
How To: Play multiphonics on the sousaphone
This is a short film recorded to discuss how to do the multiphonics on a sousaphone. For more information on the circular breathing search for didgeridoo movies


This is a short film recorded to discuss how to do the multiphonics on a sousaphone. For more information on the circular breathing search for didgeridoo movies

This is the first of what will surely be a long and detailed series on operating the F-15 Eagle in the simulator Lock-On: Flaming Cliffs. This first one introduces you to the Eagle's radar with off and Range-While-Search modes and their symbology.

This video shows different ways to save music from websites including using Google search and recording songs from websites using free software.

In this video you will see how to access network security cameras through google search engine easily!

This iPhoto '08 tutorial shows you how to add titles, descriptions, keywords for searching and ratings to your photos. This helps with finding and organizing your photos.

Learning songs is the best way for a beginner guitarist to progress. Save learning scales and technical stuff for a little later. Besides this video, Justin gives some good recommendations for where to find songs and suggests staying away from the random "TAB" internet search since this won't help you learn if you're playing them wrong or not.

In this video we'll take a look at how to create your search criteria once and use it over and over again with dynamic Collections. The Bridge is about to get a whole lot smarter in helping you find exactly what you're looking for. Check out this Terry White's video now!
This is a Computers & Programming video tutorial where you will learn how to change your NAT to OPEN with a Linksys router. Go to your browser and type in 192. 168. 1. 1 and that will take you to the basic set up. The authentication dialog box comes up. Type in ‘admin’ for the username as well as the password. These are default settings. In the Linksys page, go to ‘applications and gaming’ and on the Port Range page fed in these information. Your application you can name anything. Start 80, E...
This video demonstrates how easy it is to take a screenshot with shortcuts in Mac OS X. Pressing Command-Shift-3 will take a screenshot of the entire screen, while Command-Shift-4 will let you take a screenshot of just a selected area of the screen instead. For the latter, once you use the shortcut, your mouse pointer will turn into crosshairs, and you would click on one point of the screen, then drag and release your mouse to take a capture of the selected area.

Download .net framework and install it if you do not already have it. Download DevKitPro from here and install as instructed.
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to install KDE 4.3 Plasma on [k] Ubuntu Linux.

This video will show you how to record video on your Apple iPhone 3G for free! This is a complete guide to installing the iPhone Video Recorder on your iPhone 3G, which also works on the First Generation iPhone.

If you need to know how to make an arrangement on an acoustic solo fingerstyle guitar, you've come to the right video tutorials. This three-part instructional guitar lesson will show you want you need to know about arranging.

This software tutorial shows you how you can blend three differently exposed images using Photomatix, and then demonstrate how to use some basic Photoshop techniques to touch-up the resulting image. [Note: the Flash overlay in this video doesn't sync completely with the audio; pausing for a second and then resuming it fixes the problem.]

To hack into Google images follow the following steps. You will first need to open a new internet browser window and go to Google, then load their images website. Next type into the search bar your image query and press search. Once you have gotten your search results paste the following code into your address bar:
Researching genealogy takes a little enterprise and the skills of a master sleuth.. Watch this video to learn how to research your genealogy and family tree.
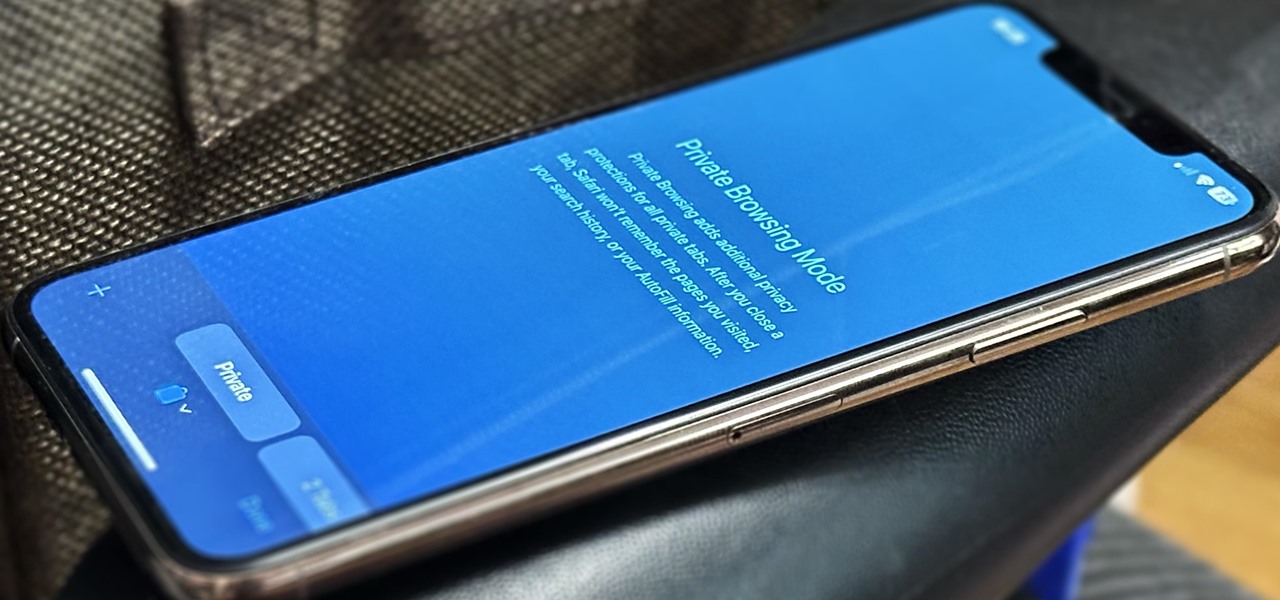
Private Browsing mode finally lives up to its name in Apple's huge Safari 17 update for iPhone, iPad, and Mac. So whether you search for things you don't want anybody to know about or want to ensure websites and trackers aren't eavesdropping on your activity, you'll want to update your devices pronto.

AirPods are not only a great way to listen to music on your iPhone, but you can also use them as a headset for phone calls, videoconference, Siri, voice memos, audio messages, and more. While each 'Pod has a built-in microphone, they aren't used simultaneously, and your AirPods will automatically choose which to use. If you want to only use the mic from one 'Pod or the other, there's a way to do that.

To share a song or album to family and friends, it's as easy as copying its link in the app and pasting that into a message. However, not everyone uses the same music streaming service, so a link to an Apple Music song won't do a Spotify, Tidal, Pandora, Deezer, or YouTube Music subscriber any good. If you're on an iPhone, though, there's an easy way to convert links from one service to another.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.
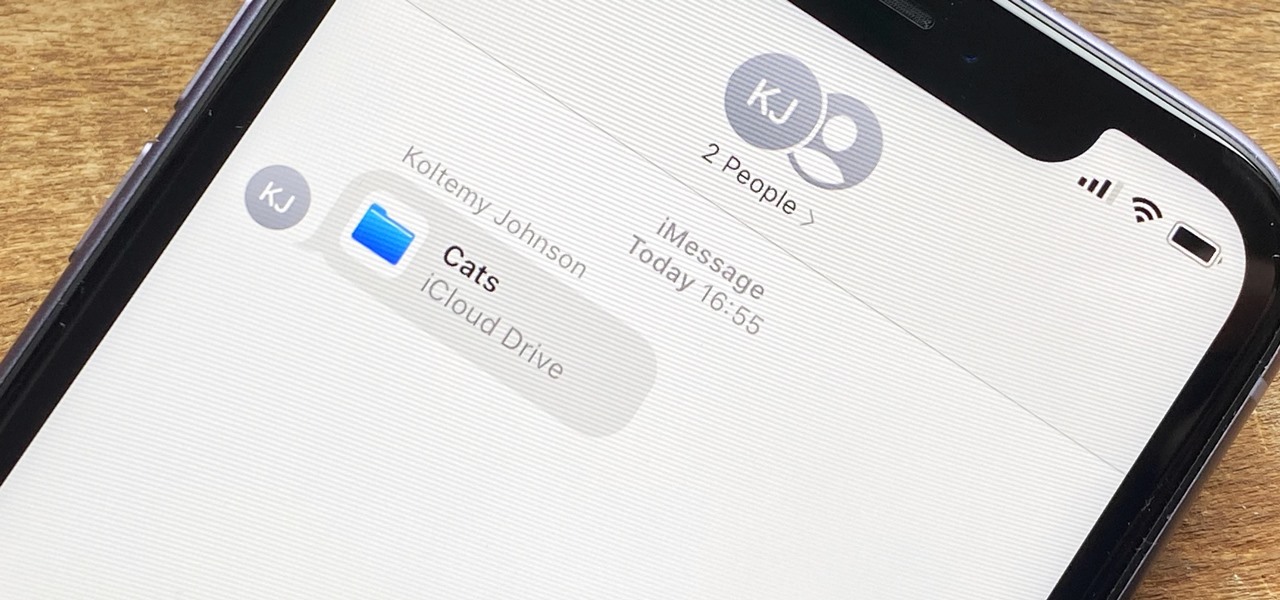
In the iOS 13.4 update, Apple added folder-sharing capabilities in the Files app. That means you can share multiple documents at the same time instead of doing it one by one. But that's not all — you can share folders with numerous contacts and even enforce access and permission settings.
With every new Galaxy flagship release comes the age-old dilemma: do I choose great hardware or great software? For years, Samsung has given users the best components available on any smartphone. The problem is the software is an acquired taste. But there is something you can do about it.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.
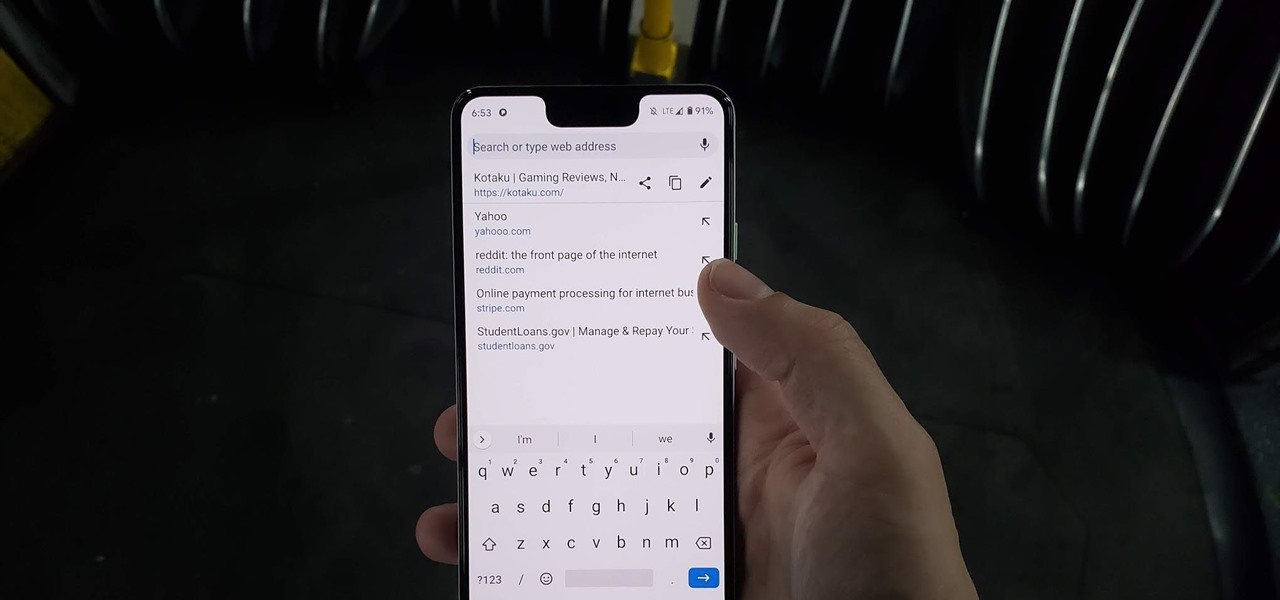
Chrome has just introduced some new UI elements for web exploration. The new URL bar is not intuitive. But once you get to grips with it, you will be so much more efficient in your address bar editing, pasting, and navigation.

Normally, when you scroll down a webpage in Safari on your iPhone, it automatically hides the bottom toolbar and minimizes the top Smart Search field. But as soon as you scroll back up, they both reappear, which can be pretty annoying if you don't need them. Apple's iOS 13 update brings many new features to Safari, one of which solves the toolbar issue so you can keep it hidden when reading.
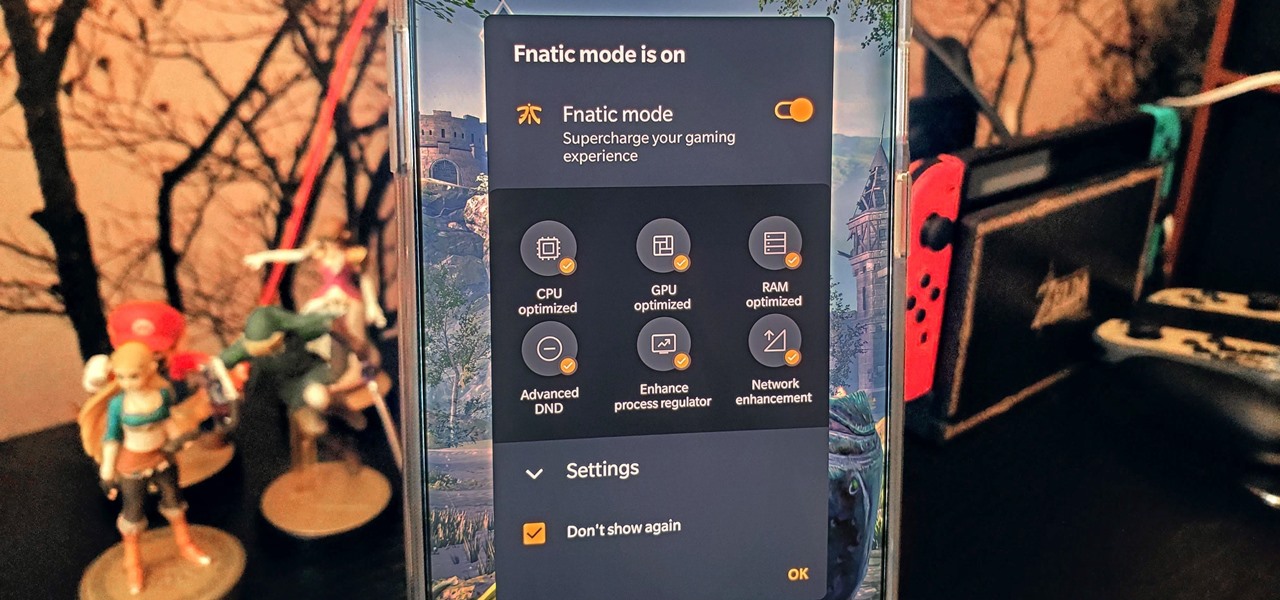
The OnePlus 7 Pro is an outright beast. From the highly rated display with minimal bezels to the 90 Hz refresh rate, there's no denying this phone is great for gaming. Although not explicitly marketed as a gaming phone, it seems OnePlus unintentionally created one by cramming in great specs and game-friendly software features like Fnatic Mode.
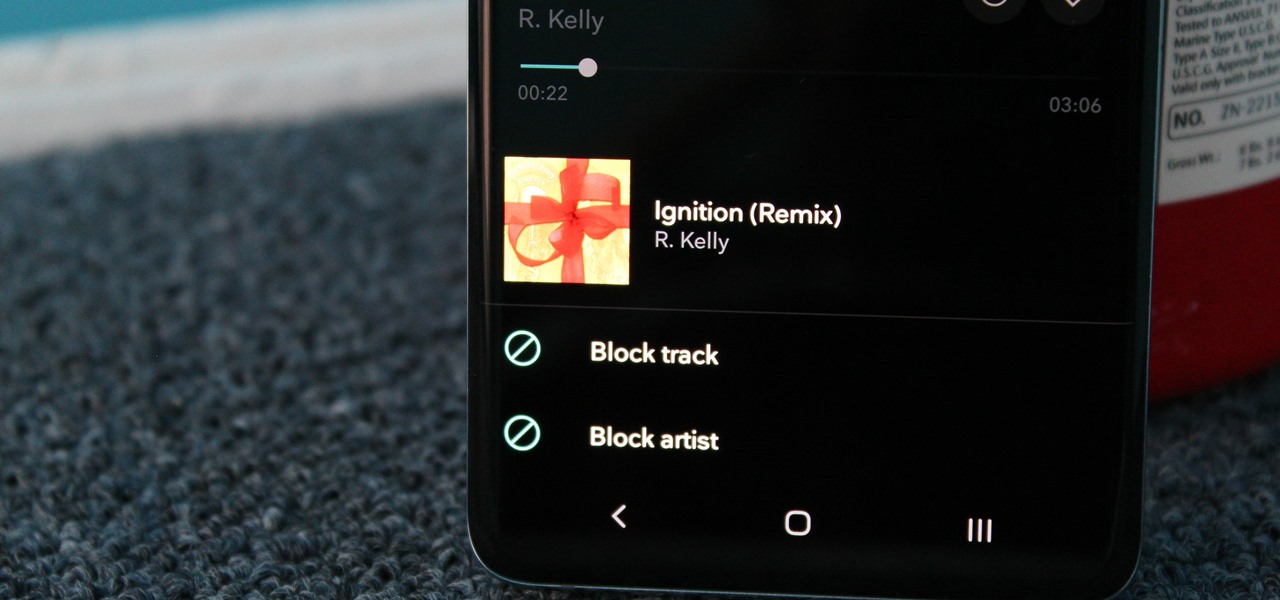
From XXXTentacion to R. Kelly, many artists have been accused of inappropriate actions, so some of us just don't want to hear their music anymore. However, each time streaming services attempt to ban such artists, they face heavy backlash. Recognizing this, Tidal decided to offer a different solution.
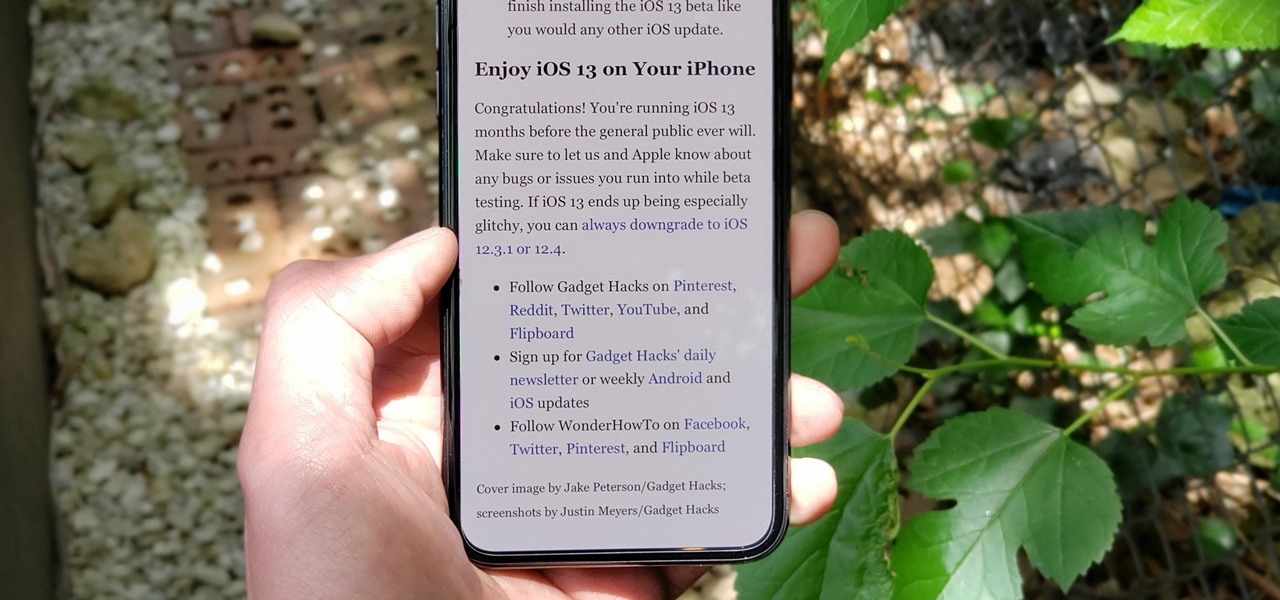
The Reader mode in Safari is a great way to view a webpage on your iPhone in a stripped-down manner, removing unnecessary images, videos, and advertisements for a streamlined experience free of distractions. Apple's iOS 13 improves upon Safari Reader when it comes to choosing which sites you want it to run automatically on, so everything is more accessible with more controls to work with.

While the Smart Invert feature was an excellent first step toward a dark mode, it's nowhere near what a true dark mode should be for iPhone. After years of rumors and disappointment, Apple finally has the dark mode everyone's been wanting, and it's one of the most significant new features in iOS 13.

YouTube has a couple of basic gestures: you can double tap each half of the video to skip forward or back ten seconds, and you can swipe down to minimize the video. But wouldn't it be more useful if there were gestures to control brightness and volume? Well, as with all things Android, where there's a will, there's a way.
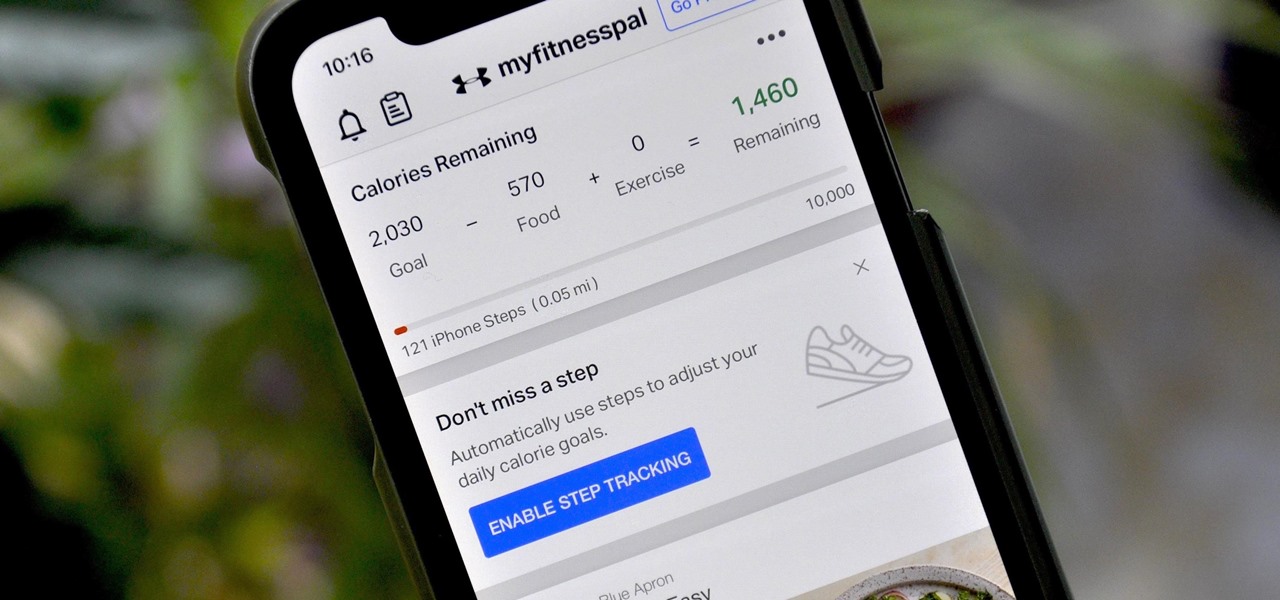
If you're new to MyFitnessPal, it might seem daunting. The app is way more than just a calorie counter, but that's because getting fit is just as much about changing your lifestyle as it is about watching what you eat. So don't let it overwhelm you — there are just a handful of tips you should know to hit the ground running.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

One of the things that sets a seasoned hacker apart from the script kiddies is the ability to effectively sneak past antivirus defenses when executing an attack. One way to do this is to use custom shellcode in an exploit. Not everyone is an expert at writing shellcode, but luckily there's an easy way to do this that is both quick and effective.

You don't need an obsessive ex stalking you to benefit from the ability to record calls on your iPhone in a pinch. Besides protecting yourself from nefarious intent, recording important conversations like verbal contracts and agreements can help you cover all your bases and ensure you're insulated from any potential liabilities that may appear down the road.
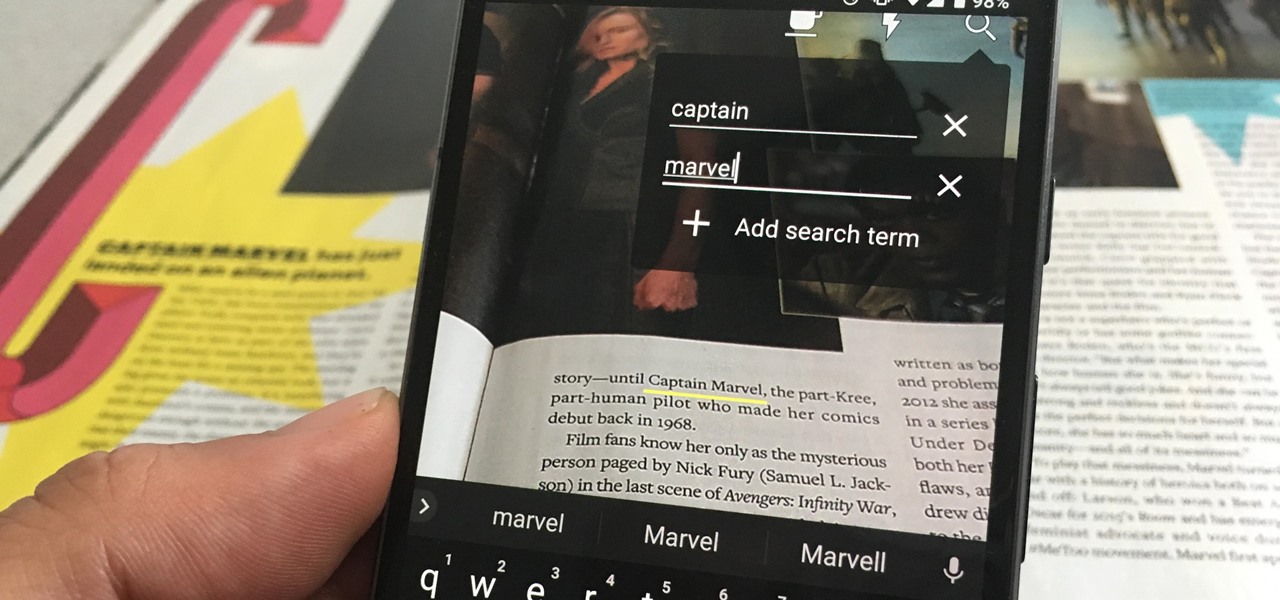
One of the neatest tricks available in Google Lens, an app that can identify and interpret real world information, is the ability to copy text from the app's camera view and paste it into a digital document.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.
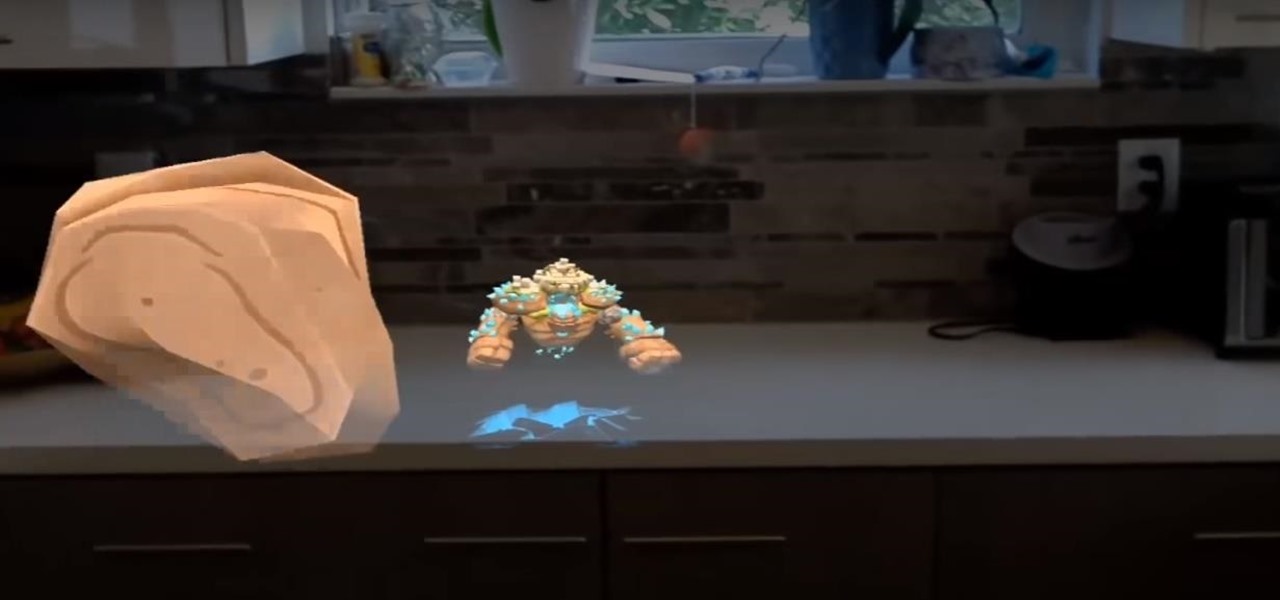
As it prepares to ship its first product by the end of the summer, Magic Leap has managed to impress yet another high-profile investor in telecommunications giant AT&T.

Apple's linear Notification Center has been scattershot at best since iOS 9 when we could group notifications by app. Without any type of grouping ability, the notification history becomes more of a nuisance of random alerts based on time alone, making it a treasure hunt to find the notification wanted. Now, iOS 12 has addressed this issue, bringing back groupings — with improvements.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.
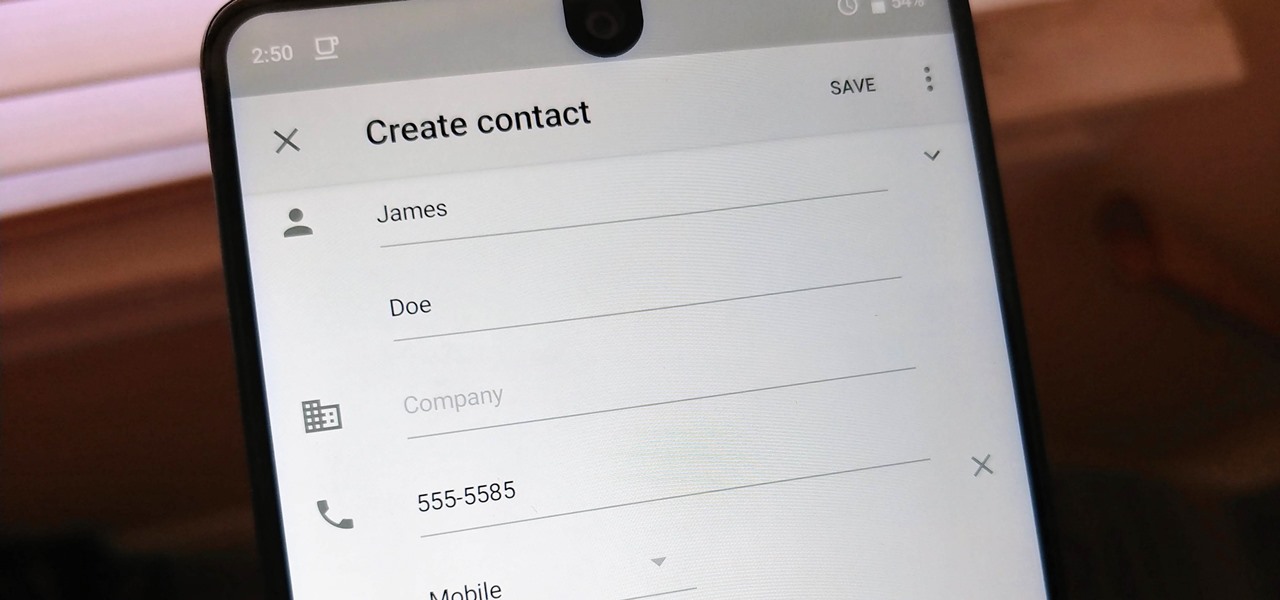
Android lets you sync your contacts across devices. The OS will use not only contacts saved on your phone, but also your Gmail. This choice can lead to a contacts list populated with entries that don't have a phone number, which can quickly add up. To mitigate this problem, there are a few methods.