
SPLOIT: Cryptography Is a Bitch (Ransomware Development): Part 1: Introduction to the Ransomware World
Greetings my fellow aspiring hackers,


Greetings my fellow aspiring hackers,
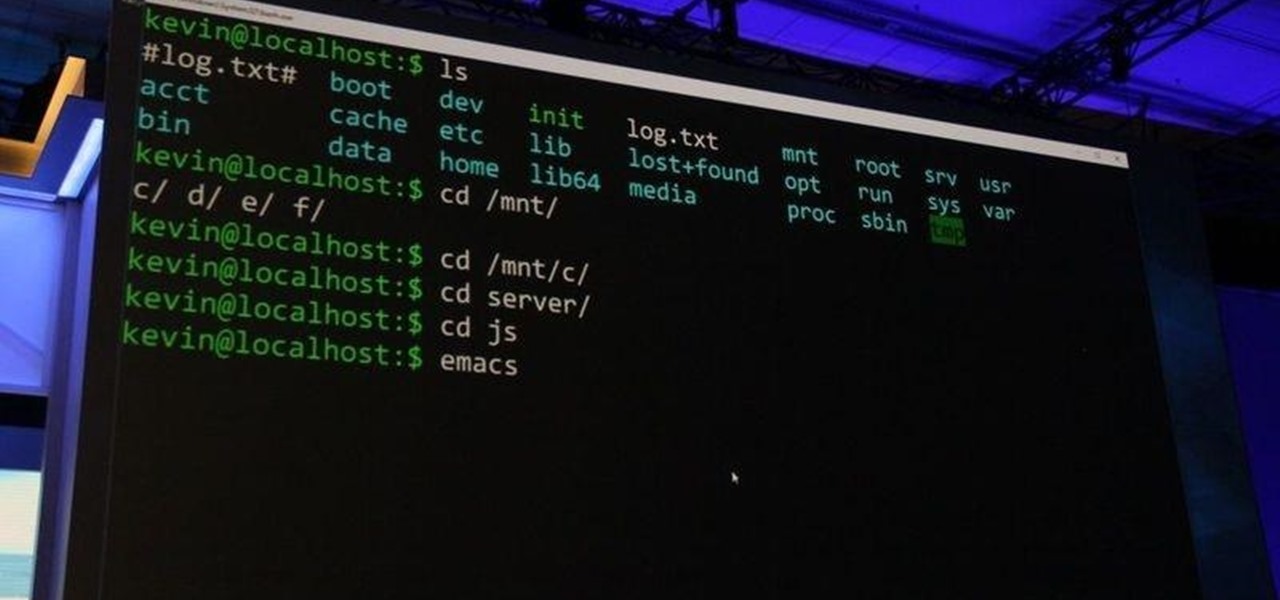
As most of you know, I am a strong advocate for using Linux for hacking. In fact, I would go so far as to say that you cannot be a hacker without knowing Linux well. I laid out various reasons for this in my "Why Every Hacker Should Know & Use Linux" article, and I even have a lengthy, continuing series on Linux Basics to help those new to Linux master it.
Researchers at MIT's Computer Science and Artificial Intelligence Laboratory have created Wi-Fi technology that identifies where you are, which may eliminate the need for passwords.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

Greetings my fellow aspiring hackers,

Welcome back, my greenhorn hackers! As expected with Null Byte's dramatic growth over the last year, we have added many new aspiring hackers who are still lacking in the basics of networking. In addition, with the new "White Hat" certifications coming out shortly, the exam will require some basic networking skills and knowledge to pass.
Hello! My name is An0nex. I am an ethical hacker who wants to share the art of hacking with all of you guys!
T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Welcome back, my hacker novitiates! In an earlier Linux Basics tutorial, I had demonstrated the basics of the Apache web server. Since Apache is the world's most widely used web server on the Internet (as of July 2015, Apache was 38%, IIS was 26%, and Nginx is 15%), the more you know about it and understand it, the more success you are likely to have hacking it.

One thing the whole Internet can agree with is that cats are cute and (sometimes) cuddly. But what those endless cat videos you find yourself watching for hours on YouTube don't tell you is that cats stink. While cats aren't the source of the smell, owning a cat means a stinky litter box.

Welcome back, my greenhorn hackers! One of the most important issues any hacker must address is how to get past security devices and remain undetected. These can include antivirus software, intrusion detection systems, firewalls, web application firewalls, and numerous others. As nearly all of these devices employ a signature-based detection scheme where they maintain a database of known exploits and payload signatures, the key is to either:

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.
With troves of sensitive information, like receipts and password reminders, hiding in your email, your inbox can become a sort of Holy Grail for hackers—or anyone with your password. Although my crazy ex-girlfriend had no hacking experience, using my email login, she was able to find a lot of account information with just a general search for "password" in my inbox.
A group ironically called the "Guardians of Peace" hacked into Sony Pictures' computer systems and released a mountain of internal information such as medical records, leaked scripts, work complaints, and even celebrity aliases.

Welcome back, my tenderfoot hackers! As you know, Metasploit is an exploitation framework that every hacker should be knowledgeable of and skilled at. It is one of my favorite hacking tools available.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"

Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

Welcome back, my greenhorn hackers! Several of you have you have emailed me asking whether it's possible to install a keylogger on a victim’s computer using Metasploit. The answer is a resounding "YES"!

Sprint has announced that it will be the first U.S. carrier to release Jelly Bean 4.1 for the Samsung Galaxy S III. The over-the-air updates have already started, with users receiving a notification on how to update on their phone. The reason Jelly Bean has garnered so much attention is due to several, well-known features like Google Talk, Project Butter and expandable notifications.

Apple and AT&T can keep changing the baseband and the firmware on the iPhone as much as they want and hackers are gonna stay ahead of them, especially now that jailbreaking is legal. This new video will show you how to unlock a jailbroken iPhone 3G or 3GS with iOS version 3.1.3 or 4.0.1 and basebands 5.12.01, 5.13.04, 5.11.07, and 4.28.08. Now you can use it on any carrier, breaking free of AT&T's crappy network for good.

Want to hack a LAN? Well, hacking local area networks is easier than you'd think. And by watching a few short videos, you can become a master hacker, something every techie wants to achieve. And what's the best way to hack a LAN? Ettercap, a password sniffing program.

Homemade Halloween costumes that exhibit the maker's creativity are always better than off-the-shelf versions. It turns out that the same is true with virtual costumers.

Imagine being able to play a video instantly on hundreds of thousands of devices across the globe. It's totally possible, as long as all of those devices have a Chromecast plugged in. When Chromecasts are left exposed to the internet, hackers can use add them to a botnet that can play YouTube videos at will. The "attack" is made even easier thanks to a simple Python program called CrashCast.
Intel's RealSense family of depth tracking cameras has a new addition with a different set of sensory capabilities.

The latest sponsored augmented reality experience on Snapchat from a movie studio might be its scariest — and perhaps most popular — yet.

One downside to iOS 11's awesome built-in QR code scanner in the Camera app is its only been live for a short while. In its short life, there has already been a security vulnerability discovered that was an issue for at least the last 4.5 months, but Apple has finally patched this weakness with its iOS 11.3.1 update.

After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

While there are tools online that let you turn photos into interesting emoji art, and mobile apps that let you create emoji mosaics, none do it better than an iPhone app by second verse, which makes it a super easy, highly customizable process.

Who doesn't love the world of Game of Thrones? Whether you're a fan of the hit HBO show, or can't wait for George R. R. Martin's next novel installment, it's a story loved by nearly everyone. It's an excellent source of inspiration for Halloween costumes too, ranging from the disturbed to the beautiful. Lady Stoneheart, Catelyn Stark risen from the dead, is the perfect scary choice—bloodied, battered, and carrying a desire for vengeance.
Welcome back, my hacking friends. We use our smartphones every day, for business, socialization, and leisure. The number of iPhone users is increasing in dozens of millions every year, with a whopping 63.2 million users in 2014 alone. That's a lot of users.

White rice is cheap, filling, and tasty. No wonder so many countries in the world rely on it as a mealtime staple, including most of East and Southeast Asia. Alas, because of its relative lack of nutrition and its high calorie count, consuming lots of white rice regularly also puts people at risk for diseases like diabetes and obesity.

The weather outside might be frightful, but heating bills are downright scary this time of year. Heat is absolutely essential during the winter season, but it's also really expensive. If you aren't blessed with a fireplace or unlimited disposable income, fear not, because you can still heat your home on the cheap using flower pots and tea lights—even if the power goes out.

Facebook today has unleashed a new way to creep...er...keep in touch with "friends" using the official Facebook apps on Android and iOS.
Even if you have the fastest internet connection in the world, it's not going to be fast if your Android device isn't optimized to use all of the bandwidth. I have pretty fast speeds at home, but every now and then my web surfing on my Nexus 7 tablet is halted in its tracks—for seemingly no reason.

Need to add some spooky ambient fog to your super-scary Halloween party? Rather than shelling out money for a fog machine you'll probably only use once a year, make a trip to the nearest drug store and pick up a bottle of glycerin, a gallon of distilled water, a 2-liter bottle of cola, a disposable mini-pie tin, and a big candle in a jar.

Notch loves Halloween. He must, because he keeps putting scarier and scarier things into Minecraft around Halloween time!

When you're a kid, the best part about Halloween is the free candy, but if you're past your trick-or-treating years, there are still plenty of things you can do. With all the costumes, scary stories, and pranks, what's not to love? And now, you can even use your smartphone to celebrate.

The "Hacker" style was created for hackwars.net for their avatar system. You can basically take the simple shapes as seen at first in the video and draw pretty much any kind of character. Just go wild! Don't forget to add the thick black line around the outside. It really makes this style. Check out this video drawing tutorial and learn how to sketch a Hacker style kid with a bazooka.

What if you could have a secret hard drive connected to your computer that only you could activate? You can! Samimy shows you how to hack a remote controlled toy car and make a super secret hard disk drive in your computer, accessed via a secret activation key. This hidden emergency HDD can only be controlled by your key, regardless of how many people use your computer.