
News: Hackers Claim 1$ Million Bounty for Security Flaw in iOS 9
Hackers are claiming money for a security flaw in Apple's new update. Quick Summary:


Hackers are claiming money for a security flaw in Apple's new update. Quick Summary:
I see many people posting the same thing on the internet. "How do I become a hacker? Where do I commence?"

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

With Halloween fast approaching, social media sites are abuzz with ghosts stories and pictures of cool costumes. By contrast, regular photos just seem to be lacking that macabre feel.

Voodoo you want the best costume this year? You're probably laughing so hard right now that you need to hold yourself together with pins and needles, right?

In this home-science how-to from Household Hacker, we learn how to create an exothermic reaction by combining sulfur with iron, producing iron sulfide in the process. For all of the details, including step-by-step instructions, as well as to see what happens when these two elements meet, watch this video guide.
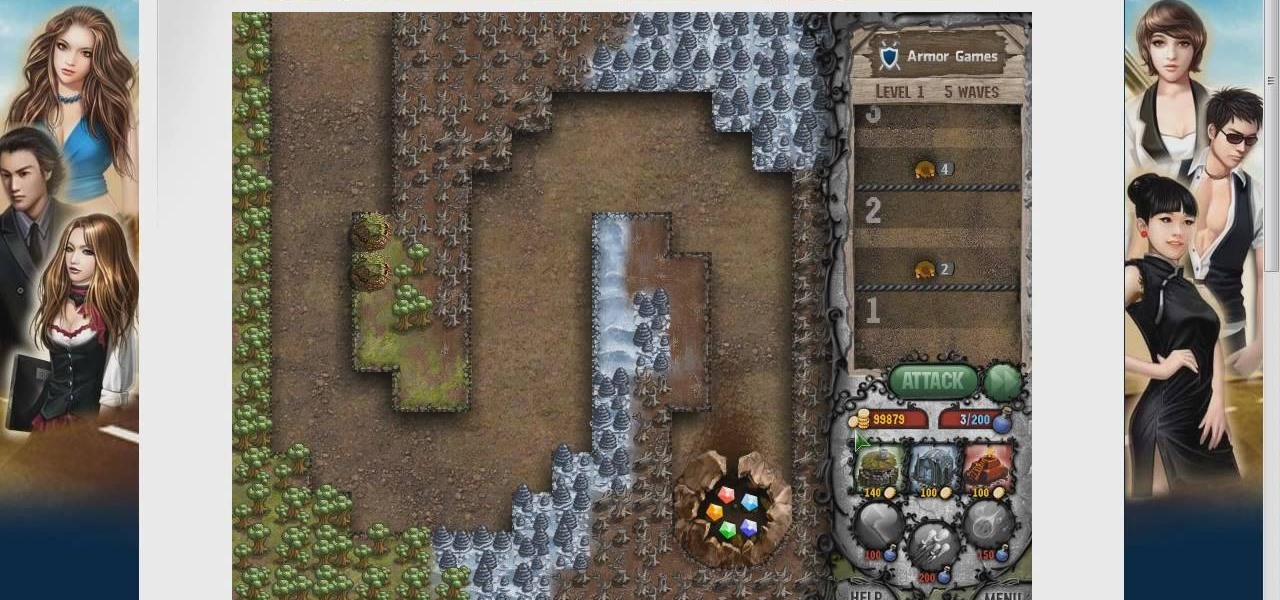
Cursed treasure is a very popular and challenging web game that, like most of it's webgame contemporaries, has attracted a lot of attention from hackers looking to make it easier to cheat in the game. This video shows you how to use cheat engine to get more money and change other numerical values in the game to improve your gameplay experience.

Protect your email account from would-be hackers and crackers with this free video tutorial from the folks at MacMost. If you have a Gmail, HotMail, Yahoo! Mail or other web-based email account, this video is much recommended. For more information, and to secure your own online free email account, watch this helpful guide.

In this how-to video, you will learn how to change your start menu text. You will need resource hacker and regedit in order to perform this. First, open resource hacker. Click file and open. Go to 37, and click on 1033. Change 578 to whatever you want the text on the start menu to be. Press compile script. Next, save this file. Now, open regedit and go to software. Go to shell and click modify. Change the value data to the name of your .exe file, which should be saved in the windows folder. N...

In this video one of the ultimate iPhone hackers, Jonathan A. Zdziarsk, demonstrates how to use a forensics toolkit to recover deleted text messages on an iPhone. But wait - there's more! Not only can you access text messages, but almost any other data on an iPhone as well. We can't be responsible for what you find though!
This how-to video shows how you can hack a standard baseball cap into a cool invisible IR mask to hide your face from cameras anywhere, and look perfectly normal to the human eye! You have to admire a technically accomplished hacker. Now don't go out a rob a bank or anything. Watch this video tutorial and learn how to camera-proof your face with a creepy infrared mask.

It seems like a new, dangerous Android exploit is uncovered every month or two. The latest headliners are NightMonkey and Chronos from the list of CIA hacks reported by Wikileaks, which have been billed as gaping security holes in the world's biggest mobile operating system.

Welcome back, my fledgling hackers! Hacking has a long and storied history in the U.S. and around the world. It did not begin yesterday, or even at the advent of the 21st century, but rather dates back at least 40 years. Of course, once the internet migrated to commercial use in the 1990s, hacking went into hyperdrive.

So, how does someone keep their hacking life completely secret? What This Is:

Each day, we read about another security breach somewhere in our digital world. It has become so commonplace that we hardly react anymore. Target, J.P. Morgan, iCloud, Home Depot, and the list goes on and on.

People who know that I am a professional hacker often ask me what they can do to make their computers and personal information safe from people like me. The answer, of course, is that nothing will make you completely safe, but there are a number of measures any computer user can take to reduce the chances of being a victim of a hacker.

Solo camping is a scary and exciting prospect. Alone in the woods at night, no one can hear you scream. But for those who crave solitude and love the wilderness, there can be no greater thrill, no greater connection to the primitive part of yourself. In this nine-part video, we learn all kinds of useful survival and camping skills by watching our host Colhane experience a three-day solo camping trip in the Brazlilian bush. You will learn how to cook, how to make fire, how to prepare a campsit...

They are after you from all over the globe. Looking for ways to exploit you. Ways to hurt you. Not political terrorists, but rather "info terrorists." Each month thousands of websites get hacked into and have hidden links inserted into the pages by people wanting their spam sites to rank highly in the search engines.

Having a secure password is essential in today's interconnected world. Hackers are just around the corner, and if you have an easy to guess or hack password that you use for all of your accounts, someone can login to all of your websites very easily. Look at this guide on how to create a strong password by following the right password rules so that your accounts stay secure.
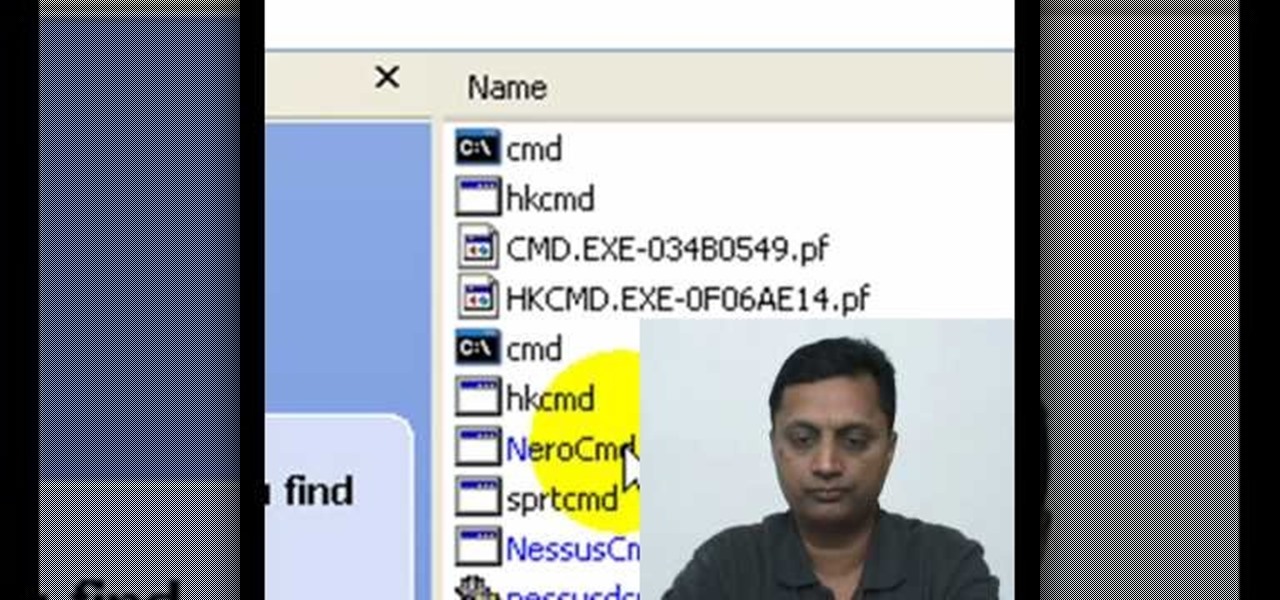
Here is a basic walk-through of how to remove the harmful file known as the cmdd.exe. The cmdd.exe file is a backdoor trojan virus that can allow a hacker remote access to a computer infected with it. Your computer can be infected with this threatening virus at any time and it must be removed immediately. This video provides several techniques that can be used to completely get rid of the file from your computer.

Believe it or not, people are still using Friendster. Which is great news for all you hackers because that means there are accounts to hack! With this video you'll find out how to exploit a programming loop hole in order to hack into someone's Friendster account. We can't promise you'll find anything interesting!

How to hack games on a Mac using iHaxGamez. This is useful for any of the facebook/myspace games. How to hack flash games, using a Mac. Recently, Household hacker made a tutorial on how to do this for PC, I thought I'd show the world how to do it on a mac.
In this episode from Household Hacker, you'll see how to put video ringtones on your cell phone for free. Check the full list of compatible mobile phones over at Vringo to make sure it will work for your cellular phone. This is a really cool alternative to the normal ringtones for mobiles phones!

Need to know how to customize your general system information? It's handy if you build or fix your own systems and want a way to brand them, or just to personalize your system. This is a great tutorial on customizing operating systems in XP by informationleak.net hacker Halla.
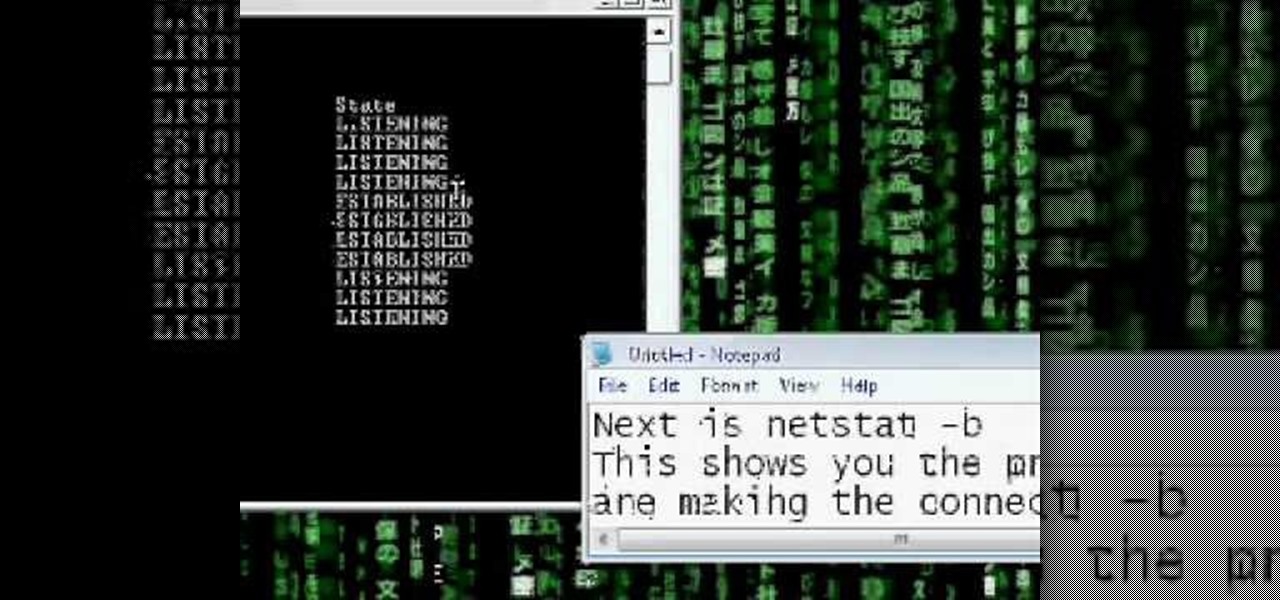
Netstat (network statistics) is a command-line tool that displays network connections (both incoming and outgoing), routing tables, and a number of network interface statistics. It is available on Unix, Unix-like, and Windows NT-based operating systems. This video tutorial presents a basic introduction to working with the netstat tool. Determine whether you've been hacked with this how-to.
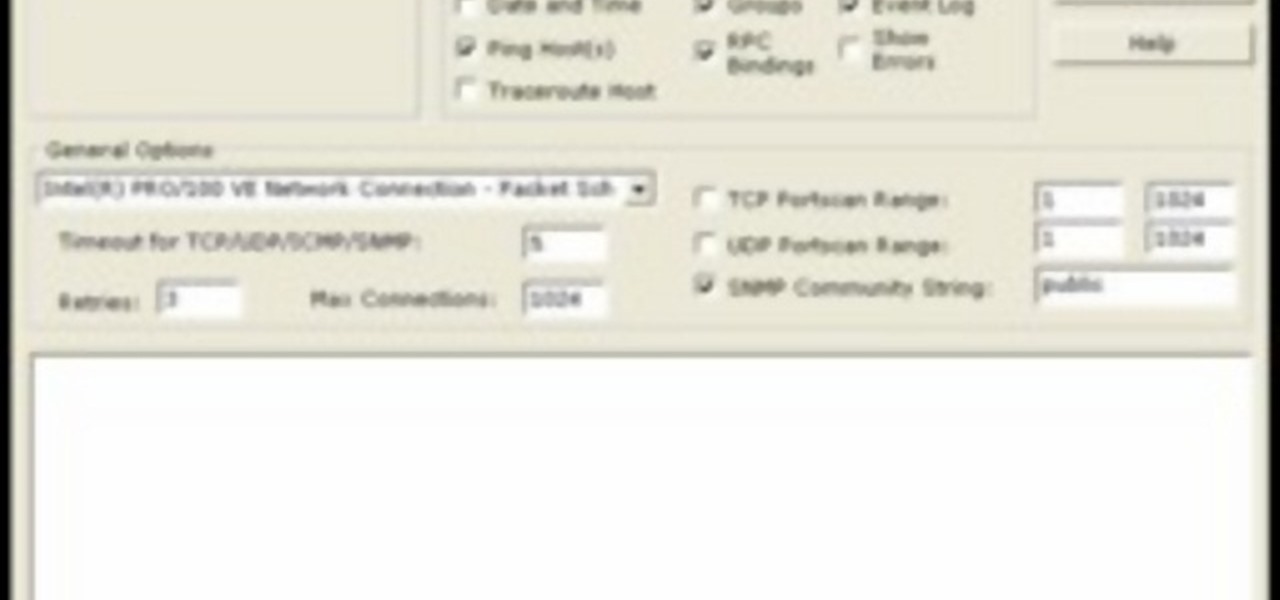
In this video tutorial, a CEH-certified Ethical Hacker will teach you how to exploit the old netbios remote IPC$ share while also demonstrating the beginning stages of a successful network security audit. For more
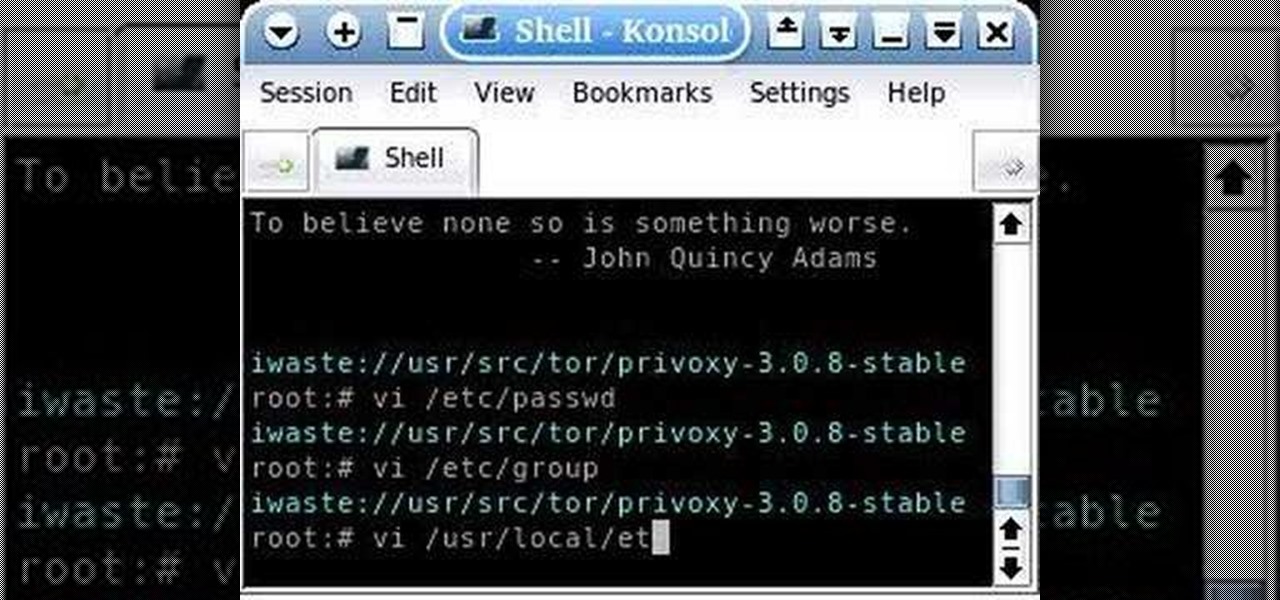
This is a tutorial about how to browse the web anonymously on a Linux server. Requires some knowledge of Linux. Be sure to note that information sent through this system is ever MORE open to hackers than the normal Internet. Don't send any personal information this way.

Every summer for the last 26 years, hoards of hackers have descended on the Las Vegas Strip for DEFCON, the biggest hacker conference in the US. There's a wealth of talks every season (DEFCON 27 has at least 95 scheduled), and there have been some essential topics to learn from in past discussions. We've dug through the last ten years and found the 15 most popular talks you should watch.

There has been significant debate over law enforcement's right to access our digital devices in recent years. New tools from Grayshift and Cellebrite are popping up faster than ever to help government agencies, as well as traditional hackers, break into iPhones. If you're concerned, you can take steps right now to beef up your passcode and prevent outsiders from gaining access to your device.

Millions of travelers pass through airports each day without understanding how powerful and insecure a boarding pass can be. Anyone can scan the boarding pass barcode with a mobile app, allowing access to frequent-flyer accounts and even a passenger's temporary airline account. In this guide, we will explore how hackers scan and decode the information contained in a boarding pass barcode and why.

Cruise Automation, General Motors' (GM) driverless car arm, has hired two hackers who were once seen by many as a safety threat to help find vulnerabilities in its self-drive car network.

Baidu Inc, the "Chinese Google" search engine and technology company, which has been actively pursuing self-driving cars, reported that a gang of hackers recently attempted to steal its driverless car technology.

If you want to make some money from catching bugs and are sick of pentesting Facebook, Google, and Microsoft's products, Uber may be your new favorite playground.

In an article published in early-2015 by Peninsula Press, it was reported that the demand and the salaries for cyber security professionals are exploding! They cite that 209,000 cyber security jobs were unfilled last year, and that job postings have increased over 74% in the last 5 years. Job opening are expected to grow by another 53% over the next 3 years. You are definitely in the right field, my tenderfoot hackers! Some researchers are expecting information security jobs to continue to gr...

Hello, my web huggers! In today's tutorial we will learn how to use the Google Hacking Database (GHDB) developed by Exploit Database, to find vulnerable web servers and "juicy" information.
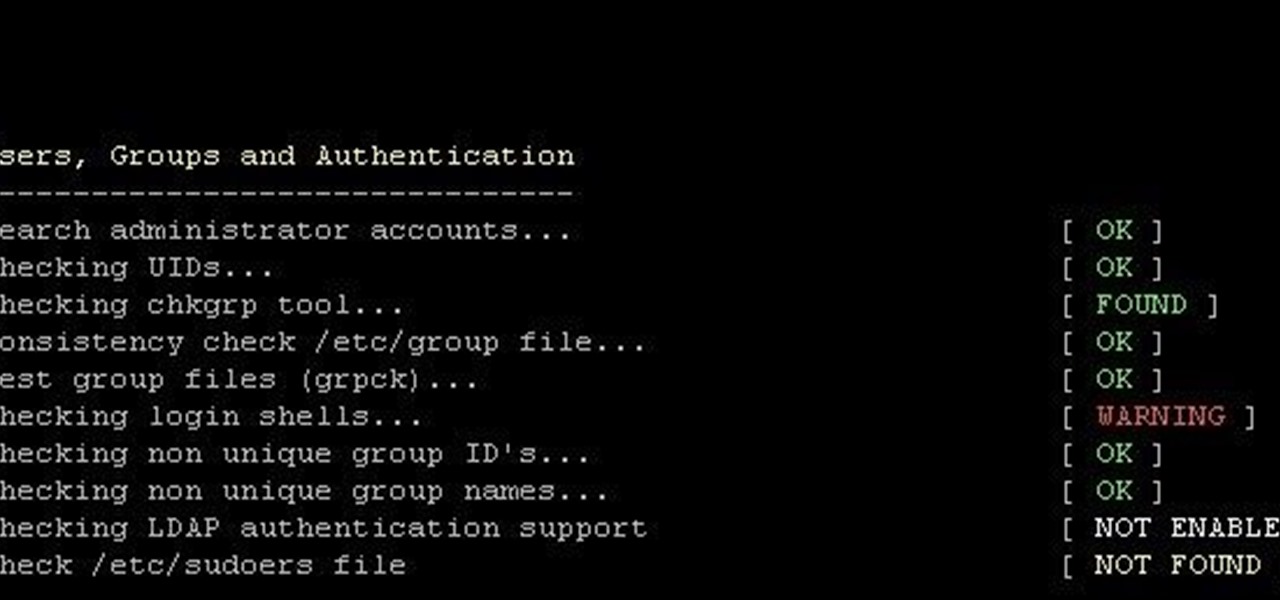
This is finding some of your vulnerability using Lynis. This tool Lynis is used on Unix and Linux type operating systems (sorry windows). So lets get started

Parties are a great way to celebrate and have fun with your good friends, so to make sure your next party rocks, I've assembled some of the biggest life-hackers on YouTube to bring you 10 outrageous party tricks your guests will not forget.

Incorporating features such as CarPlay, UI enhancements such as the new call screen, and several bug fixes, iOS 7.1 was the first major update to Apple's operating system since iOS 7 was released in June of last year.
Last week, Apple issued an iOS 7.0.6 update that fixed a serious security vulnerability that could allow hackers to steal passwords, read emails, and get info from other SSL-encrypted communications.

Just days after news spread that Snapchat could be exploited by spammers, an anonymous group of hackers have released the private information of over 4 million users of the popular photo-sharing application.