Clean out the empty bottle that you are going to use. You can use a white dish-washing soap bottle or a cleaning agent bottle. Just make sure it is empty and clean. Use the pen to draw a wide rectangle that measures 3 inches long by 1/4 inch wide onto the bottle. The teeth you are making are going to stretch from either side of your canine teeth above and over your two front teeth. This will help them be more secure. Draw this onto a part of the bottle where it is curved. Draw two vampire tee...

See how to make a very tall, simple, yet elegant centerpiece for weddings and other events. You first need a tube and a base that it will fit into. Placing the tube in the base, use a hot glue gun to secure the tube into the base. You can then fill up the balloons with air using an air pump and tie pairs of balloons together. Twisting together four balloons, place the cluster of balloons around the base of the tube. Repeat with an additional 8 balloons and place this cluster at the top of the...

Learn how to make a sword out of cardboard with this video. Materials:

This video tutorial shows you how to install a glass vessel sink or countertop. First you need to make sure that the glass vessel sink or countertop has all of the pieces needed and that none of the pieces are scratched or broken. You then need to place the mouthing ring on the countertop where the sink is going to go. Make sure that the rubber side is facing down. Then carefully set the sink on the mouthing ring. You must then take off the tail piece of the pop up drain. Take off the ridge a...

Check out this instructional RV video that demonstrates how to fix your motorhome refrigerator. Learn what to look for when fixing your RV refrigerator along with simple steps to keep your RV out of the dealership repair bays. Here are a few simple do it yourself repairs that just might save you thousands.

Digidesign has transitioned all of their plug-in software copy protection from floppy drive based key disks to copy protection authorizations that reside on the iLok technology provide by PACE. The following is some information about iLok technology.

This instructional pet video shows a good way to introduce your pet rats to water. However, it's important to understand that some pet rats will just not like water. Your success will vary depending on your individual critter(s). Watch this tutorial video to learn the best methods of approach.

Whether you're using your phone's map to navigate or entrusting your passenger with the responsibilities of the mobile DJ, your phone needs a secure place in your car. And if it could charge while it's there, that's great too. The Naztech Smart Grip Wireless Charging Car Mount is exactly what you're looking for if you need a place to keep your phone secure, charging, and able to be used when it's safe to do so. Right now, this adjustable phone mount is on sale for $39.99, an 11% discount.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

If you haven't used a Samsung device in a few years, the Galaxy S20 series will be your first taste of One UI 2, the skin running on top of Android 10. Although One UI is on the heavier side, it has loads of exciting features that go beyond what's offered in stock Android.

As much funding as Magic Leap has secured, another round of funding will still catch headlines. However, the latest funding solidifies the company's strategy for succeeding in the consumer segment of AR.

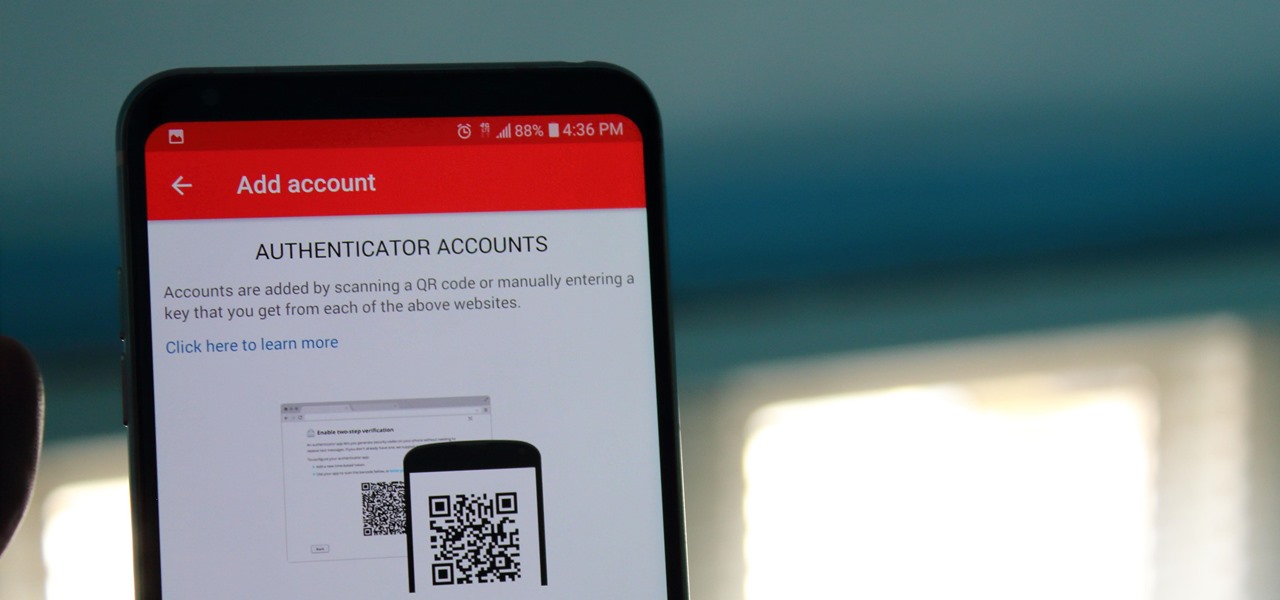
If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

RIP Touch ID. Apple's fingerprint sensor on iPhone and iPad models with Home buttons is about to become phased out on Wednesday, Sept. 12. While Touch ID will remain an integral part of models from the iPhone 5S to the iPhone 8 Plus, as well as the iPad Air 2 through the sixth generation iPad, Face ID will completely take over as the default security method for unlocking future iOS devices.

If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

Transferring hundreds of screenshots, webcam recordings, keystroke logs, and audio recordings between your VPS and a local Kali machine can be tricky. Services like Dropbox don't always have the best privacy policies and suffer data breaches just like any other website. To mitigate these risks, we'll use a secure, open source, and decentralized alternative.

We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.

Apple has introduced a special edition iPhone 8 and 8 Plus to bring attention to the ongoing worldwide battle against AIDS. As the second iPhones to carry the (PRODUCT)RED name, these rare iPhones may quickly sell out when preorders open up on Tuesday, April 10, at 5:30 a.m. (PDT), so we'll go over some tips to help you secure a red iPhone before it's gone.

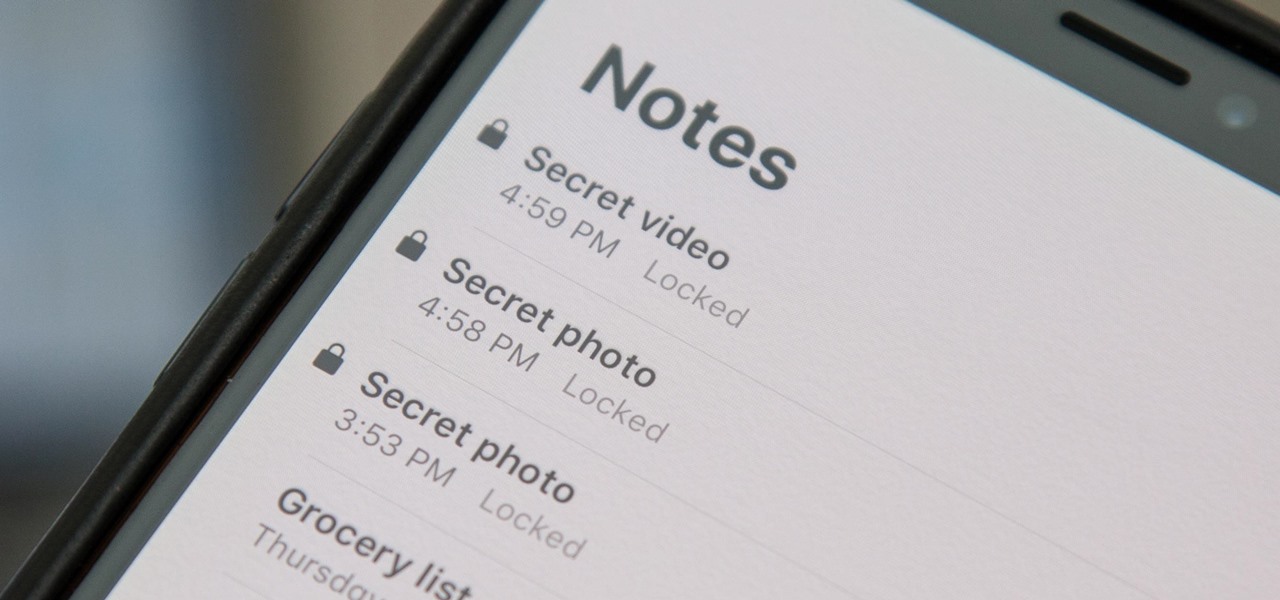
When a photo or video is just too sensitive to leave laying around in your Photos app, you'll want to either delete it for good or hide it away in safe, secure location on your iPhone. As for the latter, Apple actually has a few tools available to make photos and videos hidden — even password-protected — on your iPhone.

One unique feature of Firefox Mobile is extensions. Extensions allow users to add in features that didn't originally come with the browser. These add-ons provide an array of features, including improvement to privacy and security.

As of 2016, there are approximately 1.85 billion Android smartphones worldwide. This growing popularity has led to an increasing number hacks and cyber attacks against the OS. Unfortunately, Android users need more protection than what is offered by Google. The good thing is that there are a number of options available.

BlackBerry's focus on secure software and their new partnership with manufacturer TCL are two of the biggest factors in their recent resurgence. Last year, the company announced two new devices — the KEYone and the BlackBerry Motion. The KEYone has been available for a while, but after months of waiting, BlackBerry announced the Motion will hit US shores in a few days.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

Anyone who paid attention to the Lavabit shutdown had a feeling it was connected to Edward Snowden, the high-profile NSA whistleblower. Ever since the government's case against Lavabit went public in late-2013, people have put two and two together.

This tutorial was written with Windows 7 in mind, but the principle applies to all versions starting from 7.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

When people get accustomed to something, any type of change is typically met with resistance or disdain. So when Twitter decided to swap stars for hearts, the internet wasn't exactly receptive to the new aesthetic.

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

The internet is forever. When you put something out there, it can easily be re-shared, floating from server to server indefinitely with no way of taking it back. It's a scary thought when you consider that a young adult's grandchildren will one day have access to their drunken party pics.

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

Summer is here, and with the season comes more freedom and searing heat. It's the ultimate between-a-rock-and-a-hard-place situation. You want to be outside and enjoy the sun, but you don't want to be over-powered by it. Thankfully, you can create makeshift misters on the cheap to enjoy the summer heat right on your deck.

With all of the personal data that's stored on our smartphones, it's of vital importance that we have some sort of lock screen security enabled. One of the Galaxy S5's killer features is obviously the fingerprint scanner. It makes the process of dealing with a secure lock screen a bit easier than typing in a password or PIN.

How to build a simple planter box from reclaimed pallet wood and hardwood fence palings. Planter boxes come in all shapes and sizes and mine is a little different than most. It's taller and narrower than many of the ones you see.

Pallets, Pallets, Pallets. You have to love them! How to build an outdoor play kitchen for the kids using old pallets and recycled / reclaimed wood. I came up with the idea after seeing how my young son loved playing with the one at childcare. Pallet projects and Pallet Ideas are never far from my mind so l couldn't wait to get stuck into building my play kitchen.

How to build a sandbox / sandpit using pallet wood. Using pallet wood is a really easy way to make a sandbox / sandpit and to top things off they're free! This is another one of my reclaimed wood projects that was a heap of fun to make. Like all pallet projects, it is a good idea to use Heat Treated Pallets as they are safe for handling.

Your shiny new HTC One M8 is a pretty stellar device. From controlling your entertainment center to lock screen gestures and camera shortcuts to being pretty damn indestructible, this device has a lot going for it.

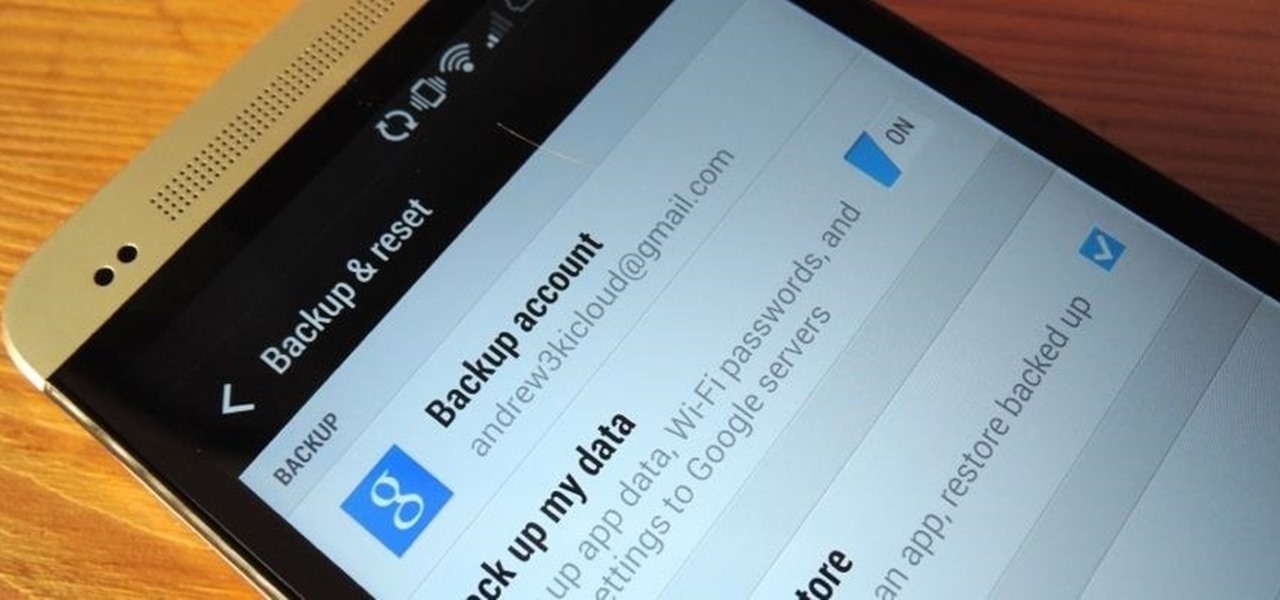
If you are using the the AT&T variant of the HTC One, you are well aware that the carrier opted not have the HTC Backup app pre-installed on the device. Luckily for us, HTC said "screw it" and put the app on Google Play, allowing anyone with an HTC One, regardless of carrier, to be able to download and use the app—if you're an AT&T customer, grab the app and let's take a quick walkthrough (again, the rest of us on other carriers should have the app already).

How to make a Lego key holder with note board. Tired of loosing your keys? Well keep them safe and in one place with this fun Lego key holder.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.