
Scary Hackers Search Results

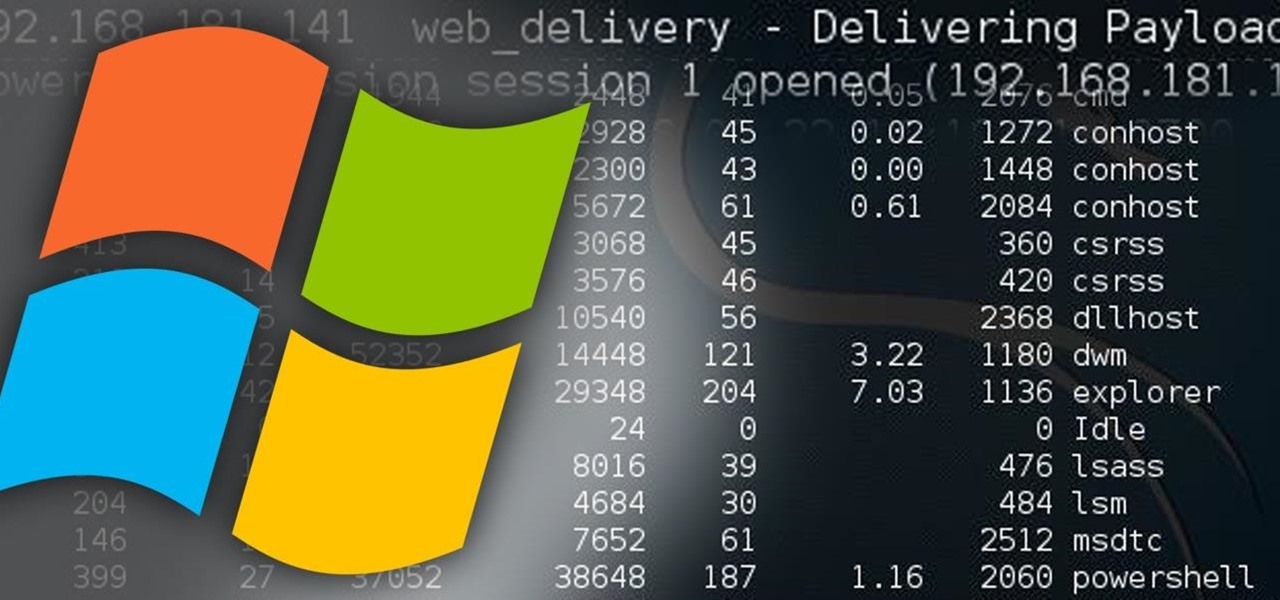
Hack Like a Pro: Metasploit for the Aspiring Hacker, Part 13 (Web Delivery for Windows)
Welcome back, my hacker novitiates! In the previous part of this series, we looked at how to use Metasploit's web delivery exploit to create a script to connect to a UNIX, Linux, or OS X machine using Python. Many members of the Null Byte community have asked me, "Can we do the same for a Windows systems?" The answer is YES!

How To: Keeping Your Hacking Identity Secret - #2
My first ever post on here was 'Keeping your hacking identity secret' and it did very well, and its not something I see here on null byte. So read along.

How To: Successfully Hack a Website in 2016!
Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, to say that I'm always willing to learn and teach. I'm also open to answer the appropriate questions.
News: You've Been Hacked
Greetings null-bytians. Firstly, I would like to apologize for the no images thing. I guess I can't upload them.

How To: Adobe Flash Player Is Bad for Your Computer (Here's How You Uninstall It)
Roughly four years ago, Adobe decided to abandon development of the mobile version of their popular Flash Player browser plugin. Their excuse at the time was that this move would enable them to focus more on HTML5 development for mobile devices and allow them to put more effort into maintaining the fluidity and security of their desktop Flash plugin.

The Hacks of Mr. Robot: How Elliot & Fsociety Made Their Hack of Evil Corp Untraceable
Welcome back, my tenderfoot hackers! Well, the first season of Mr. Robot just ended and Elliot and fsociety successfully took down Evil Corp! They have effectively destroyed over 70% of the world's consumer and student debt! Free at last! Free at last! Of course, global financial markets crashed as well, but that's another story.

Hack Like a Pro: How to Install & Use a Secure IRC Client with OTR
Welcome back, my amateur hackers! As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.

News: A Game of Real Hacking
Bad news first: It's not out yet, but it's coming really soon. The premise for the game is this:
News: How to Hack Time
Watched a great guide on hacking things through time by the most powerful hacker on the planet, Hackerman.

Hack Like a Pro: Metasploit for the Aspiring Hacker, Part 8 (Setting Up a Fake SMB Server to Capture Domain Passwords)
Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

How To: Post to Null Byte [4.10.15 Revision]
Hello readers, and welcome to Null Byte. Before we start, for those of you who may not know me, my name is ghost_; I'm a relatively active member of our community and have been around for a while.

Hack Like a Pro: How to Hack Facebook (Facebook Password Extractor)
Welcome back, my novice hackers! As we saw in my first tutorial on Facebook hacking, it is not a simple task. However, with the right skills and tools, as well as persistence and ingenuity, nothing is beyond our capabilities.

Advice from a Real Hacker: How to Know if You've Been Hacked
It seems like every day now that we see a new headline on a cyber security breach. These headlines usually involve millions of records being stolen from some large financial institution or retailer. What doesn't reach the headlines are the many individual breaches that happen millions of times a day, all over the world.
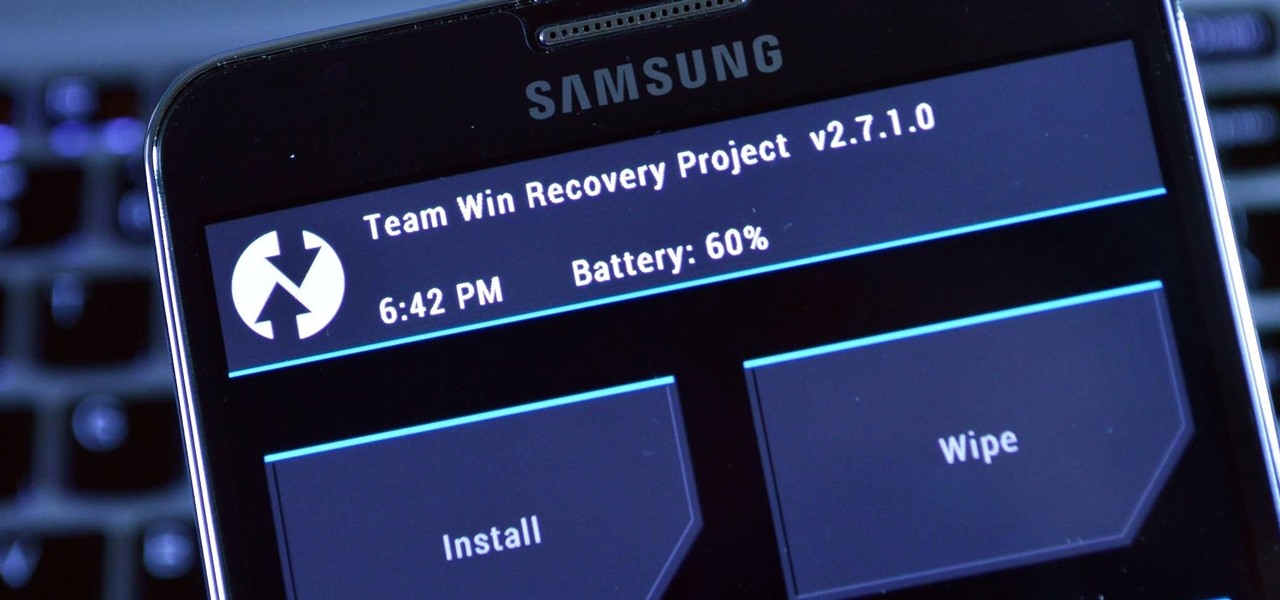
How To: Install TWRP Recovery on Your Samsung Galaxy Note 3 (Sprint or T-Mobile)
As we near the one-year anniversary of its release (and the inevitable unveiling of its successor), the Samsung Galaxy Note 3 remains a device that packs quite a punch when it comes to hardware. It boasts a 2.3Ghz CPU and was the first mobile phone ever to house 3GBs of RAM. Suffice it to say, it can handle any software you throw at it with no discernible lag. Even Samsung's notoriously bloated TouchWiz ROM seems lightning fast.

Hack Like a Pro: Digital Forensics Using Kali, Part 1 (The Tools of a Forensic Investigator)
Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 months ago on just that, we have changed hacking platforms from BackTrack to Kali, which has a much more highly developed forensic toolset.

Hack Like a Pro: Perl Scripting for the Aspiring Hacker, Part 2 (Building a Port Scanner)
Welcome back, my fledgling hackers! Scripting skills are essential is ascending to the upper echelons of the hacker clique. Without scripting skills, you are dependent upon others to develop your tools. When others develop your tools, you will always be behind the curve in the battle against security admins.

Hack Like a Pro: How to Fingerprint Web Servers Using Httprint
Welcome back, my greenhorn hackers! Earlier in this series, I showed a you a couple of different ways of fingerprinting webservers. Probably the easiest way, is to use netcat and connect to port 80 and pull the webserver banner.

Hack Like a Pro: How to Scan the Globe for Vulnerable Ports & Services
Welcome back, my hacker novitiates! Finding vulnerabilities in systems can be one of the most time-consuming tasks for a hacker. There will be times, though, when you'll find yourself in a position that you know that a particular port represents a vulnerable application or service.
Become an Elite Hacker Part 4: Hacking a Website. [Part 1]
Welcome back my fellow army of hackers! Today we'll be hacking a website. Hacking is technically not the right word used here. It should be defacing! So we are going to deface a website...

How To: Find Out If the FBI Is Keeping Tabs on Your Apple Device (UPDATED)
It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...
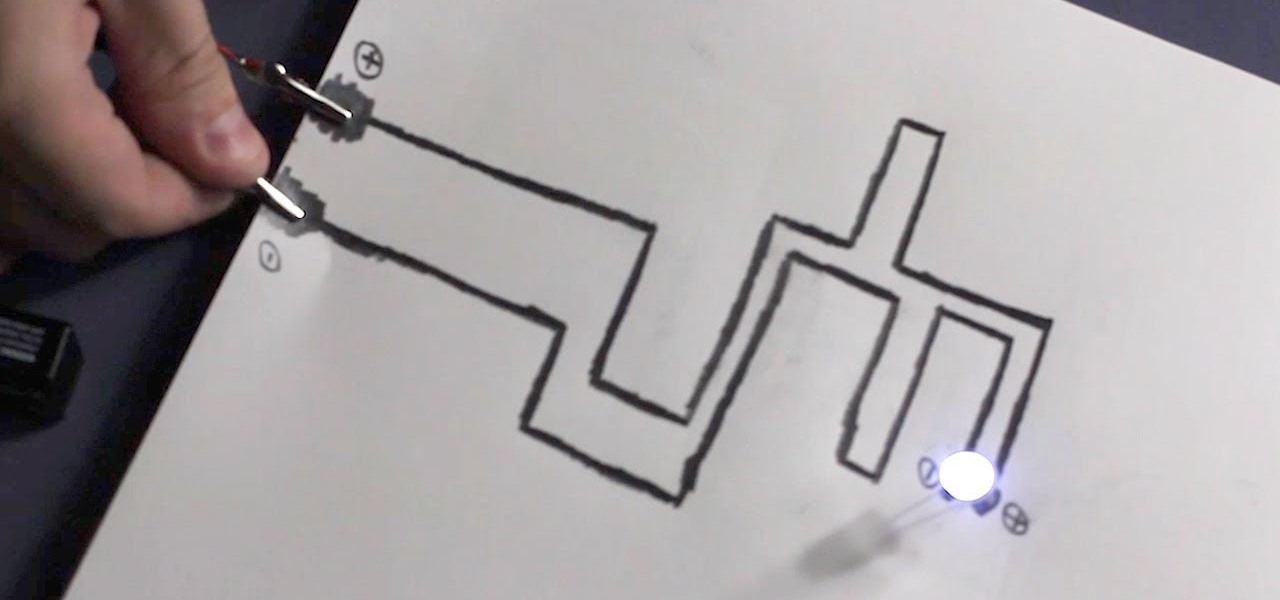
How To: Make a Functional Circuit—On Paper!
With this video tutorial from Household Hacker, you will learn how to make a functional circuit on paper. Really—on paper! See how to make an LED light up with a lead-based paper circuit and how to make a resistor on that circuit. It also shows how to make a flashlight out of one of these paper circuits, an LED, and a battery.

How to Hack Like a Pro: Getting Started with Metasploit
This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:
How To: Kick someone off of Xbox live with a host booter
Using Cain & Able and a host booter, you can kick someone off of Xbox Live. If you are annoyed with another player, this is how you take their ball and throw it into the scary old man neighbor's yard.

How To: Play "Watch Me Bleed" on piano or keyboard
Learn how to play the song "Watch Me Bleed" By Scary Kids Scaring Kids on the piano or keyboard with this step by step tutorial. This video teaches you each part slowly so it is easy to follow and play. Watch this lesson and you'll be playing "Watch Me Bleed" in no time.

How To: Time Management Will Never Be an Issue Again with This 7-Course Work from Home Bundle
While there are many advantages to working from home, properly managing your time can be a real issue. Working remotely requires a particular skill set, including an ability to focus, self-motivate, and communicate from a distance. Thankfully, all of these skills are teachable.

How To: Boost Internet Speeds & Hide Your Browsing History from Your ISP
If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to combat them.

Hacking Windows 10: How to Remotely Record & Listen to the Microphone of a Hacked Computer
The microphone in a Windows computer is accessible to most applications running on the device at all times and completely without security limitations. Information gathered from recorded audio conversations taking place in the surrounding area of a compromised computer can be used for social engineering, blackmail, or any number of other reasons.

How To: 4 Apps to Help Keep Your Android Device Secure
As of 2016, there are approximately 1.85 billion Android smartphones worldwide. This growing popularity has led to an increasing number hacks and cyber attacks against the OS. Unfortunately, Android users need more protection than what is offered by Google. The good thing is that there are a number of options available.

News: Mastercard, Qualcomm-Powered ODG Smartglasses Use Iris Authentication for AR Shopping
As the level of data being generated grows exponentially, past the Information Age and into the coming Hyper-Information Age of immersive computing — as resistant as many of us are to the idea — personal data security is becoming a necessary consideration in our everyday lives. Recognizing this, Mastercard, Qualcomm, and Osterhout Design Group have teamed up to show what secure shopping could look like in the very near future with iris authentication.

News: Malware Targets Mac Users Through Well-Played Phishing Attack
Maybe you thought sitting behind a Mac gives you special protection when it comes to getting hacked. Thanks to a a new report from Check Point, you can kiss that theory goodbye. The cyber security company just uncovered the latest strain of malware — OSX/Dok — infecting all versions of macOS (previously Mac OS X).

Hack Like a Pro: Reconnaissance with Recon-Ng, Part 1 (Getting Started)
Welcome back, my novice hackers! As many of you know, recon is crucial to a successful hack/pentest. In most cases, hackers spend more time doing good reconnaissance than actually hacking. Without proper recon, you are simply guessing at what type of approach or exploit is going to work and, as a result, your time is wasted without any useful outcomes.

Hack Like a Pro: How to Use PowerSploit, Part 1 (Evading Antivirus Software)
Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

Hack Like a Pro: Capturing Zero-Day Exploits in the Wild with a Dionaea Honeypot, Part 2 (Configuration)
Welcome back, my rookie hackers! The Golden Fleece of hackers is to develop a zero-day exploit, an exploit that has not been seen by antivirus (AV) software or and intrusion detection system (IDS). A zero-day exploit is capable of skating right past these defenses as they do not contain a signature or another way of detecting them.

Hack Like a Pro: How to Hack Like the NSA (Using Quantum Insert)
Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA did embed a backdoor on those devices.)

How To: Gathering Sensitive Information: How a Hacker Doesn't Get DoXed
before I move on to more exciting areas in this series, I want to also point out some things to protect your information & how to not get DoXed.

How To: Linux Basics for the Aspiring Hacker: Managing Hard Drives
Managing hard drives in Linux is crucial to understanding your system and its operation as well as understanding the system you are exploiting or conducting a forensic analysis on. Linux has numerous commands that can provide us with information, control, and management of hard drives, and in this tutorial, we will examine a number of the most important ones.

TypoGuy Explaining Anonymity: Choosing a Good VPN
You want to become anonymous, and dont want your IP to be logged on websites? Well read along here. Continuing This Series:
News: The Consequences of Hacking
Mostly all hackers like to have a laugh. We like to have fun! We like to troll. And maybe, even cause some havoc once in a while. But, while we do this, we must always stay in the line of the law.

Cyberwar: Hacker vs. Hacker
From time immemorial, human beings seem to be at odds with one another. When these differences become so heated and unresolvable, it eventually erodes into physical violence. This violence has manifested into some of the most horrific exercises in human history, things which every school child is aware of and none of which we have to recount here. Although humans have been cruel and violent for a very long time, the 20th century may have epitomized that behavior. With two World Wars and many,...

