Thanks to Apple's implementation of Continuity on Mac OS X Yosemite and iOS 8, communication is truly a seamless thing. Without even looking at my iPhone, I can message or call friends comfortably from my computer or iPad.

Apple's new iPhone 6 and iPhone 6 Plus go on sale Sept. 19th, but pre-orders begin on Sept. 12th. If you're ready to trade in your iPhone 5 for one of these bigger and more iOS 8-friendly devices, you're probably going to pre-order.

Over the weekend—just days before Apple's big event—an actual iPhone 6 leaked on Chinese site cnBeta. Again, nothing here that we already didn't know about—Sapphire screen, round(er) corners, larger display, and new button stylings. Below are images of the new iPhone 6 next to the current iPhone 5S. We can clearly see the protruding camera module as well as sections on the top and bottom of the back where the antennas will be housed. A second source was able to put together some videos, as yo...

Replacing your wallpaper is one of the easiest and quickest things you can do to keep your device from going stale, but it goes way beyond just picking an image from your gallery. If you use the Google Camera, you can create some really awesome 3D lens blur backgrounds, but what if you want more wallpapers on your wallpaper?

It looks like Snapchat, it feels like Snapchat, but after using it for a few minutes, you realize there is a huge difference between Facebook's new Slingshot app and the Snapchat we've all grown so accustomed to.

E3, or the Electronic Entertainment Expo, is the 20th annual trade show for video games and gaming tech. The event takes place on Tuesday, June 10th at the Los Angeles Convention Center, and you can watch a live stream of the event on Twitch.

Watch out Samsung (and you too, Pebble, Sony and the still unrealized Apple), your hold on the smartwatch market is about to get a lot less firm. Announced today, Google has released Android Wear, their platform for developing smartwatches, along with a preview of the Moto 360 smartwatch from Motorola.

Most of us have traded our desktop systems for laptops, tablets, and mobile devices, meaning there's a lot of outdated hardware sitting in attics. Want to give your old computer a new purpose? Matthew Chappee turned his iMac G4 into an HDTV using the guide by Dremel Junkie. One thing to note before you take on this project yourself is that if you want to use it to watch cable, you'll need a converter box to get around the MPAA's HDCP restriction. But, a converter box is considerably less expe...

Sea otters are the largest members of the weasel family. When people started hunting sea otters for their fur, their population fell from roughly 225,000 to about 1,500, until the International Fur Seal Treaty took effect in 1911. Since the international ban on otter hunting, the population has rebounded back to roughly 107,000.

If you bought the new iPhone 5, you've probably been less than thrilled with the lack of cases and accessories that you can use it with. Docks are no exception—users were disappointed to learn that Apple has no plans to even make one for the newest addition to the Apple family.

Keeping your supplies of caps and ammunition high in Fallout 3 is one of the game's biggest challenges. No more! This video will teach you how to use a glitch in the game's shopkeeping interface to attain unlimited caps, ammunition, and free item repairs. You should have no trouble beating this epic game after following these instructions.

Open up Cheat Engine and be prepared to hack Restaurant City! This is a new level hack that will help you gain levels fast.

Want to be the John (or Jane) D. Rockefeller of Restaurant City? Watch this video tutorial to learn how to hack Restaurant City with Cheat Engine 5.5 (02/04/10).

Here is a quick video that shows how to make a y-seam. Follow this step by step process to sew a y-seams on your hard labored quilts. Quilting becomes easy when you can borrow a few tricks of the trade.

Eve reveals the tricks of the trade and shows how to hide that double chin and manage a blotchy face.

Navigating a pandemic is new for everybody, which makes staying on top of your finances more important than ever. Fortunately, financial freedom is possible when you focus on budgeting and investing wisely.

This week, the beginning of an epic legal battle was set to begin between augmented reality players Magic Leap and Nreal, the small China-based startup accused by the former of stealing trade secrets.

It's that time of year again. No, not Thanksgiving. Black Friday. There are a lot deals available this holiday weekend, many of which include flagship Android devices. Whether you are thinking of buying a phone for yourself or looking for a gift for someone else, you can find a little savings to shop smart during the holidays.

The world finally received its first official look at the iPhone XR, XS, and XS Max, Apple's 2018 suite of smartphones, on Wednesday, Sept. 12. If you're someone looking to get their hands on one, two, or three of these new iPhones as soon as possible, you'll need to know all of the important dates so you don't end up missing out to others ahead of the line.

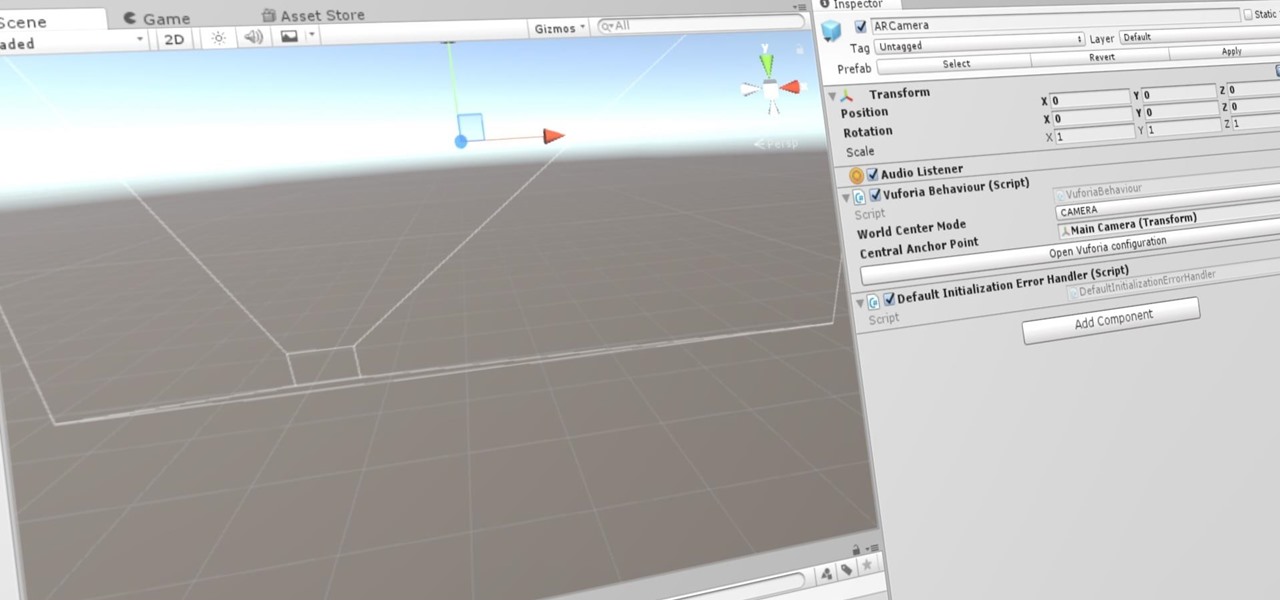
Now that we've set up Vuforia in Unity, we can work on the more exciting aspects of making physical objects come to life on the HoloLens. In this guide, we will choose an image (something that you physically have in your home), build our ImageTarget database, and then set up our Unity camera to be able to recognize the chosen image so that it can overlay the 3D holographic effect on top of it.

Ah, springtime. When the flowers bloom, the birds chirp, and a young coed's thoughts turn to steamy hook ups. Watch this video to learn how to hook up on spring break.

Next time you organize a cookout, throw a few spuds on the grill, too. Watch this video to learn how to make grilled potatoes.

How to know how pawn shops work and how to take advantage of them; get expert tips an advice on how to buy, sell, trade, and save money in pawn shops in this free instructional video.

If you want to finally pick a winning horse at the racetracks, then watch this video tutorial to learn the tricks of the horse racing tipster's trade. This is an easy tip to improve you horse racing odds. Betting on horses is easy, but winning is the hard part.

Are you trying to construct your dream house with your own two hands? Learn the tricks of the trade and watch this video tutorial on how to tie a string line.

So you can't seem to win in Mario Kart Tour? Whether it's your first game in the Mario Kart series or not, Mario Kart Tour can be challenging, especially when you don't know the tracks. Instead of struggling your way through the cups, try out these five tips to get a leg up.

The enterprise sector is where the money is for augmented reality at the moment, and remote assistance apps are the go-to app for many enterprise customers. We took a look at the leading apps and platforms from this category, from the top contenders to the underdogs with unique features.

Things that are supposed to make life easier for developers and users are often easy targets for exploitation by hackers. Like many situations in the tech world, there is usually a trade-off between convenience and security. One such trade-off is found in a system known as Distributed Ruby, which can be compromised easily with Metasploit.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

The ongoing war between Apple and Samsung fans will rage on once again. With the release of the iPhone XS Max, Apple has presented a stronger adversary for the Samsung Galaxy Note 9, released earlier. Both stack up well against each other, providing two of the best experiences on their respective operating systems.

It wasn't Christmas, but for Amazon Prime members, it was darn close: Amazon Prime Day, one of the biggest shopping days of the year, came and went earlier this week. Unfortunately, there weren't many Prime Day-specific deals to be had for augmented reality fans, but that doesn't mean AR-loving Amazon Prime members were completely left out.

The new Samsung Galaxy S8 and S8+ are two of most head-turning phones we've ever seen, thanks to gorgeous build quality and a seemingly bezel-less Infinity Display. Combine that with flagship-grade internals for top notch performance, and you can almost guarantee that Samsung has a hit on its hands—which means it's probably not going to be easy to get your hands on one of these beauties.

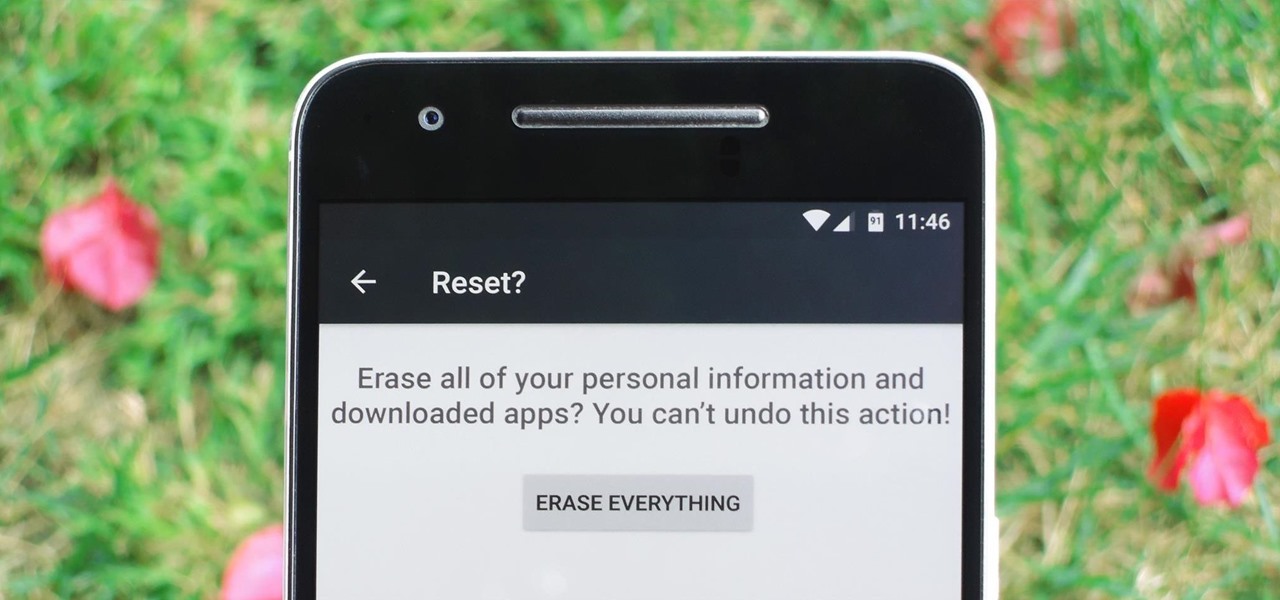
Whether you're performing a factory reset to get your device ready for sale or trade-in, or you're wiping your device in the hopes of fixing software issues, there's a right way and a wrong way to go about it. Sure, it seems like a simple task on the surface, but if you're not careful, you could end up wasting a lot of time or losing precious data.

Apple has changed how home screen shortcuts work on iOS, which makes one of the most enjoyable customization features even better than before.

Communication is an essential skill for successfully launching products. Whether you're developing the latest and greatest app or trying to get ahead of a large data science project, effective communicators are always in high demand.

A little over a year after emerging from stealth, augmented reality gaming startup Illumix has launched its first title using a familiar formula, but with a new twist.

After entering into settlement talks with Epic Games over the gaming giant's trademark challenge, Nreal is now ready to open up the floodgates to potential early adopters in the augmented reality space.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

A company whose sole product line is smartphones might be worried about early proclamations that the smartphone is dead with the advent of augmented reality wearables.

Your Google history is mostly a binary choice — either you enable it fully, taking advantage of all its features while letting Google record your activity, or you disable it, staying incognito but also missing out on some fun stuff. But now, Google will let you auto-delete your history, allowing you to utilize all the perks that come with recording your history while maintaining some level of privacy.