In this tutorial, we learn how to replace the air filer in our vehicle. Remember to do this every 12 to 13,000 miles you drive the vehicle. First, you will need to buy a new clean air filter that fits inside of your vehicle. Now, turn the engine to your car off and open up the hood. Next, undo the clamps around the air cleaner housing and lift the housing up. Now remove the dirty air filter and insert the new one in its place. Now, lower and secure the housing clamps again and you're all fini...

This video shows how to make a USB or adapter powered keyboard vacuum. You will need a piece of cardboard, scissors, a fan, a DC adapter, electrical tape, and a ruler. On the cardboard draw four triangles and cut them out. Tape two pieces together (not too tight because they will need to be folded); then tape all four together. Fold it pyramid style and tape the ends.

This video is a tutorial on how to repair a damaged garden hose using a coupling sleeve. Coupling sleeves are available at home improvement stores. First, you being by identifying the location of the lead in your hose. Hold it in a bucket of hot water for a few minutes to make the hose pliable. Second, use scissors to cut the hose right in half on the location of the hole. Put the sleeve clamps over both ends of the garden hose. The man says that the hardest part now is to insert the tube int...

Handyman teacher Hub Kirkpatrick gives a demonstration of how to install shutters to the exterior of one's home. These vinyl plastic shutters are meant to enhance the beauty of the exterior of a house without costing too much. Hub recommends using six 3-inch, hex-headed bolts for each shutter so that it is secured firmly in place. He also adds a cautionary note that one should take care not to over-tighten the bolts because that could result in dimpling and cracking of the plastic shutter.

Making a braid can be fast and simple. First start off with three pieces of string that are tied together at the top. Lay out the bundle of string flat so that all three pieces can be seen. Next, take the left string and move it over the center one so that the left string is the the middle string and the middle string is now on the left. After that, do the same with the right string and put that in the middle. Take the left string and put that in the center. Keep repeating these steps until y...

Having trouble with your green screen? You may not have it lit right, or it may not be secured properly, or you might not be using your editing software right when using chroma key. If you want to learn a few tips on how to fix a bad green screen, this is the place. Watch this video tutorial to learn how to improve your green screen skills.

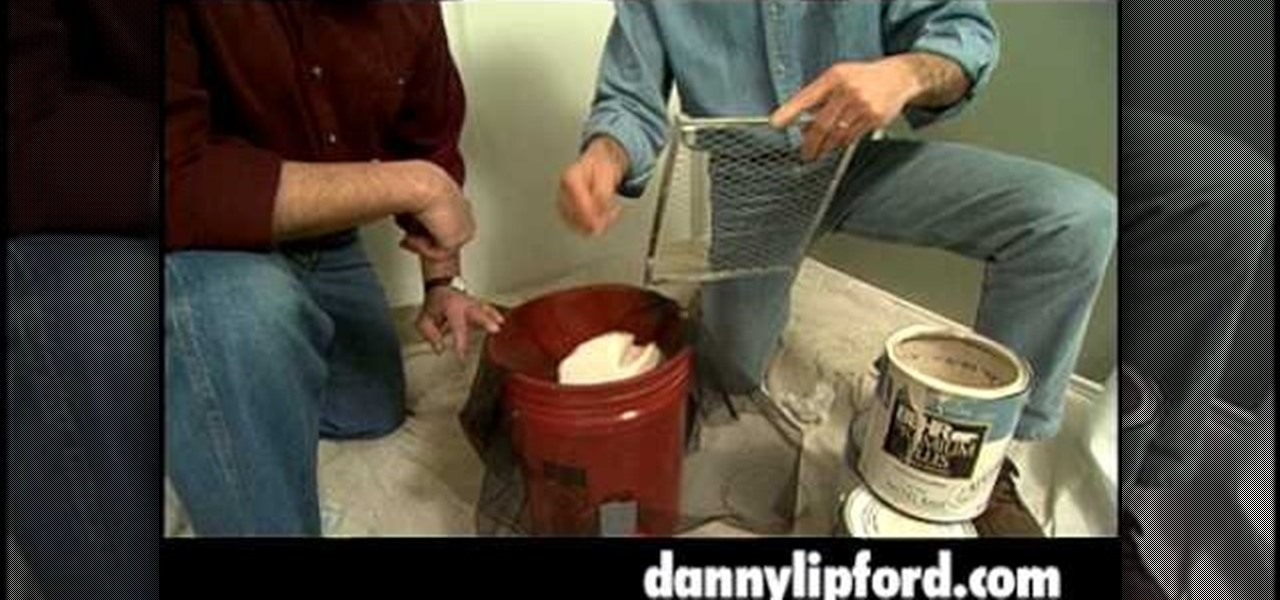
Home improvement expert Danny Lipford helps you figure out a way to mix paint thoroughly to ensure a proper paint job in your house. This video tutorial will show you just how to mix paint to ensure a well blended wall color.

Create an updo hairstyle by making a ponytail and using hair pins to secure curls to the top of the head. Tease hanging curls to make a ponytail updo hairstyle in this free how to video on haircare from an experienced hairdresser. Learn how to do your own updo!

This video conning tutorial shows how to pick a dead bolt lock. You will need a tension wrench and a lock pick, in this case, one made from a hacksaw. Watch this video demonstration and see how easy it is to break into even the most secure seeming of locks, the dead bolt.

Take off the center cap of your DIY Cube. What's under there -- screws. Why have a Rubik's Cube when you can build your own DIY Cube?

This easily installed universal towing mirror will mount to any mirror with its conforming rubber knobs and securing clamps this mirror will attach easily to any mirror you have on your vehicle. This video shows you how.

In this tutorial, we learn how to build a PVC greenhouse. The dimensions of this will be 12' x 18'. First, you will use 1/2" PVC pipe that is 12' long that crosses in the middle to make a "t" shape. The frame can be made of treated 2'x 4's. Once you have the frame up, you can use thick plastic to securely cover the pipe and wood and clamp it into place. Once you have this done, you can place your tables inside of the greenhouse and start growing your plants! If you notice the plastic not hold...

In this tutorial, we learn how to get rid of wasps and hornets without using chemicals. Take a piece of bacon and wrap it around a stick. Then secure that stick by hanging it over a bowl of water with dish soap on it. The bacon will entice the bees to come towards it. Then, the bees will eat so much bacon they will have a hard time flying and they will end up flying down into the bowl of water. Then, the soap will make them be able not to fly and they will drown in the water. This is very eff...

There are two basic ways to twist hair so that it lies on the scalp. One way to twist the hair is to section the hair into the desired size of segments. Use one hand to twist the hair with the thumb and forefinger while holding the hair down secure with the other hand. Another way to twist hair is to separate the section into two pieces. Twist one section over the other and pick up another piece while twisting the strand around again. This will feel similar to braiding, but with only two stra...

Happy140 demonstrates how to fold and wear a bandana. Folding a bandana and placing it securely onto your head for everyday use is easy using a few simple steps. The first step is to take the bandana and fold it into a triangle so that all the points touch each other and are even. Then, fold the top point down so the bandana forms a trapezoid shape. The next step is to fold the bandana in half lengthwise. Wrap the bandana around your forehead. Tie the ends of the bandana into a knot behind yo...

This video is a tutorial explaining how to erect a tipi shelter. You must make sure all poles are 11' by 10' to have the correct height tipi. The instructor then aligns three marks and ties a clove hitch around all three poles. The next step is to raise the pole by using the rope to keep the structure stable. The next step involves putting the covering onto the lead pole and the bring the covering around 360 to complete. The last step involves securing the covering with rope by tying a knot a...

Grab your long-handled wooden spoon and let's get to bed making. There is a science in making the immaculate and consistent military-style bed. Use this method at home and know that your making your bed just like soldiers do every day.

Find the indication light, located at the top of the Whirlpool refrigerator just inside the door. This tells you when to change your water filter. A green light indicates the filter is good and a red light indicates you need to change the filter.

Make sure your electronics gear stays in order! And make sure your running wires are safe. Check out this video tutorial from the Good Idea Guys at Good Buy Guys to learn how to tape down a cable correctly. Keep those microphone cables, audio cables, and extension cords secure and safely underfoot. Tape Tex shows you how in "How to Tape Down a Cable". A great helpful tip for cable safety.

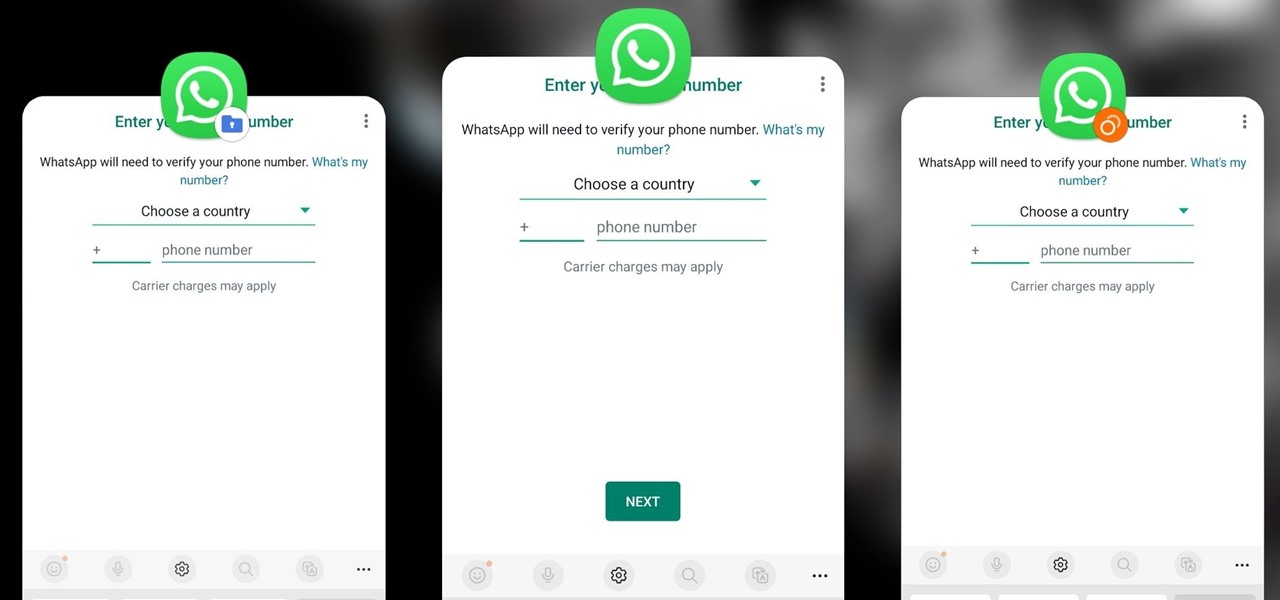
Samsung has a cool security feature built into One UI that has an interesting side effect, one that lets you have two separate copies of any Android app on your Galaxy phone. And that's not the only integrated Samsung tool for cloning apps.

With protests springing up across America, there's a chance you may have your first interaction with law enforcement. Many demonstrators will have their phones in-hand to film the action, which, sadly, could prompt an officer to demand the device and any self-incriminating data it may contain. Before this happens, you should know there are tools at your disposal to protect your data in such situations.

When Apple acquired the popular Workflow app in 2017, many were worried that it would either get replaced with something much worse, or just disappear entirely. Thankfully, Apple put these concerns to rest with the launch of Shortcuts. In iOS 13, Shortcuts is becoming more powerful than ever, providing functionality on the iPhone that the original Workflow team could only dream of.

It's always a big deal when the company that makes Android releases a new phone. Google's Pixel series has made a name for itself in three short years behind its camera prowess, but now it's time to start competing with the major players. That said, Google should like how their Pixel 4 and 4 XL stack up against the iPhones and Galaxies of the world.

In recent years, unwanted calls have become a top priority for the FCC. In 2016, analysts estimated that US customers received over 2.4 billion robocalls per month. As a result, the FCC has provided carriers new tools to combat this problem.

Many of our online accounts now come with an added two-factor authentication (2FA) functionality to help keep our data safe. This essentially means no one would be able to access the account until a specific set of requirements were met. It could be a combination of a password with a security key or even a passcode with some form of biometrics, like a fingerprint or face scan.

Whether we like it or not, our personal information and smartphones are tied together at the hip. The former needs the latter to deliver a personalized experience that matches our individual needs. This personal data, however, makes your phone a prime target for thieves of all sorts to turn your privacy into illicit profit.

It's common for IoT devices like Wi-Fi security cameras to host a website for controlling or configuring the camera that uses HTTP instead of the more secure HTTPS. This means anyone with the network password can see traffic to and from the camera, allowing a hacker to intercept security camera footage if anyone is watching the camera's HTTP viewing page.

Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for exploitation, and you'll soon learn how an attacker can exploit a SAML vulnerability to assume another user's identity.

The conversation of which operating system is most secure, macOS vs. Windows, is an ongoing debate. Most will say macOS is more secure, but I'd like to weigh in by showing how to backdoor a MacBook in less than two minutes and maintain a persistent shell using tools already built into macOS.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

Now that it's been officially released for Android, Monument Valley 2 shot to the top of our best paid puzzle games list, and rightly so. This was no easy feat, as the games we covered ran the gamut of puzzles and all had stellar reviews. But there's just something about Monument Valley 2 that made it stand out from the rest.

"I'm Rey." That's what a lot of people will be saying again this Halloween, as Rey costumes are sure to be another favorite of trick-or-treaters and cosplayers. Yes, on Oct. 31 we all have a chance to be the scavenger of Jakku who just so happens to be the "new hope" for a Jedi renaissance.

In October of 2017, Mathy Vanhoef released "Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2." This paper demonstrates a way to decrypt traffic on practically any WPA2 network, the most commonly used form of wireless security (seeing as all other forms of Wi-Fi encryption have already been broken). Practically all of the network-connected devices we use will need to be updated in some way in order to protect against this vulnerability, each of them in a different way.

Virtual private networks, or VPNs, are popular for helping you stay anonymous online by changing your IP address, encrypting traffic, and hiding your location. However, common IoT devices, media players, and smart TVs are hard to connect to a VPN, but we have a solution: Turn a Raspberry Pi into a router running through PIA VPN, which will ensure every connected device gets the VPN treatment.

The new iPhone X will be released on Friday, Nov. 3, in Apple Stores located in over 55 countries and territories. For those of you who would rather skip the in-stores lines that will start building well before the 8 a.m. local time openings, you can preorder the iPhone X on Friday, Oct. 27, starting at 12:01 a.m. PDT.

Clumsiness is the great equalizer when it comes to smartphones — it makes no distinction between the most expensive flagship handset and cheaper mid-range models. A hard drop onto pavement will usually result in a shattered screen, regardless of how pricey your device is. And with a smartphone breaking every two seconds, we're truly our own handset's ultimate nemesis.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

Buying a smartphone used is an excellent way to save money, but those savings come with a risk that your seller isn't as forthcoming as they claim. You don't want to end up buying a stolen smartphone because it might not work correctly ... and, you know, it's wrong. Luckily, there's an easy way to check if the phone you're about to buy is legit.