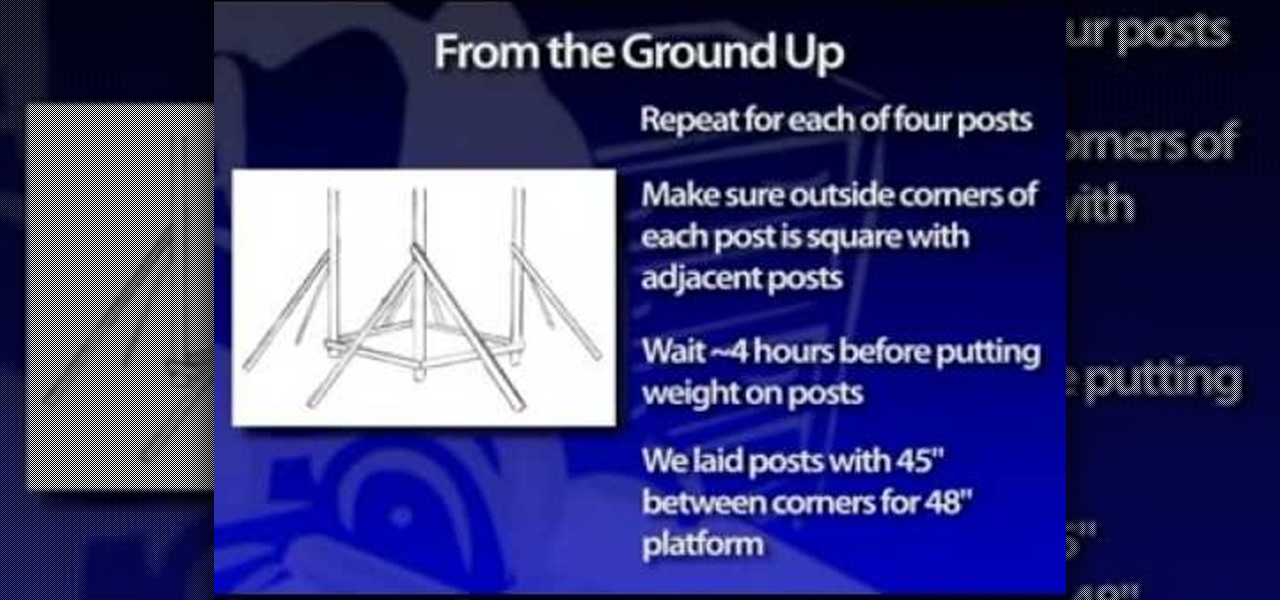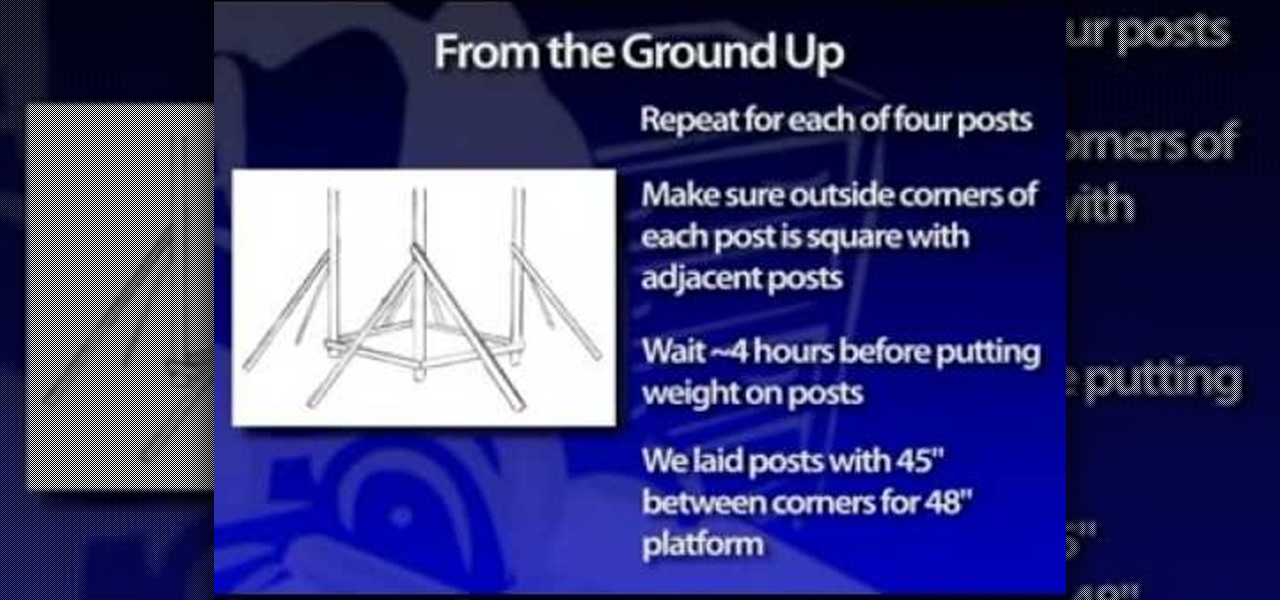
In this video tutorial, you'll find instructions for building a standard joist design playground slide, supported by 3-by-4 posts and secured with galvanized fasteners. All fasteners exposed to the outdoors must be weather-resistant, galvanized, zinc-coated brass or stainless steel. Standard homeowner tools are all you'll need to complete your slide—a tape measure, post-hole digger, circular saw, sawhorses and a level. A good drill/driver is a great tool if using decking screws as fasteners. ...

Keep your RV Entrance Steps in tip top condition with this instructional RV video. This tutorial demonstrates how to maintain and repair your recreational vehicle entrance steps. Most RVs have electric steps, which are fairly maintenance free. The biggest component is lubrication. Make sure to lubricate once every thirty days using a lithium-based grease and spray every point. Learn how to inspect the wires underneath your RV and make sure everything is secure. Just follow the simple steps in...

One important part of jewelery making involves properly attaching clasps. This how-to video jewelry making tutorial demonstrates the proper way to attach them. Begin by threading the crimp bead and the clasp onto the bead wire. Using chain nose pliers feed the thread around and loop it back around through the crimp bead. Use the pliers to hold the crimp bead tight. Crimp the bead down securing the wire and clasp.
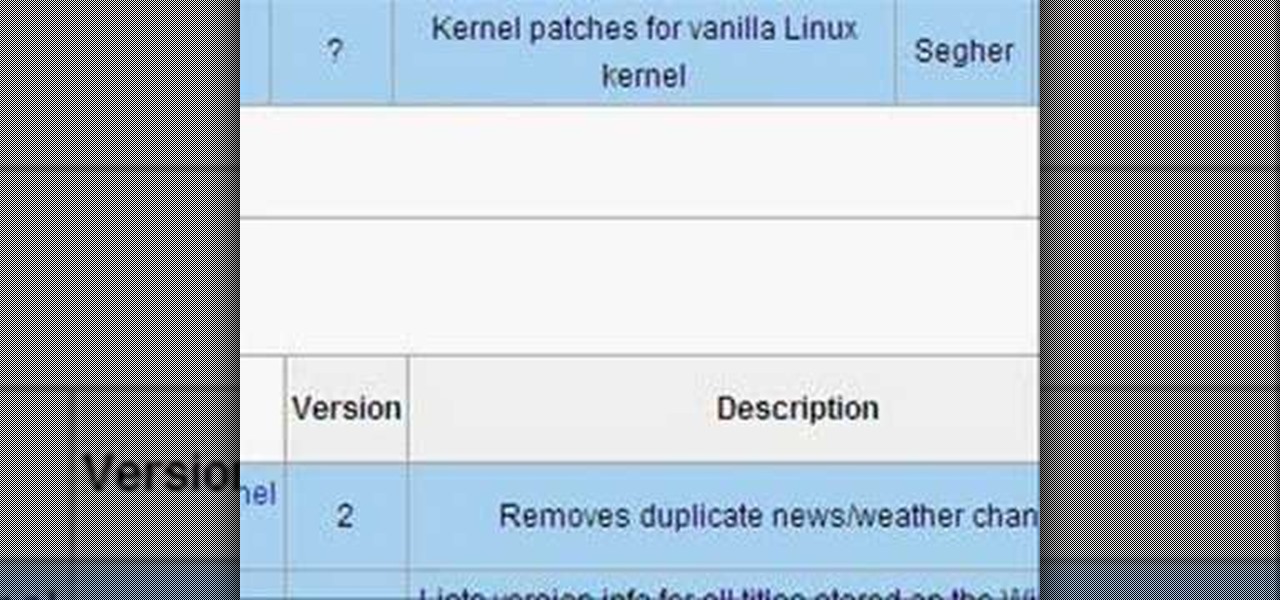
Take a look at this instructional video and learn how to load virtual console games onto your Nintendo Wii. You'll need the Twilight Hack and an SD card for this process. The Twilight hack allows you to run unofficial software through the SD (Secure Digital) card inserted into your Wii. Since the Twilight hack was found through the lastest Zelda game Twilight Princess, the game needs to be loaded every time before you can run any "homebrew" software.

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

Taking one-handed pictures with your phone can quickly devolve into a juggling act. You have to secure the phone in landscape mode (if you're doing it right), tap to focus, and then somehow hit the shutter button without shaking the device too much. Fortunately, Samsung has a nifty feature that'll help you keep a more secure grip on your Galaxy S9 or S9+ as you take photos with one hand.

Nauto, which develops driver-monitor cameras and algorithms for autonomous vehicles, is among a growing list of driverless startups able to attract tens of millions of dollars in funding after raising $159 million in its latest round of financing.

bObsweep Standard and Pethair both come with their lithium-ion battery installed for you. But if you ever need to remove and replace the battery on either model, follow the walk through below.

The original implementation of Android's face unlock feature was a mess. It took too long to unlock (when it worked), brought up a huge interface that overpowered the lock screen, and maybe most egregiously, was able to be "hacked" by someone holding up a picture of your mug.

Android 5.0 has a killer new feature that should make securing your device easier than ever. It's called Smart Lock, and it essentially lets you bypass your secure lock screen when you're in a "trusted environment." This means that if you're connected to a known Bluetooth device or near a pre-programmed NFC card, you don't have to bother entering your pattern, PIN, or password.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

Buns make the look of a woman highly fashionable and cool. Transform your appearance into highly swanky and dashing by following this simple tutorial to make an awesome Long Hair Messy Bun and instantly transform your simple look into a fashionable one. Step 1: Comb Your Hair and Make a High Pony. Now Take Small Section of Hair from the Pony and Start Backcombing the Surface Side. Step 2: Now with Your Fingers

When you're on the go, it's important to keep your belongings organized and at an arm's distance so you're not fumbling in public for your keys, cards, or phone.

Are you thinking of a ponytail or a simple bun? If you can make a ponytail, you can make a bun, and in this guide, we'll show you how to make a bow bun—for beginners. It's a very easy, but very cute and chic, way of tying up that short hair.

UPS offers a four-step guide to prepare packages for shipping. These instructions include shipping advice on packaging materials and proper labeling that can help items arrive safely and on time. And when you are ready to ship, UPS Internet Shipping guides you through the required address fields. Packaging solutions made easy. That’s logistics.

Windows users have been getting a lot of bad news about their security lately. First, we found out that passwords in Windows 7 and 8 can easily be exploited if password hints are enabled, and now, Russian password-cracking software developer Elcomsoft has found another huge vulnerability.

This video shows the basics of limit Texas Hold 'em. Limit means that there are set amounts that you can bet, unlike no limit where at any given time you can bet your whole stack. He explains a game of $2 /$4 limit Hold 'em. This means that before the flop and after the flop you can only bet $2. On the turn and on the river you can bet $4. If you decide to make a raise on someone's bet it can only be in the set increments of 2 and 4 dollars.

Materials Needed: - Use a Size K Crochet Hook - 2 strands of 4 Ply Yarn Round 1: Start with the Chain 4, then join and wrap. Pull a loop up. Work 12-Full Size Half Double loops through the loop. Then join in the beginning Half Double crochet. Round 2: Start with a chain (1 loop). then work 2-Half Double crochets, in each stitch around for a total of 24-Half Double crochet on round 2. At end of round 2 join in beginning Half Double crochet. Round 3: Start with a chain (1 loop). Do 1-Half Doubl...

Why buy lanterns for your backyard when you can recycle empty jars into beautiful ones? This video will show you how to make lanterns out of old jars.

This video shows you how to use the don't bets in craps to insure your 6 & 8 place bets.

Spray the Styrofoam ball with a color that adheres to the scheme of the ribbon and ornaments. There will be white space when you make a Christmas ornament tree, and the color on the ball will help to conceal the space.

Choose ribbon in an appropriate color, texture and width. Are you trying to match the ribbon color to a particular gift wrap? Will the ribbon width give you the size bow you want? How will you be using the bow?

Place slip knot on hook. Hold yarn taut with 2 sets of 2 of fingers placed about 1½” apart, with tail in other hand. Create loop that crosses over bottom of 1st strand with loop toward right side. Fold loop over main strand going past tail. Insert hook below at tail strand. Pull up a loop using main strand for this loop. Pull 2 ends of yarn taut while leaving slip knot on hook. In 1st chain work 1 single crochet. Skip 2 chains; work 1 double crochet in 4thchain. Picot stitch by chaining 3 & a...

Learn how to sew a button by hand. Not wearing your favorite shirt because it’s missing a button? Don’t worry—sewing on a new one is simple and fast.

The human body contains nine units of blood—but in matters of a traumatic cut or injury, it's always better to be safe than sorry. If you're unsure whether you're in an emergency situation, get to an emergency room and let them decide.

Just as Apple, Snapchat, and other tech giants are working on augmented reality wearables in the race to replace smartphones for the future of mobile computing, so is Samsung.

When it comes to digital security, one of the best ways to protect yourself is to use two-factor authentication. Most apps these days support it, including Facebook, a site where the more privacy you can muster, the better. However, of the two 2FA options available for Facebook, only one should be used as the other will share your phone number with the world, a huge privacy concern.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

Mobile payment systems have been around for almost 5 years now, starting with Google Wallet. But when Apple got into the game last year with their new Apple Pay service, things really started to take off. Around this time, Samsung responded by acquiring an up-and-coming mobile payments company that owned the rights to an incredibly innovative technology called Magnetic Secure Transmission (MST).

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

Whether you're making a poster, drawing a logo or designing a website, the font you use can make a huge difference in any visual design, and the ones available in most word processors can get pretty boring. There are thousands of sites online where you can download free fonts, and even a few that let you design your own. Here are some of the best.

In these home security and safety videos, learn how to upgrade your house in some important ways. Our expert, Jon Olson, will show you how to secure your windows and sliding glass doors, some of your home’s most vulnerable entries, with bar locks. Learn how to install a door guard latch to keep small children from getting out, as well as a peep hole to see who’s at the front door. Finally, get some important fire safety tips and learn how to install smoke detectors for your home.

The single-player campaign mode in Call of Duty: Black Ops may be intense, but the multiplayer mode is a bloodbath of pure addiction. Black Ops takes the super successful formula of Modern Warfare and adds its own special twist. There's some changes, and Jessica Chobot from IGN Strategize is going to tell you all about them!

This video tutorial shows how to hack FarmVille (07/02/10).

This is a recent glitch, similar to the chicken coop glitch, where you can make your horse stable completely ready. Just watch this brief video tip to see how to benefit from the Horse Stable glitch in FarmVille (03/09/10). It's a simple glitch in the game that allows you to use a horse that is unready to make a stable 100% ready and be able to collect from it. This is very helpful when you are trying to achieve the HorsePower ribbon on Farmville.

This is an easy glitch in FarmVille that's been around for a long time. Stacking crops. If you want to learn how to stack your crops in FarmVille, just watch this video tip on how to do it (02/16/10). This glitch allows you to grow many more crops than usual, using your limited space on your farm to maximize the most crops in the least amount of space. By doing this glitch, you can easily achieve mastery for all crops in a quicker time frame.

To quickly receive your blue ribbon with the fences in FarmVille, you're going to want to watch this video tip. It's a brief explanation of how you can easily get the Blue "Fenced In" ribbon in FarmVille (01/11/10). BEfore you start this, you will need 75,000 coins and 77 free plots of land to get the blue ribbon.

Everybody wants to find out the answer to "How do I put trees on my crops?", but it's a tricky one to figure out. But this video walkthrough will show you the steps necessary to finally Put trees on top of crops in FarmVille (12/13/09). Just watch and learn.

Is your farm looking a little bland in FarmVille? Using a basic optical illusion, you can make what appears to be hills!