Cheaters may never win but, boy, do they ever get high scores. With this hacker's how-to, you'll learn how to use Cheat Engine 5.5 to earn an absurd amount of points, guarunteeing yourself a spot on the high scores list.

Halloween doesn't have to mean frightful garb and spooky makeup. Have yourself a pretty Halloween and send smiles to your friends' faces rather than shrieks of fear by dressing up as the iconic Hello Kitty.

Halloween is a spooky time filled with eerie parties, scary Haunted Houses, and more candy than can fill all the barrels in Donkey Kong. Create an elegant way to get your sugar fix this All Hallow's Eve by baking and caking a fondant-covered jack-o-lantern cake.

Most of us use a multi-blade pivot head razor, in the hope that we will get a closer shave. But did you know that you can get a close, comfortable shave with a good wet lather and single blade safety razor. This two part hair removal tutorial teaches you how to make the transition to shaving with a single-bladed razor. This is much cheaper way to shave. It may seem scary at first, but with a bit of practice you will be getting a close shave with a single blade razor.

This tutorial video will show you how to contour and highlight your skin with makeup. Contours are "shadows" so you want to go darker than your actual skin tone.

In this how-to video from Household Hacker, we show you how to disguise a common household item as a safe to hide all your goodies in.

In this April Fool's edition of Household Hacker, we will show you how to prank a roommate, sibling or anyone really.... Follow the video instructions and have a fun day. First the table smash, then the toilet spray & finally, the tire balloon prank. Use this as inspiration for one of your April Fools Day pranks!

There are countless ways in which you can turn your love of tech and coding into a full-fledged career — from developing apps and websites as a freelancer to working in the IT departments of small startups or major tech companies. But one of the best ways that you can put your programming skills to good use is to join the increasingly important world of cybersecurity.

I mentioned in one of my earlier articles something about ghost hackers, and very shortly stated a thing or two of what they do.

I found this article a while back and I found it underneath a bunch of junk. Anyway, it's a article on 9 notorious hacker including Walter O'Brien (You know the T.V. show Scorpion? Well that's him). Not to mention the weird names:

Welcome back, my rookie hackers!
Hello and welcome to my article. I have made this article for anyone who wants to become a hacker, and wants to know how to get started.

Welcome back, my hacker novitiates!

Welcome back, my aspiring hackers! Those of you who've been reading my tutorials for some time now know that I am adamant regarding the necessity of learning and using Linux to hack. There is no substitute, period.

Do you own an HP printer? If so, it may be vulnerable to malware attacks. Researchers at Columbia University discovered that 25% of Hewlett-Packard printers have significant vulnerabilities that put your printer in danger from hackers—even your home. With a budget of just $2,000, researchers Salvatore Stolfo and Ang Cui were able to hack into the printers using remote firmware to install malware, and in some cases even cause the printer to catch on fire. The main issue is with the printer's c...

Play all of your favorite Nintendo games on your Apple iPhone, iPad or iPod Touch! In this iPhone hacker's how-to, we learn how to use Cydia to download and install a Nintendo Entertainment System (NES) emulator on a jailbroken Apple mobile device.

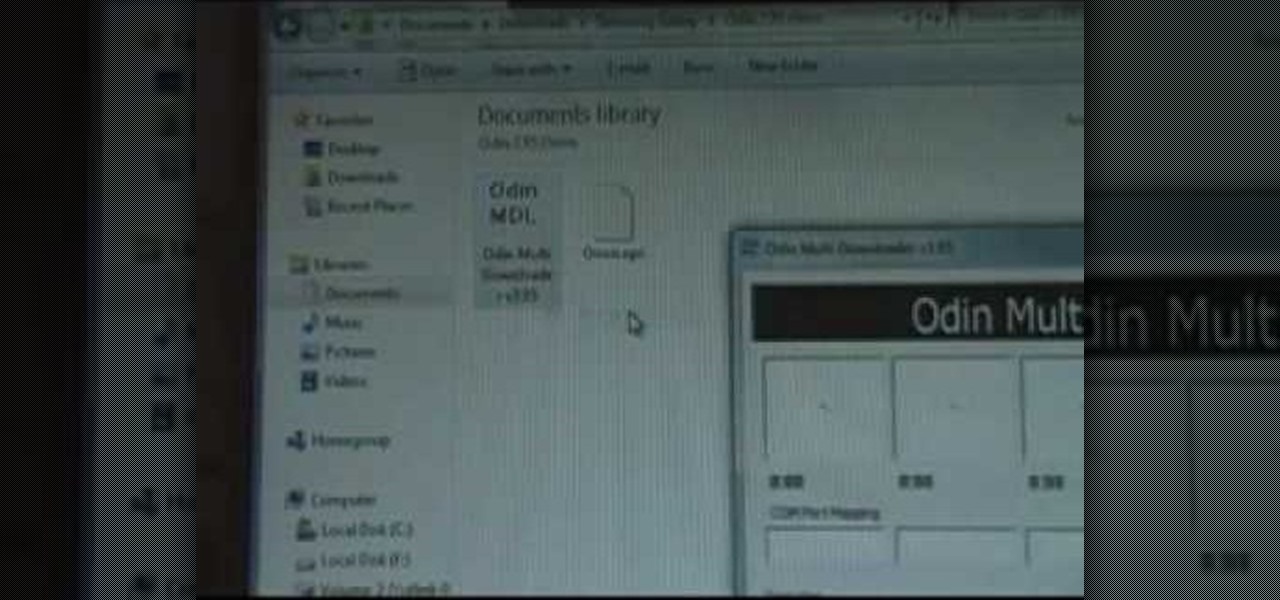
Rooter's remorse! It's a common affliction. So what do you do when you want to restore your Samsung Galaxy's factory firmware and put your mobile phone back as it was? This video's got the goods.

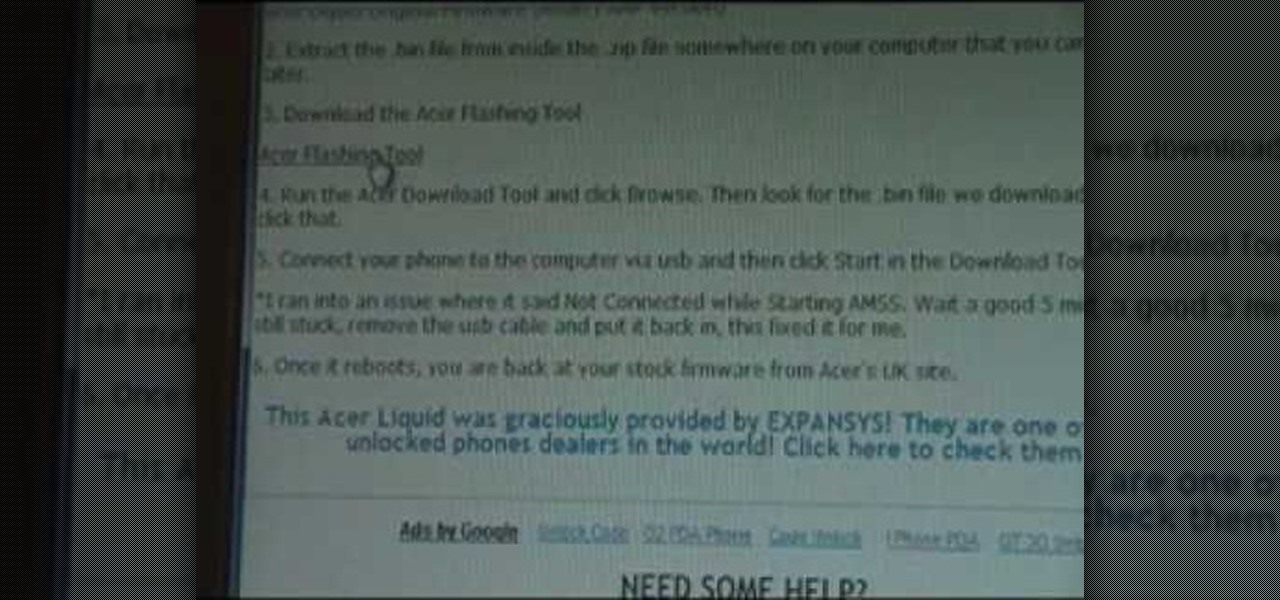
Rooter's remorse! It's a common affliction. So what do you do when you want to restore your Acer Liquid's factory firmware and put your mobile phone back as it was? This video's got the goods.

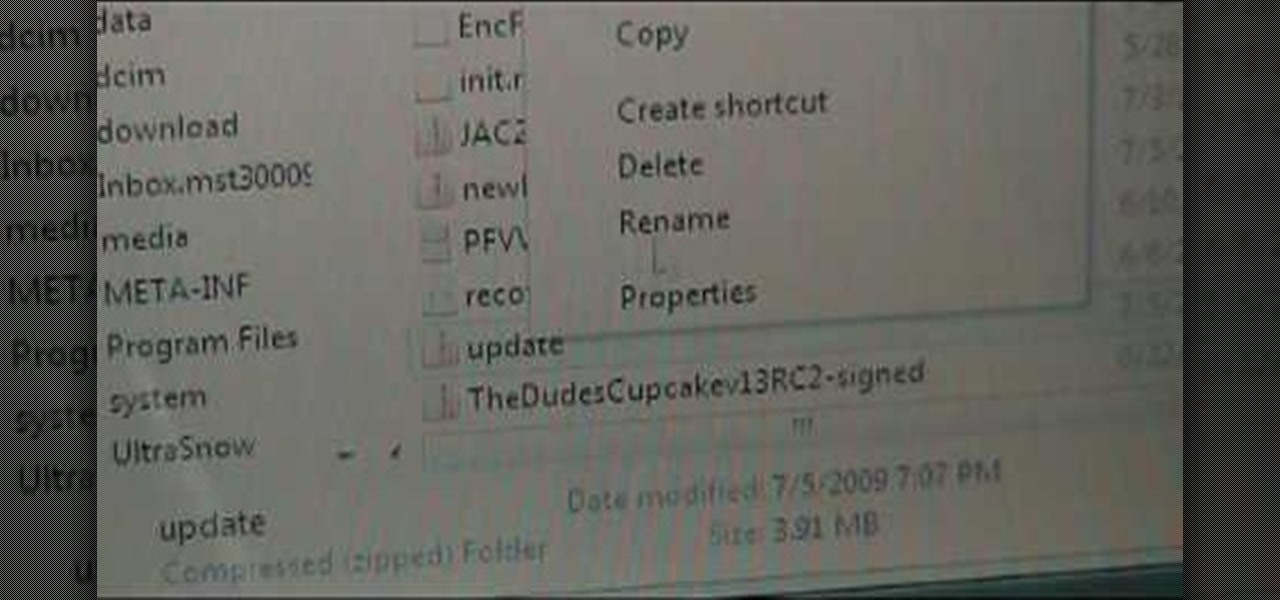
Want to set up WiFi tethering on your rooted T-Mobile G1 cell phone? How about save space by moving apps and onto your phone's SD card? Multi-touch? It's easy! All you have to do is install a custom ROM! Learn how to load a costom ROM onto your T-Mobile G1 Google Android smartphone with this six-minute mobile phone hacker's how-to.

Interested in loading a custom Hero ROM onto your MyTouch 3G Google Android smartphone? You'll need to root it first. Happily, it's a very easy process. And this three-part hacker's how-to will teach you everything you'll need to know. Learn how to root and install a Hero ROM on your MyTouch 3G or HTC Magic with this video rooting walkthrough.

Interested in rooting your Sprint HTC Evo 4G Google Android smartphone but aren't sure how to proceed? Never fear: this three-part hacker's how-to presents a complete step-by-step overview of the rooting process. For the specifics, and to get started rooting your own HTC Evo 4G cell phone, take a look.

In this clip, you'll learn how to jailbreak an iOS 4 Apple iPod Touch with version .9.5 of the redsn0w jailbreaking tool. It's easy! So easy, in fact, that this hacker's how-to can present a complete overview of the process in just over four minutes. For more information, including step-by-step instructions, and to get started jailbreaking your own Apple mobile device, watch this video guide.

Jewelry clasps don't seem all that important, right? After all, when compared to the shape of your beads and the color scheme of your jewelry piece, a clasp is merely the finisher, something that helps close off your necklace.

Certain aspects of Windows User Interface are not customizable like the text of the start button in Windows XP. However you can use certain tools and follow a procedure to change the default text of the start button. To do this you have to use a tool called Resource Hacker. Note that this is a very simple method, but be careful or you may end up causing damage to the Operating System as you are modifying system files. To do this run the program. Now browse to the Windows folder and locate win...

Got 3D glasses leftover from the Superbowl? Time to break them out! You will need cheap 3D glasses from television promotions or you can grab them off eBay for this demonstration. Or you can simply make your own 3D glasses red and blue or yellow and blue cellophane.

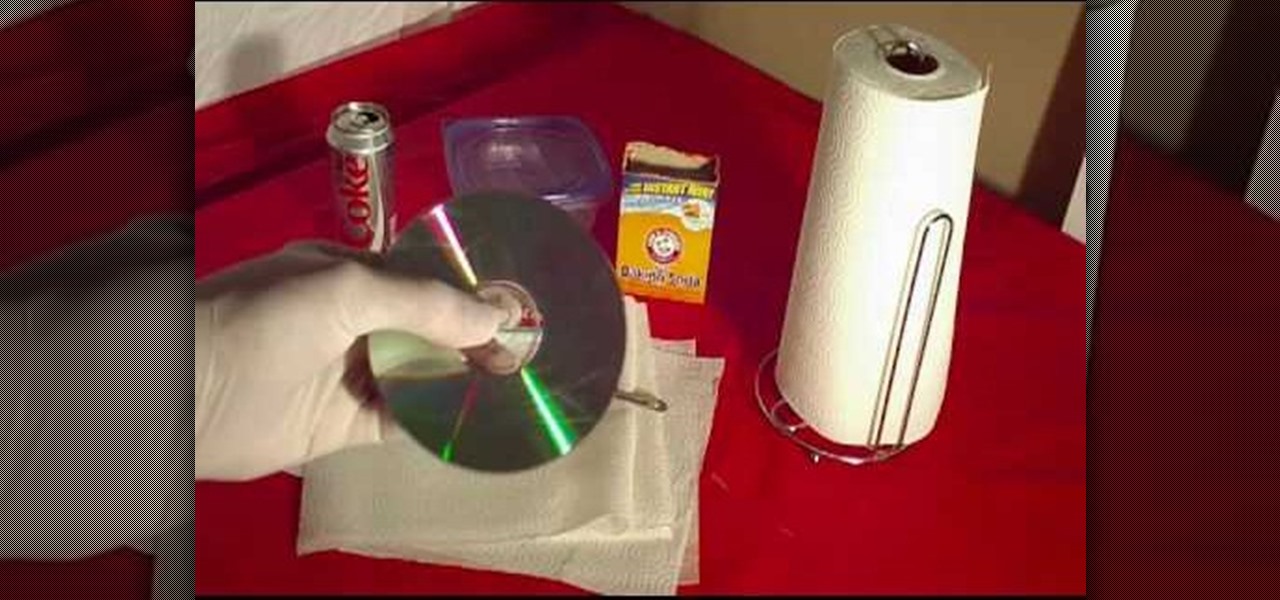
In this Household Hacker experiment, we'll demonstrate how to completely remove scratches from your CD or DVD media.

For the uninitiated, it can be difficult to buy that special hacker in your life a perfect holiday gift. That's why we've taken out the guesswork and curated a list of the top 20 most popular items our readers are buying. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2018 selection of hacker holiday gifts.

The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East.

A scary piece of malware just got a lot more terrifying this week. Security firm Comodo reports that "Tordow," a banking Trojan first uncovered in September 2016, received a massive update this December.

A while back, I wrote review of my favorite hacking movies of all time. Two of my key criteria were; (1) how realistic was the hacking, and (2) are the hackers portrayed as the "good guys." This past winter, a new hacker movie was released, appropriately named Blackhat starring Chris Hemsworth (from Thor fame) as a blackhat hacker who is released from prison to stop a notorious and destructive hacker that only he can stop. Although the movie did very poorly at the box office, I thought it was...

By now, nearly everyone with any type of media access is aware that Sony Pictures Entertainment was hacked on November 24th. Although there can be many interpretations and lessons drawn from this audacious act, there is one indisputable conclusion: it and its ripples across the globe underlines how important hacking has become in our all-digital 21st century. As I have emphasized so many times in this column, hacking is the discipline of the future. From cybercrime to cyber intelligence to cy...

Something pretty awesome happened over the last couple of days. George Hotz, better known as Geohot, the infamous hacker known for jailbreaking iOS and exploiting the Sony Playstation 3, has brought joy to owners of just about all Android smartphones and tablets, especially those on AT&T and Verizon.

If your facebook account was hacked by someone and you really want it back this tutorial would help you get it back.

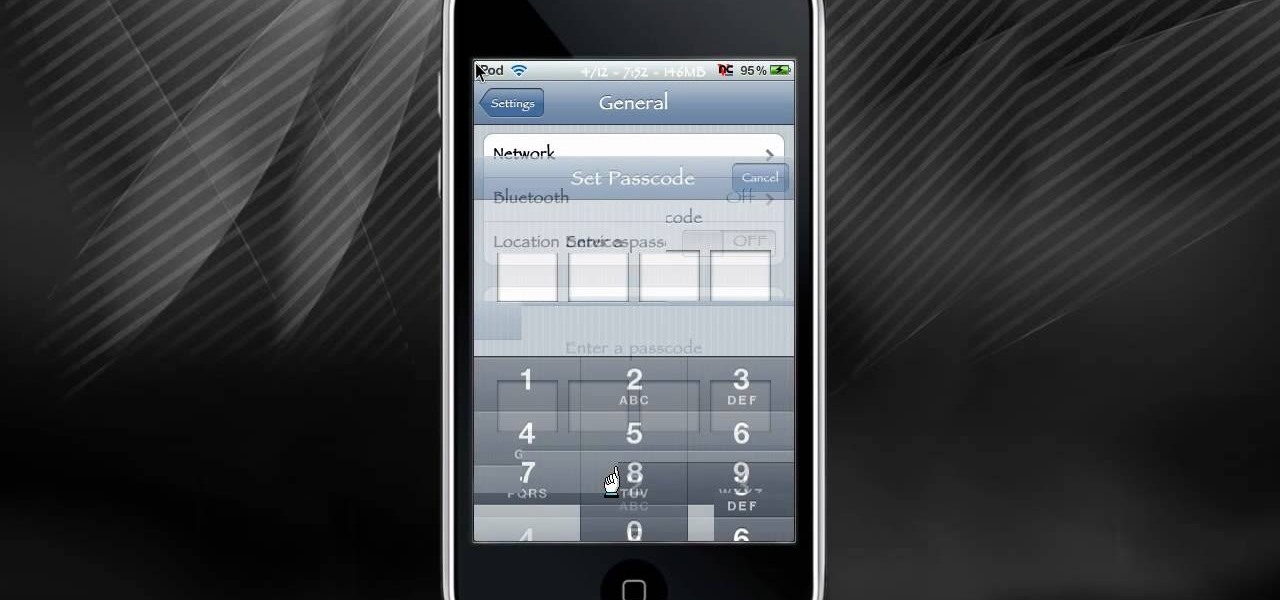
Back in the olden days, if a lock was, well, locked, you couldn't get in the door. At least, the average individual couldn't get in the door. But inventive and scheming folk (read: ye hackers of olde) devised crafty ways to pick lock keys and sometimes even created skeleton keys that opened any door or chest. This will let you unlock someones password on an ipod or iphone touch.

In this how-to from Household Hacker, we learn of a number of free proxy services that make getting around your school's Internet filter software a breeze. For all of the details, and to start accessing and using all of your favorite websites when at school, watch this video guide.

Any hacker worth her salt will need to debug from time to time. One particularly efficient way to check your code is with the RATS code checking tool. In this video, you'll learn how to use the RATS code checking tool for C/C++, PHP and Perl. For a detailed walkthrough on how to use RATS scanner to audit your source code, take a look!

The purpose of this video is to show an e-mail security flaw using telnet that allows hackers to send e-mails using anyone's e-mail address. Thankfully, many major e-mail providers have software that blocks this. My intention is to make people aware of this flaw so that other e-mail providers can protect themselves as well.

Did you know that malicious people can use scanners to read the Radio Frequency Identification (RFID) chips in your credit cards and identification documents and steal your personal information? Learn to protect your personal information from hackers and scammers with this simple method involving aluminum foil.

My message to Russian hackers is this: LEAVE BRITNEY ALONE! Russian hacking collective Turla has been targeting governments and military operations in the United States, Europe, Asia, and the Middle East for the past decade. Now, it appears that the group is targeting everyday citizens — specifically Britney Spears fans.

In recent weeks, some people have been shunned from the Null Byte community because they expressed "black hat" aspirations. This is because Null Byte is the "white hat" hacker training/playground. Although most of us think we know what that means, it does beg the question; "Who and what is a white hat hacker?"