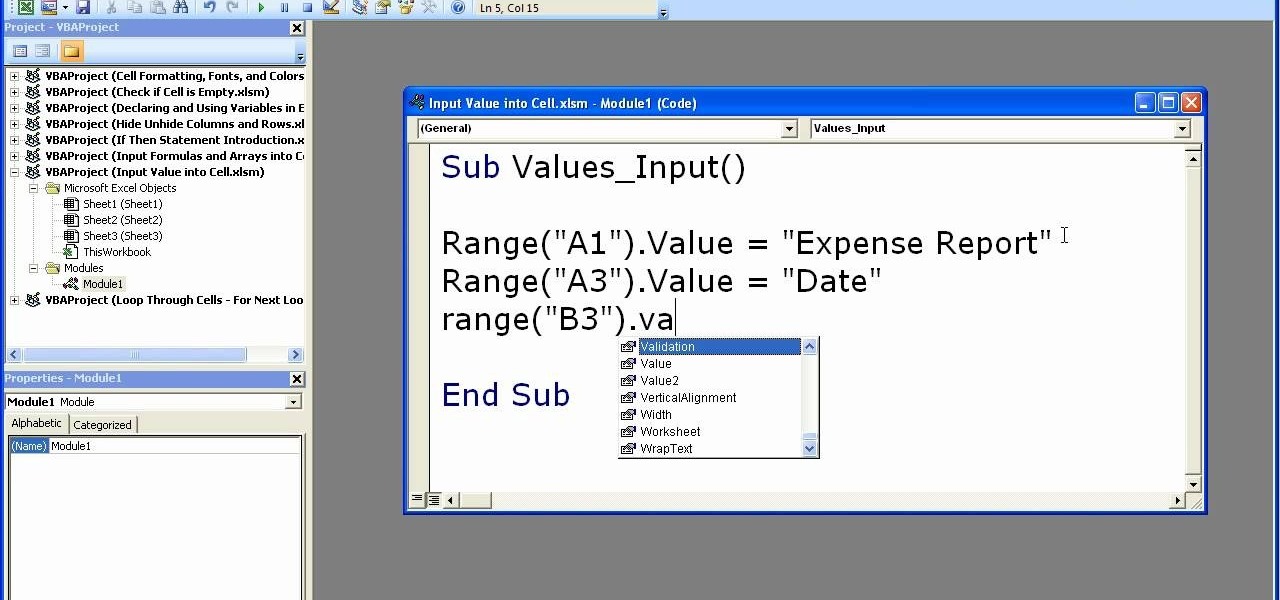
This video shows how to enter values into cells using Excel macros and Visual Basic. This includes a sample Expense Report that is used in this demonstration. In this demonstration, we will create the macro that inputs a title as "Expense Report", Three columns i.e. "Date", "Item" & "Amount", and the summery field as "Total Expenses", as well as the formulas located at the respective cells. Now, we're going to use two keyboard shortcuts i.e. "Alt + F11" to open-up the VBA window and "Alt + F8...

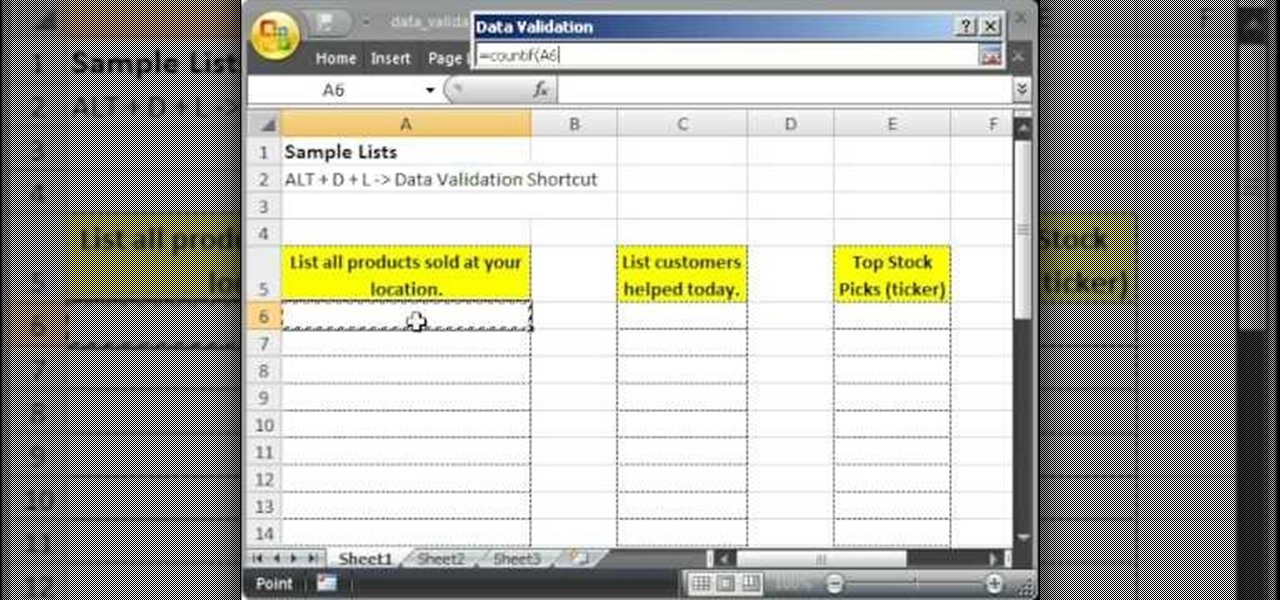
This tutorial describes how to make a list with unique values in Excel.This procedure makes the defined cells in a column (called as list) NOT to accept repeated values, which makes the list more simple, readable, easy to manipulate when preparing a worksheet.

The video is about how an old stalled photographic image with faded backgrounds to a normal image. A nice clean digital image is taken and is mixed with a texture of a paper and produces a final composite image of all effects combined. The procedure is not that difficult but it needs to be followed in a proper order. First the paper texture is taken as a base and then the clean digital image is dragged onto this texture. The blending mode is adjusted from normal to multiplied blending mode, w...

This photoshop tutorial demonstrated by Howard from tutcast.com, teaches you how to do amazing glow effects for your work and projects. Everything you need to know from the background you choose to use to editing out the leftovers. You can use any image that you choose to. Start out with the pen tool located on the toolbar on the most left of the screen. Create the initial layer for the glow by clicking now on the new layer icon located on the bottom right. Next, define brush by pressing the ...

Goldiestarling presents you this video where she does a make-up inspired by late Bette Davis was a Hollywood actress. She says that Bette Davis is her all time favorite actress and she loved her from her high school days. She says the Bette was a very strong lady even in her real life and if you Google on her or watch her movies, you too will like her. This make-up she has done she says is based on Bette's character in the movie called 'Of Human Bondage' in which she plays a waitress and late...

Here is another cool photo manipulation you can do using Photoshop CS3. You can take a normal photo you’ve taken and really make it look unique by giving it harder edges and some more texture to the shot. Mix up your photos with this effect.

Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, such as scanning. Case in point, WMAP, a web application scanner available for use from within the Metasploit framework.

Apple often cites its tight integration of hardware and software for its success. Startup Illumix is looking to do the same thing for AR gaming by building an AR platform for its apps.
Hello everyone! This is my first attempt at a tutorial here. There are a couple great assembly tutorials here, and I wanted to toss my coin in the fountain.

Welcome to a tutorial on XOR encryption. We'll be looking at what XOR is and how we can use it to encrypt or decrypt data.

Hello fellow gray hat hackers, I wrote a program in python that helps me to fill up my proxychains.conf file, so I don't have to manually enter in the proxies. I figured I will give a little how-to of how I did it and maybe I could help some of you(hackers) out there to stay anonymous.

The digital pen on the Surface Pro 4 and Surface Book is an indispensable tool for serious note-takers and artists alike.

When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

Man-in-the-Middle attacks can prove to be very useful, they allow us to do many things, such as monitoring, injection, and recon.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

Journals are a great source of hilarity and embarrassment, detailing everything from your elementary school crushes to those super awkward middle school dances. While rereading your old hand-scrawled entries might make you cringe, that old journaling habit could benefit you as an adult.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.

Welcome back, my aspiring hackers! One of those areas of Linux that Windows users invariably struggle with is the concept of "mounting" devices and drives. In the Windows world, drives and devices are automatically "mounted" without any user effort or knowledge. Well, maybe a bit of knowledge. Most Windows users know to unmount their flash drive before removing it, but they usually think of it as "ejecting" it.

Hi, gang! Time for another hack using Metasploit. We have exploited Windows XP (a very insecure operating system) and we have exploited Ubuntu and installed Meterpreter on a Linux system exploiting the Samba service. Several of you have asked for a hack on more modern Windows systems, so here goes.

No matter what age you are or what kind of life you've lived you can put your story out there by writing an autobiography. Every life can be interesting if written about in a well formulated, and honest manner.

The iPhone 11 series models have sophisticated camera systems that include both a wide and ultra-wide lens. On top of that, the Pro models also have a telephoto lens. So you can zoom anywhere between 0.5x optically to 5x or 10x digitally, depending on the one you have. While you can pinch in and out on the screen to control the zoom, there's a way to get more granular control for photos.

Few things are more important than being well-versed in data analytics and interpretation when it comes to succeeding in today's increasingly data-driven world. As a data scientist, these skills are the key to a high-paying career. For hackers, there's no better way to defeat the enemy than to become the enemy.

The Google Pixel's camera is a status symbol of sorts. When someone sees you with one, you become the photographer of choice for social events. And where do those photos end up? Social media, of course. It's how we share our lives now, and the smartphone camera defines how we approach that.

The collaboration between Magic Leap and Wacom, which was first announced during last year's L.E.A.P. conference is progressing rapidly.

At its F8 developer's conference in 2016, Facebook went on record with a roadmap that called for augmented reality integration into Oculus within 10 years. Now, it appears as though Facebook is accelerating those plans.

When it comes to web-based augmented reality, 8th Wall has emerged as one of the leading platform providers, and the company just cranked up its capabilities another notch for AR marketers.

After a little more than a year at motion tracking technology maker Leap Motion, Keiichi Matsuda has resigned his position as vice president of design and global creative director, the company announced on Wednesday.

Microsoft's Monday keynote introduced the fourth generation of the company's Kinect sensor during Build 2018 in Seattle.

San Francisco-based 6D.ai is preparing to launch a beta of its AR cloud platform that's capable of constructing a real-time dense mesh from crowdsourced data for use in 3D mapping and multi-user AR experiences.

With today's augmented reality experiences, we can see and hear virtual content, but Ultrahaptics wants you to be able to feel those experiences, too.